Our expert analysts listed the leading penetration testing companies that help organizations keep malicious systems and network attacks at bay. Search and choose the most fitting partner firm for your business with our user-friendly filtering tool.
- Home
- Cybersecurity Companies
- Penetration Testing Companies
Best Penetration Testing Firms
DesignRush evaluates all cybersecurity firms listed based on technical expertise, proven practical experience, and client reviews. Some listings may be paid.
Where Quality Meets Excellence in Software Testing
TestMatick delivers quality in software testing across a wide range of industries from finance to entertainment. With our skilled quality assurance team, we can begin testing projects of any complexity within 24 hours. Our unique mix of technical expertise, industry knowledge, and professional methodologies [... see all Testmatick reviews ]Top Services:
- Cybersecurity
- Location
- New York City, New York
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $14/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 5 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsTestmatick Services
- Software Testing
Data sourced from the agency's DesignRush profileHubrick Sweetrush PageSuite Doppler Labs KEYPR oneUp Grape Global-e
Reviews verified by DesignRush and sourced from the agency's profileTestmatick Reviews & Testimonials
 Linda Cooper Vice President Development & Operations at Daxor5.0★
Linda Cooper Vice President Development & Operations at Daxor5.0★Software Testing Review from Linda Cooper
I want to commend your team for their excellent work on our recent software testing project. They were thorough, communicated well, and delivered on time. Their expertise, flexibility, and attention to detail made our software reliable and safe for our healthcare services. Thank you for your outstanding efforts!
Show more Megan Christopher Account Director at Rethink5.0★
Megan Christopher Account Director at Rethink5.0★Software Testing Review from Megan Christopher
I would like to take this opportunity to provide feedback on the recent software testing project that I had the pleasure of working on. Overall, the project was a success, and I want to commend the team for their hard work and dedication.
Show more Paul Galido Marketing at SCS International5.0★
Paul Galido Marketing at SCS International5.0★Software Testing Review from Paul Galido
Worked with Nataliia and she was outstanding in her work. Highly recommend.
Show more
We deliver Mobile Apps, Streaming, IoT Solutions & AI automation for SMEs
We deliver Mobile Apps, Streaming, IoT Solutions & AI automation for SMEs [... view Mood Up Team profile ]Top Services:
- Cybersecurity
- IT Services
- Outsourcing
- Location
- Poznan, Poland
- Number of Employees
- Under 49
- Average Hourly Rate
- $48/hr
- Portfolios Count
- 9 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsMood Up Team Services
- Mobile App Development
- IoT
- AI Development
- Software Development
- Product Design
- Cybersecurity
- Web Development
- Software Testing
- VR/AR
- IT Services
Data sourced from the agency's DesignRush profileUnilever (United Kingdom) ProSieben (Germany) Vicodo (Germany) Swimmo (United States) Flood Flash (United Kingdom) Spar (Ireland) Neos (United Kingdom) FreundeSchenken AG (Germany) MysteryVibe (United Kingdom) Qpony (Poland)
World's #1 Rated & Reviewed App, Website & Software Development Company
Worlds #1 Rated & Reviewed Tech Partner, Probey Services is a world-renowned IT and digital solutions company, headquartered in London, UK, with a state-of-the-art development center in India and 11 international branches across the USA, UK, Australia, Dubai, and beyond. [... see all Probey Services reviews ]- Location
- New York City, New York
- Number of Employees
- 1000 & Up
- Average Hourly Rate
- $50/hr
- Minimal Budget
- Under $1,000
- Portfolios Count
- 130 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsProbey Services Services
- Mobile App Development
- Software Development
- Web Development
- Web Design
- WordPress Website Design
- Digital Marketing
- Digital Services
- SEO
- IT Services
- AI Development
Data sourced from the agency's DesignRush profileBartisans Samyakk 30 Days Fitness Isharya The Estate Residences VegenMart Fresh Menu Application PRAO Fashion Jewellery Audentia Space Wings of Change
Reviews verified by DesignRush and sourced from the agency's profileProbey Services Reviews & Testimonials
- Ronan Blake Head-Business & Marketing at Greenmatter Packaging5.0★
Web Design Review from Ronan Blake
As we are in the sustainability industry, it was essential for us to have a website that not only looks professional but also conveys our brand story clearly and engagingly.The team at Probey Services was extremely responsive and patient throughout the work process. They were open to our feedback, suggested creative ideas, and paid close attention to the small details that made the final result stand out. The website is user-friendly, visually appealing, and has made it much easier for us to showcase our products to potential clients.We’re pleased with the entire experience and would definitely recommend Probey Services to anyone looking for reliable and high-quality website development.
Show more - Leander Cross Marketing Director at B Ventures5.0★
Web Design Review from Leander Cross
I am extremely satisfied with the website Probey Services developed for us. The team took the time to understand our vision and delivered a modern, user-friendly design that perfectly reflects our brand.They combined strong technical skills with smart SEO practices, ensuring fast performance and improved visibility. Communication was clear, deadlines were met, and the entire process was smooth and professional.The experience with Probey Services was more than satisfying.
Show more  Mona Kaia Singer at Mona Kaia5.0★
Mona Kaia Singer at Mona Kaia5.0★Web Design Review from Mona Kaia
Probey Services has truly developed and presented my presence as an artist. They created a stunning portfolio and website that beautifully showcases my music, albums, and artistic journey. The branding and logo design were crafted with precision, giving my identity a strong and memorable touch. Other than that I have outsourced my Social Media to them for a year, and their social media marketing strategies have expanded my reach, allowing me to connect with my audience more effectively. The team is professional, responsive, and exceptionally creative, making the entire process smooth and enjoyable. I surely recommend Probey Services to any artist, business or any brand looking to make an impact online. May this project and review bring you all the growth and recognition you deserve.I have attached the required photography as per your specifications. Wishing you and your team great success. Hope you achieve all your goals.Thanks again for your outstanding work. I look forward to future collaborations.
Show more
Product Design & Engineering for Banks, Fintechs, and Enterprise Platforms
Alty designs and builds digital products for companies where complexity is high, and decisions must withstand scale.For 16+ years, weve helped fintech, banking, and product-led organizations turn complex digital systems into scalable products used by millions. [... see all Alty reviews ]- Location
- Cascais, Portugal
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $75/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 22 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsAlty Services
- Mobile App Development
- IT Services
- Web Design
- UI/UX Design
- Web Development
- AI Development
- Software Testing
- Software Development
- Market Research
Data sourced from the agency's DesignRush profileVISA Mastercard Raiffeisen Monobank GTBank PrivatBank ABA Bank CBH Bank Renovite Corezoid
Reviews verified by DesignRush and sourced from the agency's profileAlty Reviews & Testimonials
 Ewa Koltunczyk (Karabon) Regulatory Specialist II at CID LINES, An Ecolab Company5.0★
Ewa Koltunczyk (Karabon) Regulatory Specialist II at CID LINES, An Ecolab Company5.0★Mobile App Development Review from Ewa Koltunczyk (Karabon)
I recently had the pleasure of working with Alty to develop our mobile app. We needed a developer who was able to translate my vision and provide technical guidance. The experience has been nothing short of outstanding. From the initial consultation to the final product, Alty's professionalism, expertise, and dedication have exceeded my expectations. Alty has demonstrated a deep understanding of mobile app development and was willing to go the extra mile. Their ability to translate my ideas into a seamless, user-friendly, and visually appealing app is truly impressive
Show more Adam Kubas Director at Institute of Physical Chemistry PAS5.0★
Adam Kubas Director at Institute of Physical Chemistry PAS5.0★Mobile App Development Review from Adam Kubas
Alty did excellent work for our department. The team prepared a high-quality and easy-to-understand development roadmap for Virtual Academy of Bioinformatics. Their positive attitude and willingness to learn made them a pleasure to work with. Overall, I highly recommend Alty for any development role. They have the skills, dedication, and professionalism to excel. Thank you for developing our app.
Show more Rajesh Kasturirangan Founder at Socratus5.0★
Rajesh Kasturirangan Founder at Socratus5.0★Web Development Review from Rajesh Kasturirangan
The team at Alty is indeed filled with tech engineers and assiduous individuals with excellent software development skills! The end product work had minimal bugs. Alty has exceptional communication skills, identifies top talent, and goes above and beyond to ensure a smooth development.
Show more
Modern IT. Built Secure. Delivered Right.
Zazz covers the full cybersecurity stack, from penetration testing and Zero Trust architecture to 24/7 SOC monitoring and incident response. Delivering 100+ security audits, the cybersecurity company offers technical depth and audit-ready compliance to its clients. [... see all Zazz reviews ]- Location
- Seattle, Washington
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $45/hr
- Portfolios Count
- 36 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsZazz Services
- Mobile App Development
- IT Services
- Software Development
- Staff Augmentation
- IT Compliance Solution
- Cybersecurity
- Managed Services
- Cloud Consulting
- DevOps Consulting
- Web Development
Data sourced from the agency's DesignRush profileJP Morgan BBC News PayPal Harvard Innovation Labs HBO Jeddah Season McDonald's NBA Honda Citibank
Reviews verified by DesignRush and sourced from the agency's profileZazz Reviews & Testimonials
 Sam Zaid CEO at Getaround5.0★
Sam Zaid CEO at Getaround5.0★Mobile App Development Review from Sam Zaid
Their team's technical proficiency and creativity have significantly contributed to the success of our world's first connected carsharing marketplace. Zazz not only met but exceeded our expectations, delivering a seamlessly integrated and user-friendly mobile app that has truly empowered people to carshare everywhere. The collaboration with Zazz has proven to be a valuable partnership, marked by open communication, timely delivery, and a genuine dedication to our mission.
Show more Jay Thrash SENIOR IOS DEVELOPER at Epic Games5.0★
Jay Thrash SENIOR IOS DEVELOPER at Epic Games5.0★Mobile App Development Review from Jay Thrash
Their unparalleled expertise and dedication to excellence were evident throughout the entire collaboration. Zazz's team consistently demonstrated a deep understanding of our vision, translating it into a seamless and innovative mobile application. Their commitment to quality and precision in every aspect of the development process was truly impressive. Zazz's ability to navigate complex challenges with agility and deliver solutions that exceeded our expectations was instrumental in the success of our project.
Show more Don Harmon Director of Global IT Services at Dorel Juvenile5.0★
Don Harmon Director of Global IT Services at Dorel Juvenile5.0★Mobile App Development Review from Don Harmon
Zazz's commitment to delivering a high-quality mobile app for Dorel Juvenile was evident throughout the entire development process. The team consistently communicated progress, promptly addressed any concerns or modifications, and ensured that the final product not only met but exceeded our expectations. The mobile app developed by Zazz not only showcased cutting-edge technology but also reflected a deep understanding of the child-centric focus that Dorel Juvenile upholds.
Show more
Award-winning and Passion-driven app development company. More than a Tech partner.
Top 10 Web and Mobile App Developer in Singapore | ISO Certified | Top 100 Singapore's fastest-growing companies 2024 [... see all Vinova reviews ]- Location
- Singapore, Singapore
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $30/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 16 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsVinova Services
- Software Development
- Mobile App Development
- Web Development
- Blockchain
- AI Development
- IT Services
- ERP Consulting
- Staff Augmentation
- Web Design
- BPO
Data sourced from the agency's DesignRush profileAIA Prudential Samsung DHL Abbott MARS FWD SingHealth PWC Yale NUS
Reviews verified by DesignRush and sourced from the agency's profileVinova Reviews & Testimonials
 Ben Dietrich CEO at Mediacharge5.0★
Ben Dietrich CEO at Mediacharge5.0★Mobile App Development Review from Ben Dietrich
The thing we appreciate the most about Vinova is their dedication to understanding our specific needs and delivering tailored solutions. Their team was not just focused on completing the project but also on adding value to our business. Their expertise in software development, proactive approach, and consistent communication made the whole process remarkably smooth. Their development team was agile, and their project managers were incredibly effective in handling any hiccups along the way.
Show more Cody C. Jensen CEO at Searchbloom5.0★
Cody C. Jensen CEO at Searchbloom5.0★Software Development Review from Cody C. Jensen
The endeavor was titled "Operational Excellence System" and was executed in collaboration with Vinova. The aim of this project was to create an internal corporate system designed to automate and manage various operational processes within our organization. The system needed to integrate with existing tools and allow for real-time tracking, monitoring, and analytical reporting. Vinova delivered this system and continues to provide ongoing support and updates.
Show more Scott Darrohn Co-Founder at fishbat5.0★
Scott Darrohn Co-Founder at fishbat5.0★Web Development Review from Scott Darrohn
I had the pleasure of working with Vinova on developing a website for my company, and I can confidently say they exceeded my expectations. From start to finish, their team demonstrated exceptional expertise, professionalism, and dedication.
Show more
Engineering Intelligent Solutions Through Design and Code - Web, Mobile AI, Blockchain
At SapientPro, we build high-quality software solutions and provide expert consulting services to help businesses grow. Since 2017, our team has been delivering custom-built solutions to meet unique business needs. [... see all SapientPro reviews ]- Location
- Tallinn, Estonia
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 15 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSapientPro Services
- AI Development
- eCommerce Development
- Mobile App Development
- Web Design
- Web Development
- Software Development
- IT Services
- UI/UX Design
- Blockchain
- DevOps Consulting
Data sourced from the agency's DesignRush profileZich Solutions Contentoo HEX MasTrack Sprinkle Slab Sharks SalesLogs Piktochart The Big Data Chef Footshop
Reviews verified by DesignRush and sourced from the agency's profileSapientPro Reviews & Testimonials
 Slava Berkovich Chief Technology Officer at Saleslogs5.0★
Slava Berkovich Chief Technology Officer at Saleslogs5.0★Software Development Review from Slava Berkovich
SapientPro consistently delivers high-quality work that aligns with project requirements. The team demonstrates strong expertise in Angular, TypeScript, and JavaScript. Their project management and communication practices are highly effective, with weekly client meetings held to provide updates on progress and ensure alignment.
Show more Jeremy Ott Founder at Marketing Reporting Tool5.0★
Jeremy Ott Founder at Marketing Reporting Tool5.0★Software Development Review from Jeremy Ott
This team was extremely responsive from the start. They pulled together a comprehensive quote for my MVP and have delivered on all of the requirements. The daily updates from the product/project manager are extremely helpful and it’s clear that the team cares about the quality of work they deliver. The engineers working on the product are always willing to make recommendations and go above and beyond to make the experience and underlying infrastructure that much better.
Show more Luc Vlekken CEO at Liswood & Tache5.0★
Luc Vlekken CEO at Liswood & Tache5.0★eCommerce Development Review from Luc Vlekken
We've had the pleasure of working closely with this development team on several projects, and the experience has been consistently excellent. Not only are they highly skilled developers, but they also think along with us both from a technical and a product/customer perspective. Their proactive attitude, reliability, and ability to translate complex requirements into elegant solutions make them a true partner rather than just a supplier. Highly recommended.
Show more
The Right Technology Partner Can Change Everything
TechnoYuga is a leading AI-Native product engineering company established with the vision of helping startups, SMEs, and enterprises build powerful, scalable, and future-ready technology solutions that drive real business growth. [... see all Technoyuga Soft reviews ]- Location
- New York City, New York
- Number of Employees
- Under 49
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 23 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsTechnoyuga Soft Services
- Mobile App Development
- Software Development
- IoT
- Blockchain
- AI Development
- Software Testing
- Web Development
- eCommerce Development
- Web Design
- IT Services
Data sourced from the agency's DesignRush profileDecathlon Akasa Air Justlife Ordeno GFacility Trulipay
Reviews verified by DesignRush and sourced from the agency's profileTechnoyuga Soft Reviews & Testimonials
 Fahmi Elabed CEO at Piccolo Trattoria5.0★
Fahmi Elabed CEO at Piccolo Trattoria5.0★Mobile App Development Review from Fahmi Elabed
It was a pleasure working with TechnoYuga Soft. For Piccolo Trattoria, they created an intuitive and effective web application that has simplified our online ordering and reservation process. Their staff was punctual, kind, and professional. Their attention to detail really made a difference, and the caliber of their work surpassed our expectations. Strongly advised for any eatery trying to improve their online visibility!
Show more Manuel Sonnleithner CEO at TradersYard5.0★
Manuel Sonnleithner CEO at TradersYard5.0★Mobile App Development Review from Manuel Sonnleithner
The quality of work that TechnoYuga Soft has provided is outstanding. The commitment to delivering a mobile app that is of high quality for TradersYard has been great. Our relationship has been very collaborative, the team has been able to deliver on time and within the budget. TechnoYuga Soft enthusiasm for the project was my favorite part. I'm very pleased with project outcome, and will definitely recommend their service!
