Connect with vetted cybersecurity service providers to secure networks, monitor vulnerabilities, and maintain compliance, keeping your operations and customer data safe. Filter your search by expertise, location, and budget to find the right provider.
- Home
- Cybersecurity Companies
Discover the Best Cybersecurity Firms
DesignRush evaluates all cybersecurity firms listed based on technical expertise, proven practical experience, and client reviews. Some listings may be paid.
Goji Labs - A Digital Product Agency That Builds it Right
We help our partners turn complex challenges into intuitive products through strategy, design, and development. We've successfully launched 400+ products and helped raise over $1B in fundingand counting. [... see all Goji Labs reviews ]Top Services:
- Cybersecurity
- Wearables
- IoT
- Location
- Los Angeles, California
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $149/hr
- Portfolios Count
- 18 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsGoji Labs Services
- Mobile App Development
- Software Development
- UI/UX Design
- AI Development
- Web Design
- Product Design
- Digital Strategy
- Web Development
- Blockchain
- IoT
Data sourced from the agency's DesignRush profileWorld Wildlife Fund K-ID City of Los Angeles TGS Kangarootime World Health Organization Prediction Strike American Kennel Club Youth on Their Own Root Insurance
Reviews verified by DesignRush and sourced from the agency's profileGoji Labs Reviews & Testimonials
 Anonymous Contracted Frontend Developer at Software Solution Company4.8★
Anonymous Contracted Frontend Developer at Software Solution Company4.8★Web Development Review from Anonymous
Goji Labs designed and implemented a contact form plug-in on our WordPress site. They connected it to an external API for smooth data migration and ensured the design blended naturally with our existing site. The team made sure we were happy with the end result before wrapping up, which gave me confidence in their work.
Show more Anonymous CTO at huupe4.8★
Anonymous CTO at huupe4.8★Mobile App Development Review from Anonymous
I worked with Goji Labs on building a custom mobile solution and frontend platform. The engagement included multiple design iterations and development cycles to refine the UX. Their project manager was always available when I needed input, and their team integrated seamlessly with mine, making collaboration easy.
Show more.png) Anonymous CEO at Capi Design5.0★
Anonymous CEO at Capi Design5.0★Web Design Review from Anonymous
Goji Labs created a design that really hit the mark for us. Their team managed the project smoothly and kept communication accessible at all times, whether by email, messaging apps, or virtual meetings. The process felt structured and professional from start to finish.
Show more
Build Intelligent Apps for Web, Mobile, Data, AI and Cloud
Azumo helps businesses build intelligent apps by providing top-tier developers skilled in AI, data engineering and enterprise web & mobile applications. Our expertise has earned the trust of industry leaders like Facebook, Twitter, Discovery, Zynga, and NCSoft. [... see all Azumo reviews ]Top Services:
- Cybersecurity
- Software Development
- Web Development
- Location
- San Francisco, California
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $55/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 9 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsAzumo Services
- AI Development
- Software Development
- Staff Augmentation
- Mobile App Development
- Big Data Analytics
- DevOps Consulting
- Cloud Consulting
Data sourced from the agency's DesignRush profileDiscovery Channel Meta Zynga Jostens Assembled Brands NGL NCSoft Twitter Horoscope.com Bento
Reviews verified by DesignRush and sourced from the agency's profileAzumo Reviews & Testimonials
 Michael S. Director at Software Development Company5.0★
Michael S. Director at Software Development Company5.0★Software Development Review from Michael S.
We selected Azumo to develop our software. We transitioned from another development company, so Azumo was initially responsible for migrating our existing code and environments. We are currently still working with Azumo as our nearshore software development team on adding new items to our software.
Show more Anonymous CTO at Healthcare Company5.0★
Anonymous CTO at Healthcare Company5.0★UI/UX Design Review from Anonymous
Azumo helped us migrate our existing UIs into a new framework, creating reusable components and the infrastructure needed for future development. The developer they assigned became a seamless part of our team, always punctual, responsive, and a great fit overall.
Show more Anonymous VP Product & Engineering at Sales & Mktg Software Company5.0★
Anonymous VP Product & Engineering at Sales & Mktg Software Company5.0★Software Development Review from Anonymous
Thanks to Azumo’s work, our product is now more scalable, optimized, and ready for a growing user base. Their team has managed the engagement effectively, keeping us updated and addressing any challenges along the way. We’ve appreciated their constant availability and proactive communication.
Show more
Accelerating Software Development - Building Offshore Software Development Centers
Saigon Technology focuses on tailored web and app development for emerging startups and established enterprises. The company adheres to ISO standards and embraces an Agile approach. Models: offshore software dedicated team and fixed price. [... see all Saigon Technology reviews ]Top Services:
- Cybersecurity
- Magento
- AI Development
- Location
- Ho Chi Minh, Vietnam
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $35/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 44 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSaigon Technology Services
- Software Development
- Staff Augmentation
- AI Development
- Web Development
- Mobile App Development
- DevOps Consulting
- Cybersecurity
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio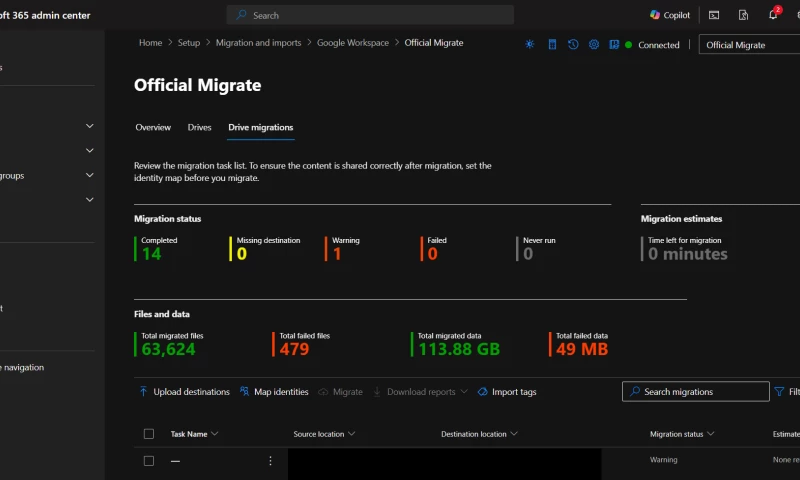
IT Services Project for Hardware & Networking Company Google Workspace to Microsoft 365 Migration
Data sourced from the agency's DesignRush profileChiliPay AWC Barddy Frupor Genesis Sun idealpos ISMS Global Lucette Minmed Telehealth MTM
Reviews verified by DesignRush and sourced from the agency's profileSaigon Technology Reviews & Testimonials
 Vasko Markovski Manager of App Development at Real Estate of Ontario5.0★
Vasko Markovski Manager of App Development at Real Estate of Ontario5.0★Mobile App Development Review from Vasko Markovski
Our company hired them to create an app designed to help expatriates find housing. A project manager and two developers from Saigon Technology worked closely with our team for the app's development. At the start, their team and ours gathered the information needed for the project and planned out how to build the product. They then designed the app's interface and added features. In the end, we launched the app successfully, and our client was satisfied with it.
Show more Rich McMahon CEO at cda ventures LLC5.0★
Rich McMahon CEO at cda ventures LLC5.0★Web Development Review from Rich McMahon
Our experience with Saigon Technology Company for our Business Consulting website design was exceptional. They displayed a profound understanding of our requirements and translated them into a visually captivating and user-friendly website. Their attention to detail, creativity, and professionalism were evident throughout the process. From concept to delivery, they surpassed our expectations, delivering a sleek and functional website that perfectly encapsulated our brand identity. Saigon Technology Company truly exceeded our expectations.
Show more Jerry Coleman Founder at Offerpad5.0★
Jerry Coleman Founder at Offerpad5.0★Web Development Review from Jerry Coleman
Saigon Technology surpassed our expectations with their exceptional website design for our real estate company. Their team displayed remarkable creativity, capturing the essence of our brand while ensuring seamless functionality and user experience. From the initial consultation to the final product, their professionalism and attention to detail were evident. They effectively incorporated our feedback, resulting in a website that perfectly showcases our properties and attracts potential buyers. Saigon Technology's expertise in website development is commendable, and we highly recommend them for anyone seeking top-notch design and technical proficiency.
Show more
Top US Mobile & Web App Development Agency
AppMakersUSA is a US-based full-service mobile application development company. We specialize in building cross-platform websites and apps (meaning iOS & Android for the price of one), informing your business decisions from a technical perspective, and being transparent in our process & thinking. [... see all AppMakers USA reviews ]Top Services:
- Cybersecurity
- IT Services
- Wearables
- Location
- Los Angeles, California
- Number of Employees
- Under 49
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 83 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsAppMakers USA Services
- Mobile App Development
- UI/UX Design
- AI Development
- Software Development
- Web Design
- Staff Augmentation
- Web Development
Data sourced from the agency's DesignRush profileCVS Pharmacy Austin Ekeler (NFL Player) ClassCalc Number Hive BookClub Arcxis Debate club Bayut Los Angeles Apparel Sun Scooter
Reviews verified by DesignRush and sourced from the agency's profileAppMakers USA Reviews & Testimonials
 Awital Ifrah Program manager at Masa Israel journey5.0★
Awital Ifrah Program manager at Masa Israel journey5.0★Cross-Platform Review from Awital Ifrah
Masa came in with a pretty loose idea and AppMakers helped turn it into something solid. What I appreciated most is they didn't overcomplicate it or try to make it into some giant monster platform. They listened, asked smart questions, and helped us focus on what would actually matter for alumni and current participants. The end result felt thoughtful and realistic. I'd definitely work with them again.
Show more Moishi Stern Customer support at Madlan5.0★
Moishi Stern Customer support at Madlan5.0★Startup Review from Moishi Stern
We create live events. We wanted a site that shows what we do without making people dig. AppMakers listened, trimmed the fluff, and gave us pages that read fast and look good on a phone. The quote form asks the right things and our team can update galleries without calling a developer. They stayed on schedule and answered messages the same day. The whole process was calm and clear. We already see better inquiries. It feels like a real upgrade, even before the full rebuild.
Show more Jubilee Haddasah Munozvilla CEO at Its Kinda Catchy5.0★
Jubilee Haddasah Munozvilla CEO at Its Kinda Catchy5.0★Small Business Review from Jubilee Haddasah Munozvilla
We loved working with AppMakers. They built us a procurement system to help quickly and easily secure materials for our labs. The process was smooth and the outcome was stellar.
Show more
We make the latest technology work for you
AI & Custom Software Development Company —We deliver end-to-end software solutions for global clients across 5 continents, with expertise in AI, custom software and web & mobile applications. [... view Pontis Technology profile ]Top Services:
- Cybersecurity
- Outsourcing
- Software Development
- Location
- Zagreb, Croatia
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $10,000 - $25,000
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsPontis Technology Services
- AI Development
- Software Development
- Mobile App Development
- Software Testing
- Big Data Analytics
- Cloud Consulting
- Cybersecurity
- Web Design
- DevOps Consulting
- UI/UX Design
Data sourced from the agency's DesignRush profileKatana Mitsubishi Qrios ZenLab's AG Design
Modern IT. Built Secure. Delivered Right.
Zazz is a trusted software engineering and IT services partner helping enterprises deliver secure, scalable, high-impact tech initiatives. We solve complex challengeslegacy bottlenecks, tech debt, talent gaps, compliance risks, and system fragmentation. [... see all Zazz reviews ]- Location
- Seattle, Washington
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $45/hr
- Portfolios Count
- 36 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsZazz Services
- Mobile App Development
- IT Services
- Software Development
- Staff Augmentation
- IT Compliance Solution
- Cybersecurity
- Managed Services
- Cloud Consulting
- DevOps Consulting
- Web Development
Data sourced from the agency's DesignRush profileJP Morgan BBC News PayPal Harvard Innovation Labs HBO Jeddah Season McDonald's NBA Honda Citibank
Reviews verified by DesignRush and sourced from the agency's profileZazz Reviews & Testimonials
 Sam Zaid CEO at Getaround5.0★
Sam Zaid CEO at Getaround5.0★Mobile App Development Review from Sam Zaid
Their team's technical proficiency and creativity have significantly contributed to the success of our world's first connected carsharing marketplace. Zazz not only met but exceeded our expectations, delivering a seamlessly integrated and user-friendly mobile app that has truly empowered people to carshare everywhere. The collaboration with Zazz has proven to be a valuable partnership, marked by open communication, timely delivery, and a genuine dedication to our mission.
Show more Jay Thrash SENIOR IOS DEVELOPER at Epic Games5.0★
Jay Thrash SENIOR IOS DEVELOPER at Epic Games5.0★Mobile App Development Review from Jay Thrash
Their unparalleled expertise and dedication to excellence were evident throughout the entire collaboration. Zazz's team consistently demonstrated a deep understanding of our vision, translating it into a seamless and innovative mobile application. Their commitment to quality and precision in every aspect of the development process was truly impressive. Zazz's ability to navigate complex challenges with agility and deliver solutions that exceeded our expectations was instrumental in the success of our project.
Show more Don Harmon Director of Global IT Services at Dorel Juvenile5.0★
Don Harmon Director of Global IT Services at Dorel Juvenile5.0★Mobile App Development Review from Don Harmon
Zazz's commitment to delivering a high-quality mobile app for Dorel Juvenile was evident throughout the entire development process. The team consistently communicated progress, promptly addressed any concerns or modifications, and ensured that the final product not only met but exceeded our expectations. The mobile app developed by Zazz not only showcased cutting-edge technology but also reflected a deep understanding of the child-centric focus that Dorel Juvenile upholds.
Show more
Top rated Artificial intelligence solutions company
At Innovacio Technologies, we bring over 7+ years of experience in AI software (Generative AI, LLM, Machine Learning, Computer Vision, Chatbot etc.), app, and web development. Our expert team is dedicated to delivering innovative solutions that drive growth for your business. [... see all Innovacio Technologies reviews ]- Location
- Boston, Massachusetts
- Number of Employees
- 50 - 99
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 39 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsInnovacio Technologies Services
- AI Development
- Mobile App Development
- Software Development
- Staff Augmentation
- VR/AR
- Big Data Analytics
- DevOps Consulting
- Cloud Consulting
- IT Compliance Solution
- Cybersecurity
Data sourced from the agency's DesignRush profileCoca Cola Bajaj Drala Haldiram's Lacoste
Reviews verified by DesignRush and sourced from the agency's profileInnovacio Technologies Reviews & Testimonials
 Haider Ali Baig CEO at Exponeur5.0★
Haider Ali Baig CEO at Exponeur5.0★AI Development Review from Haider Ali Baig
We are truly grateful to Innovacio Technologies for their exceptional work on our Vehicle Tracking System Automation. Their expertise in DevOps and vehicle tracking solutions has greatly improved our operations, ensuring real-time visibility and system reliability. We appreciate their dedication to delivering seamless, efficient solutions that have supported our growing fleet needs. Thank you for your outstanding support and commitment!
Show more Ariyan Kabir CEO at GrayMatter Robotics5.0★
Ariyan Kabir CEO at GrayMatter Robotics5.0★AI Customer Service Review from Ariyan Kabir
We collaborated with Innovacio Technologies to implement an AI-Powered Fraud Detection System for our banking and ATM services, and the results have been outstanding. The AI system quickly identifies unusual transaction patterns and flags potential fraud in real-time, significantly enhancing security and reducing fraud incidents. Innovacio Technologies seamlessly integrated the solution with our existing infrastructure while ensuring full compliance with banking security standards. Their expertise in AI has been crucial in developing a reliable, scalable system. We highly recommend Innovacio Technologies who looking to improve fraud detection.
Show more Charlie Meredith CTO at GoodMaps5.0★
Charlie Meredith CTO at GoodMaps5.0★AI Application Development Review from Charlie Meredith
Were extremely impressed with the AI-Powered Customer Insights solution from Innovacio Technologies. It has revolutionized our understanding of customer behavior and enabled us to refine our marketing strategies for a more personalized customer experience.
Show more
Next gen of QA, riding the wave of agentic pipelines.
BetterQA is a Cluj-Napoca based software testing company that has built 8 proprietary tools to power modern QA. We help startups and enterprise teams ship safer, more reliable software through practical, real-world testing services. We go beyond finding bugs, we help teams grow with confidence. [... see all BetterQA reviews ]- Location
- Cluj-Napoca, Romania
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 8 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsBetterQA Services
- Software Testing
- IT Services
- Cybersecurity
- DevOps Consulting
- Business Consulting
- Customer Support
Data sourced from the agency's DesignRush profilevulog eyeware primeur Collaboard butter. Owlet MEDIAL Multimedia services YZR
Reviews verified by DesignRush and sourced from the agency's profileBetterQA Reviews & Testimonials
 Brenda Collin FIH Executive Vice President at Preferred Travel Group5.0★
Brenda Collin FIH Executive Vice President at Preferred Travel Group5.0★Software Testing Review from Brenda Collin FIH
Our busy online marketplace couldnt afford downtime or broken features after updates. BetterQA built and maintained a robust automated regression suite that tested checkout, search, user dashboards, and seller workflows. Their automation scripts run with every deployment and catch issues before users experience them. The improvement in deployment confidence and QA turnaround has been tremendous. Their technical skills in Selenium and Cypress, plus their understanding of business workflows, helped us scale operations without QA bottlenecks.
Show more Christopher Savage CEO at Greater Fort Lauderdale Chamber of Commerce5.0★
Christopher Savage CEO at Greater Fort Lauderdale Chamber of Commerce5.0★Software Testing Review from Christopher Savage
We worked with BetterQA on a software testing project and were thoroughly impressed by their professionalism and precision. Their team identified key issues early, ensuring our product was stable and ready for launch. A reliable QA partner wed gladly work with again
Show more Ramesh Pathak CEO and Co-founder at Naamche5.0★
Ramesh Pathak CEO and Co-founder at Naamche5.0★Software Testing Review from Ramesh Pathak
We partnered with BetterQA for software testing across several of our products. Their team handled both manual and automated testing, identifying critical bugs and improving release stability. Their detailed reports and fast feedback loop made our development process smoother. We were impressed with their professionalism and consistent quality of work.
