Enterprise cybersecurity is the practice of protecting an organization’s digital systems, data, and networks from unauthorized access and threats. It plays a crucial role in safeguarding sensitive information and ensuring business continuity.
With the number of cyberattacks growing in frequency and sophistication, strong security measures are vital for mitigating risks and avoiding financial losses.
Let’s take a look at the top tips every enterprise should implement to enhance its cybersecurity posture and stay ahead of potential threats.
1. Implement Multi-Factor Authentication (MFA)

Passwords alone no longer provide adequate security against cyberattacks. Multi-factor authentication (MFA) introduces additional layers of verification, making unauthorized access significantly harder. It combines at least two independent credentials: something the user knows (a password), something they have (a phone or device), or something they are (biometric data like fingerprints).
To implement MFA:
- Start by choosing a trusted provider such as Google Authenticator, Duo Security, or Microsoft Authenticator.
- Then, integrate it across systems, focusing on applications with sensitive data like email, file storage, or CRM software.
- Encourage employees to enroll in MFA by explaining the added security benefits and offering guides to help them set it up.
Additionally, some systems allow IT departments to enforce MFA policies organization-wide.
2. Conduct Regular Security Awareness Training

Humans remain the weakest link in cybersecurity. Training employees helps them recognize and prevent cybersecurity threats such as phishing, ransomware, and social engineering.
Here are a few steps you can take to implement this:
- The first thing you should do is assess the current knowledge level of your workforce.
- Then, organize workshops or e-learning modules to cover key topics like spotting fraudulent emails, creating strong passwords, and securely handling sensitive data.
- Use platforms like KnowBe4 or Cyber Awareness Academy to deliver engaging content.
- Supplement the training with phishing simulations to measure improvement over time.
- Reward individuals who report potential threats, reinforcing positive behavior.
For a guide to creating effective training sessions, visit KnowBe4’s Resource Hub.
3. Establish a Robust Cybersecurity Policy