Show more Troy Abromaitis SDM at Musqueam Capital Corporation5.0★
Troy Abromaitis SDM at Musqueam Capital Corporation5.0★Mobile App Development Review from Troy Abromaitis
It was a pleasure to collaborate with TechnoYuga Soft on our real estate smartphone app. Our clients' ability to search properties and communicate with us has greatly increased because to the slick, user-friendly software they developed after understanding our demands. Throughout the project, their staff demonstrated professionalism, responsiveness, and a dedication to quality. We're thrilled with the outcome and forward to work together once more.
Show more
Next gen of QA, riding the wave of agentic pipelines.
BetterQA provides independent security testing using 8 proprietary tools, combining AI-powered triage and human expert review. With 50+ engineers, the cybersecurity company helps businesses with fast-moving teams needing audit-ready compliance coverage. [... see all BetterQA reviews ]- Location
- Cluj-Napoca, Romania
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 8 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsBetterQA Services
- Software Testing
- IT Services
- Cybersecurity
- DevOps Consulting
- Business Consulting
- Customer Support
Data sourced from the agency's DesignRush profilevulog eyeware primeur Collaboard butter. Owlet MEDIAL Multimedia services YZR
Reviews verified by DesignRush and sourced from the agency's profileBetterQA Reviews & Testimonials
 Brenda Collin FIH Executive Vice President at Preferred Travel Group5.0★
Brenda Collin FIH Executive Vice President at Preferred Travel Group5.0★Software Testing Review from Brenda Collin FIH
Our busy online marketplace couldnt afford downtime or broken features after updates. BetterQA built and maintained a robust automated regression suite that tested checkout, search, user dashboards, and seller workflows. Their automation scripts run with every deployment and catch issues before users experience them. The improvement in deployment confidence and QA turnaround has been tremendous. Their technical skills in Selenium and Cypress, plus their understanding of business workflows, helped us scale operations without QA bottlenecks.
Show more Christopher Savage CEO at Greater Fort Lauderdale Chamber of Commerce5.0★
Christopher Savage CEO at Greater Fort Lauderdale Chamber of Commerce5.0★Software Testing Review from Christopher Savage
We worked with BetterQA on a software testing project and were thoroughly impressed by their professionalism and precision. Their team identified key issues early, ensuring our product was stable and ready for launch. A reliable QA partner wed gladly work with again
Show more Ramesh Pathak CEO and Co-founder at Naamche5.0★
Ramesh Pathak CEO and Co-founder at Naamche5.0★Software Testing Review from Ramesh Pathak
We partnered with BetterQA for software testing across several of our products. Their team handled both manual and automated testing, identifying critical bugs and improving release stability. Their detailed reports and fast feedback loop made our development process smoother. We were impressed with their professionalism and consistent quality of work.
Show more
ELEKS, a trusted partner for guaranteed software engineering excellence, quality, and transparency.
ELEKS runs a six-stage security process from discovery to managed services, spanning penetration testing, threat hunting, and compliance. With its proprietary HITRUST-certified eCAP platform, the cybersecurity company offers expertise in complex regulatory environments. [... see all ELEKS reviews ]- Location
- Chicago, Illinois
- Number of Employees
- 1000 & Up
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 12 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsELEKS Services
- Software Development
- Mobile App Development
- Cloud Consulting
- Cybersecurity
- AI Development
- ERP Consulting
- CRM Consulting
- Product Design
- Big Data Analytics
Data sourced from the agency's DesignRush profileAramex TAIT Acino GRTGaz Autodesk Blackboard Havas ESET Eagle teleologica
Reviews verified by DesignRush and sourced from the agency's profileELEKS Reviews & Testimonials
 John Armstrong Founder, CEO & CTO at Civex5.0★
John Armstrong Founder, CEO & CTO at Civex5.0★Software Development Review from John Armstrong
ELEKS was able to take our vision and help us deliver an app that empowers retail shareholders to make their voices heard. They’ve brought a depth and breadth of technical expertise and user experience design to challenge us on our assumptions on how people would want to interact with the app. From a mobile development perspective, we wanted to go to market with both an Android and an iPhone simultaneously.
Show more Mark Battcock Digital Communication Director at Imerys5.0★
Mark Battcock Digital Communication Director at Imerys5.0★Software Development Review from Mark Battcock
We are very happy with our ELEKS partnership; the dedication of the team is exceptional. We would certainly recommend ELEKS and would be happy to work with them again. In fact, they continue to be our partner for the 2nd phase of the CDX project to add even more customer services to the website.
Show more Huntly Christie CEO at Christie Lites5.0★
Huntly Christie CEO at Christie Lites5.0★Software Development Review from Huntly Christie
What impressed me about ELEKS is the culture. There is a very strong culture of discipline and performance, and software is a profession where discipline is very important. Good software development can only happen with a strong work ethic, and I think the ELEKS team really understands that.
Show more
AI-Driven Software Development Company in Singapore
At TechTIQ Solutions, we are your most trusted software development company and digital transformation consultant partner and are focused on getting projects done accurately, effectively and efficiently. Contact us today and tell us which business challenge you are facing, and we will help you to find an [... see all TechTIQ Solutions reviews ]- Location
- Singapore, Singapore
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $35/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 2 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsTechTIQ Solutions Services
- Software Development
- Mobile App Development
- Web Development
- Web Design
- AI Development
- eCommerce Development
- Software Testing
- WordPress Website Design
- Product Design
- IT Services
Data sourced from the agency's DesignRush profileVoista Standard Chartered YPO One Harvest
Reviews verified by DesignRush and sourced from the agency's profileTechTIQ Solutions Reviews & Testimonials
 Melody Hammer Human Resources Manager at Grede Holdings LLC5.0★
Melody Hammer Human Resources Manager at Grede Holdings LLC5.0★Web Design Review from Melody Hammer
TechTIQ had to take our legacy app, move it to the cloud, improve it and redesign it. The speed of inspection interaction was reduced from 20 seconds to 4 seconds. The application is running fully on the cloud. They were flexible with reasonable changes in scope. Everything was delivered on time or within a reasonable delay due to scope changes.
Show more Dustin D. Trammell Chief Executive Officer at Blockhenge5.0★
Dustin D. Trammell Chief Executive Officer at Blockhenge5.0★Mobile App Development Review from Dustin D. Trammell
The scope of the project was to deliver an app that would integrate online and offline money transfer and payment capabilities to cater to our growing users. Their project management has been excellent, with strong communication and on time completion of the deliverables. TechTIQ was great.
Show more Max Frolov Founder and CEO at DataRoot Labs5.0★
Max Frolov Founder and CEO at DataRoot Labs5.0★Software Development Review from Max Frolov
I was particularly struck by the comprehensive consulting and advisory services rendered by Techtiq Solutions throughout the course of our project. Their consistent provision of fresh perspectives and input from both their business and engineering teams was instrumental in facilitating efficient identification of the best solutions, ultimately allowing us to meet our project deadlines.The seamless integration and cohesiveness of our teams were truly impressive, operating as a well-oiled machine. Moreover, the team's outstanding technical prowess was truly commendable, firmly establishing their reputation as true luminaries in their field.
Show more
Pixelette Technologies - Leading the way in AI & Blockchain
Pixelette Technologies - Leading the way in AI & Blockchain [... see all Pixelette Technologies reviews ]- Location
- London, United Kingdom
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 43 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsPixelette Technologies Services
- Software Development
- Web Development
- Web Design
- Blockchain
- Mobile App Development
- AI Development
- VR/AR
- Staff Augmentation
- IT Services
Data sourced from the agency's DesignRush profileCast Lighting Rooms in Huddersfield One Stop CCTV Airobounce WildWood Resturants Kumon Ystral Webfixxim Who Can Fix My Car Positive Prime
Reviews verified by DesignRush and sourced from the agency's profilePixelette Technologies Reviews & Testimonials
 Mark Vetrano CEO|CSO at Contact Fuel5.0★
Mark Vetrano CEO|CSO at Contact Fuel5.0★Blockchain Review from Mark Vetrano
Temur's team was professional, responsive, and made the entire process smooth. Were impressed with the results and how much value their solution has added to our business.If you're looking for innovative blockchain solutions, Pixelette Technologies is the way to go!
Show more Lauren Ratner President & Chief Brand Officer at rhode skin5.0★
Lauren Ratner President & Chief Brand Officer at rhode skin5.0★Software Development Review from Lauren Ratner
Pixelette Technologies designed custom software that streamlined our internal workflows and optimized our operations. The solution was tailored perfectly to our unique requirements, and their team went above and beyond to ensure a smooth implementation.
Show more Arty Harjai CEO at HGG (Harjai Global Gurukul)5.0★
Arty Harjai CEO at HGG (Harjai Global Gurukul)5.0★Mobile App Development Review from Arty Harjai
Pixelette Technologies delivered ann exceptional e-learning platform that has improved the way we deliver educational content. The team was professional and responsive, ensuring the project exceeded all expectation.
Show more
Lets build some tech together!
Genetech Solutions offers cybersecurity across application security, network security, disaster recovery, and compliance consultation. With clients across fintech, healthcare, and logistics, it suits SMBs looking for a single partner to assess, build, and manage their full security program. [... see all Genetech Solutions reviews ]- Location
- Ann Arbor, Michigan
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 37 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsGenetech Solutions Services
- Software Development
- AI Development
- Mobile App Development
- Staff Augmentation
- Cybersecurity
- Web Development
- WordPress Website Design
- Software Testing
- eCommerce Development
Data sourced from the agency's DesignRush profileDearing Studio Stubgroup NIKOS Global Nephrology Solutions Le Bijou Solutions 8 TheBlueFish.com MicroElec Technical 3PL Systems Inc. My Boracay Guide
Reviews verified by DesignRush and sourced from the agency's profileGenetech Solutions Reviews & Testimonials
 Jason Stern President at Enlightened Media5.0★
Jason Stern President at Enlightened Media5.0★Web Design Review from Jason Stern
This company is a pleasure to work with. They respond timely and have a true expertise in their field. We recommend them for any advanced website code, e-commerce coding, tracking or SEO related projects.
Show more Griffin Joliboix COO at The Basketry by Phina5.0★
Griffin Joliboix COO at The Basketry by Phina5.0★Web Development Review from Griffin Joliboix
The team at Genetech did a great job helping us get our website back on track when updates were pushed through that we were unaware of. These updates caused implications that were problematic to our website performance at the most crucial time of the year for our sales, and their timely work helped out tremendously.
Show more Ramy Hanna CEO at Trinity Design and Build LLC5.0★
Ramy Hanna CEO at Trinity Design and Build LLC5.0★Web Design Review from Ramy Hanna
Best team to contact with, Easy to communicate, They take u step by step to complete our project in an easy efficient way, Reasonable price, I recommend them
Show more
Turning Digital Ideas into Powerful & Lucrative Realities
WEZOM brings 26 years of cybersecurity experience, covering penetration testing, vCISO, EDR, and compliance support. Having 250+ long-term clients, including Metinvest and Aptiv, the cybersecurity company is best for enterprises in logistics, healthcare, and fintech seeking a proven security partner. [... see all Wezom reviews ]- Location
- Chicago, Illinois
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $49/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 23 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsWezom Services
- IT Services
- Software Development
- Mobile App Development
- Web Design
- eCommerce Development
- Cybersecurity
- UI/UX Design
- Business Consulting
- ERP Consulting
- Big Data Analytics
Data sourced from the agency's DesignRush profileMetinvest John Deer Roshen INTERPIPE Aptiv Toyota Material Handling SCHWARZ LOGISTICS Cooper & Hunter OneVoiPlanet Nova Lines
Reviews verified by DesignRush and sourced from the agency's profileWezom Reviews & Testimonials
 Elena Nosenko Lead Account Manager at Elogic Commerce5.0★
Elena Nosenko Lead Account Manager at Elogic Commerce5.0★IT Services Review from Elena Nosenko
Elogic Commerce highly recommends WEZOM as a trusted partner for CRM system development. They demonstrated a deep understanding of our needs and delivered a custom solution that optimized workflows, enhanced client engagement and ensured scalability.WEZOMs professionalism, technical expertise, and dedication made the collaboration seamless and productive. We confidently recommend them to any business seeking a reliable partner for CRM development.
Show more Victoria Savchuk Marketing Manager at Alcor5.0★
Victoria Savchuk Marketing Manager at Alcor5.0★Software Development Review from Victoria Savchuk
Alcor is pleased to recommend WEZOM as a reliable partner in the development and implementation of an R&D center management system.WEZOM demonstrated a deep understanding of our business needs and successfully implemented a platform
Show more Violeta Baranovska Head of Marketing at VT Labs5.0★
Violeta Baranovska Head of Marketing at VT Labs5.0★Software Development Review from Violeta Baranovska
VT Labs is incredibly impressed with WEZOM's expertise in developing custom VR/AR marketing and sales tools for our client. The collaboration was fascinating and successful.We were looking for ways to showcase VR/AR technology in a more engaging and immersive manner. WEZOM listened to our needs and created stunning VR experiences and interactive sales presentations that truly capture the power of VR/AR.
Show more
Certified Experts, Patented Excellence
Digis integrates security throughout the SDLC, combining SAST, DAST, penetration testing, and AI-powered threat modeling under one team. With clients like HubSpot and BlaBlaCar, it offers expertise in fintech, healthcare, and eCommerce companies that want security built in, not bolted on. [... see all Digis reviews ]- Location
- New York City, New York
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $39/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 22 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsDigis Services
- Staff Augmentation
- Web Design
- Web Development
- Mobile App Development
- IT Services
- Software Development
- Managed Services
- Cybersecurity
- Product Design
- UI/UX Design
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Staff Augmentation Project for eCommerce Company Sports Equipment Marketplace 
Staff Augmentation Project for Automotive Company Electric Scooter Solution 
Staff Augmentation Project for Automotive Company Vehicle Delivery Platform 
Staff Augmentation Project for Software & IT Services Company Leading Marketing Platform
Data sourced from the agency's DesignRush profileBlaBlaCar PWC EDP HubSpot SKF. Huma Otoqi ZEWAY
Reviews verified by DesignRush and sourced from the agency's profileDigis Reviews & Testimonials
 Wladimir Wolinski Project Manager at Seven Tips UG & Co. KG5.0★
Wladimir Wolinski Project Manager at Seven Tips UG & Co. KG5.0★UI/UX Design Review from Wladimir Wolinski
Communication was smooth either through our teams communication channel or with the project manager via email. We were in daily contact with the UX/UI designer in form of dailies or when we had to clarify some questions. With the project manager, we had a short conversation every 2 weeks to clarify all possible questions.We personally love to work in a very process-oriented way. Because when we understand how to do something, we usually know how the end result can look like. With Digis, we also had the feeling that they knew what they were doing and how to do it. Every next step was planned from the beginning. If something didn't work in line with our processes, we could readjust it.We were basically satisfied with everything.
Show more Michael Wilson Co-Founder at Part Swap5.0★
Michael Wilson Co-Founder at Part Swap5.0★Website Redesign Review from Michael Wilson
Digis is redesigning our website to a magento based platform to migrate from a Wordpress based platform. Key deliverables include a full discovery document to determine and outline the scope of the work and the magento platform with custom development to fit our needs.Everything has been delivered on time. Danila our project manager has great communication and always responds in a timely manor. We always receive clear explanations and detailed time logs for the work that is done.
Show more Gina Levy CEO at KindraConnect5.0★
Gina Levy CEO at KindraConnect5.0★Mobile App Development Review from Gina Levy
Both the developer and tester have exceeded expectations. Their performance is excellent. Together they eliminated bugs, introduced new features, and ensured that the app is working without problems. Previously, we had many complaints in the app store. Since working with this developer and tester, these complaints about the app functioning and bugs have disappeared.The time zone different is sometimes challenging, since we are in California and they are in Europe.