Show more
Pixelette Technologies - Leading the way in AI & Blockchain
Pixelette Technologies - Leading the way in AI & Blockchain [... see all Pixelette Technologies reviews ]- Location
- London, United Kingdom
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 43 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsPixelette Technologies Services
- Software Development
- Web Development
- Web Design
- Blockchain
- Mobile App Development
- AI Development
- VR/AR
- Cybersecurity
- Staff Augmentation
- IT Services
Data sourced from the agency's DesignRush profileCast Lighting Rooms in Huddersfield One Stop CCTV Airobounce WildWood Resturants Kumon Ystral Webfixxim Who Can Fix My Car Positive Prime
Reviews verified by DesignRush and sourced from the agency's profilePixelette Technologies Reviews & Testimonials
 Mark Vetrano CEO|CSO at Contact Fuel5.0★
Mark Vetrano CEO|CSO at Contact Fuel5.0★Blockchain Review from Mark Vetrano
Temur's team was professional, responsive, and made the entire process smooth. Were impressed with the results and how much value their solution has added to our business.If you're looking for innovative blockchain solutions, Pixelette Technologies is the way to go!
Show more Lauren Ratner President & Chief Brand Officer at rhode skin5.0★
Lauren Ratner President & Chief Brand Officer at rhode skin5.0★Software Development Review from Lauren Ratner
Pixelette Technologies designed custom software that streamlined our internal workflows and optimized our operations. The solution was tailored perfectly to our unique requirements, and their team went above and beyond to ensure a smooth implementation.
Show more Arty Harjai CEO at HGG (Harjai Global Gurukul)5.0★
Arty Harjai CEO at HGG (Harjai Global Gurukul)5.0★Mobile App Development Review from Arty Harjai
Pixelette Technologies delivered ann exceptional e-learning platform that has improved the way we deliver educational content. The team was professional and responsive, ensuring the project exceeded all expectation.
Show more
Grow Your Sales Pipeline With Human + AI
Founded in 2004 and headquartered in Encino, California, Callbox Inc. is a global leader in outsourced B2B lead generation, appointment setting, and event marketing. With over 20 years of experience and a multilingual team servicing APAC, LATAM, and EMEA, the agency supports medium-sized businesses to [... see all Callbox reviews ]- Location
- Los Angeles, California
- Number of Employees
- 500 - 999
- Portfolios Count
- 100 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsCallbox Services
- Managed Services
- Cybersecurity
- Cloud Consulting
- Digital Marketing
- ERP Consulting
- CRM Consulting
- BPO
- Branding
- Event Marketing
- SEO
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio-thumb-webp.webp)
Cybersecurity Project for Software & IT Services Company Appointment Setting Campaign Causes Rise in Sales-ready Leads for Cyber Security Firm -thumb-webp.webp)
Cybersecurity Project for Software & IT Services Company Malware Hunter Tracked New Leads with Callbox ABM Campaign 
Cybersecurity Project for Software & IT Services Company ABM Amped Up Brand Awareness and Potential Leads for Cybersecurity Leader -thumb-webp.webp)
Cybersecurity Project for Software & IT Services Company Callbox Caused Significant Pipeline Growth for Cybersecurity Leader 
IT Outsourcing Project for Software & IT Services Company Callbox: Successful Partnership with IT Heavyweight 
IT Outsourcing Project for Software & IT Services Company IT Telecom Consultancy Adds Over $1.3M in Sales Pipeline Opportunities
Data sourced from the agency's DesignRush profileAmazon Google Microsoft Workday SAP Telefonica Zendesk opentext Yandex NEC
Reviews verified by DesignRush and sourced from the agency's profileCallbox Reviews & Testimonials
 Joachim Fong Regional Marketing Specialist at Malvern Panalytical5.0★
Joachim Fong Regional Marketing Specialist at Malvern Panalytical5.0★Lead Generation Review from Joachim Fong
For the past year, Callbox has provided us with satisfactory lead generating and lead nurturing services. They were instrumental in securing attendees for our events, scheduling client appointments and facilitating the sale of one of our benchtop systems. Their professionalism in conveying our product attributes and valued solutions to prospective customers has brought us results.
Show more Jonathan Anderson Owner at ABS5.0★
Jonathan Anderson Owner at ABS5.0★Lead Generation Review from Jonathan Anderson
I’ve used Callbox now for about four months for my internet marketing company. The first two months they did not pay off. However with some additional training on my part, they started to close a higher percentage of my target audience. They’re really smart, nice and are really working hard to keep my business. My dedicated team keeps me up-to-date through frequent communications. My R.O.I is getting stronger and my CPA is starting to drop.
Show more Ted Calvin Co-Founder & Vice President at Charted Energy5.0★
Ted Calvin Co-Founder & Vice President at Charted Energy5.0★Appointment Setting Review from Ted Calvin
Charted Energy has enjoyed a productive relationship with Callbox. They have done a great job of helping us target prospects within the markets we serve as well as qualify leads and set up appointments with decision-makers. Callbox has generally exceeded the number of leads per week we expected and provides a good value by enabling our inside sales team.
Show more
Certified Experts, Patented Excellence
Digis is a Software Development company with a team of 200+ professionals dedicated to Custom Development (Web & Mobile) and design. We have a wealth of experience across several industries, particularly in Education, Healthcare, Fintech, E-Commerce, Media & Entertainment, GIS and Automotive. [... see all Digis reviews ]- Location
- New York City, New York
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $39/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 22 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsDigis Services
- Staff Augmentation
- Web Design
- Web Development
- Mobile App Development
- IT Services
- Software Development
- Managed Services
- Cybersecurity
- Product Design
- UI/UX Design
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio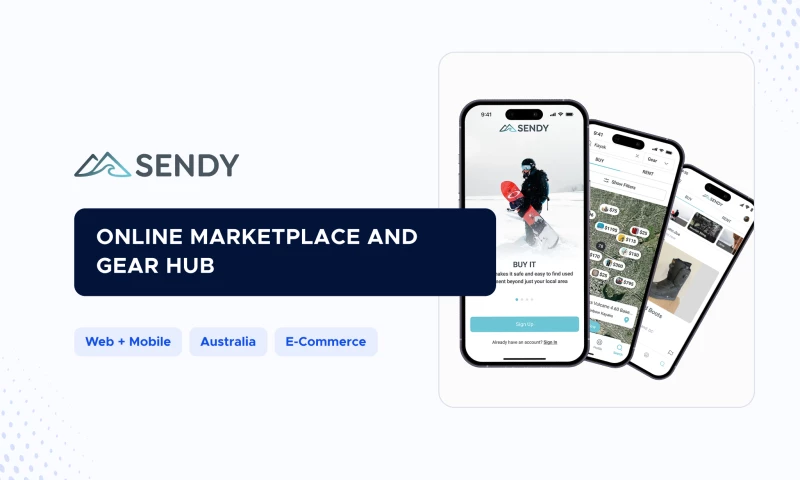
Staff Augmentation Project for eCommerce Company Sports Equipment Marketplace 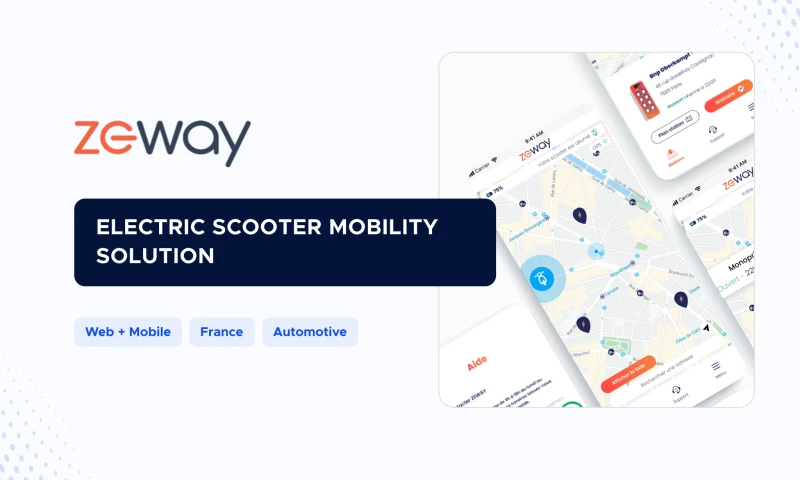
Staff Augmentation Project for Automotive Company Electric Scooter Solution 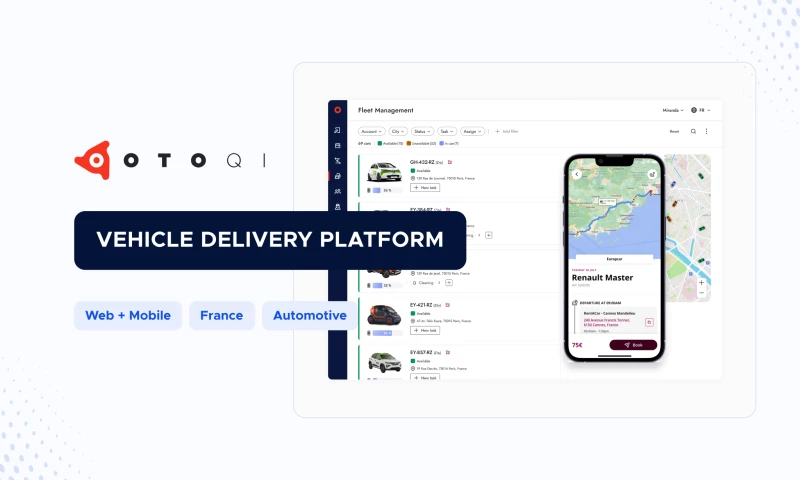
Staff Augmentation Project for Automotive Company Vehicle Delivery Platform 
Staff Augmentation Project for Software & IT Services Company Leading Marketing Platform
Data sourced from the agency's DesignRush profileBlaBlaCar PWC EDP HubSpot SKF. Huma Otoqi ZEWAY
Reviews verified by DesignRush and sourced from the agency's profileDigis Reviews & Testimonials
 Wladimir Wolinski Project Manager at Seven Tips UG & Co. KG5.0★
Wladimir Wolinski Project Manager at Seven Tips UG & Co. KG5.0★UI/UX Design Review from Wladimir Wolinski
Communication was smooth either through our teams communication channel or with the project manager via email. We were in daily contact with the UX/UI designer in form of dailies or when we had to clarify some questions. With the project manager, we had a short conversation every 2 weeks to clarify all possible questions.We personally love to work in a very process-oriented way. Because when we understand how to do something, we usually know how the end result can look like. With Digis, we also had the feeling that they knew what they were doing and how to do it. Every next step was planned from the beginning. If something didn't work in line with our processes, we could readjust it.We were basically satisfied with everything.
Show more Michael Wilson Co-Founder at Part Swap5.0★
Michael Wilson Co-Founder at Part Swap5.0★Website Redesign Review from Michael Wilson
Digis is redesigning our website to a magento based platform to migrate from a Wordpress based platform. Key deliverables include a full discovery document to determine and outline the scope of the work and the magento platform with custom development to fit our needs.Everything has been delivered on time. Danila our project manager has great communication and always responds in a timely manor. We always receive clear explanations and detailed time logs for the work that is done.
Show more Gina Levy CEO at KindraConnect5.0★
Gina Levy CEO at KindraConnect5.0★Mobile App Development Review from Gina Levy
Both the developer and tester have exceeded expectations. Their performance is excellent. Together they eliminated bugs, introduced new features, and ensured that the app is working without problems. Previously, we had many complaints in the app store. Since working with this developer and tester, these complaints about the app functioning and bugs have disappeared.The time zone different is sometimes challenging, since we are in California and they are in Europe.
Show more
ELEKS, a trusted partner for guaranteed software engineering excellence, quality, and transparency.
ELEKS is the partner of choice for many leading enterprises, SMEs and technology challengers. We help businesses elevate their value through custom software development, product design, QA and consultancy services.ELEKS is a trusted partner for guaranteed software engineering excellence. [... see all ELEKS reviews ]- Location
- Chicago, Illinois
- Number of Employees
- 1000 & Up
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 12 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsELEKS Services
- Software Development
- Mobile App Development
- Cloud Consulting
- Cybersecurity
- AI Development
- ERP Consulting
- CRM Consulting
- Product Design
- Big Data Analytics
Data sourced from the agency's DesignRush profileAramex TAIT Acino GRTGaz Autodesk Blackboard Havas ESET Eagle teleologica
Reviews verified by DesignRush and sourced from the agency's profileELEKS Reviews & Testimonials
 John Armstrong Founder, CEO & CTO at Civex5.0★
John Armstrong Founder, CEO & CTO at Civex5.0★Software Development Review from John Armstrong
ELEKS was able to take our vision and help us deliver an app that empowers retail shareholders to make their voices heard. They’ve brought a depth and breadth of technical expertise and user experience design to challenge us on our assumptions on how people would want to interact with the app. From a mobile development perspective, we wanted to go to market with both an Android and an iPhone simultaneously.
Show more Mark Battcock Digital Communication Director at Imerys5.0★
Mark Battcock Digital Communication Director at Imerys5.0★Software Development Review from Mark Battcock
We are very happy with our ELEKS partnership; the dedication of the team is exceptional. We would certainly recommend ELEKS and would be happy to work with them again. In fact, they continue to be our partner for the 2nd phase of the CDX project to add even more customer services to the website.
Show more Huntly Christie CEO at Christie Lites5.0★
Huntly Christie CEO at Christie Lites5.0★Software Development Review from Huntly Christie
What impressed me about ELEKS is the culture. There is a very strong culture of discipline and performance, and software is a profession where discipline is very important. Good software development can only happen with a strong work ethic, and I think the ELEKS team really understands that.
Show more
Your Trusted IT Consulting Partner
CyberSecOp leverages a full suite of information security consulting services for any size business, including security audits, cyber security programs, information security gap analysis, managed IT security, risk management, systems engineering, and more. [... see all CyberSec Op reviews ]- Location
- New York City, New York
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $125/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 5 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsCyberSec Op Services
- Cybersecurity
- IT Services
- Managed Services
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio-thumb-webp.webp)
Cybersecurity Project Helping Healthcare Organizations Protect Patient Records Case Study May 10, 2023 HELPING HEALTHCARE ORGANIZATIONS PROTECT PATIENT RECORDS -thumb-webp.webp)
Cybersecurity Project SECURE SOFTWARE DEVELOPMENT INFRASTRUCTURE -thumb-webp.webp)
Cybersecurity Project SOC-AS-A-PLATFORM (SOCAAP) & MDR SERVICE -thumb-webp.webp)
Cybersecurity Project Cyber Security Threat Hunting -thumb-webp.webp)
Cybersecurity Incident Response Project RETAIL COMPLIANCE SERVICES
Data sourced from the agency's DesignRush profileAltium Wealth GFI Capital RB Investment
Reviews verified by DesignRush and sourced from the agency's profileCyberSec Op Reviews & Testimonials
 Nick Kitchin CEO at Cumulus Energy Storage5.0★
Nick Kitchin CEO at Cumulus Energy Storage5.0★Cybersecurity Review from Nick Kitchin
The Cybersecop team is very skilled and knowledgeable. They also have an excellent reputation, which sets them apart from competitors. Additionally, they have excellent customer service, and we were impressed by their pricing.
Show more Joel Gibbard MBE CEO at OPen Bionics5.0★
Joel Gibbard MBE CEO at OPen Bionics5.0★Compliance Consultancy Review from Joel Gibbard MBE
Cybersecop not only documented our compliance, they helped us better understand which parts of the PCI DSS requirements we needed to comply with and how.
Show more John Sadlowki CEO at SquareOne Energy5.0★
John Sadlowki CEO at SquareOne Energy5.0★Cybersecurity Review from John Sadlowki
Very effective. We were able to fix and identify all issues and receive confirmations instantaneously. And their ability to perform high quality work at a much better price than others in this market.
Show more
Lets build some tech together!
Guiding and helping businesses worldwide build solutions that sell. Genetech is an award-winning custom software development company with almost 2 decades of experience in delivering top-notch tech services, including AI, IoT, Intelligent Apps, Cyber Security, and Tech Talent. [... see all Genetech Solutions reviews ]- Location
- Ann Arbor, Michigan
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 37 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsGenetech Solutions Services
- Software Development
- AI Development
- Mobile App Development
- Staff Augmentation
- Cybersecurity
- Web Development
- WordPress Website Design
- Software Testing
- eCommerce Development
Data sourced from the agency's DesignRush profileDearing Studio Stubgroup NIKOS Global Nephrology Solutions Le Bijou Solutions 8 TheBlueFish.com MicroElec Technical 3PL Systems Inc. My Boracay Guide
Reviews verified by DesignRush and sourced from the agency's profileGenetech Solutions Reviews & Testimonials
 Jason Stern President at Enlightened Media5.0★
Jason Stern President at Enlightened Media5.0★Web Design Review from Jason Stern
This company is a pleasure to work with. They respond timely and have a true expertise in their field. We recommend them for any advanced website code, e-commerce coding, tracking or SEO related projects.
Show more Griffin Joliboix COO at The Basketry by Phina5.0★
Griffin Joliboix COO at The Basketry by Phina5.0★Web Development Review from Griffin Joliboix
The team at Genetech did a great job helping us get our website back on track when updates were pushed through that we were unaware of. These updates caused implications that were problematic to our website performance at the most crucial time of the year for our sales, and their timely work helped out tremendously.