Every organization needs a clearly defined cybersecurity policy. A strong framework outlines acceptable behaviors, password requirements, incident response plans, and access control rules.
Key steps include:
- Start by auditing existing systems to identify gaps.
- Then, draft a policy that aligns with industry security standards, such as that of the National Institute of Standards and Technology (NIST) or ISO 27001.
- Involve important personnel, such as IT staff and department heads, to ensure buy-in and relevance.
- Review and update the policy annually or after major incidents to stay ahead of emerging threats.
- Communicate changes effectively to employees through meetings, emails, or digital handbooks.
4. Perform Regular Vulnerability Assessments and Patching
Cybercriminals often exploit known vulnerabilities in software. Regular assessments help identify weak points before attackers do.
- Use tools like Nessus or OpenVAS to scan your systems for security flaws.
- Prioritize critical vulnerabilities and apply patches promptly. Additionally, automating updates can minimize delays and reduce human error.
- For systems that cannot be patched immediately, consider mitigating risks by limiting access or implementing monitoring tools.
- Perform these assessments quarterly or more frequently for high-risk environments.
Our in-depth guide on vulnerability management provides further insights.
5. Adopt a Zero-Trust Security Model
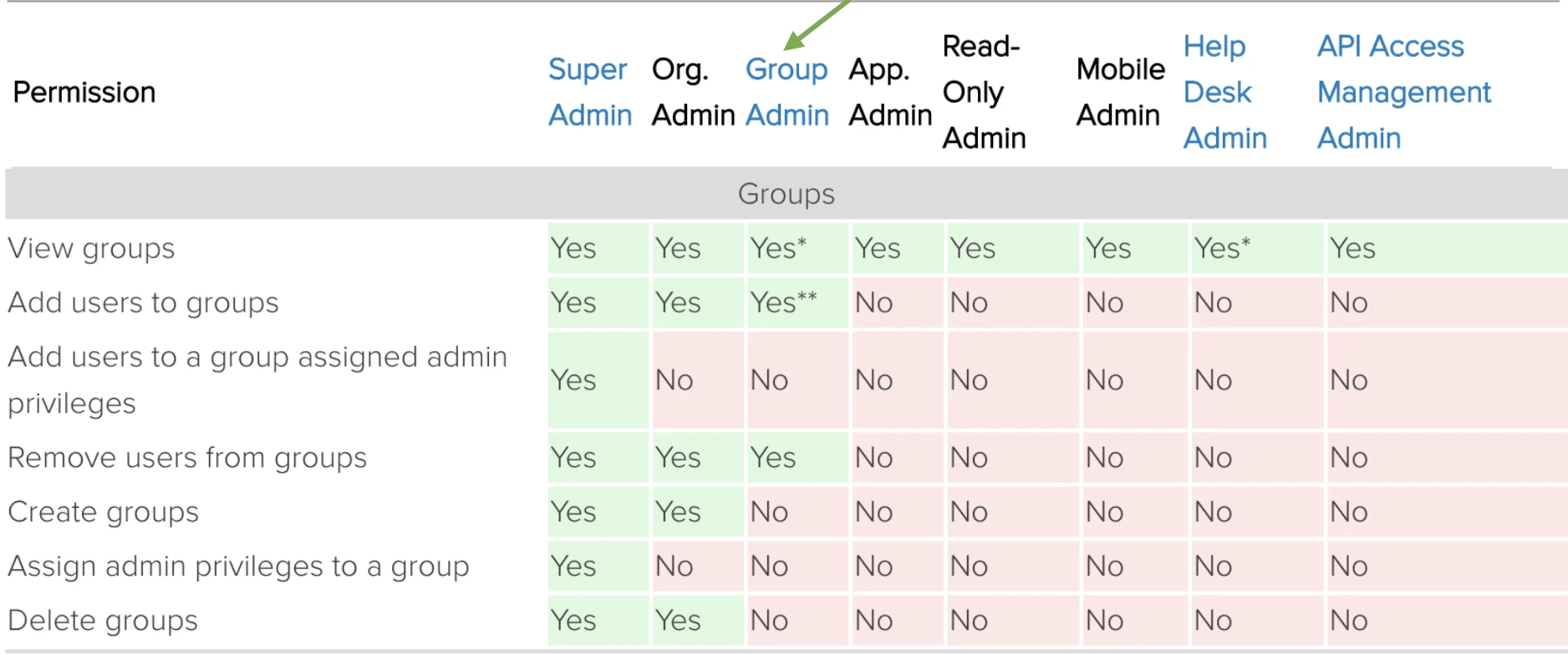
The zero-trust model assumes that no person or device can be trusted by default, even if it’s inside the corporate network. It requires continuous verification of identity and device security before granting access.
To adopt zero trust:
- Start by mapping out all assets and their access points.
- Implement solutions like identity and access management (IAM) software, such as Okta or Microsoft Entra ID, to control user permissions.
- Segment your network to limit lateral movement in case of breaches.
- Regularly audit access logs to ensure compliance.
For an in-depth look at zero trust implementation, read CSO Online’s Zero Trust Guide.
6. Secure Endpoint Devices
Endpoints like laptops, smartphones, and IoT devices are frequent attack targets. Secure your endpoint devices by following these best practices:
- Protect them with robust endpoint detection and response (EDR) solutions like CrowdStrike or Carbon Black.
- Ensure all devices have updated antivirus software and enforce encryption policies for sensitive data.
- Restrict the use of personal devices for work-related tasks unless managed through a secure BYOD (bring your own device) policy.
- Enable remote wipe capabilities to safeguard data on lost or stolen devices.
If you’d like to learn more, we’ve already covered endpoint security in detail.
7. Encrypt Sensitive Data
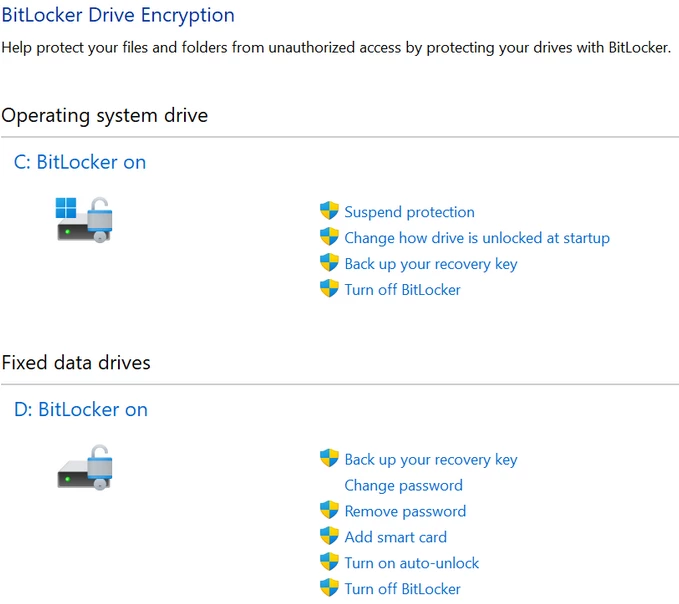
Encryption ensures that data remains unreadable even if intercepted. To protect sensitive information, implement the following encryption practices:
- Incorporate data encryption both at rest and in transit.
- Use tools like BitLocker for Windows systems or FileVault for Mac devices to secure stored information.
- Implement TLS (Transport Layer Security) protocols for encrypting data sent over the internet.
- Train employees in the importance of using encrypted communication channels, especially when handling sensitive client or business data.
- Encrypt backups as well, ensuring that disaster recovery processes maintain security.
Check out Microsoft’s Encryption Guide for practical guidance on this matter.
8. Develop and Test Incident Response Plans