Show more
Infograins Software Solutions, Innovate, Automate, Dominate
Infograins Software Solutions Pvt. Ltd., established in 2013 by Ajay and Vipin Shukla, delivers innovative IT services, including blockchain solutions, mobile app development, custom software development, staff augmentation, and AI integration. Our dedicated team provides goal-oriented solutions. [... see all Infograins reviews ]- Location
- Chicago, Illinois
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 4 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsInfograins Services
- Mobile App Development
- Staff Augmentation
- Blockchain
- Software Development
- AI Development
- IT Services
- Web Design
- Web Development
- IoT
- Software Testing
Data sourced from the agency's DesignRush profileMX-DIAMOND RAPAPORT DAMAC OS REALESTATE EAT REWARD TRADESTREET OMNIHORSE NFT FOOTY RYTHUM COIN OMAX
Reviews verified by DesignRush and sourced from the agency's profileInfograins Reviews & Testimonials
 Dan Adika CEO and FOUNDER at WalkMe5.0★
Dan Adika CEO and FOUNDER at WalkMe5.0★Software Development Review from Dan Adika
Infograins has helped us develop our custom software system. Before we signed the contract, we had initial pre-sales meetings, during which I provided them with documentation. We also signed an NDA so that they could look at everything I provided. Then, Infograins came back with an in-depth project proposal of about 50 pages and we signed the contract. As for the technology stack, we're using React.js, Python, and Django to create this software piece. Moreover, our whole backend is hosted in AWS. We're very happy and satisfied with how everything has turned out and with the whole Infograins team. Their willingness to discuss issues, fix problems, and help us with anything we need is great, so I wouldn't want to have developed this product, especially the MVP with anyone else. I can't think of anything Infograins could change. Going forward with other projects, we might find some improvements. Thus far, we're very happy with them
Show more Steve Melink Founder at Melink Corporation5.0★
Steve Melink Founder at Melink Corporation5.0★AI Development Review from Steve Melink
Infograins help us to create AI-based cloud document gateway that provides end-to-end transactional document automation. It aims to provide a comprehensive transactional document automation platform that empowers enterprises to process millions of transactions seamlessly. The software will be centered on boosting productivity, precision, and efficiency while leveraging AI-driven technologies. They deliver the project on time and i am impressed with their working style, our communication is through skype and email.they are good with there work and expertise.
Show more Dora White Management at Walmart5.0★
Dora White Management at Walmart5.0★Software Development Review from Dora White
Our complex requirements were successfully converted by them into a user-friendly, highly functional program. Throughout the project, their proficiency in both technical development and user experience design was apparent. We valued their openness and dedication to providing a first-rate product on schedule. The best choice for app development is INFOGRAINS
Show more
Strategic Technology Partner
Moving past IT Outsourcing, let us become your Strategic Technology Partner who will have you covered and kindle your digital innovations. [... see all Synodus reviews ]- Location
- Hanoi, Vietnam
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $18/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 16 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSynodus Services
- Web Development
- Blockchain
- Software Development
- AI Development
- IoT
- Mobile App Development
- IT Services
- Big Data Analytics
- Product Design
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio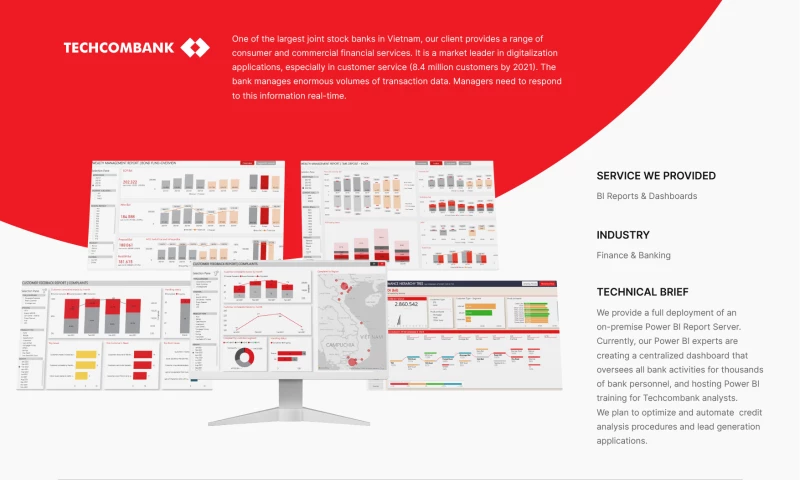
Big Data Analytics Project Techcombank BI Reports & Dashboards -thumb-webp.webp)
Big Data Analytics Project Boody Data Warehouse & Visualization 
Big Data Analytics Project Credit Scoring & Risk Management
Data sourced from the agency's DesignRush profileDeFi For You Gamestate.one Smartchannel AU Boody AU Cyber8 Softline Techcombank Unilever KPMG Viettel
Reviews verified by DesignRush and sourced from the agency's profileSynodus Reviews & Testimonials
 Joeri Leeuwerik Sales Photographer at Brandist NYC5.0★
Joeri Leeuwerik Sales Photographer at Brandist NYC5.0★Web Development Review from Joeri Leeuwerik
Synodus developed a digital identity verification solution for us, and we are very pleased with the results. The project was completed on time, and their team stayed within budget constraints. They were highly responsive and maintained clear communication throughout the process. The solution is efficient and secure, meeting all our requirements.
Show more Madeline Perez Organization Manager at Land Home Financial Services5.0★
Madeline Perez Organization Manager at Land Home Financial Services5.0★Big Data Analytics Review from Madeline Perez
Our experience with Synodus on the analytics dashboard project was fantastic. They demonstrated a deep understanding of our requirements and delivered a solution that provides actionable insights from our data. The project was completed on schedule and within budget. Their communication and support were top-notch, making the whole process smooth and effective.
Show more Hershey Rosen Tech entrepreneur at Tech Entrepreneur5.0★
Hershey Rosen Tech entrepreneur at Tech Entrepreneur5.0★Mobile App Development Review from Hershey Rosen
We work with Synodus in making a mobile banking app for us that has significantly improved our customer engagement. Their team was professional, adhered to the timeline, and stayed within budget. They provided excellent support and were always available to address our concerns. The app is intuitive and has received positive feedback from our users.
Show more
Your Technology Partner
SDLC Corp is a software development company founded in 2015 and headquartered in San Francisco, USA. With 400+ professionals, the company provides software, web and mobile, AI, ERP, blockchain, SaaS, cloud, and gaming development services for startups and enterprises across multiple industries. [... see all SDLC Corp reviews ]- Location
- San Francisco, California
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $30/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 50 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSDLC Corp Services
- Software Development
- Mobile App Development
- Web Development
- AI Development
- Blockchain
- eCommerce Development
- IT Services
- VR/AR
- CRM Consulting
- ERP Consulting
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio-thumb-webp.webp)
IT Consulting Project for HR Company Hinani solutions - Odoo Migration Services Experts 
IT Services Project for Automotive Company EximRo.Co - Odoo Implementation services for BUSINESS 
IT Services Project for Automotive Company SkyPeak Port - POS System Development
Data sourced from the agency's DesignRush profileFujitsu Rubix EduBull Giftcast Flynk Early Salary PorchLight Group Windermere Saas Bazaar Dominos
Reviews verified by DesignRush and sourced from the agency's profileSDLC Corp Reviews & Testimonials
 Navrina Singh Founder & CEO at Credo AI5.0★
Navrina Singh Founder & CEO at Credo AI5.0★Odoo Review from Navrina Singh
As a growing business in Australia, our internal systems had become difficult to manage. We partnered with SDLC CORP for Odoo development, and their team took the time to understand our workflows and bottlenecks. They automated repeated tasks, streamlined our processes, and kept communication clear at every step. This was not a one-time quick fix; it continues to improve how we run the business every day.
Show more Robert Khachatryan Founder at Freight Right Global Logistics5.0★
Robert Khachatryan Founder at Freight Right Global Logistics5.0★Software Development Review from Robert Khachatryan
Working with SDLC Corp on IoT supply chain project has helped us at Freight Right Global Logistics. Their smart tracking and fleet management have helped us work faster by reducing delays and improving delivery routes. The temperature sensors for perishables gave us peace of mind, keeping our products safe and fresh. Overall, their expertise and smooth support made the whole process easy and stress-free!
Show more Ritujoy Narayan Chowdhury Managing Director at Franklin Park5.0★
Ritujoy Narayan Chowdhury Managing Director at Franklin Park5.0★Web Design Review from Ritujoy Narayan Chowdhury
We partnered with SDLC Corp to explore automating client services like reporting and task tracking. They provided a clear and detailed roadmap for building software tailored to our needs, complete with features like client dashboards and real-time analytics. Their project management was seamless, and their ability to combine technical know-how with industry insight was outstanding. Their work has set us up to optimize our workflows and better serve our clients. We couldnt be more impressed with the collaboration!
Show more
Unlock Tomorrow
Computools covers the full cybersecurity stack from penetration testing and Zero Trust network security to industrial ICS/OT protection and DevSecOps integration. With multi-certified engineers, it serves fintech, healthcare, and manufacturing companies seeking compliant and hands-on threat defense. [... see all Computools reviews ]- Location
- New York City, New York
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 25 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsComputools Services
- Software Development
- Mobile App Development
- Web Development
- Cloud Consulting
- AI Development
- Staff Augmentation
- Big Data Analytics
- Product Design
- Cybersecurity
- Blockchain
Data sourced from the agency's DesignRush profileVisa IBM Bombardier Dior British Council Caribbean Bank MeterSnap Dental Health BeEducated Green Energy
Reviews verified by DesignRush and sourced from the agency's profileComputools Reviews & Testimonials
 Marie Jenkins CO-Founder & Sourcing Manager at Valo Recruitment5.0★
Marie Jenkins CO-Founder & Sourcing Manager at Valo Recruitment5.0★Mobile App Development Review from Marie Jenkins
Working with Computools has been a truly rewarding experience. Their team demonstrated professionalism, deep technical expertise, and strong communication throughout our project. They took the time to understand our needs and delivered a custom solution that exceeded expectations.What impressed us most was their ability to combine innovative thinking with structured execution. Computools didnt just provide software developmentthey offered valuable consulting that helped us improve efficiency and customer experience. The final product was delivered on time, met all compliance requirements, and added measurable value to our business.We highly recommend Computools to any company looking for a reliable, forward-thinking software partner.
Show more Nicole Siaw European Hydrogen Market Analyst at Aurora Energy Research5.0★
Nicole Siaw European Hydrogen Market Analyst at Aurora Energy Research5.0★Web Development Review from Nicole Siaw
Computools developed a customized CRM system that significantly improved our financial agencys operations. Their team was highly professional, responsive, and detail-oriented throughout the process. The solution streamlined client management, boosted efficiency, and provided valuable insights for decision-making. We were impressed with their technical expertise and commitment to delivering on time.
Show more Frank Tufail Smith FS Transaction Services, Manager at PwC at PwC5.0★
Frank Tufail Smith FS Transaction Services, Manager at PwC at PwC5.0★Web Development Review from Frank Tufail Smith
We partnered with Computools to develop a new CRM system for our financial agency, and the results have been outstanding. Their team quickly understood our needs and delivered a user-friendly solution that has transformed our client management process.The CRM provides a comprehensive view of our clients, enhances our communication, and streamlines our operations. We've seen a significant improvement in response times and overall efficiency. I highly recommend Computools for any software development needs!
Show more
Building AI-Powered Software That Delivers Results
Plavno is an AI-first software development company that helps businesses accelerate innovation through intelligent automation, AI assistants, and scalable digital platforms. With more than two decades of experience and hundreds of successful projects delivered, the company specializes in building advanced [... see all Plavno reviews ]- Location
- Warsaw, Poland
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 25 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsPlavno Services
- Mobile App Development
- Web Development
- eCommerce Development
- Blockchain
- Software Development
- IT Services
- AI Development
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
IT Outsourcing Project CRM and Marketplace -thumb-webp.webp)
IT Outsourcing Project Fleet management system
Data sourced from the agency's DesignRush profileMercedes Xerox Kia Amazon eBay PayPal IBM MediaCube
Reviews verified by DesignRush and sourced from the agency's profilePlavno Reviews & Testimonials
.png) Alexander Nikolaevsky CEO at Whitebird5.0★
Alexander Nikolaevsky CEO at Whitebird5.0★Web Development Review from Alexander Nikolaevsky
We have hired the Plavno team to develop a cryptocurrency exchange solution.allow users to make cryptocurrency transactions legally and transparently. Plavno team had to create a solution independent of third-party developers, develop frontend solutions for clients and service administrators, build a full-featured back-end that would include integration with banking and payment systems, and a multifunction module for managing currency exchange transactions, exchange rates.
Show more.png) Mitya Smusin CEO at Yellow Systems5.0★
Mitya Smusin CEO at Yellow Systems5.0★Financial Review from Mitya Smusin
Some problems can only be solved with code, but others require end-user thinking. So Plavno developers remember that the whole goal is to solve problems — not only to write code. They thought about the problem from the restaurantants point of view.They developed a food delivery app with both customer and admim panels, which covers all the necessary functionality.
Show more Yana Romanovskaya Product Manager at Beeline5.0★
Yana Romanovskaya Product Manager at Beeline5.0★IT Outsourcing Review from Yana Romanovskaya
Plavno was creating profiles with pulling up a lot of information (clusters). Xunit-based scoring was used when setting up a .NET 2.0 project. Scoring for this format works similarly to Junit. The team extended the products by adding features, fixing bugs. This development can change cluster parameters, cluster management system (current state of the object), customize vectors that lead to this cluster and make predictions.
Show more
Dedicated Teams That Build Complex Software Systems
Founded in 2012, SiliconMint delivers cybersecurity through static and dynamic code analysis, secure product architecture, vulnerability testing, and data encryption. Trusted by Verizon and the Royal Bank of Scotland, the firm brings enterprise-grade security to fintech, banking, and telecom. [... see all SiliconMint reviews ]- Location
- San Francisco, California
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $55/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 7 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSiliconMint Services
- Software Development
- Mobile App Development
- IoT
- AI Development
- Cybersecurity
- Blockchain
- VR/AR
- Big Data Analytics
- IT Services
- Cloud Consulting
Data sourced from the agency's DesignRush profileVerizon Yahoo Japan NASDAQ NYSE Goldman Sachs Barclays BCG Wargaming,net AA orange
Reviews verified by DesignRush and sourced from the agency's profileSiliconMint Reviews & Testimonials
 Leon Hounshell CTO, Verizon5.0★
Leon Hounshell CTO, Verizon5.0★Software Development Review from Leon Hounshell
Using SiliconMint’s AI engine and their engineering team was a great decision for us. They built the core foundation of our ThingSpace IoT platform on time and within budget, helping us serve millions of customers across the country. I would highly recommend the SiliconMint team for their drive and dedication to the art of software architecture and development.
Show more Leonid Zhukov Partner and Associate Director at Boston Consulting Group (BCG)5.0★
Leonid Zhukov Partner and Associate Director at Boston Consulting Group (BCG)5.0★Software Development Review from Leonid Zhukov
I’m always impressed by the technical depth & breadth of SiliconMint’s engineering team and the passion they bring to our projects. We’ve worked with them on distributed systems, data science projects, and a predictive maintenance system for the oil and gas sector. Every time, they blew me away with their experience, passion, energy, and the overall dedication for how they approach software engineering and delivery.
Show more Steve Grice Head of Technology Global Transaction Services at Royal Bank of Scotland5.0★
Steve Grice Head of Technology Global Transaction Services at Royal Bank of Scotland5.0★Cybersecurity Review from Steve Grice
SiliconMint built a real-time fraud detection system for us in a record period of time, with precision and recall that rivals the best in the industry. I was pleasantly impressed by their passion, dedication, and attention to detail in how they approached software development, driving excellence and speed within our organisation.
Show more
Solving complex problems with design and technology since 2005.
Accredited by NCSC and CREST, Infinum offers end-to-end security, including penetration testing, red teaming, and GRC. It is led by a team of 390+ consultants who hold CISSP, OSCP, and CHECK certifications and hands-on experience in banking, healthcare, and national defense. [... see all Infinum reviews ]- Location
- Zagreb, Croatia
- Number of Employees
- 250 - 499
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 24 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsInfinum Services
- Web Development
- Web Design
- Mobile App Development
- UI/UX Design
- Software Development
- Cloud Consulting
- DevOps Consulting
- Cybersecurity
- Staff Augmentation
- IoT
Data sourced from the agency's DesignRush profilePorsche Nike CITI Royal Caribbean Philips Bayer T-Mobile P&G Universal Virgin Mobile
Reviews verified by DesignRush and sourced from the agency's profileInfinum Reviews & Testimonials
 Matic Debelak Management Board Member at Modra zavarovalnica, d.d.5.0★
Matic Debelak Management Board Member at Modra zavarovalnica, d.d.5.0★Mobile App Development Review from Matic Debelak
Workstream 1: research and product strategyWorkstream 2: ETP release Technology : Vendor use Flutter framework, which allows one programming language and one codebase to create two different apps (for iOS and Android). Clearly defined roles and responsibilities, communication is clearly and respectfully, very effective project methodology, trying to understand every time how their activities fits into mission of Modra zavarovalnica, respect each member of team, etc.
