The Importance of Data Security: Key Points
- The global cost of a data breach hit $4.88 million in 2024, a 10% increase, making data security an urgent priority for businesses.
- Non-compliance with data protection laws like GDPR can result in fines up to 4% of a company’s annual turnover or €20 million (whichever is higher).
- Compliance with data protection laws not only helps avoid penalties but also builds consumer trust.
In this guide, we'll take a closer look into the risks associated with inadequate data security, look at how strong data protection supports compliance and builds trust, and outline best practices to fortify your defenses.
Risks and Consequences of Poor Data Security
Data security is the safeguarding of digital information against unauthorized access, corruption, or theft across its entire lifecycle. As too many businesses have already learned, neglecting data security can lead to severe (and cascading) repercussions.
From the immediate financial impact to reputational harm and the cost of resources needed to remediate the damage, here’s a breakdown of what’s at stake.
- Financial losses
- Reputational damage
- Legal and regulatory penalties
- Operational disruption
- Intellectual property theft
1. Financial Losses
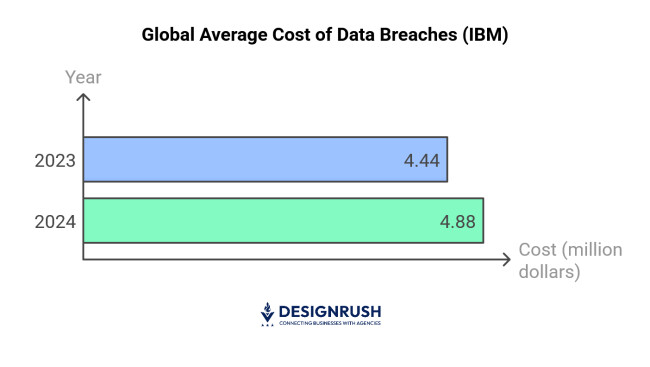
Let’s start with the most obvious and one of the most important ones. The global average cost of a data breach increased by 10% in 2024, according to IBM’s data, reaching $4.88 million, the highest recorded cost to date.
Some of the immediate costs of a breach include:
- Incident response: Costs for hiring cybersecurity experts to identify, contain, and resolve the breach.
- Business disruption: Loss of revenue due to operational downtime, system recovery, and the diversion of resources to address the breach.
- Data loss: The cost of lost or compromised intellectual property, customer records, and business data.
It turns out IBM’s report also found that organizations lacking AI-powered security automation incurred an additional $2.22 million per breach compared to those utilizing advanced security technologies.
UnitedHealth's $2.87 Billion Ransomware Fallout
In February 2024, UnitedHealth Group's subsidiary, Change Healthcare, experienced a ransomware attack that disrupted healthcare services across the US. The breach resulted in an estimated $2.87 billion in costs, encompassing system restoration, business interruptions, and support to affected providers. UnitedHealth also paid a $22 million ransom to the attackers.
This incident shows the massive financial risks associated with inadequate cybersecurity measures in critical sectors.
2. Reputational Damage
The damage to a company’s reputation following a data breach can be significant and long-lasting.
As Warren Buffett famously said during a congressional hearing in the aftermath of the Salomon Brothers scandal, "Lose money for the firm and I will be understanding. Lose a shred of reputation for the firm, and I will be ruthless."
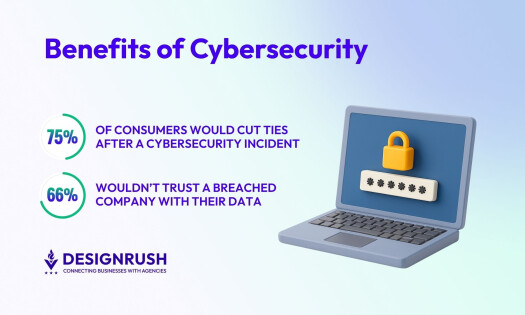
When customers’ personal information is compromised, trust is quickly eroded and hard to restore. With negative media coverage, a social media backlash, and a lasting loss of confidence, some customers will be sure to take their business elsewhere.