When breaches occur, swift and effective response can minimize damage. A well-documented incident response plan outlines the steps to contain, eradicate, and recover from attacks.
Here are steps you can take to strengthen your plan:
- Assign roles and responsibilities within the organization, ensuring all team members know their duties.
- Regularly test these plans through simulations and tabletop exercises.
- Evaluate the results to identify gaps and refine your approach.
- Include external contacts, such as cybersecurity consultants, in the plan for complex incidents.
You can find best practices and templates for incident response planning via the Cybersecurity and Infrastructure Security Agency (CISA) website.
9. Monitor Networks Continuously

Continuous monitoring detects anomalies before they escalate into full-scale breaches.
- Take advantage of tools such as security information and event management (SIEM) systems to aggregate and analyze data from across the network.
- Use platforms like Splunk or SolarWinds to help identify unusual activity in real time.
- Encourage proactive monitoring by training IT teams to respond quickly to alerts.
- Combine automated tools with manual review processes to ensure accuracy.
- Regularly update monitoring systems to keep pace with evolving threats.
10. Manage Third-Party Risks

Third-party vendors often have access to sensitive systems, making their security practices a priority. To manage third-party risks:
- Start by assessing each vendor’s cybersecurity measures through questionnaires or audits.
- Require vendors to follow your organization’s security standards as part of contractual agreements.
- Implement network segmentation to limit vendor access and use monitoring tools to track their activities.
- Periodically review these relationships to ensure compliance.
Resources like Deloitte’s Guide to Vendor Risk Management offer practical tips for managing third-party risks effectively.
Enterprise Cybersecurity Takeaways
Enterprise cybersecurity is essential for protecting an organization’s digital systems, data, and networks from unknown threats. It ensures the security and integrity of vital company sensitive information, which makes it a critical component of modern business operations.
With the increasing frequency of cyberattacks, strong security measures are necessary to reduce vulnerabilities and stay ahead of potential threats. Proactive steps not only protect against disruptions but also safeguard business continuity.
By implementing tailored strategies and maintaining vigilance, you can effectively enhance your cybersecurity posture and adapt to evolving threats.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the Top Cybersecurity Companies as well as:
- Top Cybersecurity Marketing Agencies
- Top Cybersecurity Incident Response Companies
- Top AI Cybersecurity Companies
- Top Cybersecurity Companies in Virginia
And don’t miss our Awards section, where we celebrate the most innovative projects in design — from logo and app design to print and packaging.