Show more Claus-Peter Mueller Managing Director at NLB Lease&GO doo5.0★
Claus-Peter Mueller Managing Director at NLB Lease&GO doo5.0★Software Development Review from Claus-Peter Mueller
We have engaged Infinum to develop an app that would digitalise our leasing process. From creating the initial offer through the necessary financing application and client identification to the final signature – all the steps required to successfully lease a vehicle or other object can be performed in-app, freeing the users of friction and having to deal with tedious paperwork.The app itself in the background has 30+ integrations, while keeping a seamless and quick to follow process on the front for our users. That application is in production and Infinum is responsible for maintaining it and further improving. After the initial development, we have additionally expanded our scope from vehicles to other equipment. They have also developed a Leasing widget, product which enables quick financing model while purchasing a vehicle online on car seller marketplace pages. At this moment, we are still in partnership with Infinum, and their engagement is mainly focused on localising the app to other countries and supporting us in our further business expansion. The work performed was done in Ruby on Rails and React technology, with support of other services.
Show more- Anonymous VP of Marketing at SaaS Company5.0★
Web Design Review from Anonymous
Thanks to Infinum's website refresh, the client has seen an almost 100% improvement in their website's conversion rates. The team excels at project management, using the client's own proprietary tool and also Figma very well. Their proficiency in design, delivery, and client relations stands out.
Show more
Award-Winning IT & Cybersecurity
TruAdvantage delivers managed cybersecurity to SMBs and healthcare organizations through a 24/7 staffed SOC, Zero Trust network access, MDR, and SIEM log monitoring. Providing comprehensive cybersecurity since 2001, it is best for businesses needing enterprise-grade security without an in-house team. [... see all TruAdvantage reviews ]- Location
- San Jose, California
- Number of Employees
- Under 49
- Average Hourly Rate
- $165/hr
- Portfolios Count
- 8 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsTruAdvantage Services
- Managed Services
- Cybersecurity
- IT Services
- Staff Augmentation
- Business Consulting
- Cloud Consulting
- IT Compliance Solution
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio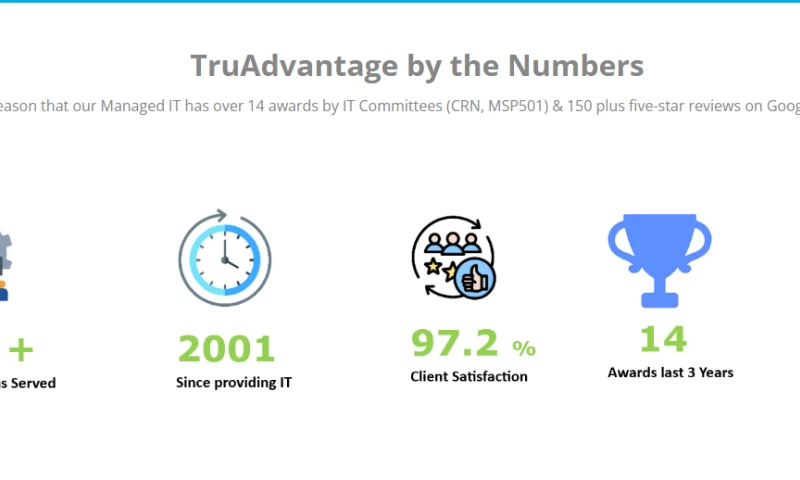
Cybersecurity Project TruAdvantage by the Numbers 
Cybersecurity Project Managed IT & Cybersecurity 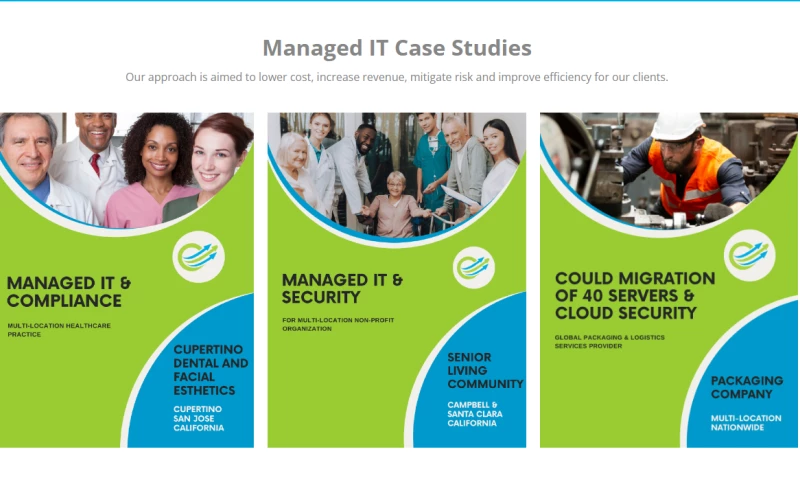
IT Services Project Managed IT Case Studies 
Managed Service Providers Project Awards and Meet the Team 
IT Services Project Watch Our Clients Success Stories 
Managed Service Providers Project Managed IT, Cybersecurity & Compliance
Data sourced from the agency's DesignRush profileMinimally Invasive Surgical Solutions (MISS) Santa Clara Methodist Retirement Foundation (SCMRF Kern Radiology
Reviews verified by DesignRush and sourced from the agency's profileTruAdvantage Reviews & Testimonials
.png) Rhosel Dayrit Practice Administrator at Neurospine Institute Medical Group5.0★
Rhosel Dayrit Practice Administrator at Neurospine Institute Medical Group5.0★IT Services Review from Rhosel Dayrit
My top 3 things about TruAdvantage:1) The single biggest benefit is Security. Since we are a medical field office, our primary concern is securing patient’s files and account information. Second would be backup. Since most of our work is online it is important to have back up on all files electronic and non-electronic.2) Customer service is excellent and dealing with our issue at a moment’s notice is beyond expectation.3) I would highly recommend for them to try it out. they will see a big difference in the proficiency of work, the team itself and the care to their customer’s need.
Show more.png) Mohammad Shenasa Executive and Cardiovascular Specialist at Southbay Cardio Vascular Group5.0★
Mohammad Shenasa Executive and Cardiovascular Specialist at Southbay Cardio Vascular Group5.0★IT Services Review from Mohammad Shenasa
Switching from our previous IT vendor to TruAdvantage seemed like a daunting process but TruAdvantage addressed this concern from our initial meeting and made it very smooth. Four years later and I can assertively say choosing TruAdvantage has been one of my best business decisions.
Show more.png) Joseph Dunn CEO at EndogenX5.0★
Joseph Dunn CEO at EndogenX5.0★IT Services Review from Joseph Dunn
Before TruAdvantage as our IT advisor, my staff used to spend way too much time on IT issues. Now with their support and process my staff is way more prod120uctive and is back to the business of research and inventing great pharmaceutical products.
Show more
DICEUS Driving Innovation in Insurance Technology
DICEUS is a product-led technology company delivering next-generation insurance software solutions, system integration, and product engineering services. Since 2011, weve empowered insurers and brokers to enhance operational efficiency, automate core processes, and elevate customer experiences. [... see all DICEUS reviews ]- Location
- Wilmington, Delaware
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $45/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 16 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsDICEUS Services
- Software Development
- Mobile App Development
- IT Services
- Web Development
- Big Data Analytics
- Staff Augmentation
- Cloud Consulting
- DevOps Consulting
- Blockchain
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
System Integrator Project Integration and Optimization of the Core CRM
Data sourced from the agency's DesignRush profileUNIQA Bank al Etihad Raiffeisen Bank Willis Towers Watson Fadata BriteCore Insider Palmers Bridgestone Verisense
Reviews verified by DesignRush and sourced from the agency's profileDICEUS Reviews & Testimonials
 Phil Reynolds CEO at BriteCore5.0★
Phil Reynolds CEO at BriteCore5.0★Software Development Review from Phil Reynolds
The DICEUS team has consistently supported the BriteCore team for many years. Their engineers are well-educated and highly invested in the ongoing quality of the BriteCore platform with sustained relationships that extend over four years. We appreciate everything the DICEUS team brings to the table as a development partner.
Show more Antoaneta Karagyozova CPSO at Fadata5.0★
Antoaneta Karagyozova CPSO at Fadata5.0★Software Development Review from Antoaneta Karagyozova
We are happy with DICEUS' software implementation services. The team's workflow is highly effective and professional in all aspects of the engagement. All clearly understand what goals we'd like to reach and do their best to do that as efficiently as possible. Overall, the partnership has been successful.
Show more Игорь Крищук Head of installation service at Lanet5.0★
Игорь Крищук Head of installation service at Lanet5.0★Android Review from Игорь Крищук
Our company ordered the development of an Android application, which should provide installers working with subscribers with complete information that is needed to perform Internet connections, service repairs, and much more.The implementation of the project was done in 4 parts, and the full implementation took 14 months.I was personally impressed by the fact that each part was completed on time, and there were very few defects and they were quickly corrected.
Show more
Web-development labolatory
Abyron is a close-knit team of developers whose main values are attention to employees, honesty with clients and transparency of processes. [... see all Abyron reviews ]- Location
- Białystok, Poland
- Number of Employees
- Under 49
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 53 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsAbyron Services
- Web Design
- UI/UX Design
- eCommerce Development
- Web Development
- Staff Augmentation
- IT Services
- CRM Consulting
- ERP Consulting
- Managed Services
Data sourced from the agency's DesignRush profileVisbook Your Sky Jets Jimber EcoVadis Wyld Technologies TK Digital Carebits AZBELPOL
Reviews verified by DesignRush and sourced from the agency's profileAbyron Reviews & Testimonials
 Anastasiya Rabtsevich Founder at Your Sky Jets5.0★
Anastasiya Rabtsevich Founder at Your Sky Jets5.0★Web Development Review from Anastasiya Rabtsevich
The experience of working with Abyron has been wonderful. Their team of accomplished experts is committed to provide the best possible service and assistance. They are not simply knowledgeable in their respective fields. They took the effort to fully understand our particular requirements and produced a customised solution that beyond our expectations. I can't say enough good things about entire team for any company looking for innovative solutions and excellent customer service.
Show more Yauhen Razhko CEO at Hypetrain5.0★
Yauhen Razhko CEO at Hypetrain5.0★Web Development Review from Yauhen Razhko
I worked directly with one of the Abyron team members, dedicated to my business needs. In general, I am satisfied with his work done for me. Almost all suggestions and ideas from my side were implemented, for those which were difficult to implement we looking for appropriate solutions together. Thanks for your help and great technical expertise.
Show more Alex Valadzko CEO at JayDevs5.0★
Alex Valadzko CEO at JayDevs5.0★Web Development Review from Alex Valadzko
Abyron has contributed significant process value. Their ability to identify and circumvent potential roadblocks has resulted in steady development progress. Customers can expect regular updates and thorough, high-quality app testing.
Show more
Your Product Engineering & Gen AI Partner
Simform is a premier product engineering services company specializing in Cloud/MACH architectures, DevOps automation, Data Engineering, Generative AI and Machine Learning to create seamless digital experiences and scalable products. [... see all Simform reviews ]- Location
- Orlando, Florida
- Number of Employees
- 1000 & Up
- Average Hourly Rate
- $30/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 8 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSimform Services
- Software Development
- Cloud Consulting
- AI Development
- Big Data Analytics
- DevOps Consulting
- IoT
- eCommerce Development
- UI/UX Design
- IT Services
- Managed Services
Data sourced from the agency's DesignRush profileSony Music (EMI) Pepsico Zep Inc Intralinks Nxt-ID FreeWire Inc Accent Inc Mission Rabies DoggyBnB Drizzle Labs
Reviews verified by DesignRush and sourced from the agency's profileSimform Reviews & Testimonials
 Andrew Muroff CEO at Strainprint Technologies Ltd.5.0★
Andrew Muroff CEO at Strainprint Technologies Ltd.5.0★Software Development Review from Andrew Muroff
We worked with Simform for many years ongoing software development on our core product, the Strainprint mobile outcomes tracker for medical cannabis patients. We have only positive things to say about their work product and attention to detail. We highly recommend them and will work with them again.
Show more Robel Yemane Head of Engineering at Privilee5.0★
Robel Yemane Head of Engineering at Privilee5.0★Software Development Review from Robel Yemane
I've been working with Simform for over six months now. The engagement began with bringing our subscription management platform in-house, and we've since expanded the partnership to other projects due to their broad skill set and consistent reliability. They've gone the extra mileeven over weekends and public holidaysto help us move faster when needed. Communication and project management have been excellent, with any issues swiftly addressed. It genuinely felt like Simform was invested in our success. Having worked with similar firms throughout my career, I can confidently say Simform stands out and comes highly recommended.
Show more Russ Makhauri Front-End Engineer at Midas5.0★
Russ Makhauri Front-End Engineer at Midas5.0★Software Development Review from Russ Makhauri
We worked with Simform to hire a front-end engineer for our SaaS platform. The process was well-organized, and their team was professional, responsive, and efficient. They quickly identified a candidate who met our technical requirements and ensured a smooth onboarding process.Simforms communication and project management were strong throughout the engagement. They were proactive in addressing feedback and remained flexible in adapting to our needs. While there is some room for improvement in developer vetting and quality assurance, their overall service was excellent.For companies looking to scale their development teams efficiently, Simform is a reliable partner. Their structured approach, responsiveness, and commitment to client satisfaction make them a great choice. We would recommend them without hesitation.
Show more
Innovative, Reliable and Affordable
We build custom Software Solutions, Mobile Apps, Content Management Systems, Document Management Systems, Customer Relationship Management Systems (CRM), Enterprise Resource Planning (ERP), E-Commerce Software Development, Web Product Development, IT Consulting Services, Web Designing & Development. [... see all Hexagon IT Solutions reviews ]- Location
- Salt Lake City, Utah
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $45/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 5 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsHexagon IT Solutions Services
- Software Development
- Mobile App Development
- IT Services
- Web Development
- Product Design
- eCommerce Development
- ERP Consulting
- Digital Services
- CRM Consulting
- Web Design
Data sourced from the agency's DesignRush profileUtah Dental Association Morph2o Got Incite Cullsy Compliant Experts ZAMP HR Edifice Denver Air Connection ( Digital Marketing)
Reviews verified by DesignRush and sourced from the agency's profileHexagon IT Solutions Reviews & Testimonials
 Bart Cassidy Attorney at Manko, Gold, Katcher & Fox, LLP at MANKO | GOLD | KATCHER | FOX LLP5.0★
Bart Cassidy Attorney at Manko, Gold, Katcher & Fox, LLP at MANKO | GOLD | KATCHER | FOX LLP5.0★Web Development Review from Bart Cassidy
We are is satisfied with the engagement; Hexagon IT Solutions has delivered the web on time and within budget. The team excels in their communication and understanding of the requirements; they solve any issue that arises. Overall, they stand out for their quality work; customers can expect great service.
Show more Dominique Dujardin VP IT Shared Services Europe chez XPO Logistics Europe at XPO Logistics Europe5.0★
Dominique Dujardin VP IT Shared Services Europe chez XPO Logistics Europe at XPO Logistics Europe5.0★Software Development Review from Dominique Dujardin
The product was developed successfully and has been undergoing pilot usage. Hexagon IT Solutions managed the engagement effectively, delegating tasks and assignments between us and the team. They met timelines and communicated efficiently through Slack. Their resources also resolved bugs quickly.Hexagon makes it easy for people trying to develop software. Ultimately, Hexagon was and has been on the same page with us from the beginning. They knew exactly what we were looking for, and what we didn't want. Other software development firms jumped at us with marketing proposals, designers, and irrelevant business consulting. Hexagon IT Solutions took the time to understand who we are and offer us their services accordingly.
Show more Edona Haliti FOUNDER at Electric Mobility LLC5.0★
Edona Haliti FOUNDER at Electric Mobility LLC5.0★Software Development Review from Edona Haliti
Thanks to Hexagon IT Solutions work, we have witnessed an enhanced performance in our software and received positive feedback from end customers. They have communicated and responded promptly, ensuring an effective workflow. Their efficiency and timely delivery have been hallmarks of their work.Communication and Response time, and the execution. They have provided us with quality of work within the stipulated time. Their affordable rates are a cherry on the cake. It's difficult to find these kinds of perfect combinations.
