Cyberattacks like ransomware and phishing are hitting small businesses harder than ever, and while modern EDR tools offer advanced defenses, their effectiveness varies. We've identified trusted vendors to ease the selection process.
Best EDR Solutions for Small Business: Key Point
- Nearly half of all global cyberattacks target small businesses, yet these organizations are often underprepared to defend themselves.
- EDR tools with automated remediation reduce incident response time by up to 95%, as shown in platforms like CrowdStrike and Microsoft Defender.
- MITRE ATT&CK framework integrations encompass a common EDR offering, used to map detections to adversary tactics.
- The majority of the providers offer free trials, while paid packages start at $59.99 per endpoint.
Best EDR Solutions for Small Business Overview
Small businesses are the target of nearly half of all global cyberattacks, yet many lack the internal resources to respond effectively. To spare you the trial-and-error of comparing countless tools, we’ve narrowed the field to eight EDR providers that cater to small
businesses.
| Provider | Threat detection | Automated response | Endpoint visibility | Root cause analysis | Pricing (starting at) |
| Sophos | ✅ MITRE ATT&CK mapping | ✅ Process termination, rollback, and containment | ✅ | ✅ Rich telemetry, timeline views, and context-aware investigation tools | Available per inquire |
| SentinelOne Singularity | ✅ Real time static and behavioral analysis | ✅ Automated device isolation and single-click rollback | ✅ Powered by centralized console and single-agent architecture | ✅ Reconstructs attack paths and supports forensic analysis | $179.99/end point |
| Palo Alto Networks Cortex XDR | ✅ MITRE ATT&CK evaluations | ✅ Native automation | ✅ Single agent architecture | ✅ Automated reconstruction of attack paths | Custom pricing |
| CrowdStrike Falcon® Insight XDR | ✅ AI, behavioral analytics, and adversary intel | ✅ Orchestrated, autonomous remediation | ✅ Single agent architecture | ✅ Reconstruction of attack chains | Free trial available |
| Symantec Endpoint Protection | ✅ Signature, behavioral, and anomaly detection | ✅ Policy-based automatio, threat quarantine | ✅ Single-agent telemetry and unified console | ✅ Attack chain analytics and forensic investigation | Custom pricing |
| Microsoft Defender For Endpoint | ✅ Global telemetry, behavioral analytics, MITRE ATT&CK evals | ✅ Automated investigation and remediation | ✅ | ✅ Incident timelines, attack graphing | Free trial available |
| Trend Micro Vision One | ✅ Correlated telemetry | ✅ Policy-based remediation and response orchestration | ✅ Unified monitoring of endpoints, servers, legacy devices, and IoT | ✅ Attack chain visualization and behavioral mapping | Free trial available |
| Bitdefender GravityZone | ✅ Behavioral analysis, process monitoring | ✅ Quarantine, rollback, and process termination | ✅ Centralized visibility across endpoints, servers, IoT, and legacy systems | ✅ Traceable attack chain and impact | Free trial available |
1. Sophos
Sophos provides a unified, AI-native detection and response platform encompassing both EDR and extended detection and response (XDR) capabilities.
Built on top of Sophos’ Intercept X endpoint protection, the EDR solution addresses the full threat lifecycle through a single, lightweight agent and cloud-based management interface.
| Key features | Pricing |
|
|
EDR delivers deep visibility into endpoint and server activity, enabling organizations to detect, investigate, and respond to threats that bypass initial defenses.
It retains rich telemetry data (up to 90 days, extendable to one year) from endpoints and servers, allowing for historical and real-time analysis.
Threat analysts and IT admins can interact with this data using an intuitive search interface that does not require SQL, yet supports advanced querying through customizable templates.
Its live response capabilities provide secure, audited shell access to affected endpoints, enabling direct command execution such as killing processes, removing malicious artifacts, or updating configurations.
Sophos also emphasizes response acceleration, offering automated remediation actions like process termination, ransomware rollback, and network isolation. The company offers the EDR package as a managed service as well.