Show more Ramy Hanna CEO at Trinity Design and Build LLC5.0★
Ramy Hanna CEO at Trinity Design and Build LLC5.0★Web Design Review from Ramy Hanna
Best team to contact with, Easy to communicate, They take u step by step to complete our project in an easy efficient way, Reasonable price, I recommend them
Show more
Award-Winning IT & Cybersecurity
TruAdvantage is a Bay Area based, award-winning IT firm specializing in managed IT, managed Cybersecurity, cloud solutions and strategic IT . Our passion is to bring enterprise-level productivity, simplicity, scalability, and security to over 100 businesses that have chosen us as their IT partner. [... see all TruAdvantage reviews ]- Location
- San Jose, California
- Number of Employees
- Under 49
- Average Hourly Rate
- $165/hr
- Portfolios Count
- 8 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsTruAdvantage Services
- Managed Services
- Cybersecurity
- IT Services
- Staff Augmentation
- Business Consulting
- Cloud Consulting
- IT Compliance Solution
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio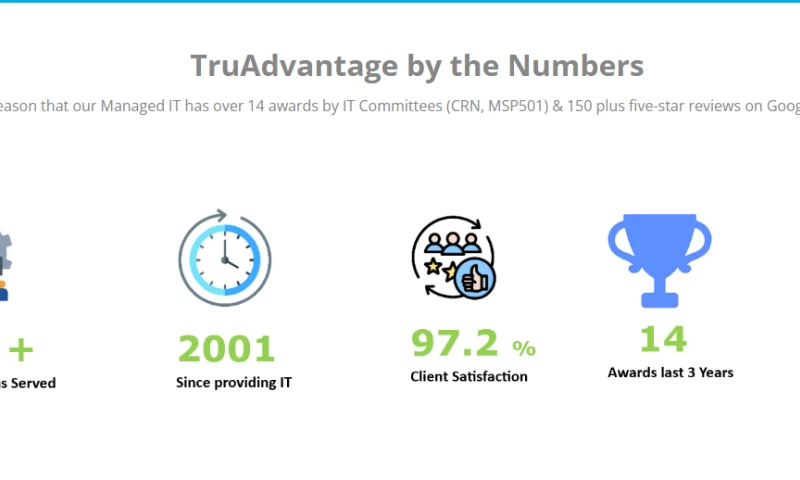
Cybersecurity Project TruAdvantage by the Numbers 
Cybersecurity Project Managed IT & Cybersecurity 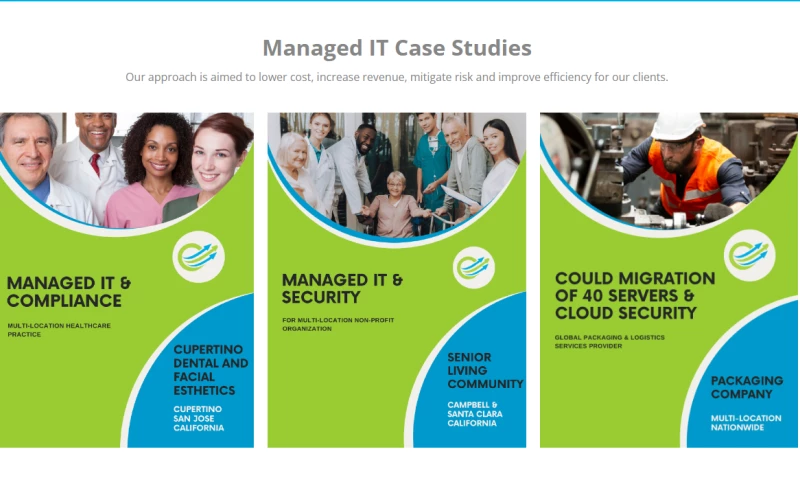
IT Services Project Managed IT Case Studies 
Managed Service Providers Project Awards and Meet the Team 
IT Services Project Watch Our Clients Success Stories 
Managed Service Providers Project Managed IT, Cybersecurity & Compliance
Data sourced from the agency's DesignRush profileMinimally Invasive Surgical Solutions (MISS) Santa Clara Methodist Retirement Foundation (SCMRF Kern Radiology
Reviews verified by DesignRush and sourced from the agency's profileTruAdvantage Reviews & Testimonials
.png) Rhosel Dayrit Practice Administrator at Neurospine Institute Medical Group5.0★
Rhosel Dayrit Practice Administrator at Neurospine Institute Medical Group5.0★IT Services Review from Rhosel Dayrit
My top 3 things about TruAdvantage:1) The single biggest benefit is Security. Since we are a medical field office, our primary concern is securing patient’s files and account information. Second would be backup. Since most of our work is online it is important to have back up on all files electronic and non-electronic.2) Customer service is excellent and dealing with our issue at a moment’s notice is beyond expectation.3) I would highly recommend for them to try it out. they will see a big difference in the proficiency of work, the team itself and the care to their customer’s need.
Show more.png) Mohammad Shenasa Executive and Cardiovascular Specialist at Southbay Cardio Vascular Group5.0★
Mohammad Shenasa Executive and Cardiovascular Specialist at Southbay Cardio Vascular Group5.0★IT Services Review from Mohammad Shenasa
Switching from our previous IT vendor to TruAdvantage seemed like a daunting process but TruAdvantage addressed this concern from our initial meeting and made it very smooth. Four years later and I can assertively say choosing TruAdvantage has been one of my best business decisions.
Show more.png) Joseph Dunn CEO at EndogenX5.0★
Joseph Dunn CEO at EndogenX5.0★IT Services Review from Joseph Dunn
Before TruAdvantage as our IT advisor, my staff used to spend way too much time on IT issues. Now with their support and process my staff is way more prod120uctive and is back to the business of research and inventing great pharmaceutical products.
Show more
Unlock Tomorrow
GET OUR EXPERT CONSULTING AND SOFTWARE ENGINEERING SERVICES [... see all Computools reviews ]- Location
- New York City, New York
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 25 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsComputools Services
- Software Development
- Mobile App Development
- Web Development
- Cloud Consulting
- AI Development
- Staff Augmentation
- Big Data Analytics
- Product Design
- Cybersecurity
- Blockchain
Data sourced from the agency's DesignRush profileVisa IBM Bombardier Dior British Council Caribbean Bank MeterSnap Dental Health BeEducated Green Energy
Reviews verified by DesignRush and sourced from the agency's profileComputools Reviews & Testimonials
 Marie Jenkins CO-Founder & Sourcing Manager at Valo Recruitment5.0★
Marie Jenkins CO-Founder & Sourcing Manager at Valo Recruitment5.0★Mobile App Development Review from Marie Jenkins
Working with Computools has been a truly rewarding experience. Their team demonstrated professionalism, deep technical expertise, and strong communication throughout our project. They took the time to understand our needs and delivered a custom solution that exceeded expectations.What impressed us most was their ability to combine innovative thinking with structured execution. Computools didnt just provide software developmentthey offered valuable consulting that helped us improve efficiency and customer experience. The final product was delivered on time, met all compliance requirements, and added measurable value to our business.We highly recommend Computools to any company looking for a reliable, forward-thinking software partner.
Show more Nicole Siaw European Hydrogen Market Analyst at Aurora Energy Research5.0★
Nicole Siaw European Hydrogen Market Analyst at Aurora Energy Research5.0★Web Development Review from Nicole Siaw
Computools developed a customized CRM system that significantly improved our financial agencys operations. Their team was highly professional, responsive, and detail-oriented throughout the process. The solution streamlined client management, boosted efficiency, and provided valuable insights for decision-making. We were impressed with their technical expertise and commitment to delivering on time.
Show more Frank Tufail Smith FS Transaction Services, Manager at PwC at PwC5.0★
Frank Tufail Smith FS Transaction Services, Manager at PwC at PwC5.0★Web Development Review from Frank Tufail Smith
We partnered with Computools to develop a new CRM system for our financial agency, and the results have been outstanding. Their team quickly understood our needs and delivered a user-friendly solution that has transformed our client management process.The CRM provides a comprehensive view of our clients, enhances our communication, and streamlines our operations. We've seen a significant improvement in response times and overall efficiency. I highly recommend Computools for any software development needs!
Show more
Doing IT Right Since 2005.
Capital Techies, established in 2005, fills the void of sub-par IT support for small businesses and non-profits in the Washington DC area. Through the Managed Service Provider model, we offer specialized and comprehensive IT solutions, addressing the ever-changing technology landscape that full-time, in-house [... see all Capital Techies reviews ]- Location
- Fairfax, Virginia
- Number of Employees
- Under 49
- Average Hourly Rate
- $199/hr
- Minimal Budget
- $1,000 - $10,000
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsCapital Techies Services
- Cybersecurity
- IT Services
- AI Development
Data sourced from the agency's DesignRush profileArlington Country Public Schools Generation You Employ Mckinsey.org C2 Construction Springboard Enterprises
Reviews verified by DesignRush and sourced from the agency's profileCapital Techies Reviews & Testimonials
 Aleksandra Puzyno Manager at DYWIDAG Concrete Technologies5.0★
Aleksandra Puzyno Manager at DYWIDAG Concrete Technologies5.0★IT Services Review from Aleksandra Puzyno
Capital Techies' experience with us Their professionalism, knowledge, and commitment to protecting our digital assets struck us from the first minute we interacted with their staff. We felt at ease knowing that our data was in capable hands because of their proactive approach to spotting and removing risks. Their continuous assistance has been nothing short of exceptional, and the smooth integration of their technologies into our current infrastructure beyond our expectations. Our confidence and security in our online activities are enhanced by Capital Techies.
Show more James Rodriguez Chief Executive Officer at EmpowerTech LLC5.0★
James Rodriguez Chief Executive Officer at EmpowerTech LLC5.0★Cybersecurity Review from James Rodriguez
Our encounters with Capital Techies We were immediately pleased by their team's professionalism, knowledge, and commitment to protecting our digital assets. Our data was in good hands, and their proactive approach to identifying and mitigating dangers offered us piece of mind. Our expectations were surpassed by the smooth integration of their technologies into our current infrastructure, and their continuous support has been excellent. We feel safe and secure in our online pursuits because of Capital Techies.
Show more Christopher T Co-Founder at Luxury Fire5.0★
Christopher T Co-Founder at Luxury Fire5.0★IT Services Review from Christopher T
Capital Techies' follow-through and response have pleased us. Internal stakeholders at Luxury Fire expressed satisfaction with Capital Techies' long-standing collaboration. Additionally, Luxury Fire notes that its ability to provide excellent recommendations is made possible by Capital Techies' dependability, organization, devotion, and technological know-how.
Show more
World-Class Software Development Company
Datazo InfoTech is an Award-Winning & World-Class Software Development Company with Engineering Hubs in NYC. We are committed to providing end-to-end IT services with a mission to solve complex software engineering problems. [... see all Datazo InfoTech reviews ]- Location
- Dhaka, Bangladesh
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $150/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 12 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsDatazo InfoTech Services
- IT Services
- Cybersecurity
- Software Development
- AI Development
- eCommerce Development
- Web Development
- Blockchain
- Mobile App Development
- VR/AR
- IT Compliance Solution
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project for Social Networks Company Secure Mobile Messenger App Development 
Cybersecurity Project for Software & IT Services Company Migration Of Aes File security Software For Macos To Xamarin 
Cybersecurity Project for Finance Company Firewells For a As Consumer Reporting Agency -thumb-webp.webp)
IT Services Project for Finance Company SharePoint Consulting for a Financial Advisory Firm -thumb-webp.webp)
IT Services Project for Corporate Services Company IT Consulting for Enterprise Application Integration for a Multi-Industry Corporation
Data sourced from the agency's DesignRush profileFinancial Indutry IT Industry Small Buiness Industry
Reviews verified by DesignRush and sourced from the agency's profileDatazo InfoTech Reviews & Testimonials
 Bobby Neil Senior Director Global Services at Iron Mountain5.0★
Bobby Neil Senior Director Global Services at Iron Mountain5.0★Software Development Review from Bobby Neil
The redesign of our solution was warmly welcomed by the users that were involved in its beta-testing process. We appreciate efficient communication, quick reactions to suggestions and their Agile Scrum approach to project management and definitely the portfolio and skills of the designer that was working on our project! The prepared UI hit the point. Also, the engagement and quick introduction of all changes made working on a project much more productive and less challenging.
Show more Matthew Grant Vice President at Impact XM5.0★
Matthew Grant Vice President at Impact XM5.0★Software Development Review from Matthew Grant
The three major tools that our employees use daily are all connected via the same interface, which is a huge success. I also get a lot of anecdotal feedback from people about how fast and responsive the system is. Enhancements and features are being implemented very quickly, and people feel that theyre being heard by our team and Datazo. If we ask for something, then it will be delivered. They've been terrific in that respect.
Show more Eudis Anjos Head of Engineering at SS&C Technologies5.0★
Eudis Anjos Head of Engineering at SS&C Technologies5.0★Software Development Review from Eudis Anjos
Its difficult to measure success, since we had just launched the app last week. However, there are a number of people who have contacted us and were interested in having a meeting to know more. In that respect, weve achieved our main goal of calling the attention of mobile network operators and mobile money providers. Weve accomplished the level of success that we targeted for initially. Everyone was congratulating us for the UI/UX of the app and nobody came to us with any problems, which is a very good metric.
Show more
Top Cyber Security Company in Australia
Borderless CS is a leading cybersecurity company based in Australia. Borderless Creative Solutions is a dynamic agency that brings imagination to life through compelling design and strategic communication. Our team is committed to helping businesses transcend boundaries with innovative branding, digital [... see all Borderless CS reviews ]- Location
- Melbourne, Australia
- Number of Employees
- Under 49
- Average Hourly Rate
- $200/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 1 Project Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsBorderless CS Services
- Cybersecurity
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project Identity and Access Management (IAM) Implementation Project
Data sourced from the agency's DesignRush profileColes NAB IBM
Reviews verified by DesignRush and sourced from the agency's profileBorderless CS Reviews & Testimonials
 Anthony Treyman Marketing Coordinator at Kids in the Game5.0★
Anthony Treyman Marketing Coordinator at Kids in the Game5.0★Cybersecurity Review from Anthony Treyman
Their knowledge not only strengthened our cybersecurity defenses but also created confidence in our workforce. The measurable results and their distinctive proactive strategy demonstrate their dedication to greatness. While there were small communication issues, they did not overwhelm the great value they delivered to our organization. We strongly recommend Borderless cs to everyone looking for high-quality cybersecurity solutions.
Show more Jorge Guzman Brand Ambassador at Vaporesso5.0★
Jorge Guzman Brand Ambassador at Vaporesso5.0★Cybersecurity Review from Jorge Guzman
While our experience with Borderlescs was overwhelmingly positive, there is always room for improvement. One area they could consider enhancing is the documentation of their processes and solutions. Having more detailed documentation would help us better understand the implemented measures and would be useful for future reference.
Show more Jeremy Huffman Director of Technology at Sprout5.0★
Jeremy Huffman Director of Technology at Sprout5.0★Cybersecurity Review from Jeremy Huffman
Their comprehensive approach, technical expertise, and commitment to our security stood out. The positive impact on our cybersecurity measures and the peace of mind that came with their service made the partnership incredibly valuable. Despite minor areas for improvement, we have no hesitation in recommending Borderlescs to other businesses seeking top-notch cybersecurity solutions tailored to their industry-specific requirements.
Show more
Managed IT Support & Consulting Services Company
Rivell is a leading Managed IT Services Provider (MSP) based in New Jersey, serving clients in North America. With a team of experienced IT professionals, Rivell offers a comprehensive suite of IT solutions tailored to meet each client's unique needs. [... see all Rivell reviews ]- Location
- Mantua Township, New Jersey
- Number of Employees
- Under 49
- Average Hourly Rate
- $40/hr
- Portfolios Count
- 4 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsRivell Services
- IT Services
- Cloud Consulting
- Cybersecurity
- Managed Services
- Software Development
- IT Compliance Solution
- Mobile App Development
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Managed Service Providers Project Managed IT Services For LISCIOS BAKERY 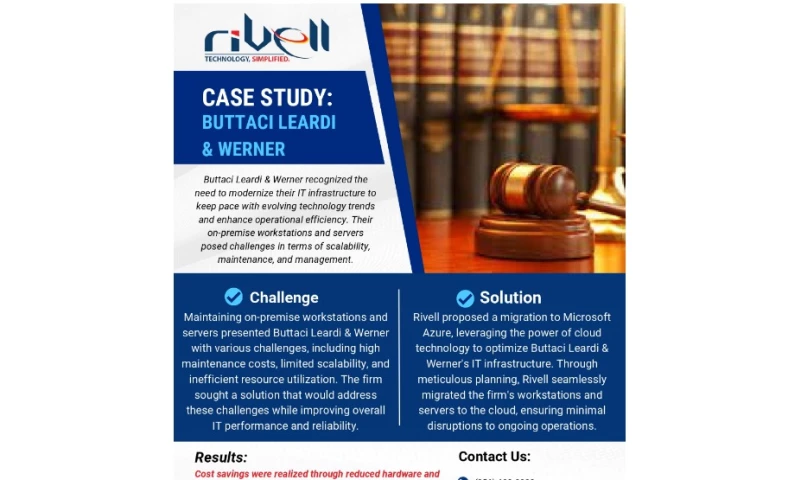
Managed Service Providers Project Managed IT Services For BUTTACI LEARDI & WERNER 
Managed Service Providers Project What our clients say about us 
Managed Service Providers Project Project with Law firm
Data sourced from the agency's DesignRush profileIT Industry Film Industry Education Industry Healthcare Small Businesses State and Local Government Law Firms Non - Profits Fintech Retail
Reviews verified by DesignRush and sourced from the agency's profileRivell Reviews & Testimonials
 Hamed Sadeghian CEO at Nearfield instrument5.0★
Hamed Sadeghian CEO at Nearfield instrument5.0★Mobile App Development Review from Hamed Sadeghian
Our world's first linked carsharing marketplace has been made possible in large part by the technical expertise and inventiveness of their team. Rivell not only met but surpassed our expectations by providing a mobile app that is easy to use and flawlessly integrated, enabling individuals to carpool anywhere. With open communication, prompt delivery, and a sincere commitment to our goal, our cooperation with Rivell has shown to be a useful one.