Show more
Innovating Success Through Technology & Blockchain.
InvoZone applies AI-powered threat detection and human-led expertise across its cybersecurity services, including behavioral analytics, data encryption, and cloud security. With a team of 500+ developers across the USA, UK, Canada, and Australia, it has completed 300+ projects with a 97% success rate. [... see all InvoZone reviews ]- Location
- Pembroke Pines, Florida
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $45/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 28 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsInvoZone Services
- Mobile App Development
- Software Development
- eCommerce Development
- Blockchain
- AI Development
- UI/UX Design
- ERP Consulting
- DevOps Consulting
- VR/AR
- Cybersecurity
Data sourced from the agency's DesignRush profileStitch Kamoota Global Reader Homepie Column Anakeed Mart Meridio Stakester Shield Republic
Reviews verified by DesignRush and sourced from the agency's profileInvoZone Reviews & Testimonials
 Wiley Jones Co-Founder at Doss5.0★
Wiley Jones Co-Founder at Doss5.0★Mobile App Development Review from Wiley Jones
The app launched successfully six months ago and is now actively used by over 300employees. We got a very good response from the end users as well.
Show more Tessa Young Product Manager at Tiny Genius5.0★
Tessa Young Product Manager at Tiny Genius5.0★Mobile App Development Review from Tessa Young
Working with InvoZone for my web app development project was an awesome experience. Right from the beginning of our partnership, they made everything super easy to understand. Their commendable Project Managers carefully listened to whatever I wanted to add and kept notes of all my suggestions. They provided us with every feature we needed and gave us some interesting ideas as well. Throughout the duration of my project, I was pretty much in the loop with the project and knew what was happening with our product development. It was great to see how things were coming along, loved working with them and I see a long-term future of our partnership.
Show more Angelina Sophia Product Head at Custom Box Makers5.0★
Angelina Sophia Product Head at Custom Box Makers5.0★eCommerce Development Review from Angelina Sophia
We thank InvoZone for their prompt response. Their team built our packaging ecommerce store from scratch. Their developers seamlessly integrated additional features as well as helped our in-house team with fixing bugs and coding errors. All in all, their team worked swiftly and professionally, coming up with robust solutions for each blocker during the process. If anyone is looking to develop a ecommerce store, InvoZone provides exceptional services. So, go ahead and connect with them.
Show more
Exoft is a software house with a significant background in web and mobile development.
Since 2013, Exoft protects software across its full lifecycle: from security and penetration testing to AI-powered threat detection and IT infrastructure hardening. Delivering 150+ projects in healthcare, logistics, and finance, it offers businesses a security partner accountable for long-term outcomes. [... see all Exoft reviews ]- Location
- Lviv, Ukraine
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 14 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsExoft Services
- Software Development
- Web Development
- Software Testing
- Cybersecurity
- IT Services
- AI Development
- ERP Consulting
- Staff Augmentation
- Managed Services
- DevOps Consulting
Data sourced from the agency's DesignRush profileBridgestone PlugSurfing Eloquenti
Reviews verified by DesignRush and sourced from the agency's profileExoft Reviews & Testimonials
 David Veksler Principal Web Architect at Undisclosed4.5★
David Veksler Principal Web Architect at Undisclosed4.5★Educational Review from David Veksler
We are happy with the work. We worked with a number of developers, and when we were not happy with a developer, our Exoft contact worked to find someone to meet our needs.
Show more Colin Stone Developer at ANALEC Infotech Private Ltd5.0★
Colin Stone Developer at ANALEC Infotech Private Ltd5.0★Web Development Review from Colin Stone
Exoft bring strong engineering talent to bear on our projects. They are always willing to go the extra mile to meet our expectations.
Show more Boris Jinjolava CEO at ViClinic Inc4.8★
Boris Jinjolava CEO at ViClinic Inc4.8★Software Development Review from Boris Jinjolava
Exoft has successfully supported us to push our business forward. They bounce ideas off each other and give feedback and context to help in tech areas. Moreover, theyre approachable, responsive partners, and the team stands out for their expertise. It feels more like an internal team than an outsourcing relationship. thank you.
Show more
We provide efficient software solutions tailored to your business needs.
SmartTek Solutions is a software development company that delivers software products, biotech, managed IT outsourcing services, and solution engineering to world-renowned customers. [... see all Smart Tek SAS reviews ]- Location
- Austin, Texas
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 36 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSmart Tek SAS Services
- Web Design
- Software Development
- IT Services
- VR/AR
- Mobile App Development
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
IT Services Project for Manufacturing Company Bluesky Solutions 
IT Services Project for Transportation & Logistics Company Kinetic Sourcing Group 
IT Services Project for Software & IT Services Company Bryntum Gantt 
IT Services Project for eCommerce Company Jomla 
IT Services Project for eCommerce Company LUXLogic 
IT Services Project for Food and Beverage Company Soul Spice
Data sourced from the agency's DesignRush profileEducation Industry eCommerce Industry HealthCare Industry Manufacturing Industry Real Estate Industry Supplements Industry Hospitality Industry
Reviews verified by DesignRush and sourced from the agency's profileSmart Tek SAS Reviews & Testimonials
 Anna Suchard CEO at Sentro5.0★
Anna Suchard CEO at Sentro5.0★IT Services Review from Anna Suchard
[The] SmartTek team has provided experienced engineers to address issues and complete the platform on time. SmartTek Solutions has successfully built the website and solved all issues promptly, meeting [...] our expectations. The team keeps in touch with us to address their technical needs and foster a positive relationship. Overall, the specialists are easy to work with, skilled, and responsive. (Verified via email)
Show more Andrew Zarytskyy Project Manager at Spark Media4.8★
Andrew Zarytskyy Project Manager at Spark Media4.8★PHP Review from Andrew Zarytskyy
I sought out WordPress development services, and I must say, I am extremely satisfied with the results. [The] SmartTek team create[d] a website that exceeded my expectations in terms of design, functionality, and user experience. Throughout the entire process, [the] SmartTek team was professional and responsive. They kept me informed every step of the way and were always available to address any questions or concerns I had. I am thrilled with the results! (Verified via email)
Show more Marcus A Founder at Rhodium Labs5.0★
Marcus A Founder at Rhodium Labs5.0★Software Development Review from Marcus A
I initially had another software company that developed our website but it was done by junior developers. The project had many issues. Our company made the decision to hire a more experienced company that can handle a complex project. Hiring UkrInSofT was one of the best decisions we've made. They took the time to understand the project and deliver a fast and scalable website with all of our requirements. We've been working with them for 3 years now and will continue to do so for many years.
Show more
World-Class Software Development Company
Datazo InfoTech is an Award-Winning & World-Class Software Development Company with Engineering Hubs in NYC. We are committed to providing end-to-end IT services with a mission to solve complex software engineering problems. [... see all Datazo InfoTech reviews ]- Location
- Dhaka, Bangladesh
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $150/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 12 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsDatazo InfoTech Services
- IT Services
- Software Development
- AI Development
- eCommerce Development
- Web Development
- Blockchain
- Mobile App Development
- VR/AR
- IT Compliance Solution
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project for Social Networks Company Secure Mobile Messenger App Development 
Cybersecurity Project for Software & IT Services Company Migration Of Aes File security Software For Macos To Xamarin 
Cybersecurity Project for Finance Company Firewells For a As Consumer Reporting Agency -thumb-webp.webp)
IT Services Project for Finance Company SharePoint Consulting for a Financial Advisory Firm -thumb-webp.webp)
IT Services Project for Corporate Services Company IT Consulting for Enterprise Application Integration for a Multi-Industry Corporation
Data sourced from the agency's DesignRush profileFinancial Indutry IT Industry Small Buiness Industry
Reviews verified by DesignRush and sourced from the agency's profileDatazo InfoTech Reviews & Testimonials
 Bobby Neil Senior Director Global Services at Iron Mountain5.0★
Bobby Neil Senior Director Global Services at Iron Mountain5.0★Software Development Review from Bobby Neil
The redesign of our solution was warmly welcomed by the users that were involved in its beta-testing process. We appreciate efficient communication, quick reactions to suggestions and their Agile Scrum approach to project management and definitely the portfolio and skills of the designer that was working on our project! The prepared UI hit the point. Also, the engagement and quick introduction of all changes made working on a project much more productive and less challenging.
Show more Matthew Grant Vice President at Impact XM5.0★
Matthew Grant Vice President at Impact XM5.0★Software Development Review from Matthew Grant
The three major tools that our employees use daily are all connected via the same interface, which is a huge success. I also get a lot of anecdotal feedback from people about how fast and responsive the system is. Enhancements and features are being implemented very quickly, and people feel that theyre being heard by our team and Datazo. If we ask for something, then it will be delivered. They've been terrific in that respect.
Show more Eudis Anjos Head of Engineering at SS&C Technologies5.0★
Eudis Anjos Head of Engineering at SS&C Technologies5.0★Software Development Review from Eudis Anjos
Its difficult to measure success, since we had just launched the app last week. However, there are a number of people who have contacted us and were interested in having a meeting to know more. In that respect, weve achieved our main goal of calling the attention of mobile network operators and mobile money providers. Weve accomplished the level of success that we targeted for initially. Everyone was congratulating us for the UI/UX of the app and nobody came to us with any problems, which is a very good metric.
Show more
Digital Transformation | IT Consulting - We build your business brick by brick!
At Matrix Bricks, we fuse cutting-edge technology with creative innovation to elevate your business performance globally. [... see all Matrix Bricks reviews ]- Location
- Mumbai, India
- Number of Employees
- Under 49
- Average Hourly Rate
- $45/hr
- Minimal Budget
- Under $1,000
- Portfolios Count
- 54 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsMatrix Bricks Services
- Digital Services
- eCommerce Development
- SEO
- Digital Marketing
- Web Development
- Branding
- Reputation Management
- DevOps Consulting
- Managed Services
- IT Services
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio-thumb-webp.webp)
Hosting and cloud Project for Real Estate Company WTC Mumbai - Website Hosting Services
Data sourced from the agency's DesignRush profileCISWW Valyou Enlogic Gourmet House Word Trade Centre SEBI NCDEX Stock Holding Corporation Angel Broking Glenmark
Reviews verified by DesignRush and sourced from the agency's profileMatrix Bricks Reviews & Testimonials
 Suneet Luthra CEO at Facilon Services5.0★
Suneet Luthra CEO at Facilon Services5.0★Web App Review from Suneet Luthra
We've had an excellent experience working with Matrix Bricks as our technology partner. Their team is proactive, technically sound, and always ready to go the extra mile to deliver solutions that align with our goals. Their support has been instrumental in driving our digital transformation.
Show more Tim David Director of Sales Marketing at Data Marketers Group5.0★
Tim David Director of Sales Marketing at Data Marketers Group5.0★eCommerce Development Review from Tim David
The Matrix Bricks team helped us migrate a website from Drupal to Hubspot. They were responsible for utilizing the Hubspot CMS to create page templates, developing custom code, and migrating content. Matrix Bricks provided excellent project management, handling resources, meetings, invoices, and scheduling efficiently. Their communication was always prompt and clear. They were very easy to work with and seamlessly became an extension of our own team.
Show more Christina Delord Managing Director at TracPrac by Vestigo Health Solutions5.0★
Christina Delord Managing Director at TracPrac by Vestigo Health Solutions5.0★Web Development Review from Christina Delord
Matrix Bricks was responsible for pioneering a cutting-edge education management platform, featuring an AI-powered recommendation engine that set a new standard in the field. Their strategy combined advanced technology with education management, creating a personalized and engaging experience for learners. I thoroughly enjoyed working with the team. Matrix Bricks met all my expectations, and I was highly satisfied with the project's outcome. What stood out the most was their excellent communication and quick response times. The team demonstrated a high level of expertise and provided a seamless onboarding process.
Show more
Techforce Global: Your Catalyst for Seamless Solutions
Techforce Global: Your partner for government custom software development, React Native development and more. Offering comprehensive services across industries with a global presence and a focus on scalable, intelligent solutions. [... see all Techforce Global reviews ]- Location
- Naperville, Illinois
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $26/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 20 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsTechforce Global Services
- Software Development
- Web Development
- Mobile App Development
- IT Services
- Cloud Consulting
- DevOps Consulting
- Software Testing
- Staff Augmentation
- AI Development
- eCommerce Development
Data sourced from the agency's DesignRush profileConscisys Calidatech Apexx Global Freeway Token The Jazz Kitchen Soladefy The Rare Antiquities Grande Experiences Leven Token iensure
Reviews verified by DesignRush and sourced from the agency's profileTechforce Global Reviews & Testimonials
 Marc Bond None of your business at GDPR compliance1.0★
Marc Bond None of your business at GDPR compliance1.0★Legal Review from Marc Bond
This company is [...] ignoring UK GDPR rules. (Verified via email)
Show more Mark Webster Brand & Creative at Grande Experience5.0★
Mark Webster Brand & Creative at Grande Experience5.0★Web Development Review from Mark Webster
Techforce working on the transition of our website name from Grande Exhibitions to Grande Experiences. The project involved the creation of a clone website where we could apply the new brand and update all content to reflect the name change before pointing the new and old domains at this new site. At the projects commencement, all details were scoped out and clarified to ensure that everything went according to plan. Through the entire project, Bhavin and the Techforce Team were professional,
Show more Fanny Gotschall Creative Services Director at Fanny Gotschall Studios5.0★
Fanny Gotschall Creative Services Director at Fanny Gotschall Studios5.0★Web Development Review from Fanny Gotschall
Bhavin is brilliant, and the project's success is largely because of his personal involvement. Over recent months, Fanny Gotschall Studios collaborated with Bhavin in the role of art director for one of its top Midwest clients. While the client had a clear creative vision, Bhavin and his team at Techforce Global consistently executed it to perfection. For every scope change, Bhavin had the appropriate team and ensured all parties were aligned. (Verified via email)
Show more
Mobile & Web Software Dev Team
Kernelics is a boutique web and mobile software development firmfor startups and tech companies. [... see all Kernelics reviews ]- Location
- London, United Kingdom
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 18 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsKernelics Services
- Mobile App Development
- Staff Augmentation
- Product Design
- Software Development
- eCommerce Development
- IT Services
- Web Design
- Software Testing
- Web Development
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Staff Augmentation Project for Crypto Company SPORTS-FOCUSED BLOCKCHAIN APP 
IT Outsourcing Project for Real Estate Company APP FOR PROPERTY MANAGMENT 
Staff Augmentation Project for Real Estate Company REAL ESTATE WEB APP FOR NON-LISTED HOMES 
Staff Augmentation Project for AI Company AI-POWERED PERSONAL TRAINER 
IT Outsourcing Project for eCommerce Company E-COMMERCE MOBILE APP
Data sourced from the agency's DesignRush profileSmall Business Industry Fintech Industry Marketing Industry
Reviews verified by DesignRush and sourced from the agency's profileKernelics Reviews & Testimonials
 Dzmitry Novikau Co-Founder at Obsidian AI5.0★
Dzmitry Novikau Co-Founder at Obsidian AI5.0★Staff Augmentation Review from Dzmitry Novikau
I worked with Kernelics on a crypto project where we needed help with both design and development. From the beginning, the team was easy to communicate with and clearly understood what we were trying to build.The designer improved our initial ideas by making the user experience more intuitive. They suggested better ways to structure the navigation and user flow, which helped reduce friction and made the product easier to use.We also brought in one of their developers, who worked alongside our existing team member. They collaborated well, completed the work on time, and handled some challenging parts of the exchange functionality without any issues.Overall, Kernelics delivered quality work, stayed within budget, and were professional throughout the process. I’d recommend them to others looking for a reliable design and development partner, especially for crypto or fintech projects.
Show more Stsiapan Kolesau CEO at Module Technology5.0★
Stsiapan Kolesau CEO at Module Technology5.0★Web Development Review from Stsiapan Kolesau
I CEO at the construction company specializing in modular buildings and their components. With years of experience and multiple projects, we decided to expand our online presence beyond our two existing landing pages. We needed a corporate portal to showcase products, manage content easily, and dynamically calculate product costs.On a recommendation, we chose Kernelics, and their organized approach and clear task division impressed us from the start. They began with an in-depth analysis of our needs and a competitive review. For the design, we requested a minimalist style, and the results were spot on, requiring only minor tweaks to meet our expectations.For development, Kernelics selected React, Next.js, and TypeScript, with Strapi for the admin panel. They also integrated Google Sheets to handle dynamic price calculations, enabling instant updates on the site by simply modifying the spreadsheeta feature weve found incredibly useful.Now, two years later, the portal continues to support our growth, and were planning new developments for our main site.Kernelics stood out for their transparent approach and professionalism at every stage, and I confidently recommend them to anyone seeking a reliable web development partner.