2. SentinelOne Singularity

SentinelOne Singularity is an advanced endpoint security platform that integrates EDR, XDR, and next-generation endpoint protection (EPP) within a single-agent architecture.
Envisioned as a low operational overhead solution, it provides real-time threat prevention, automated response, and deep forensic analysis across distributed enterprise environments.
| Key features | Pricing |
|
|
At its core, Singularity uses AI-powered static and behavioral analysis to identify and mitigate known and unknown threats autonomously, without reliance on signature-based methods.
The platform is engineered to act without human intervention, making it particularly effective for resource-constrained security teams or small businesses.
The EDR component includes SentinelOne's proprietary Storyline technology, which constructs attack timelines by correlating telemetry across systems, enabling root cause analysis and contextual decision-making.
This facilitates forensic investigations and rapid triage without manual correlation effort.
The platform's centralized management console offers complete operational visibility and control, while its rollback feature restores endpoints to a known-good state after ransomware attacks or other destructive activity.
3. Palo Alto Networks Cortex XDR
Cortex XDR, developed by Palo Alto Networks, is a unified detection and response platform that consolidates EDR with extended visibility across cloud, network, and identity sources.
Its core function is to reduce organizational risk by detecting, correlating, and responding to threats in real time using a single-agent architecture powered by AI and behavioral analytics.
| Key features | Pricing |
|
|
At endpoint level, Cortex XDR delivers robust protection against a wide range of attack techniques including fileless malware, in-memory exploits, and process hijacking.
Its AI-driven prevention modules are engineered to stop zero-day and advanced persistent threats before execution, with demonstrated 100% detection and zero false positives in the latest MITRE ATT&CK evaluations.
For detection and triage, Cortex XDR uses cross-data correlation and machine learning to reduce alert volume by 98%, allowing security teams to focus on high-fidelity incidents.
Automated root cause analysis further reconstructs the full attack chain for each alert to reduce investigation time.
The platform also extends to full XDR, integrating endpoint telemetry with cloud, network, and identity sources. It supports native incident response automation and integrates with NG-SIEM, SOAR, and ASM modules in the Cortex platform to provide a cohesive SOC environment.
4. CrowdStrike Falcon® Insight XDR
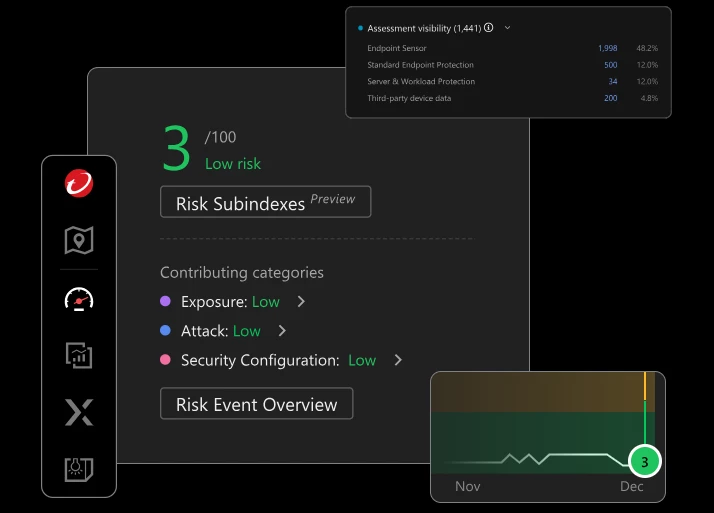
CrowdStrike Falcon Insight XDR is an AI-driven detection and response platform that grants unified protection across endpoints, identities, cloud workloads, and networks.
Built on a single-agent architecture and powered by CrowdStrike’s adversary intelligence, the platform delivers end-to-end visibility, autonomous response, and contextual detection with high accuracy.
| Key features | Pricing |
|
|
Falcon Insight’s EDR offering uses behavioral analytics, AI-powered detection, and real-time response (RTR) capabilities to identify and contain sophisticated threats including ransomware, fileless malware, and lateral movement.
Its automated triage accelerates investigation workflows and maps activity to MITRE ATT&CK for threat context and root cause determination.