Show more Giorgio Tinacci CEO at Casavo5.0★
Giorgio Tinacci CEO at Casavo5.0★Cybersecurity Review from Giorgio Tinacci
It was a pleasure working with Rivell on the internet testing automation for our real estate services company. The organization developed a strong system to effectively handle quality assurance (QA) by offering both manual testing and test automation. Thanks to Rivell's proactive and adaptable attitude, the deployment of a new portal was made possible by its smooth integration into our Agile process. The agency's professionalism and level of experience pleased us.
Show more Hank Sorensen CEO at iad florida5.0★
Hank Sorensen CEO at iad florida5.0★IT Services Review from Hank Sorensen
Our organization hired Rivell developers and a project manager to provide IT services for assisting IAD Florida in locating accommodation. During the project, there was close collaboration between our team and Rivell. Initially, both teams worked together to plan the construction of the product and gather required project data. Subsequently, their team added features to our software. Finally, after successful launch, our client expressed satisfaction with the outcome. This collaboration appears to have been effective in achieving the project's goals.
Show more
Stop trusting others with your security.
Eclypses's MTE Technology, offers a new level of cyber security by replacing actual data with instantly obsolete, meaningless random streams of values. Through this process, Eclypses MTE Technology protects an organization's most critical and valuable asset, its data, from current and future cyber threats. [... see all Eclypses reviews ]- Location
- Boston, Massachusetts
- Number of Employees
- Under 49
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsEclypses Services
- Cybersecurity
Data sourced from the agency's DesignRush profileApexaiQ Voatz First Rate Archethought Liveplex Beasy WholesalePayroll WILLPORTtrust
Reviews verified by DesignRush and sourced from the agency's profileEclypses Reviews & Testimonials
.png) Lokesh Aggarwal CEO at APEXA IQ5.0★
Lokesh Aggarwal CEO at APEXA IQ5.0★Cybersecurity Review from Lokesh Aggarwal
Understanding security and remaining on top of new and upcoming cyber threats is extremely important to us at Apexa iQ. We are excited to be partnering with Eclypses and utilizing their MTE Technology. Leveraging this powerful data security is a business differentiator that will allow us to provide the full endpoint-to-endpoint security necessary to protect both our customers as well as our own mobile, web, and IoT devices.
Show more Doris Schwartz Founder and CEO at WILLPORTtrust5.0★
Doris Schwartz Founder and CEO at WILLPORTtrust5.0★Cybersecurity Review from Doris Schwartz
What an efficient integration process! We're looking forward to the expansion of this security software within all our product offerings.
Show more Nimit Sawhney CEO and Co-Founder at Voatz5.0★
Nimit Sawhney CEO and Co-Founder at Voatz5.0★Cybersecurity Review from Nimit Sawhney
Eclypses has been an invaluable partner of Voatz since 2020 when it assisted in offering a 'Quantum Resistant' security solution in several elections that we oversaw. Its MTE technology was integrated into aspects of our mobile voting infrastructure to future-proof the security of the network communication. We have also collaborated with Eclypses on a quarterly webinar program that has brought together some of the top minds in cybersecurity and quantum computing and has been viewed by thousands of scientists, educators, policymakers, activists, and other parties interested in the marriage of elections and emerging technologies.
Show more
Award-winning mobile app development agency
We've delivered over 200 projects in 15 years to do with mobile apps, web and motion. [... see all Internut reviews ]- Location
- Gold Coast, Australia
- Number of Employees
- Under 49
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 3 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsInternut Services
- Mobile App Development
- Web Development
- Web Design
- Cybersecurity
- Video Production
- IT Services
Data sourced from the agency's DesignRush profileAir Asia HSBC Lexus Digi PNB CIMB Bank Coway Petronas Bank Rakyat FGV
Reviews verified by DesignRush and sourced from the agency's profileInternut Reviews & Testimonials
 Keith Butler Marketing Manager at Upsellz Technologies5.0★
Keith Butler Marketing Manager at Upsellz Technologies5.0★Mobile App Development Review from Keith Butler
We hired Internut to develop an interactive top of the line e-commerce app for our company. They were always reachable at any time and at any stage of the whole project. They never let us down on any milestone of the project.
Show more Utpal Joshi Operations Manager at Hungry Landfill5.0★
Utpal Joshi Operations Manager at Hungry Landfill5.0★Mobile App Development Review from Utpal Joshi
In 2020 I started developing a mobile app with a developer based in Melbourne, but the project had to stop for they went into operational issues. So I decided to look for the other developer to continue the project. In 2022 I contacted Internut to handle the project, we start everything all over again from scratch and hoping it is ready to launch in 2021. The project manager that we were assigned was easy to communicate with and provided us frequent updates.
Show more Sharon Baek Marketing Manager at Undisclosed5.0★
Sharon Baek Marketing Manager at Undisclosed5.0★Mobile App Development Review from Sharon Baek
Internut is the place to build your game.
Show more
Turning Digital Ideas into Powerful & Lucrative Realities
Wezom offers web and mobile development services, providing solutions that address business challenges, meet market demands, enhance internal operations, and stay up-to-date with digital trends. [... see all Wezom reviews ]- Location
- Chicago, Illinois
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $49/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 23 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsWezom Services
- IT Services
- Software Development
- Mobile App Development
- Web Design
- eCommerce Development
- Cybersecurity
- UI/UX Design
- Business Consulting
- ERP Consulting
- Big Data Analytics
Data sourced from the agency's DesignRush profileMetinvest John Deer Roshen INTERPIPE Aptiv Toyota Material Handling SCHWARZ LOGISTICS Cooper & Hunter OneVoiPlanet Nova Lines
Reviews verified by DesignRush and sourced from the agency's profileWezom Reviews & Testimonials
 Elena Nosenko Lead Account Manager at Elogic Commerce5.0★
Elena Nosenko Lead Account Manager at Elogic Commerce5.0★IT Services Review from Elena Nosenko
Elogic Commerce highly recommends WEZOM as a trusted partner for CRM system development. They demonstrated a deep understanding of our needs and delivered a custom solution that optimized workflows, enhanced client engagement and ensured scalability.WEZOMs professionalism, technical expertise, and dedication made the collaboration seamless and productive. We confidently recommend them to any business seeking a reliable partner for CRM development.
Show more Victoria Savchuk Marketing Manager at Alcor5.0★
Victoria Savchuk Marketing Manager at Alcor5.0★Software Development Review from Victoria Savchuk
Alcor is pleased to recommend WEZOM as a reliable partner in the development and implementation of an R&D center management system.WEZOM demonstrated a deep understanding of our business needs and successfully implemented a platform
Show more Violeta Baranovska Head of Marketing at VT Labs5.0★
Violeta Baranovska Head of Marketing at VT Labs5.0★Software Development Review from Violeta Baranovska
VT Labs is incredibly impressed with WEZOM's expertise in developing custom VR/AR marketing and sales tools for our client. The collaboration was fascinating and successful.We were looking for ways to showcase VR/AR technology in a more engaging and immersive manner. WEZOM listened to our needs and created stunning VR experiences and interactive sales presentations that truly capture the power of VR/AR.
Show more
Exoft is a software house with a significant background in web and mobile development.
Exoft is a custom software development company that provides solutions to address various business needs. [... see all Exoft reviews ]- Location
- Lviv, Ukraine
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $40/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 14 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsExoft Services
- Software Development
- Web Development
- Software Testing
- Cybersecurity
- IT Services
- AI Development
- ERP Consulting
- Staff Augmentation
- Managed Services
- DevOps Consulting
Data sourced from the agency's DesignRush profileBridgestone PlugSurfing Eloquenti
Reviews verified by DesignRush and sourced from the agency's profileExoft Reviews & Testimonials
 David Veksler Principal Web Architect at Undisclosed4.5★
David Veksler Principal Web Architect at Undisclosed4.5★Educational Review from David Veksler
We are happy with the work. We worked with a number of developers, and when we were not happy with a developer, our Exoft contact worked to find someone to meet our needs.
Show more Colin Stone Developer at ANALEC Infotech Private Ltd5.0★
Colin Stone Developer at ANALEC Infotech Private Ltd5.0★Web Development Review from Colin Stone
Exoft bring strong engineering talent to bear on our projects. They are always willing to go the extra mile to meet our expectations.
Show more Boris Jinjolava CEO at ViClinic Inc4.8★
Boris Jinjolava CEO at ViClinic Inc4.8★Software Development Review from Boris Jinjolava
Exoft has successfully supported us to push our business forward. They bounce ideas off each other and give feedback and context to help in tech areas. Moreover, theyre approachable, responsive partners, and the team stands out for their expertise. It feels more like an internal team than an outsourcing relationship. thank you.
Show more
Driving Digital Transformation with Advanced Tech
Unified Infotech is a 14-year-old, multi-award winning digital transformation partner. We turbocharge business growth for Fortune 500 companies, multinational corporations (MNCs), small and medium-sized enterprises (SMEs), and Startups using emerging tech and streamlined digital processes. [... see all Unified Infotech reviews ]- Location
- New York City, New York
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 16 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsUnified Infotech Services
- Software Development
- Web Development
- Mobile App Development
- Web Design
- eCommerce Development
- Staff Augmentation
- IT Services
- Blockchain
- AI Development
- Cybersecurity
Data sourced from the agency's DesignRush profileCitibank NBCUniversal United Nations McGraw Hill Colorcon Johnson Lambert CQ fluency
Reviews verified by DesignRush and sourced from the agency's profileUnified Infotech Reviews & Testimonials
 Subroto Mukherjee General Manager HR, Admin & IT at Tuaman Engineering Limited5.0★
Subroto Mukherjee General Manager HR, Admin & IT at Tuaman Engineering Limited5.0★Web Development Review from Subroto Mukherjee
Unified Infotech designed and developed a website for an engineering company. Unified Infotech successfully developed the client's website. The team was proactive and dedicated. Unified Infotech provided periodic updates about the site's development and was responsive to the client through email and virtual and in-person meetings.
Show more Juliette Rothera Associate Director, Marketing at Voz Advisors5.0★
Juliette Rothera Associate Director, Marketing at Voz Advisors5.0★Web Design Review from Juliette Rothera
The team was highly collaborative in the design process. They listened, understood, and executed the initial scope of the project. Unified Infotech takes responsibility for their work and immediately corrects any oversights. The new website was loved by all the stake holders and significantly reduced bounce rates while increasing customer inquiries..
Show more Gustavo Lima Founder & CEO at Risposta5.0★
Gustavo Lima Founder & CEO at Risposta5.0★Mobile App Development Review from Gustavo Lima
The most impressive thing about the team is their desire to deliver and to please their client. The product which they have delivered has been a great commercial success
Show more
Innovating Success Through Technology & Blockchain.
InvoZone provides comprehensive software development consulting services for businesses, startups, and enterprises. [... see all InvoZone reviews ]- Location
- Pembroke Pines, Florida
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $45/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 28 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsInvoZone Services
- Mobile App Development
- Software Development
- eCommerce Development
- Blockchain
- AI Development
- UI/UX Design
- ERP Consulting
- DevOps Consulting
- VR/AR
- Cybersecurity
Data sourced from the agency's DesignRush profileStitch Kamoota Global Reader Homepie Column Anakeed Mart Meridio Stakester Shield Republic
Reviews verified by DesignRush and sourced from the agency's profileInvoZone Reviews & Testimonials
 Wiley Jones Co-Founder at Doss5.0★
Wiley Jones Co-Founder at Doss5.0★Mobile App Development Review from Wiley Jones
The app launched successfully six months ago and is now actively used by over 300employees. We got a very good response from the end users as well.
Show more Tessa Young Product Manager at Tiny Genius5.0★
Tessa Young Product Manager at Tiny Genius5.0★Mobile App Development Review from Tessa Young
Working with InvoZone for my web app development project was an awesome experience. Right from the beginning of our partnership, they made everything super easy to understand. Their commendable Project Managers carefully listened to whatever I wanted to add and kept notes of all my suggestions. They provided us with every feature we needed and gave us some interesting ideas as well. Throughout the duration of my project, I was pretty much in the loop with the project and knew what was happening with our product development. It was great to see how things were coming along, loved working with them and I see a long-term future of our partnership.
Show more Angelina Sophia Product Head at Custom Box Makers5.0★
Angelina Sophia Product Head at Custom Box Makers5.0★eCommerce Development Review from Angelina Sophia
We thank InvoZone for their prompt response. Their team built our packaging ecommerce store from scratch. Their developers seamlessly integrated additional features as well as helped our in-house team with fixing bugs and coding errors. All in all, their team worked swiftly and professionally, coming up with robust solutions for each blocker during the process. If anyone is looking to develop a ecommerce store, InvoZone provides exceptional services. So, go ahead and connect with them.
Show more
Managed I.T. Services & Cybersecurity Solutions Since 1994
LME Services provides Managed IT Services, Cybersecurity, Ai Automation and Compliance Consulting since '94. [... see all LME Services reviews ]- Location
- Hoffman Estates, Illinois
- Number of Employees
- Under 49
- Average Hourly Rate
- $150/hr
- Portfolios Count
- 8 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsLME Services Services
- Managed Services
- IT Services
- Cybersecurity
- Cloud Consulting
- IT Compliance Solution
- Business Consulting
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project for Health Care Company Cybersecurity Implementation 
Cybersecurity Project for Real Estate Company Cybersecurity Implementation 
Cybersecurity Project for Corporate Services Company SOC2 Compliance Project 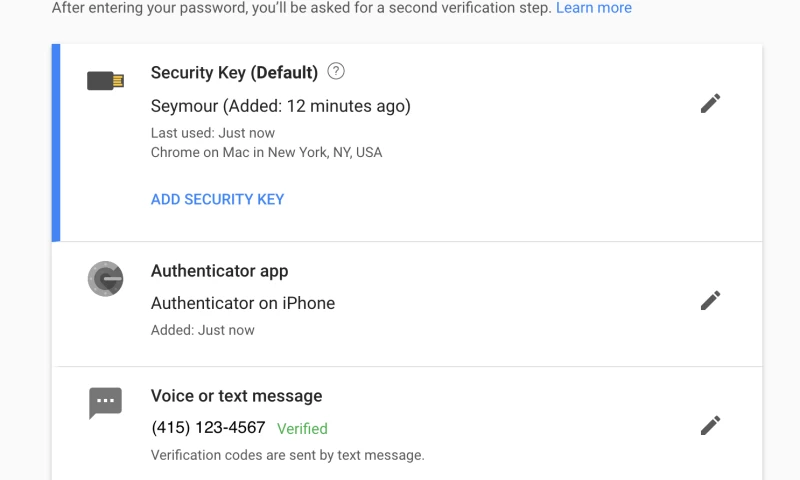
Cybersecurity Project for Nonprofit Company Enabling Multi-Factor Authentication -thumb-webp.webp)
IT Consulting Project for Real Estate Company MSP Services -min-thumb-webp.webp)
IT Services Project for Health Care Company Tech Refresh for Dispensary
Data sourced from the agency's DesignRush profileSPK Law Prairie Contractors Habitat for Humanity Swap-O-Rama Packback SATC, LLC Skokie Country Club Lake Shore Country Club Tuf Tite Subway of Chicago
Reviews verified by DesignRush and sourced from the agency's profileLME Services Reviews & Testimonials
 Michael Held CEO, Founder at LifeSpeak Inc.5.0★
Michael Held CEO, Founder at LifeSpeak Inc.5.0★Cybersecurity Review from Michael Held
LME SERVICES excels in the realm of project management. Their budgetary approach has been commendable, and their adherence to schedules has been impeccable. Our means of communication, primarily through Zoom and emails, have proven effective. Since collaborating with them, we have experienced no security breaches, a testament to their expertise. I am thoroughly satisfied with the meticulousness and communicative nature of LME SERVICES.
Show more Gary Hoffman President at Advanced Power Technologies5.0★
Gary Hoffman President at Advanced Power Technologies5.0★Cybersecurity Review from Gary Hoffman
We are incredibly astounded by the exceptional work performed by Lme Services. Their profound exploration of our security systems and databases surpassed our expectations. Lme Services astutely presented us with a comprehensive 100-page dossier, shedding light on their meticulous processes and offering invaluable recommendations to rectify the vulnerabilities in our system. These recommendations have been promptly implemented within our company, significantly enhancing our cybersecurity measures
Show more Tom Loveless President and CEO at VisionWeb5.0★
Tom Loveless President and CEO at VisionWeb5.0★Software Development Review from Tom Loveless
LME SERVICES promptly delivers top-notch resources of exceptional quality. LME SERVICES was engaged to augment our existing workforce for the development and enhancement of our Electronic Health Records (EHR) and Practice Management products. LME SERVICES excels in providing high-caliber resources promptly. We swiftly initiated the hiring process upon engaging with them, enabling us to onboard talented professionals swiftly. Highly recommend them !!