Show more
Your helping hand in software quality
a1qa, a global pure-play QA and test automation provider, brings over 20 years of expertise in delivering quality assurance and software testing services. The organization adjusts its workflows to comply with ISO 9001/27001 standards. [... see all A1qa reviews ]- Location
- Decatur, Georgia
- Number of Employees
- 1000 & Up
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 16 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsa1qa Services
- Software Testing
- Managed Services
- IT Services
- Staff Augmentation
Data sourced from the agency's DesignRush profileAdidas Pearson SAP Acronis Expedia
Reviews verified by DesignRush and sourced from the agency's profilea1qa Reviews & Testimonials
- Anonymous Chief Engineering Officer at Confidential5.0★
Applications Review from Anonymous
Working with A1QA has been exceptional since the very beginning. Their professionalism, efficiency, and quality of work often exceed what we’ve seen from much larger providers. From the early planning stages through test execution and continuous improvements, the team has shown strong expertise and maintained clear, reliable communication. Their dedicated focus on QA has given us an experienced group that manages the entire process with little need for oversight on our side. They are true experts in their field.
Show more  Undisclosed Research and Development Manager at IT Company5.0★
Undisclosed Research and Development Manager at IT Company5.0★Software Testing Review from Undisclosed
Highly qualified staff and quick search for new employees. The outstaffed guys have high technical expertise and are well-versed in the latest technologies. My overall experience with the service has been positive. Their guys have integrated well with our in-house staff and contributed significantly to projects.
Show more Rick Fox QA Lead at Bally's Interactive5.0★
Rick Fox QA Lead at Bally's Interactive5.0★Software Testing Review from Rick Fox
The team's clear communication and hardworking nature made them easy to work with. Tasks included writing and managing test cases and conducting various QA tests, such as feature acceptance and regression testing. Worked alongside internal teams to ensure we tested the priority each Day & Week of the project. Issues raised communicated out so any blockers were prioritised appropriately.
Show more
Recommended by 96% CEO, CTO and COO Globally
At SPEC INDIA, we are Empowering businesses with AI in the digital world. With more the 36+ years of experience in the tech space we have been delivering bespoke software solution that power businesses worldwide. Our commitment and assurance of quality makes us stand out in the market.. [... see all SPEC INDIA reviews ]- Location
- Ahmedabad, India
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 54 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSPEC INDIA Services
- Software Development
- Mobile App Development
- Web Development
- UI/UX Design
- Software Testing
- CRM Consulting
- Cloud Consulting
- IT Services
- ERP Consulting
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio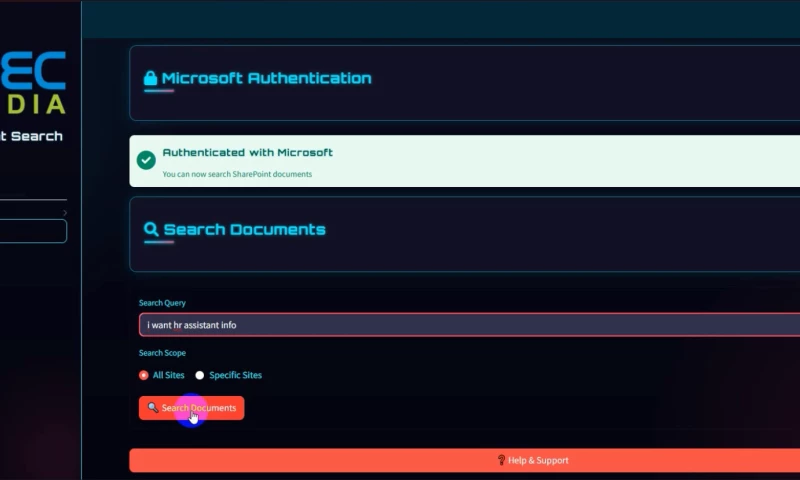
Software Evaluation Project AI-Powered Document Search & Chat
Data sourced from the agency's DesignRush profilePharmacor REMAX Fursan AstraZeneca TOTSA HITACHI UCSF Schneider Loreal PEPSICO
Reviews verified by DesignRush and sourced from the agency's profileSPEC INDIA Reviews & Testimonials
 Cas Diependaal Head of Platform at Zeals4.8★
Cas Diependaal Head of Platform at Zeals4.8★Software Testing Review from Cas Diependaal
Through SPEC India we've hired a QA automation specialist who has helped us set up testing automation for our software. The service was professional, friendly and well executed. It was a smooth experience to hire a resource and assign it to the tasks we needed them to perform.
Show more Ron Eliot Dichter Founder & CEO at SIXPAC4.3★
Ron Eliot Dichter Founder & CEO at SIXPAC4.3★Software Development Review from Ron Eliot Dichter
Spec has been a good partner to work with for my project. They're responsive and nimble. They provide good feedback and creative suggestions for solving challenges and building the features. I've appreciated their collaboration while working on my software.
Show more- Keshav Lohiya CEO at Oilytics Ltd5.0★
Dashboard Design Review from Keshav Lohiya
We have been very happy with the support we have received for the last 2 years. Spec India helps small businesses like ours to remain agile, competitive and stay at the forefront of technological innovation.
Show more
Managed IT Support & Consulting Services Company
Working with nonprofits, government agencies, and SMEs since 1997, Rivell’s cybersecurity expertise spans threat detection, network security, and cloud protection. The leading cybersecurity company provides proactive 24/7 monitoring and support with a local focus. [... see all Rivell reviews ]- Location
- Mantua Township, New Jersey
- Number of Employees
- Under 49
- Average Hourly Rate
- $40/hr
- Portfolios Count
- 4 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsRivell Services
- IT Services
- Cloud Consulting
- Cybersecurity
- Managed Services
- Software Development
- IT Compliance Solution
- Mobile App Development
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Managed Service Providers Project Managed IT Services For LISCIOS BAKERY 
Managed Service Providers Project Managed IT Services For BUTTACI LEARDI & WERNER 
Managed Service Providers Project What our clients say about us 
Managed Service Providers Project Project with Law firm
Data sourced from the agency's DesignRush profileIT Industry Film Industry Education Industry Healthcare Small Businesses State and Local Government Law Firms Non - Profits Fintech Retail
Reviews verified by DesignRush and sourced from the agency's profileRivell Reviews & Testimonials
 Hamed Sadeghian CEO at Nearfield instrument5.0★
Hamed Sadeghian CEO at Nearfield instrument5.0★Mobile App Development Review from Hamed Sadeghian
Our world's first linked carsharing marketplace has been made possible in large part by the technical expertise and inventiveness of their team. Rivell not only met but surpassed our expectations by providing a mobile app that is easy to use and flawlessly integrated, enabling individuals to carpool anywhere. With open communication, prompt delivery, and a sincere commitment to our goal, our cooperation with Rivell has shown to be a useful one.
Show more Giorgio Tinacci CEO at Casavo5.0★
Giorgio Tinacci CEO at Casavo5.0★Cybersecurity Review from Giorgio Tinacci
It was a pleasure working with Rivell on the internet testing automation for our real estate services company. The organization developed a strong system to effectively handle quality assurance (QA) by offering both manual testing and test automation. Thanks to Rivell's proactive and adaptable attitude, the deployment of a new portal was made possible by its smooth integration into our Agile process. The agency's professionalism and level of experience pleased us.
Show more Hank Sorensen CEO at iad florida5.0★
Hank Sorensen CEO at iad florida5.0★IT Services Review from Hank Sorensen
Our organization hired Rivell developers and a project manager to provide IT services for assisting IAD Florida in locating accommodation. During the project, there was close collaboration between our team and Rivell. Initially, both teams worked together to plan the construction of the product and gather required project data. Subsequently, their team added features to our software. Finally, after successful launch, our client expressed satisfaction with the outcome. This collaboration appears to have been effective in achieving the project's goals.
Show more
A Reliable Full-Service Software Development, Cloud, DevOps and QA Partner
Leveraging 30 years of excellence designing, developing, deploying and supporting world-class software solutions, Kanda Software has established itself as a trusted Software Development, Cloud Engineering, DevOps and QA partner for companies ranging from innovative startups to large enterprises. [... see all Kanda Software reviews ]- Location
- Boston, Massachusetts
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 16 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsKanda Software Services
- Software Development
- Mobile App Development
- IT Services
- IoT
- VR/AR
- UI/UX Design
- Staff Augmentation
- Business Consulting
- ERP Consulting
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio-thumb-webp.webp)
AWS Project Facilitating the Migration to AWS Cloud with a Focus on High Performance and Full HIPAA Compliance
Data sourced from the agency's DesignRush profileOneSky Rue La La imprivata Lionbridge CBRE Havas Media College Interactive KAUST Nuance Association of Computing Machinery
Reviews verified by DesignRush and sourced from the agency's profileKanda Software Reviews & Testimonials
 Alex Koifman President at RJCF5.0★
Alex Koifman President at RJCF5.0★Software Development Review from Alex Koifman
I've used Kanda's services for years. They're reliable and their work is of high quality. I'd recommend them to anyone looking for a partner in software engineering initiatives.
Show more Andrew Duggan CEO at medQue5.0★
Andrew Duggan CEO at medQue5.0★Mobile App Development Review from Andrew Duggan
Kanda proved to be an exceptional choice for our development needs. They were much more [of] a partner to our startup than a vendor. The entire team treated our project like it was their own company, and the results showed that. Our customers were extremely please[d] with the desktop and mobile applications. I would definitely recommend hiring Kanda for any and all of your development needs. (Verified via email)
Show more Alan Bugos Head of Technology at LifePod Solutions4.8★
Alan Bugos Head of Technology at LifePod Solutions4.8★Software Development Review from Alan Bugos
We have worked with Kanda Software for over two years and [are] very please[d] with the quality of work, cost-effective approach in resourcing team members, and the expertise they bring to solving very complex development challenges. Overall, we are very happy with Kanda's team! (Verified via email)
Show more
Building Software with Integrity and Impact
KeenEthics is a long-term software development partner supporting clients from early AI prototypes to no-code apps, fully custom solutions. [... see all KeenEthics reviews ]- Location
- Tallinn, Estonia
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 6 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsKeenEthics Services
- Web Development
- Software Development
- Mobile App Development
- Web Design
- UI/UX Design
- IT Services
- Staff Augmentation
- Software Testing
- AI Development
Data sourced from the agency's DesignRush profileReal Estate Industry Education Industry Agriculture Industry Non Profit Industry Publishing Industry
Reviews verified by DesignRush and sourced from the agency's profileKeenEthics Reviews & Testimonials
 Mike Spear CEO at Altruous5.0★
Mike Spear CEO at Altruous5.0★Software Development Review from Mike Spear
The KeenEthics team is great! Very talented and responsive. For startups and mid-sized companies that need outsourced design and development support, you really can't ask for better!
Show more Khrystyna Sliana Digital marketing manager at Red Jumpers5.0★
Khrystyna Sliana Digital marketing manager at Red Jumpers5.0★Web Development Review from Khrystyna Sliana
We collaborated with this company while supporting our client with a request focused on a TypeScript, Node.js, and Angular stack.After engaging them through our partner network, they quickly shared a strong candidate who turned out to be an excellent match for the clients needs. The developer demonstrated solid technical expertise and professionalism throughout the entire engagement, which was highly appreciated by both our team and the end client.At the beginning of the collaboration, there was a need to adjust the developers working schedule. Keenethics handled this situation very efficiently, resolving it within a few days and ensuring full 8-hour availability. Their responsiveness and problem-solving approach made a strong positive impression.We are very satisfied with both the quality of the specialist provided and the company's ability to react quickly and effectively to operational challenges.
Show more Kostiantyn Marchuk CEO at gFit4.8★
Kostiantyn Marchuk CEO at gFit4.8★Next.js Review from Kostiantyn Marchuk
We collaborated with KeenEthics to develop our gFit app using the Next.js stack. As the CEO of a Health & Wellness startup, I especially value two things: code quality and meeting deadlines. The KeenEthics team delivered perfectly on both counts.The communication process is transparent; the team was always available and reacted promptly to feedback. The quality of work is top-tier. While their services aren't the cheapest (hence the 4 stars for cost), the result and the peace of mind they provide are well worth it. I definitely recommend them as a reliable technological partner.
Show more
SoloWay - your sustainable digital transformation companion!
Custom Software Development. SoloWay Technologies is an international technology company focused on digital business transformation, solving global challenges, and bringing big ideas to life. [... see all SoloWay Technologies reviews ]- Location
- Ivano-Frankivsk, Ukraine
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $30/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 33 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSoloWay Technologies Services
- Software Development
- Mobile App Development
- Web Development
- Web Design
- eCommerce Development
- Product Design
- WordPress Website Design
- IT Services
- Staff Augmentation
- Software Testing
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio-thumb-webp.webp)
Staff Augmentation Project Veer - Development Staff Augmentation for SaaS Company
Data sourced from the agency's DesignRush profileLibresse Netpeak SOCAR Energy Chain Broker VEER Gastroli.ua MOYO Concert.ua PROPY Adamson
Reviews verified by DesignRush and sourced from the agency's profileSoloWay Technologies Reviews & Testimonials
 Yana Okushko Growth Manager at DreamX5.0★
Yana Okushko Growth Manager at DreamX5.0★Software Development Review from Yana Okushko
We partnered with SoloWay Technologies to build a comprehensive solution for real estate inspections and property management in the US market. The project involved developing a mobile application and CMS web portal to help inspectors capture property data, estimate renovation costs, and calculate potential resale profits.From the very beginning, SoloWay demonstrated a strong understanding of industry-specific workflows and effectively translated them into an intuitive and efficient digital product. Their team was proactive and highly collaborative, maintaining regular communication through virtual meetings and messaging platforms. We appreciated their ability to remain flexible and responsive as our business needs evolved throughout the project.The mobile application allows inspectors to take and upload hundreds of photos, input detailed property information, and sync everything to the cloud, even when working offline. Meanwhile, the web portal enables managers to review, organize, and manage all the incoming data in one place. SoloWay also delivered a lightweight version of the app tailored for limited use cases, adding to the systems versatility.What impressed us most was their dedication to solving complex technical challenges, such as handling large volumes of multimedia content and implementing offline functionality - all while ensuring the platform remained user-friendly and efficient. Their project management was solid: deadlines were met, deliverables were of high quality, and updates were transparent.Overall, were extremely satisfied with the partnership. SoloWay Technologies has proven to be a reliable and forward-thinking development partner, and we highly recommend them to any company seeking custom software solutions with real impact.
Show more- Ross Shevchenko Review from Google5.0★
Ross Shevchenko's Review Sourced from Google
Friendly, close-knit, straightforward team of professionals. I can recommend it to both clients and as a place to work. Although I myself moved on, my decision was dictated by the desire to open my own business. I can only leave a grateful review about the company and the people in it
Show more - Zoriana Kalinenko Review from Google5.0★
Zoriana Kalinenko's Review Sourced from Google
They say about them: "Professionals with a capital letter." An incredible atmosphere and a team that leaves a pleasant aftertaste in any business.
Show more
Leading the AI Revolution in Healthcare & Enterprise Solutions
Next-Generation AI Development Company - Transforming Ideas into Intelligent RealityDreamSoft4u is pioneering the future of AI-powered software development with cutting-edge Generative AI solutions that deliver measurable business impact. [... see all Dreamsoft4u reviews ]- Location
- Corona, California
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 18 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsDreamsoft4u Services
- Software Development
- Mobile App Development
- Web Development
- IoT
- AI Development
- Staff Augmentation
- IT Services
- UI/UX Design
- Cloud Consulting
- DevOps Consulting
Data sourced from the agency's DesignRush profileWebeDoctor inTouchEMR IcareIntelligence SONDE BetterMind Oncolence CareHalo ChiroSpring MEDSAYS
Reviews verified by DesignRush and sourced from the agency's profileDreamsoft4u Reviews & Testimonials
 Adil Abbas CEO at Alacrity5.0★
Adil Abbas CEO at Alacrity5.0★eCommerce Review from Adil Abbas
We were not looking for one specific task to be done. We hired Dreamsoft4u for many different tasks. For our existing platform, some features were to be added. This was one task. Next, we wanted to build our own e-commerce platform for our own products with a crypto-checkout feature. Next, we also wanted to build a prediction platform. Among all the requirements that we had, our major requirement was the e-commerce platform that we needed for our own products. Also, we needed a crypto checkout platform for the same. The design is very minimalistic. Thus, giving a very user-friendly experience. The product will show its USD price and during the checkout, its crypto price will be shown. We have also added some new features to our existing platform. We were able to host the website successfully. The whole project, despite so many things to be done, went smoothly. It was a completely hassle-free experience. The team worked in coordination. We had to stand up calls on a daily basis to discuss the upgrades, improvements and progress. The team at Dreamsoft4u is very flexible to work with. So far, we have not felt the need for any sort of improvement for Dreamsoft4u.