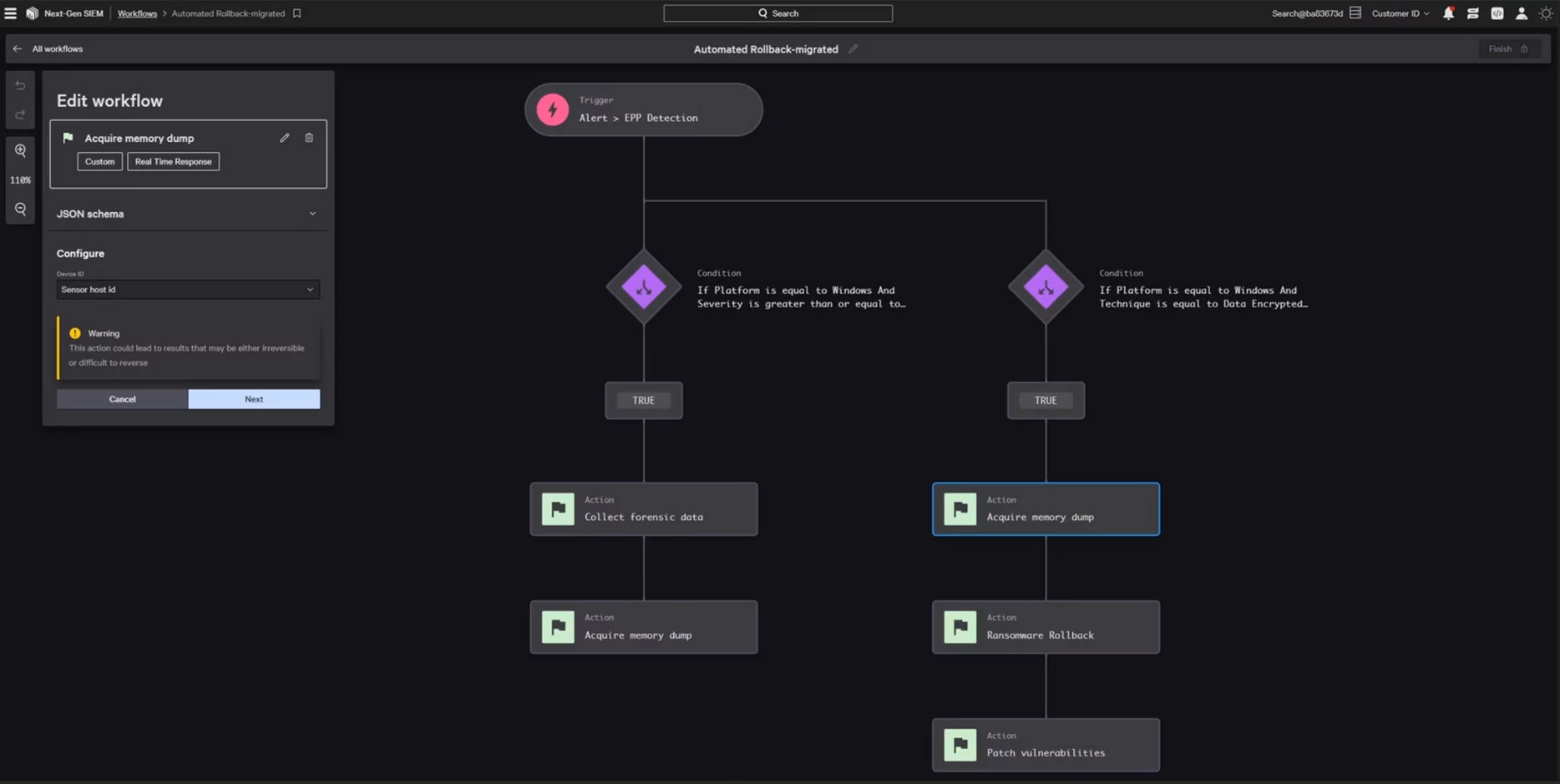
On the XDR end, Falcon Insight extends correlation and visibility beyond endpoints by integrating telemetry from identity systems, cloud environments, mobile devices, and third-party data sources.