Show more
Your Vision Our Mission
We are your partner that transforms your ideas into digital products. We help your business scale up and become more profitable through technology utilization. We have seen many businesses fail and use those experiences to help improve your business offering through technology. [... see all Motomtech reviews ]- Location
- Salt Lake City, Utah
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $45/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 5 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsMotomtech Services
- Web Development
- Software Development
- Mobile App Development
- Cybersecurity
- Big Data Analytics
- IT Services
- UI/UX Design
Data sourced from the agency's DesignRush profileSpaceIQ Agreed Software Paramount Acceptance PurpoSolver Firstmile
Reviews verified by DesignRush and sourced from the agency's profileMotomtech Reviews & Testimonials
 Amanda Garceau Vice President of Engineering at HUSL Digital5.0★
Amanda Garceau Vice President of Engineering at HUSL Digital5.0★Software Development Review from Amanda Garceau
Motomtech developed an efficient automated lead generation tool that seamlessly captures and qualifies leads from multiple online sources. The software integrated smoothly with our sales pipeline, boosting our lead flow and saving valuable time. Their team was responsive and delivered the project on schedule, exceeding our expectations.
Show more Russell Millar CEO & Founder at Millar Property Consultants Ltd5.0★
Russell Millar CEO & Founder at Millar Property Consultants Ltd5.0★Big Data Analytics Review from Russell Millar
Their team delivered actionable insights on land value patterns, buyer behavior, and strategic development zones. The reports were clear, data-rich, and timely. Their professionalism and deep analytical capabilities significantly enhanced our planning and decision making processes. Highly recommended.
Show more Ihor Kubalskyi Vice president at QBEIN.net5.0★
Ihor Kubalskyi Vice president at QBEIN.net5.0★Web Development Review from Ihor Kubalskyi
They built a sleek, professional website that perfectly reflects our brand and services at QBEIN.net. Their team was attentive, timely, and easy to work with. The final result exceeded our expectations and has strengthened our online presence.
Show more
Appikr Labs Leading Mobile App Development Company
Appikr is the top choice for app development worldwide. We've eliminated decision-making dilemmas for countless clients by creating outstanding apps tailored to their business needs. With a track record of delivering over 500 high-performing apps across the globe, we continue to lead in the UK, US, UAE [... see all Appikr Labs reviews ]- Location
- Dubai, United Arab Emirates
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 44 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsAppikr Labs Services
- Blockchain
- Software Development
- Software Testing
- Mobile App Development
- eCommerce Development
- Web Development
- AI Development
- CRM Consulting
- Cybersecurity
- DevOps Consulting
Data sourced from the agency's DesignRush profileBest Ride Cabify Curb Arab Chat Free Dating Mingle2 Zoosk UAE Property Trulia Rent MAF
Reviews verified by DesignRush and sourced from the agency's profileAppikr Labs Reviews & Testimonials
 Sajid Mohamed Head of Service Delivery at Gravity Payments5.0★
Sajid Mohamed Head of Service Delivery at Gravity Payments5.0★Mobile App Development Review from Sajid Mohamed
We engaged Appikr Labs for a mobile app development project, and the results were outstanding. Their team's expertise and commitment to delivering a high-quality app were evident throughout the entire process. I highly recommend Appikr Labs to anyone looking for a reliable app development partner.
Show more Layla Zouhair Vice President of Product Management at Nomadia5.0★
Layla Zouhair Vice President of Product Management at Nomadia5.0★Mobile App Development Review from Layla Zouhair
Appikr Labs mobile app development team has exceeded our expectations with their innovative approach and technical proficiency. They have created a cutting-edge mobile app that has enhanced our customer engagement and boosted our brand visibility. Their dedication to delivering top-notch results makes them a go-to choice for mobile app development projects.
Show more Shamsid Deen Chief Technology Officer at SFL Corporation Ltd5.0★
Shamsid Deen Chief Technology Officer at SFL Corporation Ltd5.0★Mobile App Development Review from Shamsid Deen
Appikr consistently delivered items on time and maintained strong communication. Their responsiveness to our needs, whether for technical support or custom feature development, was highly commendable. The collaboration with Appikr resulted in a notable 40% reduction in fuel consumption, a 30% increase in on-time deliveries, and a 25% improvement in fleet operator satisfaction ratings. These tangible outcomes signify the project's success in enhancing fleet management for businesses.
Show more
Innovate Today to Lead Tomorrow.
LeverX, an SAP Gold Partner, brings unparalleled expertise nurtured since 2004, delivering successful projects across manufacturing, automotive, and more. [... see all LeverX reviews ]- Location
- Miami, Florida
- Number of Employees
- 1000 & Up
- Average Hourly Rate
- $75/hr
- Portfolios Count
- 26 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsLeverX Services
- IT Services
- CRM Consulting
- ERP Consulting
- Cloud Consulting
- Software Development
- Staff Augmentation
- Mobile App Development
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
SAP S/4HANA Project SAP S/4HANA Implementation in the Automotive Industry 
SAP S/4HANA Project Greenfield Implementation of SAP S/4HANA 
SAP S/4HANA Project S/4HANA Manufacturing Logistics Implementation for a Leading Automaker 
SAP S/4HANA Project Streamlining Global Material Request Workflows: A LeverX Success Story with JBS
Data sourced from the agency's DesignRush profileJBS CPG DATA RETAL Praxie FUCHS Group
Reviews verified by DesignRush and sourced from the agency's profileLeverX Reviews & Testimonials
 Undisclosed SVP Business Development at Government Company5.0★
Undisclosed SVP Business Development at Government Company5.0★Software Development Review from Undisclosed
Products always work as advertised; products are reasonably priced; support of products is very good. The only dislike was software product was developed offshore at the time of the initial deployment, making it more difficult to get certified on government networks.
Show more Undisclosed IT Manager at Manufacturing Industry5.0★
Undisclosed IT Manager at Manufacturing Industry5.0★IT Services Review from Undisclosed
Leverx has broad and deep knowledge as well as products in the area of engineering management processes and provides flexible SAP solutions/add-ons that help our end users to perform their business efficiently. Their team is dedicated to deliver the right solution and always works closely with us to understand our needs and proposes solutions that meet our needs.
Show more Undisclosed Data & Analytics Manager at Manufacturing Industry5.0★
Undisclosed Data & Analytics Manager at Manufacturing Industry5.0★IT Services Review from Undisclosed
IPS workflow engine from LeverX is easy to deploy and manage in terms of IT perspective. Our business key-users are also able to manage, design and configure their own workflow without any IT involvement.
Show more
Solving complex problems with design and technology since 2005.
We craft digital products that streamline your processes, expand your customer base, and drive business growth. Strategically located within your reach, we'll take your ambitious project from an intriguing idea to an outstanding success stories. [... see all Infinum reviews ]- Location
- Zagreb, Croatia
- Number of Employees
- 250 - 499
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 24 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsInfinum Services
- Web Development
- Web Design
- Mobile App Development
- UI/UX Design
- Software Development
- Cloud Consulting
- DevOps Consulting
- Cybersecurity
- Staff Augmentation
- IoT
Data sourced from the agency's DesignRush profilePorsche Nike CITI Royal Caribbean Philips Bayer T-Mobile P&G Universal Virgin Mobile
Reviews verified by DesignRush and sourced from the agency's profileInfinum Reviews & Testimonials
 Matic Debelak Management Board Member at Modra zavarovalnica, d.d.5.0★
Matic Debelak Management Board Member at Modra zavarovalnica, d.d.5.0★Mobile App Development Review from Matic Debelak
Workstream 1: research and product strategyWorkstream 2: ETP release Technology : Vendor use Flutter framework, which allows one programming language and one codebase to create two different apps (for iOS and Android). Clearly defined roles and responsibilities, communication is clearly and respectfully, very effective project methodology, trying to understand every time how their activities fits into mission of Modra zavarovalnica, respect each member of team, etc.
Show more Claus-Peter Mueller Managing Director at NLB Lease&GO doo5.0★
Claus-Peter Mueller Managing Director at NLB Lease&GO doo5.0★Software Development Review from Claus-Peter Mueller
We have engaged Infinum to develop an app that would digitalise our leasing process. From creating the initial offer through the necessary financing application and client identification to the final signature – all the steps required to successfully lease a vehicle or other object can be performed in-app, freeing the users of friction and having to deal with tedious paperwork.The app itself in the background has 30+ integrations, while keeping a seamless and quick to follow process on the front for our users. That application is in production and Infinum is responsible for maintaining it and further improving. After the initial development, we have additionally expanded our scope from vehicles to other equipment. They have also developed a Leasing widget, product which enables quick financing model while purchasing a vehicle online on car seller marketplace pages. At this moment, we are still in partnership with Infinum, and their engagement is mainly focused on localising the app to other countries and supporting us in our further business expansion. The work performed was done in Ruby on Rails and React technology, with support of other services.
Show more- Anonymous VP of Marketing at SaaS Company5.0★
Web Design Review from Anonymous
Thanks to Infinum's website refresh, the client has seen an almost 100% improvement in their website's conversion rates. The team excels at project management, using the client's own proprietary tool and also Figma very well. Their proficiency in design, delivery, and client relations stands out.
Show more
We Maximize Your ROI, Trusted by 1000+ Clients ️
With over 9+ years of experience and 1000+ happy clients, we commit ourselves to your growth. Our team of 85+ of digital marketing experts has delivered:1. 493.37% Increase In Conversions2. 140.91% Increase In Purchases3. 702.60% Increase In Conversion Value4. 180.50% Increase In New Users [... see all Webspero Solutions reviews ]- Location
- Mohali, India
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 32 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsWebspero Solutions Services
- Digital Marketing
- Public Relations
- Cybersecurity
- IT Services
- UI/UX Design
- Software Testing
- eCommerce Development
- Web Development
- Blockchain
Data sourced from the agency's DesignRush profileMedia.Net BYJUS Better Help Betway Modelchic Couture Candy Tiny Hearts Education Dragon bicycles Italian Food Online Keababies
Reviews verified by DesignRush and sourced from the agency's profileWebspero Solutions Reviews & Testimonials
 Trent Rossini CEO at inQuba5.0★
Trent Rossini CEO at inQuba5.0★UI/UX Design Review from Trent Rossini
Exhibiting unmatched development and design skills, WebSpero Solutions successfully created functional websites for us. Their team's work quality and effective communication stood out in our partnership. They were responsive, communicative, and dedicated.
Show more Bishoy Messih President at Nabster Solutions5.0★
Bishoy Messih President at Nabster Solutions5.0★Digital Marketing Review from Bishoy Messih
I had the pleasure of working with Webspero for my social media advertising needs, and I must say they exceeded my expectations. Their team was professional, creative, and highly responsive throughout the entire process. They delivered on their promises and helped boost my social media presence significantly. I would highly recommend Webspero to anyone looking for top-notch marketing services.
Show more Yoko Garg 🏠✨ Serviced Accommodation / Company Let Provider Director at Your Lettings Peterborough Ltd5.0★
Yoko Garg 🏠✨ Serviced Accommodation / Company Let Provider Director at Your Lettings Peterborough Ltd5.0★SEO Review from Yoko Garg 🏠✨ Serviced Accommodation / Company Let Provider
Webspero is an exceptional SEO company that provided personalized, effective strategies to boost my website's ranking and organic traffic. Their transparent, dedicated team genuinely cares about your success. Highly recommended!
Show more
Your Custom Product Lab
We are a leading app design and development company headquartered in Texas, with a dedicated development center in India. With over 75 talented employees, we have successfully delivered 100+ projects across various industries. [... see all Simublade reviews ]- Location
- Houston, Texas
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 13 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSimublade Services
- Mobile App Development
- AI Development
- Software Development
- Web Design
- IoT
- VR/AR
- Blockchain
- UI/UX Design
- eCommerce Development
- DevOps Consulting
Data sourced from the agency's DesignRush profileTavus Savve Opar Beer Run Just Live DoughFi Caristas Used Engines Oral Assist Crowdtrace
Reviews verified by DesignRush and sourced from the agency's profileSimublade Reviews & Testimonials
 Undisclosed Founder & CEO at BeerRun5.0★
Undisclosed Founder & CEO at BeerRun5.0★Mobile App Development Review from Undisclosed
Simublade developed a mobile application for a liquor delivery company. Their work also included design and user interface. The application is now complete and awaiting launch in the App Store. The client is happy with Simublade’s work, particularly their superior customer service and the personal touch they put on their work. The team stuck to deadlines and communicated clearly during the project.
Show more Quinn Favret CEO at Restaurant Ordering Solution5.0★
Quinn Favret CEO at Restaurant Ordering Solution5.0★Software Development Review from Quinn Favret
Simublade provided frontend development with React. Their team integrated the system to API endpoints. Simublade has built a functional frontend. The code has become an integral part of the business. Their team was communicative and flexible. The work was very clean and well-organized.
Show more Roy de la Rosa Founder & CEO at Just.Live5.0★
Roy de la Rosa Founder & CEO at Just.Live5.0★Web Development Review from Roy de la Rosa
From scratch, Simublade designed and developed a social justice application for iOS and Android. The team implemented a feature to temporarily maintain deleted items in the Cloud. They also developed a website. Simublade delivered a product that not only exceeded the client’s expectations but also received positive user feedback for its modern aesthetic and innovative features. The team provides guidance to support lasting collaboration. Their timeliness and commitment result in a valuable partnership.
Show more
Helping companies grow.
Ascendro comprises a seasoned team of software developers dedicated to seamlessly integrating with your organization to conceptualize, develop, and maintain software solutions that drive business growth. Our commitment lies in meticulously understanding your challenges and devising tailored solutions to [... see all Ascendro reviews ]- Location
- Bad Nauheim, Germany
- Number of Employees
- Under 49
- Average Hourly Rate
- $45/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 55 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsAscendro Services
- Staff Augmentation
- Software Development
- Mobile App Development
- Cloud Consulting
- IT Services
- DevOps Consulting
- Customer Support
- IoT
- Web Development
- Cybersecurity
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Azure Project for Manufacturing Company Wolf Backbone - Modernizing Legacy Applications -thumb-webp.webp)
Azure Project for Manufacturing Company Wolf - From Legacy to Digital with DevOps methodology 
AWS Project for Manufacturing Company Ariston - Enhanced Cloud Log Management Solution with ECK 
AWS Project for Health Care Company SciCan - High Availability Architecture Transformation 
AWS Project for Automotive Company Carsharing Platform Modernization & Cloud Migration 
Azure Project for Manufacturing Company Sales Management Tool for Wolf GmbH
Data sourced from the agency's DesignRush profileBMW Audi Samsung Ariston Modernizing Medicine Thinksurance Telekom DE Wio Bank Pnemuoackdemie iGiGi
Reviews verified by DesignRush and sourced from the agency's profileAscendro Reviews & Testimonials
 Tobias König Collaborator at KönigsMedia5.0★
Tobias König Collaborator at KönigsMedia5.0★Software Development Review from Tobias König
The collaboration with Ascendro involved a comprehensive scope of work focused on developing web-based eLearning tools over the course of multiple years. The project required extensive expertise in JavaScript, SCORM interfaces, integration with various Learning Management System (LMS) tools, and the creation of fully XML configurable presentations and executions.Key deliverables of the project included:Development of interactive eLearning modules: The provider successfully created engaging and interactive eLearning modules that effectively conveyed educational content to learners.SCORM integration: The provider expertly integrated the eLearning tools with SCORM standards, ensuring seamless compatibility with different LMS platforms and enabling tracking and reporting of learner progress.LMS integration and compatibility: The provider demonstrated a strong understanding of various LMS tools and efficiently integrated the eLearning tools into these platforms. This allowed for easy deployment and access to the content across different learning environments.XML configuration: The provider implemented a fully XML configurable framework, enabling administrators to customize the presentation and execution of the eLearning modules. This flexibility allowed for tailored learning experiences and easy updates.Overall, the collaboration with our provider involved a meticulous approach to creating eLearning tools with a focus on JavaScript, SCORM interfaces, LMS integration, and XML configurability. The delivered project encompassed a wide range of functionalities and met our expectations in terms of quality and effectiveness.
Show more Christian Kokot CEO at CYMOS Medizin IT5.0★
Christian Kokot CEO at CYMOS Medizin IT5.0★Software Development Review from Christian Kokot
We partnered with Ascendro for custom software development and Linux administration, and the experience has been outstanding. Their team demonstrated exceptional technical expertise and professionalism throughout the project. They quickly understood our requirements and delivered a tailored solution that exceeded our expectations. Their support in managing our Linux infrastructure was also top-notch, ensuring everything ran smoothly and securely. We highly recommend Ascendro for their reliable service, attention to detail, and commitment to quality.
Show more
AI-Native App & Enterprise Software Development Company
TechAhead, a global leader in AI-powered custom software development & cloud engineering services, trusted by Fortune 500 companies and enterprises worldwide. We are a Great Place to Work-certified company with 240+ experts and 16 years of experience in engineering innovative, scalable applications. [... see all TechAhead reviews ]- Location
- Agoura Hills, California
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 26 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsTechAhead Services
- Mobile App Development
- AI Development
- Software Development
- IoT
- Staff Augmentation
- DevOps Consulting
- Blockchain
- Wearables
- Cybersecurity
Data sourced from the agency's DesignRush profileAmerican Express Disney Lafarge The Times Group Allianz AXA ESPN F1 Audi JLL DLF
Reviews verified by DesignRush and sourced from the agency's profileTechAhead Reviews & Testimonials
 Dolly Pundeer Director of Sales at Elite Mindz5.0★
Dolly Pundeer Director of Sales at Elite Mindz5.0★Mobile App Development Review from Dolly Pundeer
We were thrilled with our experience developing a Shipping App with TechAhead. They delivered exactly what we envisioned, and the entire process was smooth and efficient. Their team was incredibly knowledgeable and always kept us informed throughout the project. The final product is not only functional but also user-friendly, exceeding our expectations. Their creativity truly stood out! When we approached them for our shipping app development, they didn't just follow a template. They took the time to understand our specific needs and came up with innovative features that enhanced the user experience for both our customers and our own staff. We highly recommend TechAhead for any app development needs.