Show more Dipanjan Chatterjee CEO at Bevvi5.0★
Dipanjan Chatterjee CEO at Bevvi5.0★Mobile App Development Review from Dipanjan Chatterjee
We hired Dreamsoft4u to rapidly build an on demand liquor delivery app - that also serves an alcohol marketplace, liquor store locator and a rare source to find alcohol. The product they developed is not just a stereotype on demand delivery mobile app but it is the best liquor store locator and a rare source to find alcohol. Our dream was to build a platform that caters to enterprise customers who are looking to procure alcohol online for events and special uses. We signed a contract with them to develop an on demand liquor delivery app for both Android and iOS platform. We want to build a product that serves as beer finder and alcohol tracker wherein users should be able to shop a wide selection of liquor from multiple local stores in one go. Further, they should also be able to compare prices, deals from the liquor stores nearby their location at fingertips. The most impressive thing about Dreamsoft4u was everything got designed and developed inhouse by experienced developers. We had rough draft of wireframes but they improved it with their designing and added the elements of branding and personality. The app got launched on App Store and Play Store. Since the launch of this version of the app, we have gotten all positive feedback. Not only users are admiring the app design but we are also experiencing good amount of downloads with high user retention. Cant find any areas for improvement , they have been fantastic throughout our journey.
Show more Toby Cosgrove CEO at Planoly5.0★
Toby Cosgrove CEO at Planoly5.0★IT Services Review from Toby Cosgrove
We realized that there is a direct correlation between Instagram posts and online sales of our product. Hence, we met Dreamsoft4u with our vision to create a visual planner for Instagram from a designers and editors point of view that boosts and protects any ecommerce brand. The task looks simple but to build such tool is indeed full of complexity and throws challenge. We started with a pleasant kick-off meeting with the account- and project manager to make sure all involved parties are on the same wavelength and inline with our vision. They provided Basecamp, JIRA, Notion, Figma as a collaboration tool for daily communication, questions and updates. Earlier we wanted to develop a planner but they advised us to go ahead with incorporating scheduling feature too which is like an icing on the cake. The product got launched before time and received pretty impressive feedback from our community. Hardly any other development companies can meet deadlines before due time and that too without compromising on quality and impacting on your pockets. Their technical team is active and goes deep into the solutions. The team possess high level of integrity and passion for quality delivery, The product they have developed is launched and we received pretty good response. The impressive facts about them are commitment to delivery, understanding of customer requirements, and quality of development. Cant find any areas for improvement, they have been awesome throughout our journey.
Show more
Managed I.T. Services & Cybersecurity Solutions Since 1994
LME Services has protected businesses since 1994, offering 24/7 SOC monitoring, MDR, SIEM, and compliance support across legal, accounting, and financial services. Trusted by clients including Spring Bank Wisconsin and HighRadius, the cybersecurity firm delivers enterprise-grade cybersecurity to businesses. [... see all LME Services reviews ]- Location
- Hoffman Estates, Illinois
- Number of Employees
- Under 49
- Average Hourly Rate
- $150/hr
- Portfolios Count
- 8 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsLME Services Services
- Managed Services
- IT Services
- Cybersecurity
- Cloud Consulting
- IT Compliance Solution
- Business Consulting
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project for Health Care Company Cybersecurity Implementation 
Cybersecurity Project for Real Estate Company Cybersecurity Implementation 
Cybersecurity Project for Corporate Services Company SOC2 Compliance Project 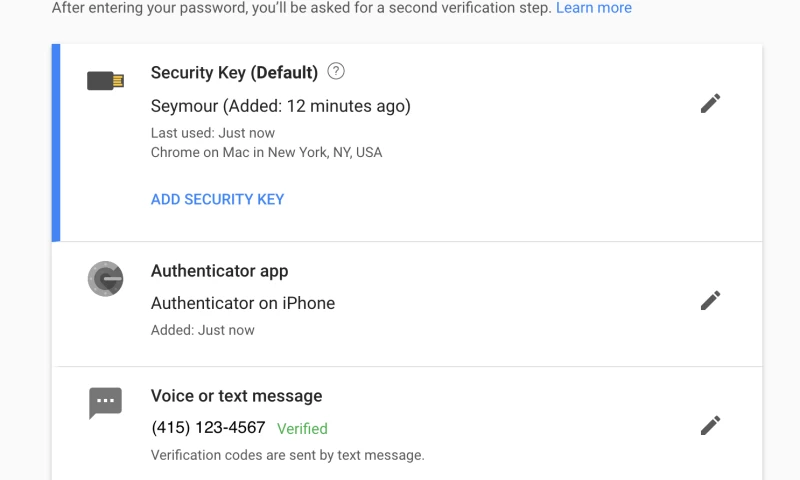
Cybersecurity Project for Nonprofit Company Enabling Multi-Factor Authentication -thumb-webp.webp)
IT Consulting Project for Real Estate Company MSP Services -min-thumb-webp.webp)
IT Services Project for Health Care Company Tech Refresh for Dispensary
Data sourced from the agency's DesignRush profileSPK Law Prairie Contractors Habitat for Humanity Swap-O-Rama Packback SATC, LLC Skokie Country Club Lake Shore Country Club Tuf Tite Subway of Chicago
Reviews verified by DesignRush and sourced from the agency's profileLME Services Reviews & Testimonials
 Michael Held CEO, Founder at LifeSpeak Inc.5.0★
Michael Held CEO, Founder at LifeSpeak Inc.5.0★Cybersecurity Review from Michael Held
LME SERVICES excels in the realm of project management. Their budgetary approach has been commendable, and their adherence to schedules has been impeccable. Our means of communication, primarily through Zoom and emails, have proven effective. Since collaborating with them, we have experienced no security breaches, a testament to their expertise. I am thoroughly satisfied with the meticulousness and communicative nature of LME SERVICES.
Show more Gary Hoffman President at Advanced Power Technologies5.0★
Gary Hoffman President at Advanced Power Technologies5.0★Cybersecurity Review from Gary Hoffman
We are incredibly astounded by the exceptional work performed by Lme Services. Their profound exploration of our security systems and databases surpassed our expectations. Lme Services astutely presented us with a comprehensive 100-page dossier, shedding light on their meticulous processes and offering invaluable recommendations to rectify the vulnerabilities in our system. These recommendations have been promptly implemented within our company, significantly enhancing our cybersecurity measures
Show more Tom Loveless President and CEO at VisionWeb5.0★
Tom Loveless President and CEO at VisionWeb5.0★Software Development Review from Tom Loveless
LME SERVICES promptly delivers top-notch resources of exceptional quality. LME SERVICES was engaged to augment our existing workforce for the development and enhancement of our Electronic Health Records (EHR) and Practice Management products. LME SERVICES excels in providing high-caliber resources promptly. We swiftly initiated the hiring process upon engaging with them, enabling us to onboard talented professionals swiftly. Highly recommend them !!
Show more
Expert Samurais in Developing Secure Apps With Sensitive Data
We love innovation! With more than ten years of experience in app and custom dev solutions, we found that it all starts with a good idea. A powerful one, looking for a change in the behavior of people through creativity, teamwork, and perseverance. [... see all FOONKIE MONKEY reviews ]- Location
- Miami, Florida
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $30/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 28 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsFOONKIE MONKEY Services
- Software Development
- Mobile App Development
- IoT
- Blockchain
- IT Services
- Web Design
- UI/UX Design
- Web Development
Data sourced from the agency's DesignRush profilePfizer Novartis Takeda Huawei Technologies Interamerican Development Bank IDB Mastercard BSJI Bank Bancolombia Davivienda Keralty
Reviews verified by DesignRush and sourced from the agency's profileFOONKIE MONKEY Reviews & Testimonials
 Anthony Link CEO at ConnectionsGRP5.0★
Anthony Link CEO at ConnectionsGRP5.0★Mobile App Development Review from Anthony Link
Anthony Link of Connections GP commends FOONKIE MONKEY’s work. He says the agency delivered everything it guaranteed. Its experts adhere to timelines and budget. They also collaborate via email and messaging apps. They were consistent with tasks completion, which led to a successful partnership. (Source: 3rd Party Review Platform)
Show more Justinian Brock Co-Founder/CEO at Vinosmith5.0★
Justinian Brock Co-Founder/CEO at Vinosmith5.0★Software Development Review from Justinian Brock
According to Justinian Brock of Vinosmith, FOONKIE MONKEY's team was prompt and great at communication and project management. The team promptly delivered high quality output. They were collaborative, flexible, and managed the client's expectations. The team also adapted to processes and tools well. Also, they are professional and a pleasure to work with. (Source: 3rd Party Review Platform)
Show more Viocary Feliz Assistant to CEO at Corporate Stays5.0★
Viocary Feliz Assistant to CEO at Corporate Stays5.0★Web Design Review from Viocary Feliz
According to Viocary, Assistant to CEO at Corporate Stays, FOONKIE MONKEY did an exemplary job delivering mobile app development services for his company. The agency's solutions met the client's expectations and received positive user feedback. Its project management approach was proactive and flexible. (Source: 3rd Party Review Platform)
Show more
Precise Software Solutions
Exaud develops custom cybersecurity software for high-tech companies, covering real-time threat detection, data protection, and compliance with industry standards. With expertise spanning AI, IoT, and blockchain, the cybersecurity firm builds security directly into complex technology ecosystems. [... see all Exaud reviews ]- Location
- Ermesinde, Portugal
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $70/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 12 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsExaud Services
- AI Development
- IoT
- Mobile App Development
- Software Development
- Wearables
- Blockchain
- DevOps Consulting
- Staff Augmentation
- Cybersecurity
- IT Compliance Solution
Data sourced from the agency's DesignRush profileAnoto Samsung NDrive Blaupunkt Audi Essent Facebook Google Nissan Presto
Reviews verified by DesignRush and sourced from the agency's profileExaud Reviews & Testimonials
 Dmitriy Ksendzovsky CEO at Software Consulting4.8★
Dmitriy Ksendzovsky CEO at Software Consulting4.8★Educational Review from Dmitriy Ksendzovsky
I have had an positive experience working with Exaud on expanding and maintaining several software products. Our software consulting technology stack is quite wide, from embedded development to mobile game dev, making it challenging to find the right partner knowledgeable in a number of these areas. The Exaud team is professional, flexible and continues to provide the development expertise we require to fulfill our project needs on time and budget.
Show more Stacy McCarthy President at Learning Design Network, Inc.4.8★
Stacy McCarthy President at Learning Design Network, Inc.4.8★Educational Review from Stacy McCarthy
Learning Design Network has been providing expert learning programs for 20 years, helping nearly 1 million employees worldwide achieve professional success. COVID prompted us to digitalize our product and we chose Exaud as our technology partner. Together, we developed a comprehensive digital tool for customized training and effortless collaboration in a 3D digital environment. The platform leverages our expertise and Exaud's technical capabilities, delivering a high-quality user experience.
Show more Tim Martin Software Architecture and Engineering at FS Studio5.0★
Tim Martin Software Architecture and Engineering at FS Studio5.0★Enterprise Review from Tim Martin
We have a very long history of working with Exuad, which in itself is about the best endorsement you can have. We have been working with them on projects for going on 10 years and they are our go to external dev team. Georg and team are not only very talented they are highly ethical. To me the later point is the most important, you can trust that they will provide high quality work and you can absolutely trust them on the business side.
Show more
Making functional and user friendly software's for humans
Mobirevo is a Leading custom software development agency focused on web, mobile app development & saas application development, Enterprise resource planning, and management software (ERP software development). We are a team of incredible Design & Agile software development experts in all major technology [... see all Mobirevo reviews ]- Location
- Port Harcourt, Nigeria
- Number of Employees
- Under 49
- Average Hourly Rate
- $200/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 2 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsMobirevo Services
- Web Design
- UI/UX Design
- Web Development
- Wearables
- Software Development
- Mobile App Development
- IT Services
- DevOps Consulting
- AI Development
- Blockchain
Data sourced from the agency's DesignRush profileEvery Event Delivery Monnee Inc. Rent is Cheap Virtual Lungs Fitness Propvat
Reviews verified by DesignRush and sourced from the agency's profileMobirevo Reviews & Testimonials
 Bobby Palmieri CEO at Lilo Social5.0★
Bobby Palmieri CEO at Lilo Social5.0★UX Strategy Review from Bobby Palmieri
Creating a smooth and engaging user experience was very important for our advertising company, and the team delivered exactly what we needed. They took the time to understand our goals and designed a strategy that made our platform easier to use and more attractive to clients. Their communication was excellent, and they kept us updated every step of the way. They worked fast, made changes when needed, and delivered everything on time. Since implementing the new UX strategy, weve seen better engagement and more positive feedback from users. The entire process was simple and stress-free. Highly recommended for UX strategy!
Show more Jeanette Marais CEO at Momentum Group Limited5.0★
Jeanette Marais CEO at Momentum Group Limited5.0★Mobile App Development Review from Jeanette Marais
Building a mobile app for a finance company requires precision, security, and ease of use, and the results were outstanding. The team took the time to understand every requirement and created an app that is both user-friendly and reliable. From start to finish, communication was clear, and every update was delivered on time. Any requested changes were handled quickly, and the final product has made financial transactions much easier for clients. The process was hassle-free, and their expertise truly made a difference. Highly recommended for mobile app development!
Show more Tiziano Tassi CEO at Caffeina5.0★
Tiziano Tassi CEO at Caffeina5.0★Web Development Review from Tiziano Tassi
Creating a professional and user-friendly website was a top priority for our advertising company, and the results were impressive. The team carefully listened to our requirements and designed a site that is both visually appealing and easy to navigate. Throughout the project, communication was clear, and any adjustments we requested were handled promptly. The website performs smoothly and has significantly improved our online presence. The experience was seamless, and their expertise truly stood out. Highly recommended for web development services!
Show more
Driving Project Success No Matter What
ScienceSoft USA Corporation, doing business as ScienceSoft, is an IT consulting and software development company with 36 years of experience. We deliver secure solutions for healthcare and financial services, as well as retail, manufacturing, telecom, and more. [... see all ScienceSoft reviews ]- Location
- McKinney, Texas
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $50/hr
- Portfolios Count
- 11 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsScienceSoft Services
- Software Development
- Mobile App Development
- Cloud Consulting
- Managed Services
- Wearables
- IoT
- AI Development
- eCommerce Development
- Blockchain
- IT Services
Data sourced from the agency's DesignRush profileBaxter PerkinElmer Child Mind Institute bioAffinity RIVANNA AKLOS Health TriadXP HealthPoint Plus Delaware Valley Community Health ScribeAmerica
Reviews verified by DesignRush and sourced from the agency's profileScienceSoft Reviews & Testimonials
 Shawn Hyman Jr. Manager of Information Technology at Delaware Valley Community Health5.0★
Shawn Hyman Jr. Manager of Information Technology at Delaware Valley Community Health5.0★Web Development Review from Shawn Hyman Jr.
Working with ScienceSoft was nothing but a learning experience while building our Intranet! I started my search for someone to help my organization to help us build an intranet site and came across ScienceSoft. Their reviews were nothing but positive and I've learned why first hand! Their very responsive and very knowledgeable for assisting with our Intranet implementation. We met twice a week, and everyone was punctual with meetings and deadlines. I recommend ScienceSoft for any needs and will work with the company again if needed in the future!