Ticketmaster Breach: 560M Records Exposed, Brand Takes a Hit
In 2024 the Ticketmaster breach exposed the personal data of 560 million customers, resulting in widespread negative press coverage severely damaging its brand reputation. The company was also forced to divert resources to managing the fallout (which included customer compensation).
3. Legal and Regulatory Penalties
Non-compliance with data protection laws can result in massive fines and legal challenges. These regulations are designed to safeguard personal and sensitive information by ensuring organizations handle data responsibly, so compliance demonstrates a commitment to ethical data practices.
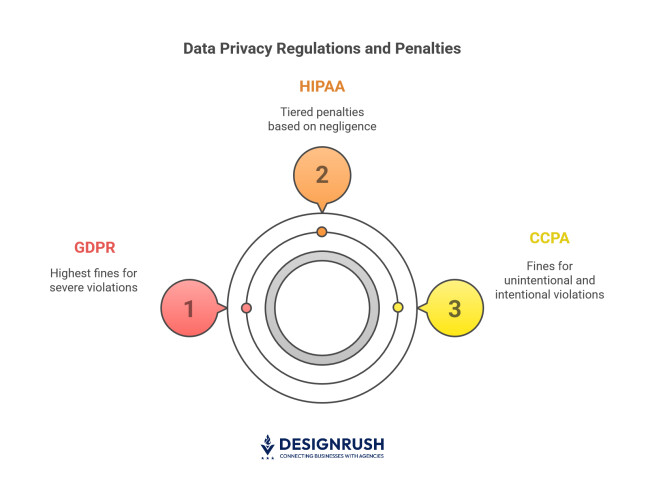
Ignore data protection laws, and here’s what you’re risking:
- General Data Protection Regulation (GDPR): Violate this, and you could be staring down fines up to €20 million or 4% of your global annual revenue — whichever hits harder. Even "milder" offenses can still cost up to €10 million or 2% of revenue. That’s enough to bankrupt smaller firms.
- Health Insurance Portability and Accountability Act (HIPAA): Mishandle health data, and you’re looking at penalties from $100 to $50,000 per violation, depending on how careless you’ve been. If the violations pile up, your total damage could reach $1.5 million per year per violation category.
- California Consumer Privacy Act (CCPA): Slip up here, and it’s $2,500 per unintentional violation and $7,500 if it’s intentional. Multiply that by the number of consumers affected, and you’ll see how fast those fines add up.
Transparency in data handling practices, such as clear privacy policies and accessible data subject rights, is sure to build consumer confidence. Remember, customers that trust a brand are more likely to engage with and remain loyal to that brand.
Meta Fined €1.2 Billion for GDPR Violation Over EU Data Transfers
In May 2023, Meta Platforms Ireland Limited faced a record €1.2 billion ($1.3 billion) fine from Ireland's Data Protection Commission for violating the General Data Protection Regulation (GDPR). The penalty was imposed due to Meta's continued transfer of EU user data to the U.S. without adequate safeguards, contravening Article 46(1) of the GDPR.
4. Operational Disruption
Compromised data can severely disrupt business operations, leading to significant downtime and loss of productivity. The impact of cyberattacks that target your business data often extends beyond immediate technical issues, affecting various facets of the organization:
- System downtime: Critical systems may become unavailable, making it challenging to maintain normal business activities.
- Data loss: Cyberattacks can lead to the loss of critical business information, affecting decision-making and operations.
- Business continuity challenges: The inability to access essential services can halt organizational activities, leading to procedural delays.