Native orchestration via Falcon Fusion enables automated playbooks for incident response and reduces mean time to respond by up to 95%. The tool also offers built-in SOAR capabilities, managed detection and response (MDR), and expert-led threat hunting.
5. Symantec Endpoint Protection

Symantec Endpoint Security, developed by Broadcom Inc., is a multi-layered endpoint protection platform that combines traditional security controls with advanced detection and response capabilities.
Built on the foundation of Symantec Endpoint Protection (SEP), it integrates prevention, detection, and automated response into a single-agent architecture.
| Key features | Pricing |
|
|
The platform’s capabilities extend to antivirus, anti-spyware, intrusion prevention, and application control to reduce the attack surface.
It also incorporates anomaly detection by aggregating user behavior patterns, allowing it to identify and respond to suspicious activity in real time.
Its access policy engine enables granular control, while threat quarantine features help isolate compromised assets and prevent lateral movement.
The EDR capabilities, available in the Endpoint Security Complete tier, provide threat hunting, advanced analytics, and automated remediation. XDR functionality is also available through extended telemetry and integration across endpoint and mobile environments.
The platform supports several deployment options, including cloud-based, on-premises, and hybrid models.
6. Microsoft Defender For Endpoint
Microsoft Defender for Endpoint is a unified endpoint security solution that consolidates EDR, XDR, antivirus, and threat and vulnerability management.
The solution is a good match for organizations using Microsoft 365, as it delivers deep platform integration, broad telemetry coverage, and native automation to secure devices across Windows, macOS, Linux, Android, iOS, and IoT environments.
| Key features | Pricing |
|
|
In terms of EDR, Defender provides behavioral-based detection, incident correlation, attack timeline reconstruction, and real-time investigation capabilities.
Underlined by Microsoft’s global threat intelligence network, the tool detects known and novel threats across endpoints and the broader enterprise estate.
Automated investigation and remediation workflows reduce mean time to respond, while deception technologies and endpoint attack notifications enhance threat containment.
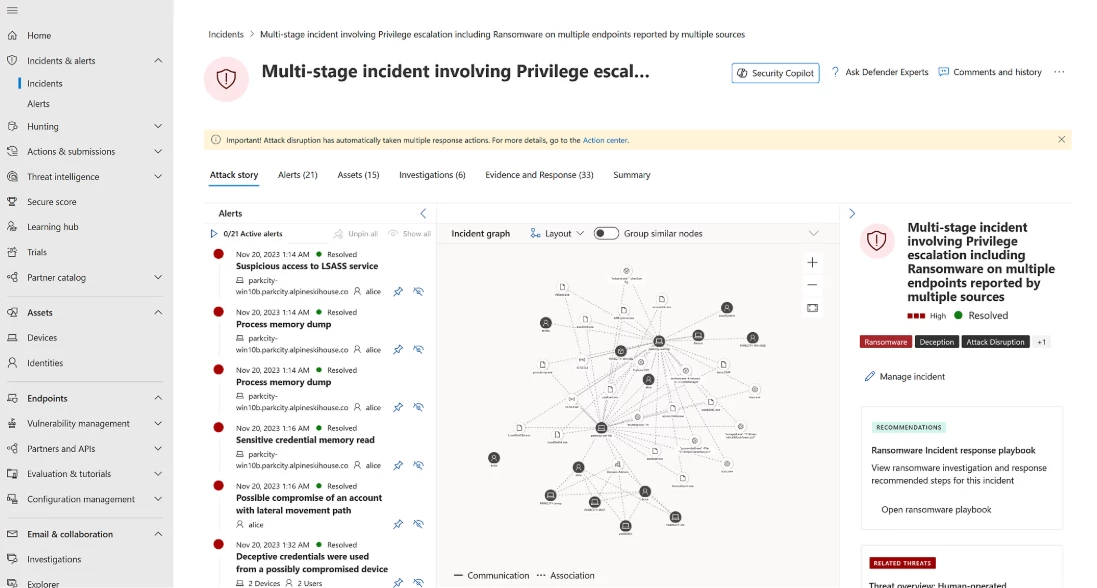
Defender’s XDR functionality is embedded in Microsoft Defender XDR, offering native integration with other Microsoft security tools such as Microsoft Sentinel (SIEM), Azure AD, and Microsoft 365 services.