Show more.png) Justin Turner CTO at Chiron Health5.0★
Justin Turner CTO at Chiron Health5.0★Mobile App Development Review from Justin Turner
Chiron Health’s core business is providing caregivers with a web-based telemedicine platform which allows them to connect with patients for routine follow-ups and similar use cases. We engaged ScienceSoft to build an Android app that complements our web-based platform for our patients. ScienceSoft developers proved themselves to be Android experts. They advised and successfully lead the way from end to end through the technical challenges and considerations with development of the Android app. ScienceSoft team was in daily contact with our developers and our method of communication was a huge factor in how successful this engagement was. I would also like to point out ScienceSoft’s solid approach to testing. The thorough testing they performed on our beta environment ensured that the app was launched without critical bugs. We have also engaged them to introduce a few enhancements to the app and would certainly consider ScienceSoft as a technology partner in further software development initiatives.
Show more.png) Patrick Pakan Founder and CEO at AKLOS Health5.0★
Patrick Pakan Founder and CEO at AKLOS Health5.0★Healthcare Review from Patrick Pakan
I’ve had six orthopedic surgeries since playing college football and tried every major digital exercise therapy platform on the market. None of them offer the comprehensive and personalized care they claim. Thanks to ScienceSoft’s practical healthcare IT expertise, we created a musculoskeletal therapy platform that can be fully customized and reflect the needs of each program member. I am excited to see AKLOS Health change the approach to physiotherapy and offer each member a truly bespoke experience that’s based in science.
Show more
Together, beyond expectations
CHI Software is a technology solution provider that offers a full set of software-based services from custom software development to maintenance & support. Our talented team is passionate about Generative AI, Cloud Computing, Data Engineering, and IoT. CHI's success comes from care of every client [... see all CHI reviews ]- Location
- Lviv, Ukraine
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $60/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 12 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsCHI Services
- AI Development
- Mobile App Development
- Software Development
- Web Development
- Staff Augmentation
- Software Testing
- IoT
- Big Data Analytics
- IT Services
- DevOps Consulting
Data sourced from the agency's DesignRush profileVodafone Lecre Media Mrkt
Reviews verified by DesignRush and sourced from the agency's profileCHI Reviews & Testimonials
.png) David Gornshtein Co-Founder at Binadox5.0★
David Gornshtein Co-Founder at Binadox5.0★Web Development Review from David Gornshtein
My company was looking for a development team to proceed with the development process. We needed to set up a service [that] allows our clients to monitor, control, and optimize their Cloud & SaaS spend. [The] CHI Software team delivered services and technologies we need[ed] to reach our financial goals. (Verified via email)
Show more
Top Cyber Security Company in Australia
CREST-accredited penetration testing expert, Borderless CS specializes in over 15 cybersecurity services, including vCISO as a Service and Microsoft 265 protection. Led by a team of 36 Australian certified experts, the cybersecurity firm serves SMEs and enterprises seeking a local partner. [... see all Borderless CS reviews ]- Location
- Melbourne, Australia
- Number of Employees
- Under 49
- Average Hourly Rate
- $200/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 1 Project Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsBorderless CS Services
- Cybersecurity
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project Identity and Access Management (IAM) Implementation Project
Data sourced from the agency's DesignRush profileColes NAB IBM
Reviews verified by DesignRush and sourced from the agency's profileBorderless CS Reviews & Testimonials
 Anthony Treyman Marketing Coordinator at Kids in the Game5.0★
Anthony Treyman Marketing Coordinator at Kids in the Game5.0★Cybersecurity Review from Anthony Treyman
Their knowledge not only strengthened our cybersecurity defenses but also created confidence in our workforce. The measurable results and their distinctive proactive strategy demonstrate their dedication to greatness. While there were small communication issues, they did not overwhelm the great value they delivered to our organization. We strongly recommend Borderless cs to everyone looking for high-quality cybersecurity solutions.
Show more Jorge Guzman Brand Ambassador at Vaporesso5.0★
Jorge Guzman Brand Ambassador at Vaporesso5.0★Cybersecurity Review from Jorge Guzman
While our experience with Borderlescs was overwhelmingly positive, there is always room for improvement. One area they could consider enhancing is the documentation of their processes and solutions. Having more detailed documentation would help us better understand the implemented measures and would be useful for future reference.
Show more Jeremy Huffman Director of Technology at Sprout5.0★
Jeremy Huffman Director of Technology at Sprout5.0★Cybersecurity Review from Jeremy Huffman
Their comprehensive approach, technical expertise, and commitment to our security stood out. The positive impact on our cybersecurity measures and the peace of mind that came with their service made the partnership incredibly valuable. Despite minor areas for improvement, we have no hesitation in recommending Borderlescs to other businesses seeking top-notch cybersecurity solutions tailored to their industry-specific requirements.
Show more
Making Lives Better Through Managed IT
Mainstream Technologies has operated as a certified MSSP since 2010, covering managed risk assessments, threat monitoring, incident response planning, disaster recovery, and compliance management. Based in Arkansas, the firm offers a complimentary external vulnerability assessment. [... see all Mainstream Technologies reviews ]- Location
- Little Rock, Arkansas
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $100/hr
- Portfolios Count
- 5 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsMainstream Technologies Services
- Mobile App Development
- Managed Services
- IT Services
- Software Development
- Cybersecurity
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio-thumb-webp.webp)
Managed Service Providers Project McGehee Hospital Case Study
Data sourced from the agency's DesignRush profileMcGehee Hospital HIPAA The Triple Constraint
Reviews verified by DesignRush and sourced from the agency's profileMainstream Technologies Reviews & Testimonials
 Jackie d'Escoto Marketing and IT Manager at d'Escoto5.0★
Jackie d'Escoto Marketing and IT Manager at d'Escoto5.0★IT Services Review from Jackie d'Escoto
Because of Mainstream Technologies’ hosting services, we’re able to respond to our clients’ needs faster without increasing overhead.
Show more Greg Holder Co-Founder and CEO at Traverse Systems5.0★
Greg Holder Co-Founder and CEO at Traverse Systems5.0★IT Services Review from Greg Holder
There came a time when we decided to offer our solution in an ASP environment. With the help of Mainstream Technologies, we leveraged their data center and staff to actively monitor and manage our systems.
Show more Brad Cazort Director at Arkansas Crime Information Center5.0★
Brad Cazort Director at Arkansas Crime Information Center5.0★IT Services Review from Brad Cazort
I have been infinitely pleased with the work product and the results.
Show more
Enterprise AI Solutions | Scalable . Flexible. Sustainable
Achieving a CMMI Level 5, Seasia Infotech offers robust, scalable IAM, cloud security, CSOM, advanced threat protection, and managed cybersecurity services. With over 20+ years in enterprise IT security, it has helped BFSI, healthcare, government, and logistics companies achieve cyber resilience. [... see all Seasia Infotech reviews ]- Location
- Emeryville, California
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 52 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSeasia Infotech Services
- Software Development
- Mobile App Development
- Web Development
- AI Development
- Big Data Analytics
- Cloud Consulting
- Staff Augmentation
- Cybersecurity
- IoT
- Software Testing
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Azure Project for Automotive Company Canbrowser (CB System) High-Performance Enterprise Data Integration
Data sourced from the agency's DesignRush profileAdani Group Flipkart Harley-Davidson Microsoft MainStreet Equity Corp HDFC Bank Swaraj Innopharma Education Renault Puda
Reviews verified by DesignRush and sourced from the agency's profileSeasia Infotech Reviews & Testimonials
 cornelia verden Web Developer at Cornelia Verden LLC5.0★
cornelia verden Web Developer at Cornelia Verden LLC5.0★eCommerce Development Review from cornelia verden
This Company is AMAZING, they are very professional. We hired them to build my website, and they did an EXCELLENT job. They continuously communicated with me during the development phase. If you want a beautiful, well-designed, professional website that has optimum functionabilty, You must go with Seasia Infotech. You can always expect excellent quality services from the professionals at Seasia Infotech.
Show more
What Are Penetration Testing Companies?
Penetration testing companies perform ethical cybersecurity tests designed and built to identify and carefully exploit vulnerabilities impacting a certain organization's computer systems, networks, websites, and applications.
What Does a Penetration Testing Firm Do?
Pen testing companies intentionally launch a series of simulated cyberattacks, a form of ethical hacking, while utilizing strategies, methodologies, and tools formulated and created to gain access to IT systems and networks.
A penetration testing firm executes this process to uncover weak points and risks so they can be addressed immediately, significantly lowering the odds of getting targeted and harmed by malicious attacks.
Weak areas in the defenses of systems and networks may cause easy exposure to threats or data and overall security breach. Pen testing firms detect these exploitable issues and spot other susceptibilities.
Here are what a penetration testing service provider can do for your company or business:
1. Expose Exploitable Vulnerabilities
Penetration testing companies perform deliberate attempts at breaching application systems such as application protocol interfaces or APIs and frontend and backend servers. This procedure will reveal vulnerable input that may be prone to attacks and code injection by hackers.
2. Reinforce WAF
A penetration testing firm can deliver valuable insights and assessments following the results of the pen tests. Using these observations, the penetration test team can finetune your web application firewall or WAF, making adjustments, modifications, and tweaks where necessary.
3. Propose Strengthened Security Plans & Policies
Pen testing companies meticulously examine and evaluate computer systems and networks level and depth of security. Using the same techniques, processes, and tools that attackers use, pen testing experts discover and demonstrate what impact and damage system and network weaknesses can have on your business.
In this light, your penetration testing service provider can give you data-driven and well-calculated recommendations for more robust and powerful security policies and strategies.

What are the Stages of Penetration Testing?
These are the five phases that complete the whole cycle of a pen test:
1. Planning and Reconnaissance
This is when your penetration testing firm defines the test's scope and goal. It includes identifying and locating the systems that need to be addressed and the most appropriate method.
During this stage, your penetration testing service provider will gather as much information as possible such as mail server, and network, and domain names. This information will help them better understand the vulnerabilities of potential targeted applications of threats or attacks.
2. Scanning
Next up, the pen test team will evaluate how a specific target may respond to different intrusions and attempts of interruption.
Scanning can be done either through static analysis or dynamic analysis. On the one hand, static analysis allows for the inspection of a target application’s code to estimate how it behaves while it’s running. On the other hand, the dynamic analysis provides real-time evaluation of the overall performance of a target application in its running state, making it the more practical choice for the scanning process.
3. Gaining Access
This stage involves using web application attacks like cross-site scripting, SQL injection, and backdoors to expose the target application’s weaknesses. What pen-testing firms do is try exploiting these vulnerabilities. They will attempt to steal data, escalate privileges, and intercept traffic.
The results of this intentional infringement and disruption will then give them information about the repercussions these may trigger and the extent of potential damages that may be inflicted.
4. Maintaining Access
The objective of maintaining an exploit is to determine if the affected vulnerability may turn into a long-term, advanced threat in the system.
This stage will help penetration testing companies more carefully gauge how deeply an attacker could reach if the persistent threat stays in the exploited system. It will also answer the question of how long it would take to detect a lingering threat and its potential to steal sensitive and confidential company data.
5. Review and Analysis
The final step comprises the compilation of results and reports following the first four stages. The review and analysis aim to detail the following:
- Specific vulnerabilities deliberately exploited
- Sensitive data that the intentional attacks managed to access
- The duration of time the penetration testing company spent in the system without detection
- Configuration by the penetration testing firm of the company’s WAF settings
- Application of solutions proposed by the security testers to close network and system gaps, safeguard vulnerabilities, and protect against future attempts at intrusion
What are the Types of Pen Tests?
Penetration testing companies must have extensive know-how and capabilities to execute and complete each of the following types of penetration testing:
1. External Testing
In an external penetration test, pen testing companies target external-facing assets of your business. These technologies are visible on the internet, such as company websites, web applications, email and domain name servers (DNS), and external network servers.
In some scenarios, there is no need for the penetration testing service provider to be physically present in office. Their security personnel and ethical hackers will conduct the attack remotely from another location.
2. Internal Testing
During an internal pen test, the security tester simulates an attack toward vulnerabilities from behind the firewall. This intends to mimic an intrusion from the inside of the company, whether it is a malicious insider or an employee with compromised credentials that have actual hackers.
3. Blind Testing
A blind penetration test is also called closed-box pen text or single-blind test. In this case, pen testing firms are only provided with no more than the target company’s name. It aims to give a real-time glimpse into how an application attack and a system breach occur.
4. Double-Blind Testing
The double-blind pen test is also known as the covert pen test. During this testing, almost no one within your organization knows that a penetration test is happening. In most situations, not even your in-house IT specialists or security professionals, responding to the impending system assault simulation, are made aware of the pen test.
The covert or double-blind pen tester especially requires a thoroughly detailed scope of the ethical hack in written form to ensure there is no disregard for legal policies and no law is violated.
Why Hire Pen Testing Companies?
Beyond its function as a vulnerability scan and a compliance audit, penetration tests are designed for in-depth examination of the effectiveness and efficiency of security controls and protocols in real use by real enterprises in real situations. It is through pen tests that the capacities and preparedness of an organization are measured.
These tests are so valuable in that they can answer whether your company can tackle multiple simultaneous attacks. That is why you will need the expertise of skilled, ethical hackers from a dedicated penetration testing firm.
1. Get to the Bottom of Vulnerabilities Before Malicious Attackers Do
Pen testing companies can bring light to vulnerabilities early on. Recognizing applications and other aspects of your company’s IT systems and networks that are susceptible keeps you on the lookout and positions you several steps ahead of a would-be intruder. Hiring the services of a penetration testing firm is practical and strategic.
2. Know the Strengths of Your Network Defenders
A penetration test is a precautionary measure, too. Through the proficiencies of a pen testing company, you can unveil and measure the readiness and effectiveness of your intrusion detection programs and defenses. Penetration testers will know if your security and protection tools are robust enough and working correctly.
3. Evaluate the Potential Damages in the Event of a Successful Attack
The detrimental effects of an attack include disruption of business processes, financial losses, damaged brand reputation, dissemination of critical and classified data, and interference in the organizational infrastructure.
In the United States alone, the average data breach cost in 2021 was $4.24 million, and the amount continues to rise annually.
Identifying these impacts following a breach allows your company to map out actionable steps to mitigate them, if not entirely avert them.
How Much Does a Penetration Testing Service Provider Charge for Their Services?
Several variables influence the asking fees of pen testing firms. These include the complexity of the tests, the choice of or required methodology, and the experience of the agency in the industry.
A pen testing company will also factor in whether the test will be performed on one application or whether there will be multiple tests for various applications. On-site visits mean additional charges, too.
On average though, an excellent-quality, professional penetration testing costs between $15,000 and $30,000. The price for a “simple” pen testing for a single app can start from $5,000.
How to Select the Right Penetration Testing Firm for Your Project?
Here are the qualifications to look for when choosing the best penetration testing agency partner for your business:
1. Review Certifications
Make sure you work with a pen test firm with industry certifications. This guarantees that the agency is a leader and authority in the industry and is equipped with expertise in specific business models. Here are some of the most prominent certifications penetration testing companies can obtain:
- Computer Resilience Evaluation Standard Tool (CREST)
- Certified Ethical Hacker (CEH)
- EC Council Certified Ethical Hacker certification
- Certified Information Systems Security Professional (CISSP)
2. Be Clear on Communication Channels
Your ideal penetration testing service provider must excel on the job and keep you in the loop of the entire testing process. Its team should inform and provide you with updates during each step of the testing procedures. It is their responsibility to give you adequate explanation and clarification regarding technicalities and other details which may not be clear to you.
Complete transparency in payment structure and payment plans is also a must from the start of the transaction up to the project completion.
3. Look for Flexibility
Partner with a firm whose testing methods are adaptable to your organizational structure and business model. Your agency choice must also be willing to adjust to your preferred schedule.
10 Questions to Ask When Interviewing Pen Testing Firms
- What professional certifications and training does your firm hold?
- What are your available testing methodologies?
- What data are included in your review and analysis report?
- How do you maintain internal security for your agency?
- Do you also offer remediation services?
- Will you be assigning us a single dedicated team of penetration testers?
- How in-depth are your background and screening check procedures for your employees?
- How do we maintain communication with your company?
- What are your specialized focus areas?
- Will our business services remain live even during the pen testing?
Takeaways on Penetration Testing Companies
In any business or organization, the security of networks, data, and its people is a foremost priority. Investing in a reputable and vastly experienced penetration testing firm is genuinely worthwhile.
You will gain more from investing in prevention and defenses against malicious intruders. In addition to securing finances and crucial information, the benefits of working with a penetration testing service provider entail a specific capacity of freedom and give you your share of peace of mind.
Best of luck!


















