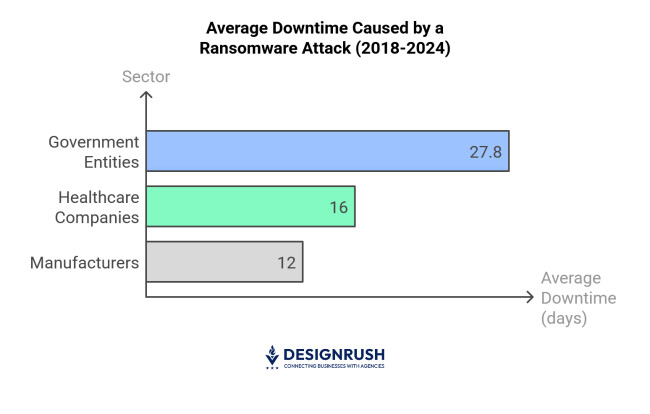
For instance, between 2018 and 2024, the average downtime caused by a ransomware attack on government entities was 27.8 days, 16 days for healthcare companies and 12 days for manufacturers. This extended period of inactivity can cripple operations, affecting everything from customer service to financial transactions.
Ransomware Attack on DDS Safe Disrupts 400 US Dental Clinics
In August 2019, a ransomware attack infiltrated DDS Safe, a data backup service used by dental offices across the US. The attack encrypted patient records and practice management data at approximately 400 dental clinics, leaving many unable to access critical systems.
The disruption halted routine operations, including appointment scheduling and billing, forcing some practices to temporarily close.
5. Intellectual Property Theft
Your innovations, products, designs, trade secrets, can be stolen, sold, or exploited before you even realize what’s missing. That’s why intellectual property (IP) theft is one of the most serious threats in data security today.
The total manufacturer's suggested retail price (MSRP) of intellectual property rights (IPR) seizures more than doubled from FY 2020 to FY 2024, indicating a significant rise in IP theft.
Acer Hit by Data Breach: 160GB of Sensitive IP Exposed and Sold
In February 2023, Taiwanese electronics giant Acer suffered a major data breach when a threat actor known as "Kernelware" infiltrated one of its document servers used by repair technicians.
The hacker claimed to have exfiltrated approximately 160GB of sensitive data, including confidential product documentation, technical manuals, BIOS and ROM files, backend infrastructure details, and Windows Imaging Format files. This trove of intellectual property was subsequently listed for sale on a hacking forum
Best Practices for Ensuring Data Security
Every business must take a careful and strategic approach to implementing robust data security measures. As Peter Leeb, VP of Commercial and Business Development at Veritone, points out, "We are in a data-driven world right now, and protecting the data ethically is our number one priority." With this in mind, businesses should prioritize ethical data protection as a core part of their security strategy.
Below are key best practices to guide your journey to improved data protection:
- Encrypting data in transit and at rest
- Restricting data access with access control
- Adding an extra layer of security with multi-factor authentication (MFA)
- Regular security audits to identify and mitigate vulnerabilities
- Employee training to build a security-aware workforce
1. Encrypting Data in Transit and at Rest
Encryption transforms readable data into unreadable ciphertext, ensuring that even if data is intercepted during transmission or accessed without authorization, it remains protected.
Utilizing strong encryption protocols, such as AES-256, helps maintain data confidentiality and integrity. Cloudflare and VeraCrypt are useful tools that offer encryption solutions to keep data secure.
You need to apply encryption consistently across all data storage and transmission points, including databases, backup systems, and communication channels.
2. Restricting Data Access With Access Control
Implementing strict access control measures ensures that only authorized individuals can access sensitive data. This can be achieved through:
- Role-Based Access Control (RBAC): Granting permissions according to predefined roles within the organization.
- Principle of Least Privilege (PoLP): Granting users the minimum level of access necessary for their job functions.
- Regular audits: Conducting periodic reviews of access permissions to ensure they remain appropriate.
Tools like Okta or Microsoft Entra ID help manage and enforce role-based access policies efficiently. By enforcing these practices, you can minimize the risk of unauthorized access and potential data breaches.
3. Adding an Extra Layer of Security With Multi-Factor Authentication (MFA)
Before gaining access to systems or data, MFA requires users to provide two or more verification factors: something they know (password), something they have (security token), or something they are (biometric data). Tools like Google Authenticator and Duo Security provide reliable MFA solutions to help secure sensitive systems.