This unified architecture allows for correlation of telemetry across endpoints, identities, apps, cloud, and email, supporting cross-domain investigations and coordinated responses.
The platform is powered by machine learning and AI to automate triage, risk prioritization, and incident response. It also offers layered defenses against ransomware and fileless attacks through real-time protection and network-based threat disruption.
7. Trend Micro Vision One
Trend Micro Vision One was engineered to reduce security silos and deliver cross-layer threat detection and response.
Intended for modern, heterogeneous IT environments, it protects endpoints, servers, IoT devices, cloud applications, email, and networks via a centralized architecture that consolidates telemetry and correlates attack signals with precision.
| Key features | Pricing |
|
|
The platform’s EDR component provides native endpoint visibility, advanced threat analytics, and response orchestration directly from a centralized console.
It supports rapid detection and containment of threats across endpoints and legacy systems, with built-in support for automated policy enforcement and real-time remediation.
Its integration of behavioral analysis and AI-driven correlation enables high-fidelity detections without requiring manual tuning.
Trend Micro’s XDR offering aggregates and enriches telemetry from a broad set of native sensors across email, cloud, endpoint, and network layers, to deliver end-to-end visibility and attack path reconstruction.
The system maps malicious behavior across these vectors, allowing for context-aware response actions and reducing the time to detect and contain threats. Managed detection and response (MDR) services are also available across the company’s portfolio.
8. Bitdefender GravityZone
Bitdefender GravityZone combines EDR and XDR capabilities into a unified system, specifically engineered for small and midsize businesses (SMBs) with limited resources but demanding security requirements.
Empowered by signatureless threat detection, behavioral analytics, and machine learning, the solution identifies zero-day attacks, ransomware, fileless threats, and other advanced risks.
| Key features | Pricing |
|
|
As part of its EDR offering, GravityZone provides detailed endpoint telemetry, automated response mechanisms, and centralized investigation capabilities through a single-pane-of-glass console.