Show more Noah Kraft CEO and Co-Founder at Wonderbelly5.0★
Noah Kraft CEO and Co-Founder at Wonderbelly5.0★Mobile App Development Review from Noah Kraft
It was a pleasure to collaborate with TechAhead on our mobile app development project. Their team went above and beyond our expectations with their creative ideas, showcasing their extraordinary Flutter and IoT experience. Throughout the project, their expertise and dedication were clear, and we were very grateful for their proactive grasp of our requirements. We are thrilled with the app's performance and eager to work with TechAhead again in the future.
Show more Rory Bordiuk Co-Founder and CEO at Cirrus Glass5.0★
Rory Bordiuk Co-Founder and CEO at Cirrus Glass5.0★Mobile App Development Review from Rory Bordiuk
Techahead proven to be an essential partner on our application development project. Their team demonstrated good communication and seamless collaboration from the start, which contributed to the delivery of a high-quality product. We were particularly pleased by their ability to provide creative technological solutions that exactly matched our needs. Overall, we appreciate Techahead's service and competence and would certainly recommend them to anybody looking for great mobile app development services.
Show more
Precise Software Solutions
We are a software engineering and digital strategy AI company. [... see all Exaud reviews ]- Location
- Ermesinde, Portugal
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $70/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 12 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsExaud Services
- AI Development
- IoT
- Mobile App Development
- Software Development
- Wearables
- Blockchain
- DevOps Consulting
- Staff Augmentation
- Cybersecurity
- IT Compliance Solution
Data sourced from the agency's DesignRush profileAnoto Samsung NDrive Blaupunkt Audi Essent Facebook Google Nissan Presto
Reviews verified by DesignRush and sourced from the agency's profileExaud Reviews & Testimonials
 Dmitriy Ksendzovsky CEO at Software Consulting4.8★
Dmitriy Ksendzovsky CEO at Software Consulting4.8★Educational Review from Dmitriy Ksendzovsky
I have had an positive experience working with Exaud on expanding and maintaining several software products. Our software consulting technology stack is quite wide, from embedded development to mobile game dev, making it challenging to find the right partner knowledgeable in a number of these areas. The Exaud team is professional, flexible and continues to provide the development expertise we require to fulfill our project needs on time and budget.
Show more Stacy McCarthy President at Learning Design Network, Inc.4.8★
Stacy McCarthy President at Learning Design Network, Inc.4.8★Educational Review from Stacy McCarthy
Learning Design Network has been providing expert learning programs for 20 years, helping nearly 1 million employees worldwide achieve professional success. COVID prompted us to digitalize our product and we chose Exaud as our technology partner. Together, we developed a comprehensive digital tool for customized training and effortless collaboration in a 3D digital environment. The platform leverages our expertise and Exaud's technical capabilities, delivering a high-quality user experience.
Show more Tim Martin Software Architecture and Engineering at FS Studio5.0★
Tim Martin Software Architecture and Engineering at FS Studio5.0★Enterprise Review from Tim Martin
We have a very long history of working with Exuad, which in itself is about the best endorsement you can have. We have been working with them on projects for going on 10 years and they are our go to external dev team. Georg and team are not only very talented they are highly ethical. To me the later point is the most important, you can trust that they will provide high quality work and you can absolutely trust them on the business side.
Show more
Enterprise AI Solutions | Scalable . Flexible. Sustainable
Seasia, being a well-known world-class enterprise software development company, serves small, medium, and large-sized businesses in a seamless and secure manner. We enable competitive digital strategies within your organization that will boost your business. [... see all Seasia Infotech reviews ]- Location
- Emeryville, California
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $25/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 52 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSeasia Infotech Services
- Software Development
- Mobile App Development
- Web Development
- AI Development
- Big Data Analytics
- Cloud Consulting
- Staff Augmentation
- Cybersecurity
- IoT
- Software Testing
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio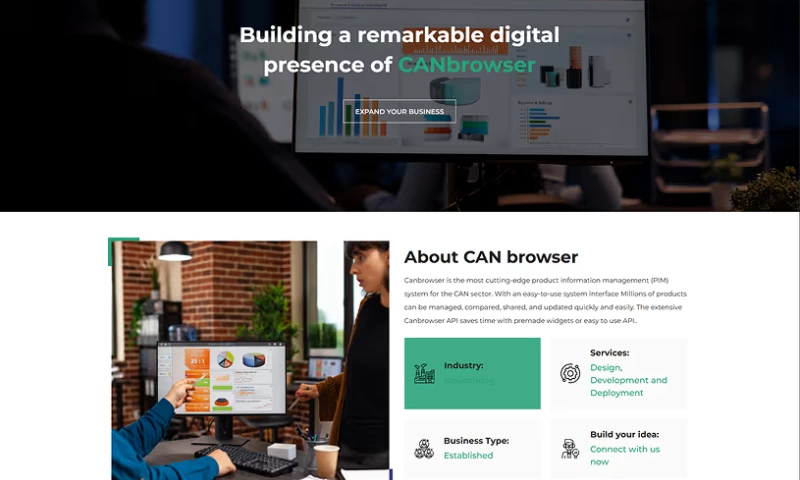
Azure Project for Automotive Company Canbrowser (CB System) High-Performance Enterprise Data Integration
Data sourced from the agency's DesignRush profileAdani Group Flipkart Harley-Davidson Microsoft MainStreet Equity Corp HDFC Bank Swaraj Innopharma Education Renault Puda
Reviews verified by DesignRush and sourced from the agency's profileSeasia Infotech Reviews & Testimonials
 cornelia verden Web Developer at Cornelia Verden LLC5.0★
cornelia verden Web Developer at Cornelia Verden LLC5.0★eCommerce Development Review from cornelia verden
This Company is AMAZING, they are very professional. We hired them to build my website, and they did an EXCELLENT job. They continuously communicated with me during the development phase. If you want a beautiful, well-designed, professional website that has optimum functionabilty, You must go with Seasia Infotech. You can always expect excellent quality services from the professionals at Seasia Infotech.
Show more
From Analysis To Transformation
Born in 2015 as an e-commerce solutions provider, WiserBrand has become the trusted partner for enterprises driving AI-powered transformations. With our headquarters in New York and R&D hub in Latin America, we help businesses across industries automate smarter, scale faster, and stay ahead of the curve. [... see all Wiserbrand reviews ]- Location
- New York City, New York
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $200/hr
- Minimal Budget
- $10,000 - $25,000
- Portfolios Count
- 16 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsWiserbrand Services
- Web Development
- Digital Marketing
- eCommerce Development
- Web Design
- AI Development
- BPO
- SEO
- PPC
- Business Consulting
- Cybersecurity
Data sourced from the agency's DesignRush profileCarolina Refinetti Epuzer Dan Newlin Injury Attorneys ScamAdviser
Reviews verified by DesignRush and sourced from the agency's profileWiserbrand Reviews & Testimonials
 Jorij Abraham Managing Director at Global Anti-Scam Alliance (GASA)5.0★
Jorij Abraham Managing Director at Global Anti-Scam Alliance (GASA)5.0★Web Design Review from Jorij Abraham
We hired WiserBrand as they came strongly recommended by one or our strategic partners. The recommendation was absolutely right. We are no amateurs with 6,5 million unique visitors per month but we learned a lot how we could further optimize our website both from a search engine optimization as well as user experience perspective. The project was completed on time and within budget with several major insights. I can strongly recommend WiserBrand. Feel free to contact me via LinkedIn if you have any questions.
Show more Jennifer L. Sargeant Chief Digital Marketing Officer at Dan Newlin Injury Attorneys5.0★
Jennifer L. Sargeant Chief Digital Marketing Officer at Dan Newlin Injury Attorneys5.0★SEO Review from Jennifer L. Sargeant
WiserBrands strategies have increased consistent search rankings for the clients site since the initial engagement. The continued performance confirms the agency's claim as a leading digital marketing firm. (Verified via email)
Show more Idan Didi COO at Swiftic5.0★
Idan Didi COO at Swiftic5.0★Web Development Review from Idan Didi
Wiserbrand and Swiftic had an agreeable and smooth collaboration. The agency transformed a stalled project into a highly functional site that met internal expectations. WiserBrand can build a responsive partnership and provide useful field-specific advice. The agency is reliable in meeting deadlines. (Verified via email)
Show more
Dedicated Teams That Build Complex Software Systems
SiliconMint designs, develops, and supports mission-critical software systems. Based in San Francisco, SiliconMint has offices in New York and Europe to serve clients across the globe. [... see all SiliconMint reviews ]- Location
- San Francisco, California
- Number of Employees
- 50 - 99
- Average Hourly Rate
- $55/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 7 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSiliconMint Services
- Software Development
- Mobile App Development
- IoT
- AI Development
- Cybersecurity
- Blockchain
- VR/AR
- Big Data Analytics
- IT Services
- Cloud Consulting
Data sourced from the agency's DesignRush profileVerizon Yahoo Japan NASDAQ NYSE Goldman Sachs Barclays BCG Wargaming,net AA orange
Reviews verified by DesignRush and sourced from the agency's profileSiliconMint Reviews & Testimonials
 Leon Hounshell CTO, Verizon5.0★
Leon Hounshell CTO, Verizon5.0★Software Development Review from Leon Hounshell
Using SiliconMint’s AI engine and their engineering team was a great decision for us. They built the core foundation of our ThingSpace IoT platform on time and within budget, helping us serve millions of customers across the country. I would highly recommend the SiliconMint team for their drive and dedication to the art of software architecture and development.
Show more Leonid Zhukov Partner and Associate Director at Boston Consulting Group (BCG)5.0★
Leonid Zhukov Partner and Associate Director at Boston Consulting Group (BCG)5.0★Software Development Review from Leonid Zhukov
I’m always impressed by the technical depth & breadth of SiliconMint’s engineering team and the passion they bring to our projects. We’ve worked with them on distributed systems, data science projects, and a predictive maintenance system for the oil and gas sector. Every time, they blew me away with their experience, passion, energy, and the overall dedication for how they approach software engineering and delivery.
Show more Steve Grice Head of Technology Global Transaction Services at Royal Bank of Scotland5.0★
Steve Grice Head of Technology Global Transaction Services at Royal Bank of Scotland5.0★Cybersecurity Review from Steve Grice
SiliconMint built a real-time fraud detection system for us in a record period of time, with precision and recall that rivals the best in the industry. I was pleasantly impressed by their passion, dedication, and attention to detail in how they approached software development, driving excellence and speed within our organisation.
Show more
Writing Your Future.
HIREQUARTERS is a results-driven agency specializing in SEO, AI-powered content creation, and optimization for iGaming, crypto, cybersecurity, and FinTech brands. We help businesses grow their visibility and authority online. [... see all HIREQUARTERS reviews ]- Location
- Niš, Serbia
- Number of Employees
- Under 49
- Average Hourly Rate
- $60/hr
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 3 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsHIREQUARTERS Services
- Content Marketing
- SEO
- Digital Marketing
- Social Media Marketing
- Affiliate Marketing
- Business Consulting
- Market Research
- Translation Services
- AI Development
- Cybersecurity
Data sourced from the agency's DesignRush profileCovers Media Gentoo Media Catena Media Better Collective Raketech LCB SoftGamings Oddschecker White Hat Gaming Casino.org
Reviews verified by DesignRush and sourced from the agency's profileHIREQUARTERS Reviews & Testimonials
 Davor Štefanović Site Manager at Gentoo Media5.0★
Davor Štefanović Site Manager at Gentoo Media5.0★Content Creation Review from Davor Štefanović
We've had an excellent experience working with Hirequarters on research and content writing for SweepsChaser. Communication was clear, professional, and proactive throughout the collaboration, which made planning and feedback loops straightforward and efficient.Deliverables were consistently submitted on time, with strong attention to detail and a clear understanding of project requirements. The content quality met our standards across structure, accuracy, and tone, requiring minimal revisions before publication.Overall, the Hirequarters team proved to be reliable, responsive, and easy to work with. Wed gladly recommend them for research-driven content projects and look forward to collaborating again in the future.
Show more Goran Kostadinov SEO Specialist at 10bet5.0★
Goran Kostadinov SEO Specialist at 10bet5.0★SEO Review from Goran Kostadinov
Working with 'Headquarters' has been a transformative experience for our brand. Even though we were sometimes overly demanding, emphasizing semantic concepts of writing to aid algorithms in content comprehension, they rose to the challenge brilliantly. Their unparalleled attention to detail and commitment to understanding our unique needs have made our collaboration seamless and productive. We're deeply appreciative of their high standards and commendable work ethic. A heartfelt thank you to the
Show more Dave Rathmanner CEO at Upper 9 Media LLC5.0★
Dave Rathmanner CEO at Upper 9 Media LLC5.0★SEO Review from Dave Rathmanner
HIREQUARTERS has been fundamental in growing my websites traffic. They have great writers and deliver typo-free, high-quality content. Couldn't recommend them enough for iGaming content!
Show more
Making the cyberspace more secure, one enterprise at a time
At Consulting Systems we provide proactive cybersecurity solutions, integrating cutting-edge technologies and deep expertise to stay ahead of threats. Adhering to ISO 27001, NIST, and GDPR, we ensure strong protection for organizations navigating todays evolving digital landscape. [... see all Consulting Systems reviews ]- Location
- Guayaquil, Ecuador
- Number of Employees
- Under 49
- Minimal Budget
- $1,000 - $10,000
- Portfolios Count
- 3 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsConsulting Systems Services
- Cybersecurity
- IT Compliance Solution
- IT Services
- Managed Services
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project Penetration Testing 
Cybersecurity Project Computer Forensics 
Cybersecurity Project Compliance Audits
Data sourced from the agency's DesignRush profileAFP Génesis VERIS Conauto Grupo Berlín PICA Ecuaquímica Quicornac Swissgas Swisslub Farmagro
Reviews verified by DesignRush and sourced from the agency's profileConsulting Systems Reviews & Testimonials
 Fatima Alarcon VP IT at Tecnova5.0★
Fatima Alarcon VP IT at Tecnova5.0★Cybersecurity Review from Fatima Alarcon
Consulting Systems provides top-notch cybersecurity services. Their personalized approach, professionalism, and expert assistance have been invaluable in safeguarding our information security and protecting our corporate image from potential breaches
Show more Alex Serrano Cueva Director at ContyLeg5.0★
Alex Serrano Cueva Director at ContyLeg5.0★Cybersecurity Review from Alex Serrano Cueva
"Consulting Systems delivers exceptional cybersecurity services. Their dedication, expertise, and personalized support have played a vital role in fortifying our information security and shielding our corporate identity against security breaches."
Show more Jorge Luis Galarza R. Systems Coordinator at DATA TOOLS S.A5.0★
Jorge Luis Galarza R. Systems Coordinator at DATA TOOLS S.A5.0★Digital Forensics Review from Jorge Luis Galarza R.
Consulting Systems' Digital Forensics services helped us find evidence related to internal processes on computers that were compromised in data leakage and hacking.
Show more
Conquer IT with confidence.
Elevate your journey with DYOPATH, your premier ally in IT outsourcing. Born from a powerful merger, we bring amplified value and expertise, safeguarding your success in the face of evolving challenges. Experience end-to-end IT excellence, robust cybersecurity, and unparalleled customer care. [... see all DYOPATH reviews ]- Location
- Oakbrook Terrace, Illinois
- Number of Employees
- 500 - 999
- Portfolios Count
- 5 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsDYOPATH Services
- IT Services
- Cybersecurity
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project Case Study: CPS Energy 
IT Outsourcing Project DESKTOP-AS-A-SERVICE (DAAS) 
IT Outsourcing Project Implemented a Continuity of Operations Plan (COOP). 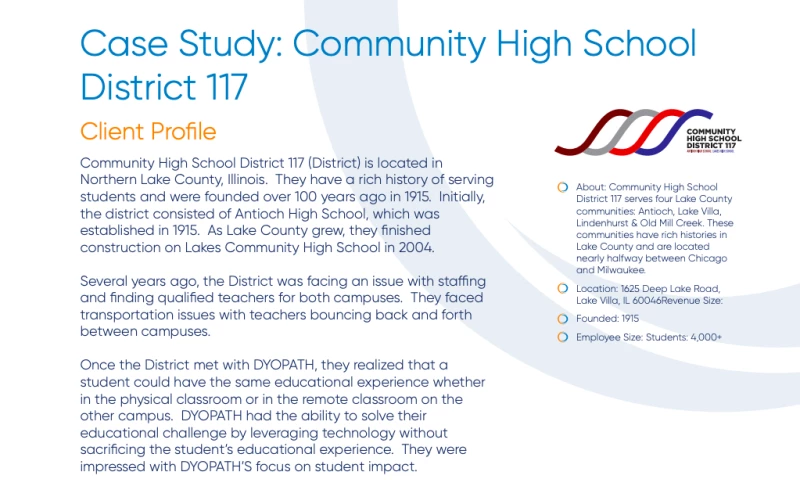
IT Services Project Case Study: Community High School District 117 
IT Outsourcing Project CONSTRUCTION INDUSTRY: IAAS AND DAAS
Data sourced from the agency's DesignRush profileGreat Lakes Academy Blue Prairie Group Academy Chicago White Sox
Reviews verified by DesignRush and sourced from the agency's profileDYOPATH Reviews & Testimonials
 James P. Branch Chief at Enforcement and Removal Operations of a Large Federal Agency5.0★
James P. Branch Chief at Enforcement and Removal Operations of a Large Federal Agency5.0★IT Services Review from James P.
DYOPATH had an exceptional understanding of our technical needs and mission requirements. They planned and executed all maintenance across more than 20 clinics, where more than 10 also had dental services, as well as headquarters operations. They also planned and executed the migration from one network to another. In addition, the DYOPATH Call Center and on-site support was highly praised by both field and headquarters staff.
Show more Brian F. IT Manager at Choose Chicago5.0★
Brian F. IT Manager at Choose Chicago5.0★IT Services Review from Brian F.