This additional layer significantly improves security by making it more difficult for unauthorized individuals to gain access, even if they have compromised a password. It would be wise to implement MFA across all critical systems and applications.
4. Regular Security Audits To Identify and Mitigate Vulnerabilities
Conducting regular security audits helps organizations identify potential vulnerabilities and assess the effectiveness of existing security measures.
As Tom Wozniak, COO of OPTIZMO, emphasizes, "Whether it’s a company’s internal databases or those stored by vendors or technology partners, it’s important to audit the security processes and procedures in place to keep those databases secure."
Tools like Nessus for vulnerability scanning and Kali Linux for penetration testing can help organizations evaluate their security measures.
Audits should include:
- Vulnerability scanning: Identifying weaknesses in systems and applications.
- Penetration testing: Simulating attacks to evaluate system defenses.
- Compliance checks: Ensuring adherence to relevant data protection regulations.
Findings from audits should inform updates to security policies and procedures for continuous improvement.
5. Employee Training to Build a Security-Aware Workforce
Employees are often the first line of defense against cyber threats. Regular training programs should educate staff on:
- Recognizing phishing attempts: Identifying suspicious emails and links.
- Creating strong passwords: Understanding the importance of complex and unique passwords.
- Data handling best practices: Properly managing and disposing of sensitive information.
Implementing training platforms like KnowBe4 or Cofense can help teach staff to recognize phishing attempts, create strong passwords, and follow best practices for data handling.
A well-informed workforce is less likely to fall victim to cyberattacks and can contribute to a culture of security within the organization.
Incident Response Planning: Preparing for the Unexpected
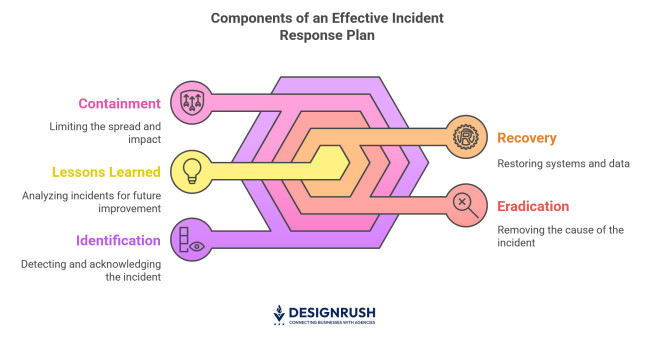
An effective incident response plan outlines the steps to take when a data breach or security incident occurs. Key components include:
- Identification: Detecting and acknowledging the incident promptly.
- Containment: Limiting the spread and impact of the breach.
- Eradication: Removing the cause of the incident.
- Recovery: Restoring systems and data to normal operations.
- Lessons Learned: Analyzing the incident to improve future responses.
Regularly testing and updating the incident response plan ensures that the organization is prepared to handle security incidents effectively, minimizing potential damage.
The Importance of Data Security: Final Words
Businesses across industries must prioritize robust data security measures to protect sensitive information and maintain stakeholder trust. The consequences of neglecting data security can be severe, affecting not just finances but reputation and operational integrity.
Before your business becomes a statistic, use the experience and expertise you need to secure its data effectively.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the Top Cybersecurity Companies as well as:
- Top Cybersecurity Marketing Agencies
- Top Cybersecurity Incident Response Companies
- Top AI Cybersecurity Companies
- Top Cybersecurity Companies in Virginia
And don’t miss our Awards section, where we celebrate the most innovative projects in design — from logo and app design to print and packaging.
The Importance of Data Security FAQs
1. How can small businesses ensure effective data security with limited resources?
Small businesses can focus on low-cost but highly effective security measures like using strong passwords, implementing multi-factor authentication, encrypting sensitive data, and conducting regular employee training. Cloud-based security services can also be a cost-effective solution for small businesses.
2. How do cloud services impact data security?
Cloud services can improve data security through advanced encryption, automatic backups, and robust access controls. However, ensure you choose reputable providers, understand shared responsibility models, and implement strong security practices to protect your cloud-hosted data.