When threats are detected, the system initiates immediate remediation steps such as process termination, quarantine, rollback of unauthorized changes, and policy enforcement based on preconfigured risk thresholds.
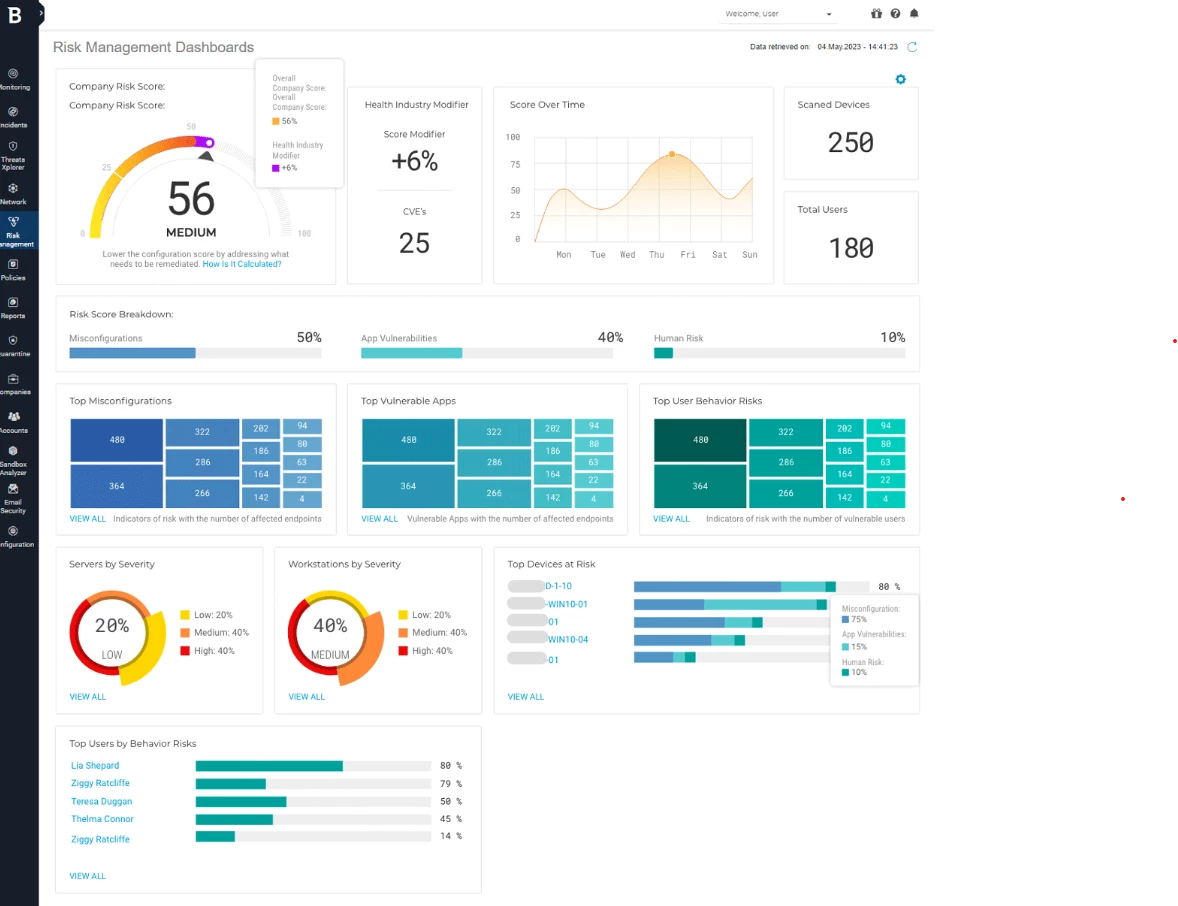
Bitdefender’s XDR capabilities extend visibility beyond the endpoint by correlating data across email, network, and cloud applications through native sensors.
This correlation allows for faster identification of attack campaigns and coordinated response across multiple vectors.
Best EDR Solutions for Small Business: Final Thoughts
As cyber threats are evolving in complexity, small businesses are increasingly in the crosshairs. To keep pace, investing in a robust EDR solution is a proactive measure to maintain a robust security posture.
If overseeing threat management across distributed, hybrid, or remote teams is stretching your internal resources thin, engaging a dedicated security partner can bring in the expertise needed to safeguard your endpoints.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory to find top-rated cybersecurity companies, as well as:
- Top Digital Forensics Companies
- Top Identity Access Management Companies
- Top Penetration Testing Companies
- Top Security Assessment Companies
To get a bit more insight into the biggest security risks we can anticipate in the coming years, we spoke with Christopher Barber, CEO and founder of Cheaper Than A Geek. Here’s his take:
“At this point, it looks like AI-assisted cyber attacks could do some damage. The more realistic the attack, the more likely it is to succeed. Good cyber hygiene, combined with training and testing is key.”
Best EDR Solutions for Small Business: FAQs
1. What should small businesses prioritize when evaluating EDR solutions?
Focus on ease of deployment, automated remediation capabilities, and a unified dashboard. For lean teams, solutions with minimal manual configuration and built-in threat intelligence are likely to drive ROI faster and reduce alert fatigue.
2. Can EDR tools integrate with existing IT infrastructure and tools?
Most modern EDR platforms offer native integrations with common productivity suites, cloud services, and SIEM tools. Check for API access and compatibility with your operating systems, email platforms, and authentication tools before committing.
3. Is EDR overkill for a business with fewer than 100 endpoints?
Not at all. Small businesses are often targeted due to weaker defenses. Lightweight EDR tools with centralized management and automation are specifically designed for environments with limited IT personnel.