I would not hesitate in a heartbeat to recommend your company. I’ve worked with DYOPATH at my last job (UCAN) for project based worked and when I moved on, I took my contact along with me. Over the years I’ve used you for project-based work with a lot of success. Now that I am using you for a level 1 helpdesk/desktop support role, the experience has been wonderful.
Show more Don B. Senior Director of Management Information Systems at Chicago White Sox5.0★
Don B. Senior Director of Management Information Systems at Chicago White Sox5.0★IT Services Review from Don B.
With the old phone system all we could do was make calls. With the Cisco Unified Communications platform from DYOPATH we enhanced our phone system functionality, but also gained advanced features that deliver major productivity gains. The organization can now click to call from desktops, integrate voice over our state-of-the-art WLAN, allow for intelligent call routing to the sales/marketing team, create screen pops through our CRM application, and deliver an integrated public safety solution for employees and vendors. It’s an incredibly powerful system, very 21st Century.
Show more
Trusted software engineering and IT consulting company
We deliver cutting-edge, scalable, and fully functional software products and ecosystems that help clients achieve their specific objectives. [... see all Yalantis reviews ]- Location
- Warsaw, Poland
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $45/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 24 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsYalantis Services
- Software Development
- Mobile App Development
- AI Development
- IoT
- IT Services
- Cybersecurity
- Staff Augmentation
- Cloud Consulting
- UI/UX Design
- Big Data Analytics
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio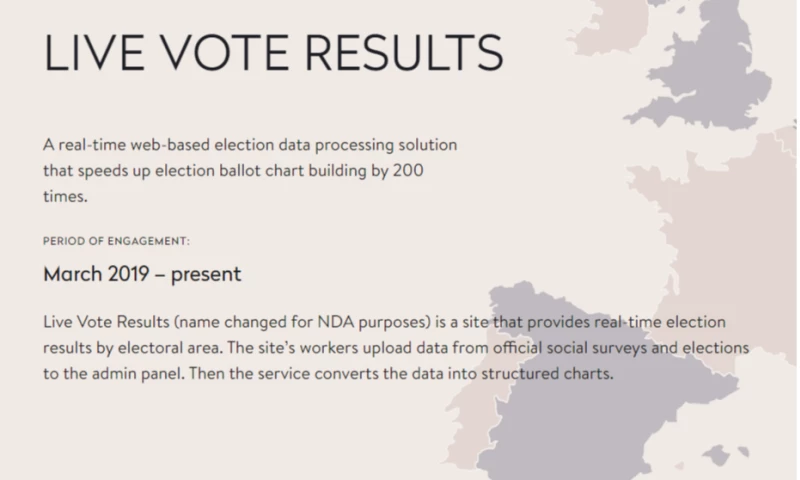
IT Services Project for Government Company Live Vote Results
Data sourced from the agency's DesignRush profileRAKwireless Toyota Tsusho KPMG Healthfully Orbis Systems Lifeworks Scholz Databank 123 Sourcing Truhoo
Reviews verified by DesignRush and sourced from the agency's profileYalantis Reviews & Testimonials
 Sergei Lishchenko Director of Digital Experience and Innovation at Orbis System5.0★
Sergei Lishchenko Director of Digital Experience and Innovation at Orbis System5.0★Fintech Review from Sergei Lishchenko
The exception team the client collaborated with brought in fresh ideas and innovative technologies previously unfamiliar to the client. For example, with Yalantis' guidance, the client's developers explore the Go language. The primary reason the client chose Yalantis is its strong organizational and project management skills. It's not just about the developers; Yalantis provides a comprehensive support framework, ensuring that a project manager is consistently present. (Verified via email)
Show more.png) Jason Jung Senior engineering manager at Zillow5.0★
Jason Jung Senior engineering manager at Zillow5.0★Software Development Review from Jason Jung
Yalantis functions as an integral scrum team, supporting the development teams of a real estate firm. It created renovation project management tools that encompass a web app, a mobile app, and a backend system. Thanks to Yalantis, the client expanded development capabilities and achieved key short-term goals. Its quick integration was pivotal in launching various projects. Beyond delivering top-notch work, Yalantis emphasizes a culture that prioritizes the customer's needs. (Verified via email)
Show more.png) Roy D Partner at RAKwireless5.0★
Roy D Partner at RAKwireless5.0★Outsourcing Review from Roy D
An IoT manufacturer teamed up with Yalantis to craft an application, enabling users to manage their devices more efficiently. Utilizing Node.js and basing the architecture on Circulus, Yalantis delivered commendable outcomes. It is responsive to any development challenges, offering swift resolutions. The client appreciates Yalantis' proactive stance, impressive technical expertise, and practical solution suggestions. (Verified via email)
Show more
Software development company that delivers measurable results.
SparxIT is a trusted tech partner delivering expert web design and development, mobile solutions, and eCommerce development. We build custom digital platforms powered by AI, ML & IoT for startups to enterprises. Trusted by HP, Suzuki & Hisense. Lets shape your digital future. [... see all Sparx IT reviews ]- Location
- Noida, India
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $30/hr
- Portfolios Count
- 35 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSparx IT Services
- Web Design
- Web Development
- Mobile App Development
- Software Development
- eCommerce Development
- AI Development
- Cybersecurity
- Blockchain
Data sourced from the agency's DesignRush profileVedanta Hp Huawei Motorola D-Link Hisense Necco Intel
Reviews verified by DesignRush and sourced from the agency's profileSparx IT Reviews & Testimonials
 Tariq Khan Manager at EG- Retail5.0★
Tariq Khan Manager at EG- Retail5.0★Mobile App Development Review from Tariq Khan
Developing the grocery app with SparxIT was a terrific experience for me. The team provided us with regular updates regarding the app, keeping us informed. Their prompt action and extensive technical know-how made the project complete smoothly.
Show more Paul Landherr Manager at AusCellardoor4.5★
Paul Landherr Manager at AusCellardoor4.5★Mobile App Development Review from Paul Landherr
The company hired Sparx IT to create a mobile app for its premium wine business. It wanted a seamless app that improves the process of buying wine, making it fun and simple for customers to discover and enjoy excellent wines. SparxIT's expertise in MVP development truly impressed the client. The completed MVP for the premium wine business app has gotten overwhelmingly positive feedback from users. (Verified by email)
Show more Dylan Brown Manager at www.tchomecare.ca5.0★
Dylan Brown Manager at www.tchomecare.ca5.0★Mobile App Development Review from Dylan Brown
The app development is still in progress, and they have provided us with weekly updates on the progress of the app development project. The quality of work is outstanding. We are thoroughly impressed with the team's level of expertise and skill. Overall, we're having an excellent experience working with the SparxIT team and would highly recommend their services to anyone needing mobile app development services. (Verified via email)
Show more
Engineering peace of mind
At Vention, unparalleled customer care isnt just a promise its our mission. We blend personalized experience, unwavering attention to detail, and a genuine passion for your business, ensuring that every aspect of our collaboration is tailored to your success. [... see all Vention reviews ]- Location
- New York City, New York
- Number of Employees
- 1000 & Up
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 16 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsVention Services
- Software Development
- Staff Augmentation
- Mobile App Development
- Software Testing
- Web Development
- Blockchain
- AI Development
- Cloud Consulting
- CRM Consulting
- Cybersecurity
Comprehensive analysis done by DesignRush Agency Experts.Clients and Projects
View Full Portfolio
Cybersecurity Project for Electronics Company DAQ Electronics 
Cloud Consulting Project for Wellness & Fitness Company Juice Plus+ 
Cloud Consulting Project for Nonprofit Company Doctors Without Borders
Data sourced from the agency's DesignRush profileIBM PayPal Cuvva Costa Coffee Memrise Urban Tailored Dog Food Delivery RealVNC Label on a Cable ClassPass
Reviews verified by DesignRush and sourced from the agency's profileVention Reviews & Testimonials
 Lee Tupper CTO at Remotiv (formerly Financial Soundings)3.8★
Lee Tupper CTO at Remotiv (formerly Financial Soundings)3.8★Mobile App Development Review from Lee Tupper
Vention has delivered excellent design prototypes and accurate time estimates. The app is still in beta mode, and the partnership with [...] Vention will [continue] until the release of the next version. Vention is a reliable team that offers quality service. (Verified via email)
Show more Jon Wade CTO & Founder at Union545.0★
Jon Wade CTO & Founder at Union545.0★Staff Augmentation Review from Jon Wade
Vention’s efforts allowed the successful development of the product, resulting in new customers. They provided backend developers, business analysts, UI designers, and QA testers to develop our solution. Vention cultivated a seamless partnership through constant updates and a collaborative approach. Overall, their team’s well-rounded expertise was impressive.
Show more AJ Canty CTO and Co-Founder at Primer5.0★
AJ Canty CTO and Co-Founder at Primer5.0★Web Development Review from AJ Canty
We’ve been working with Vention for quite some time and consider them an extension of our team, rather than an offshore vendor. We needed solid mobile developers to work with our in-house engineers to build our Primer SDKs on both mobile platforms. This was not a trivial thing as it required a lot of cross-functional communication, but the Vention team was up to the challenge. They quickly adopted the best practices we follow at Primer and proved to be effective and proactive.
Show more
Software, mobile and SaaS application development since 2004.
We are located in beautiful Phoenix, Arizona, and we can meet you in person anywhere in Arizona or Southern California. We have clients coast to coast and we have a long and proud history as a technology advocate for small business. To learn more, call us at 623-845-2747 or visit datatitan.com. [... see all Data Titan reviews ]- Location
- Phoenix, Arizona
- Number of Employees
- Under 49
- Average Hourly Rate
- $100/hr
- Minimal Budget
- $1,000 - $10,000
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsData Titan Services
- Mobile App Development
- Software Development
- IT Services
- Cybersecurity
- Digital Services
- Digital Strategy
- UI/UX Design
- eCommerce Development
- Web Development
- Business Consulting
Data sourced from the agency's DesignRush profileUnited States Air Force Fidelity National Financial The University of Texas at San Antonio Continental Floral Greens International Insurance Group Cupid Nation Blue Sky Communications Nitti Builders Edvance Research Vilore Foods Internationa
Reviews verified by DesignRush and sourced from the agency's profileData Titan Reviews & Testimonials
 Emma Bowers Founder, CEO at LabPair, Inc.5.0★
Emma Bowers Founder, CEO at LabPair, Inc.5.0★Software Development Review from Emma Bowers
John Tomblin has served as the software architect and Chief Technology Officer for our software startup, LabPair, for the past two years. During this time John has played an essential role in developing the LabPair software, helping us hone our business model, and plan our launch strategy. I have been delighted with John's services and look forward to our continued partnership.John enjoys a high degree of success as a developer because he is able to engineer software solutions for a variety of marketplaces, no matter how complex or niched. In additional, he has a highly orchestrated, efficient, time- tested process that he uses to scope software projects and get them programmed to clients' specifications. I have been especially appreciative of how John and his team have been both forthright and accurate in estimating the time and cost associated with project development. By far, my favorite part about working with John is his jovial personality, can-do attitude, and excellent communication skills.
Show more Thomas Canale Founder at Truppraisal. LLC5.0★
Thomas Canale Founder at Truppraisal. LLC5.0★Software Development Review from Thomas Canale
In 2022, I realized that I needed to find a software development firm capable of designing and developing a SaaS application that would serve the real estate community's need to create reliable, usable, Competitive Market Analysis (CMA) reports, but do so in such a way that also reduced the creation time by as much as 95%. After meeting John and his team, and talking for several weeks about my project, I knew instantly that Data Titan was the right company. Not only were they attentive to every detail of the project, but they also remained vigilant with communications, managing change orders, and keeping to the exact time schedules set for the two-year project, and its numerous phases. Additionally, John's company used 'Scope Atlas', their company's software development application system, to design every screen before any programming work. Having now been through a two-year development process, I realize this project would have never launched without 'Scope Atlas', John's leadership, his senior team, and most importantly, his considerable expertise and insight in the software development sector. I wholeheartedly recommend John and his company for any software or mobile app development project you may be considering. Thank you.
Show more.png) Kara Peterson Founder at Epic Publisher5.0★
Kara Peterson Founder at Epic Publisher5.0★Software Development Review from Kara Peterson
Have you ever had a dream? Have you envisioned greatness? This is who I am, I had the idea, but it was just out of my grasp. John Tomblin is in the business of making your creativity and genius a reality. When I first reached out to John, I thought I was on one track. I have a habit of seeing the end, but all of the details are distractions and I had not given them any thought. I was completely unaware of the scope of my project. John did a year long scope and sequence with me, that turned into consulting. He showed me that there is so much more than the end product. I have worked with technology companies in the past and they do one thing really well, they develop technology. John looks at the project holistically. From when the consumer/customer first engages with your product, to how they will actually purchase the product, to the ease of use of the technology, to the performance of your product, to the marketing - how will you first find these customers, and so much more. John is detail oriented and very organized. Nothing slips past him because of his methodology with his wireframes. He holds weekly meetings to make sure the client (me) and he have both done our "homework" to move the project forward. The meetings also ascertain that we are both on the same page about the project. Working with John is a pleasure; I look forward to our weekly talks. I am certain that he is "on my side" and is looking out for my best interests. The world has gotten very small and it is easy to find someone to build your product. However, it is not easy to find someone who will listen to your dream, help you reach it, look out for your best interests and whom you can put complete faith in.
Show more
Building Products AI-Native Way
Talentica Software is a leading product engineering company that helps startups, growth-stage, and technology companies build end-to-end products and achieve business outcomes. The company has specialized in AI & Machine Learning, Generative AI, Data Engineering, Blockchain, and Big Data [... see all Talentica Software reviews ]- Location
- Pune, India
- Number of Employees
- 500 - 999
- Average Hourly Rate
- $30/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 7 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsTalentica Software Services
- Software Development
- AI Development
- IT Services
- Big Data Analytics
- Cybersecurity
- Blockchain
- Mobile App Development
- Staff Augmentation
Data sourced from the agency's DesignRush profileWideorbit Sema4.AI Realization Technologies Inc. TailoredMail StructuredWeb Inc Amplify Mist Systems (Juniper Company)
Reviews verified by DesignRush and sourced from the agency's profileTalentica Software Reviews & Testimonials
 Ashish Sharma Sr Engineering Manager at OpenGov India Pvt Ltd4.7★
Ashish Sharma Sr Engineering Manager at OpenGov India Pvt Ltd4.7★Software Development Review from Ashish Sharma
Talentica has proven to be an exceptional software outsourcing partner, consistently exceeding expectations in both the quality of their resources, deliverables and their commitment to our success. They function not merely as a vendor, but as an extension of our core engineering team.Key Highlights of our Partnership:High Resource Quality: The engineers provided by Talentica are technically strong and highly competent. They integrate seamlessly with our internal teams and quickly take ownership of complex projects.Commitment and Reliability: Talentica is a truly reliable partner that consistently demonstrates a strong willingness to go beyond the standard scope of work. They proactively identify risks and contribute innovative solutions.Critical Project Support: Their expertise was pivotal in two critical areas:Data Pipeline & Reporting: They were instrumental in both enhancing and maintaining a reliable data pipeline & reporting infrastructure. Software Upgrades: They managed challenging, large-scale software upgrades, ensuring we successfully transitioned to modern technology stacks with minimal disruption.Overall, Talentica is a dependable and high-value partner assisting our mission-critical projects.
Show more Anonymous Advisor at IT Company5.0★
Anonymous Advisor at IT Company5.0★Software Development Review from Anonymous
We had created a conceptual framework to authenticate and verify the provenance, transaction history, and authorship of blockchain-based NFTs. Talentica was brought on board to test and refine the concept from both functional and engineering perspectives, and later to build a Minimum Viable Product (MVP) aligned with the agreed specifications and constraints.
Show more Anonymous Engineering Manager at SaaS Company5.0★
Anonymous Engineering Manager at SaaS Company5.0★Software Development Review from Anonymous
For several years, the team was composed entirely of Talentica contractors. Since January 2022, I have been directly managing them. The Talentica team handled the admin tooling backend, which included multiple Python Flask services with Postgres and Elasticsearch. These services operated in a service-oriented architecture deployed on Kubernetes, using Istio for service mesh and Spinnaker for deployments.
Show more
Transforming Business Through Scalable Software and Ethical AI
SumatoSoft helps global enterprises and ambitious startups bridge the gap between traditional digitalization and the AI frontier. As a premier AI software development company, we build more than just code; we engineer governed AI ecosystems and scalable platforms that turn raw data into a competitiv [... see all SumatoSoft reviews ]- Location
- Boston, Massachusetts
- Number of Employees
- 100 - 249
- Average Hourly Rate
- $50/hr
- Minimal Budget
- $25,000 - $50,000
- Portfolios Count
- 10 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSumatoSoft Services
- Software Development
- Mobile App Development
- IoT
- UI/UX Design
- Big Data Analytics
- IT Services
- AI Development
- Wearables
- Cybersecurity
- IT Compliance Solution
Data sourced from the agency's DesignRush profileGlamz - Platform for Beauty Professionals Tartle – Big Data Trading Platform Smart integration Fuelz - Aggregator Web Platform Umergence MyMediAds Toyota Widgety Sous Kitchen Boxforward
Reviews verified by DesignRush and sourced from the agency's profileSumatoSoft Reviews & Testimonials
 Sergey Novik Co-Founder at El Pixel5.0★
Sergey Novik Co-Founder at El Pixel5.0★Staff Augmentation Review from Sergey Novik
Were developing an internal image processing tool for our design team and needed two machine learning engineers, since our core developers were busy with other client projects. We required extra hands familiar with Python and computer vision, so after a developers market review, we hired them from SumatoSoft.The SumatoSoft developers joined our team and were able to swiftly adapt to our workflows, which resulted in them delivering the working models well before our hard deadline.Communication was straightforward throughout the engagement. We had video calls and exchanged brief text updates on a weekly basis. The delivered code is clean, and pull requests are well-documented.I appreciate that they pushed back on a few of our initial architecture ideas. They challenged our original approach and proposed a better method for handling the model weights. We plan to bring them back for the next phase of development.
Show more Domien Van Eynde Team Lead at Daiokan5.0★
Domien Van Eynde Team Lead at Daiokan5.0★Web Development Review from Domien Van Eynde
SumatoSoft is the firm to work with if you want to keep up to high standards. The professional workflows they stick to result in exceptional quality. Important, they help you think with the business logic of your application and they don’t blindly follow what you are saying. Which is super important. Overall, great skills, good communication, and happy with the results so far.
Show more Alexander McCaig Co-Founder & CEO at Tartle5.0★
Alexander McCaig Co-Founder & CEO at Tartle5.0★eCommerce Development Review from Alexander McCaig
The system has produced a significant competitive advantage in the industry thanks to SumatoSoft’s well-thought opinions. They shouldered the burden of constantly updating a project management tool with a high level of detail and were committed to producing the best possible solution.
Show more
Custom Applications That Drive Business Growth
Ntiva is a technology company that provides managed IT and security, cloud solutions, digital transformation, and advanced IT consulting. We support the midsized and enterprise markets, including manufacturing, construction, healthcare, financial services, real estate, and nonprofits. [... see all Ntiva reviews ]- Location
- Chicago, Illinois
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $80/hr
- Portfolios Count
- 6 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsNtiva Services
- Mobile App Development
- Software Development
- Managed Services
- IT Services
- Cybersecurity
- UI/UX Design
Data sourced from the agency's DesignRush profileAetna Blue Cross Blue Shield of Illinois Illinicare Fairlife Greater Chicago Food Depository Health Care Services Corporation Quality Training Systems All-Tech Decorating Rush University Illinois State Board of Investments
Reviews verified by DesignRush and sourced from the agency's profileNtiva Reviews & Testimonials
 David Terroba Senior Accountant at CASEL5.0★
David Terroba Senior Accountant at CASEL5.0★IT Services Review from David Terroba
Ntiva is great with managing both Windows and Mac environments, a rare find amongst IT companies. More importantly, I no longer have to wear the “IT hat” and can focus on my true priorities.
Show more Ira Starr CAO at Streetsense5.0★
Ira Starr CAO at Streetsense5.0★IT Services Review from Ira Starr
Every single company today is completely reliant on technology for growth and success. Companies who are technology enabled have a distinct competitive advantage, which is why we chose to partner with Ntiva.
Show more Andy Lomasky Director of IT at PMMI5.0★
Andy Lomasky Director of IT at PMMI5.0★IT Services Review from Andy Lomasky
I don’t want to be in the business of server administration or patching or help desk. Those are perfect targets to be outsourced so that we can stay focused on what differentiates us as a business.
Show more
A Versatile Tech Company!
Softeq is a versatile technology and Greentech company offering a wide range of services, including embedded system development, machine learning, digital transformation, hardware design, UX/UI design, and more. [... see all Softeq reviews ]- Location
- Houston, Texas
- Number of Employees
- 250 - 499
- Average Hourly Rate
- $80/hr
- Minimal Budget
- $50,000 & Up
- Portfolios Count
- 8 Projects Listed
Data sourced from the agency's DesignRush profile, its website, and other relevant accountsSofteq Services
- Mobile App Development
- Software Development
- Software Testing
- Blockchain
- Wearables
- UI/UX Design
- Cybersecurity
- AI Development
Data sourced from the agency's DesignRush profileLenovo Epson Microsoft WTA NVIDIA Verizon G.J.Gardner Walt Disney Parks and Resorts Happiest Baby
Reviews verified by DesignRush and sourced from the agency's profileSofteq Reviews & Testimonials
 Quan Gan Owner at Gantom Lighting & Controls5.0★
Quan Gan Owner at Gantom Lighting & Controls5.0★Software Development Review from Quan Gan
We collaborated with Softeq to develop an infrared emitting platform. Softeq provided software development and support services, streamlining our project. While our hardware technology was excellent, Softeq elevated our company's products with superb software development and implementation solutions. Working with Softeq was highly beneficial for us, as the agency managed our projects more efficiently due to exceptional project management and organized workflows.
Show more Jeff Johnston Founder and Chief Executive Officer at A-List Enterprises5.0★
Jeff Johnston Founder and Chief Executive Officer at A-List Enterprises5.0★Mobile App Development Review from Jeff Johnston
We hired Softeq for mobile app development services. Softeq developed a functional and user-friendly app, efficiently integrating productivity features like calendar, contacts, and task management. The agency organized regular meetings with our product management department, communicated effectively, and promptly resolved issues. Softeq's team worked diligently and provided valuable insights. We were satisfied with Softeq's services.
Show more Trent Gardner Information Technology (IT) Manager at G.J. Gardner Homes5.0★
Trent Gardner Information Technology (IT) Manager at G.J. Gardner Homes5.0★Software Development Review from Trent Gardner
We worked with Softeq for software redevelopment services to improve our company's proprietary software. Softeq updated the business platform, streamlining operations and enhancing the platform's user UI and functionality. This improvement aided our sales, job estimating, purchase orders, and administration efforts. Softeq's team was professional, attentive, and prompt in implementing feedback. The agency delivered high-quality work, impressing our company's internal stakeholders.
Show more
Cybersecurity Specializations
Services Related to Cybersecurity
How to Hire Top Cybersecurity Service Providers
What should be included in the scope before you start comparing cybersecurity companies?
Before approaching cybersecurity companies, define your business outcome, in-scope assets and environments, service type and depth, access model, deliverables, exclusions, timeline, and compliance or contractual requirements.
Once these details are defined, you can compare providers based on whether they can support your environment, constraints, and expected outcomes.
Below are more details on each element:
| Scope | Example |
| Business outcome | Security assessment, penetration test, incident response, compliance support, managed detection and response (MDR) |
| Compliance requirements | HIPAA, PCI DSS, GDPR, state-specific privacy regulations |
| IT environment details | Cloud, SaaS, on-premise setup, applications, network, endpoints, operational technology |
| Assets and data | Systems, apps, users, data classes, and third-party platforms that should be part of the company's coverage |
| Depth of work | Point-in-time test vs. Ongoing service, executive reporting needs, black/gray/white-box depth |
| Access and coordination | Accounts, approvals, internal owners, maintenance windows, change freeze |
| Deliverables | Technical report, executive summary, remediation workshop, retest, action plan |
| Exclusions | Systems, customer data, geographies, production limits |
How do you compare cybersecurity proposals?
Compare cybersecurity proposals by standardizing your decision grid: scope, named team, methodology, deliverables, follow-up, timeline, assumptions, and total cost.
A strong proposal reveals hidden work, assumptions, and costs, allowing you to assess cybersecurity companies fairly, reduce third-party risks, and make an informed decision.
Expect the following details from a cybersecurity proposal:
- Named team: Senior lead, delivery staff, subcontractors, escalation owner
- Methodology: Test type, manual vs. automated effort, assumptions, and technical constraints
- Deliverables: Report types, executive summary, remediation support, retest
- Timeline: Kickoff, active work, draft findings, final report, retest window
- Internal effort: Access needs, meetings, approvals, change windows, customer-side workload
- Commercial model: Fixed fee, overages, travel, add-ons, renewals
- Expected outcomes: Prioritization, remediation guidance, follow-up support
What red flags should you pay attention to?
The biggest red flags when evaluating cybersecurity firms include vague scoping, unverifiable credentials, unclear access and ownership terms, unrealistic guarantees, and bundled services that are not clearly defined.
Watch out for the following:
- Unrealistic guarantees: Cybersecurity is about reducing and managing risk, not eliminating it. A company that promises 100% security without clear assumptions or scope is offering certainty that no provider can honestly guarantee.
- Cookie-cutter approach: If a company produces a proposal without first learning about your environment, tools, business processes, and team structure, it is likely offering a generic solution rather than one tailored to your risks.
- No practical experience: Certifications matter, but they are not enough on their own. A credible firm should be able to provide relevant references, anonymized case studies, or recent examples of work similar to your environment and problem.
- Case studies with no specifics: Outcomes described only as "improved security posture" or "reduced risk" with no mention of the threat category, the client industry, or a measurable result are not evidence of capability.
- Reluctance to define scope in writing: If a provider resists putting scope boundaries, assumptions, exclusions, and deliverables in the contract, it may expose you to budget overruns, disputes, or misaligned expectations.
- Inflexible contracts: Long lock-in periods, proprietary tooling with no clear justification, or demands for sole control over key administrative accounts can create unnecessary dependency and make transition difficult.
Verizon's 2025 Data Breach Investigations Report found third-party involvement accounts for 30% of the breaches, twice the amount from the previous year. As such, cybersecurity firm selection should be considered part of your security posture rather than just a procurement process.
How much access should you provide to the cybersecurity services company?
Provide only the minimum access needed for the scoped work. Access should be role-based, time-bound, approved, monitored, protected with MFA, and easy to revoke. For privileged work, use separate privileged accounts only when necessary, and log privileged actions.
Here are a few examples:
- Audits and assessments: Exported evidence or read-only access. If live access is needed, limit it to the systems under review and set it to expire at the end of the approved task or engagement window.
- Penetration testing: Match access to the agreed test type. Black-box testing generally uses no internal credentials or internal system knowledge. Gray-box testing uses limited internal information or test accounts. White-box testing may include source code, architecture, or deeper internal access, and privileged access should be granted only if the test requires it.
- Managed monitoring: Start with log, API, and telemetry access. Add limited response permissions only if containment or response actions are in scope, and document exactly what the provider is allowed to do. Provider activity should be monitored.
- Incident response: In emergencies, grant elevated access only to affected systems and only for as long as needed, using MFA, named approvers, session logging, and rapid revocation. The provider's authority, restrictions, and communication path should be defined in advance.
According to Delinea's 2026 Identity Security Report, nearly 90% of respondents reported at least one identity visibility gap, especially around machine and non-human identities.
That finding underscores the importance of tightly controlling and monitoring the access granted to cybersecurity service providers.
What contract details should you review before signing with a cybersecurity services company?
Review the contract's scope boundaries, roles and responsibilities, confidentiality and data-handling terms, incident notification and escalation procedures, reporting and follow-up obligations, ownership of work product, pricing and change-control terms, liability and insurance provisions, and exit terms before signing a contract with a cybersecurity services company.
Look for the following in your cybersecurity contract:
| Contract clause | Why it matters | What it should cover |
| Scope boundaries | Stops disputes and blind spots | Named systems, environments, data, geographies, and explicit exclusions |
| Roles and responsibilities | Prevents assumption gaps | Who owns hardening, monitoring, testing, incident response, remediation, and retesting |
| Confidentiality and data handling | Protects findings, credentials, and sensitive business data | NDA terms, data storage, retention, sharing limits, and deletion timing |
| Escalation and incident handling | Determines what happens if a serious issue is found | Severity thresholds, named contacts, notification timing, and response path |
| Reporting and follow-up | Turns findings into action | Technical report, executive summary, remediation workshop, retest, and action plan |
| Change control and pricing | Prevents scope creep | Overages, change orders, emergency work, and renewal terms |
| Liability and insurance | Allocates downside when something goes wrong | Coverage evidence, indemnities, caps, and carve-outs |
| Exit and termination terms | Prevents vendor lock-in | Notice period, early exit fee, how access is revoked and data is turned over |
According to the World Economic Forum's Global Cybersecurity Outlook 2026, 46% of organizations say that third-party and supply chain vulnerabilities are among their top challenges to becoming cyber resilient.
A well-structured contract helps manage this risk by clearly defining security requirements, responsibilities, notification obligations, and accountability.
Why People Trust DesignRush
Rated 4.8 on Google and 4.7 on Trustpilot, DesignRush Agency Directory is a reliable resource for finding top cybersecurity companies. We owe this to our executive selection team, which follows a strict screening process when featuring agencies on the platform, assessing key performance indicators, like portfolio, client reviews, and industry reputation.
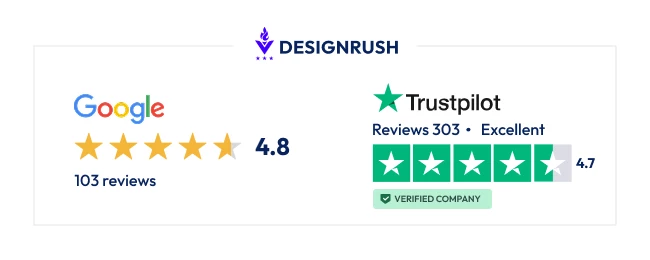
Sources
DesignRush sustains a directory of over 40,000 agencies categorized by service category, location, expertise, and reviews. We build our database in two ways:
- Our dedicated team of agency experts actively searches the web for top-performing companies. We then pull information from their websites, online presence, and client testimonials to verify their status and qualifications prior to listing.
- The agencies listed get notified of their profiles on the website and they can choose to claim it or not, which suggests their availability for more collaborations.
Agencies can also reach out to DesignRush and must go through the verification process prior to being listed.
6 Frequently Asked Questions About Cybersecurity Companies
When should you hire a cybersecurity services provider vs. keeping it internal?
Hire a cybersecurity services provider when the work requires independent validation, specialized expertise, or round-the-clock coverage that your internal team cannot reliably provide.
Internal IT teams are often excellent at day-to-day operations, but many are not staffed or equipped to deliver the depth of security expertise needed for advanced threat detection, incident response, penetration testing, or compliance assessments.
That said, internal IT and external cybersecurity firms are not mutually exclusive.
Many businesses use both: the internal IT manages day-to-day infrastructure, while an external company providing cybersecurity services handles threat monitoring, incident response, penetration testing, or compliance audits.
A good time to bring in a cybersecurity company is when your team is being asked to manage security risks beyond its training, capacity, or specialization.
When should you work with specialist cybersecurity firms, full-service partners, or managed security service providers?
Choose a specialist for a narrow high-stakes problem that requires deep expertise, a full-service cybersecurity partner for a coordinated strategy and execution across multiple workstreams, and a managed security service provider (MSSP) for ongoing monitoring, detection, and response.
Below is a side-by-side comparison:
| Focus | Engagement style | Best for | |
| Specialist cybersecurity firms | Deep expertise in one domain, such as digital forensics, penetration testing, or cloud security | Project-based, but some offer retainer engagements | Breaches, point-in-time assessments, or complex niche problems |
| Full-service cybersecurity service providers | Strategy, implementation, advisory, and ongoing program support across multiple domains | Project-based or long-term retainer | Organizations building or maturing a security program, consolidating vendors, or needing vCISO support |
| MSSP | Security monitoring, alert triage, threat detection, and incident response, often 24/7 | Recurring managed security contract | Organizations that need continuous security operations without building their own SOC |
How much should you realistically budget for cybersecurity services?
A realistic cybersecurity budget is approximately 5%-15% of your IT budget for small businesses with 1-10 employees, and 10%-20% of the IT budget for larger firms with a team of 51-100 professionals.
Additionally, the Security Budget Benchmark report found that organizations globally allot 13.2% of their IT budget to cybersecurity.
Although these are common benchmarks, you should budget based on your organization's size, industry, regulatory obligations, risk exposure, security maturity, internal capability, project scope, and whether the engagement is project-based or ongoing.
How can you verify the credentials of cybersecurity service providers?
Verify the credentials of cybersecurity service providers by checking both firm-level assurance and individual staff credentials.
Ask for current, independently verifiable certifications or audit reports, confirm that the people assigned to your engagement hold credentials relevant to the work, and review recent projects that match your environment and scope.
For instance, ISACA certifications can be checked using the certification number and last name. For firm-level assurance, ask for a current SOC 2 Type II report, ISO/IEC 27001 certification, or relevant CREST accreditation when applicable.
While certifications signal technical knowledge, they do not always confirm business fit.
A more viable approach is to look for practical experience in conjunction with certificates that align with your specific IT environment and situation.
How do you know if a cybersecurity services company is the right fit for your business?
A cybersecurity services company is the right fit when it has relevant experience in your industry, technical environment, and the specific security challenges you need to solve.
A cybersecurity services company is the right fit for your business if:
- It shows recent work in your stack, architecture, operating model, and sector.
- It can explain risk in both technical and business terms.
- It offers processes, reporting, and staffing to match your team's capacity.
- It understands the legal, regulatory, and contractual requirements that impact your business.
- It demonstrates how its work leads to remediation, retesting, or operational change.
What should you expect to receive at the end of the engagement?
At the end of your engagement with a cybersecurity services provider, expect to receive a clear final report package that explains what was reviewed, what was found, how severe the issues are, and what should happen next.
In most cases, that includes:
- Technical report documenting scope, methodology, findings, and supporting evidence
- Executive summary that communicates risk in the business context
- Remediation plan that ranks issues by priority and actionable next steps
- Retesting results, validation evidence, or compliance-specific reporting, if included in scope
If the deliverables stop at a list of flaws with no prioritization, ownership path, validation plan, or business context, then you bought evidence of risk rather than a practical strategy to help reduce it.
About The Author and Expert Reviewer
Selina Garcia has authored 500+ articles and edited 50+ published books in economics, law, and history. Her unique blend of experiences allows her to approach content creation from a well-rounded perspective. Currently, Selina applies her expertise to producing insightful articles on IT, software, and applications for DesignRush.
Sergio is a technology leader with over six years of experience managing global teams and delivering projects across fintech, sportstech, and B2B platforms. At DesignRush, he drove product growth and development execution, building tools that speed up processes by 95% and cut costs by 35% while maintaining full uptime.


















































