The Health Insurance Portability and Accountability Act of 1996 (HIPAA) is more than just a regulatory requirement — it’s a pillar of patient trust and privacy in the healthcare industry.
HIPAA empowers patients by granting them rights to access and control their health information. This transparency encourages them to take an active role in their healthcare, leading to better health outcomes and stronger patient-provider relationships.
Despite its importance, many are unclear about what HIPAA compliance entails and why it’s essential. Let’s explore its intricacies, who it affects, the rules it enforces, and the common pitfalls to avoid.
What Is HIPAA Compliance?
HIPAA is a US law designed to protect sensitive patient data. HIPAA compliance involves going by the standards and practices established to ensure the confidentiality, integrity, and security of protected health information (PHI).
Entities covered under HIPAA must implement safeguards to protect patient information from unauthorized access and breaches. This involves a comprehensive approach to managing how PHI is used, stored, and shared, both electronically and physically.
Who Needs To Be HIPAA Compliant?
HIPAA compliance is mandatory for specific entities, primarily within the healthcare sector.
- Healthcare providers: If they manage patient health information, they must be compliant, and by ‘they,’ we mean doctors, clinics, psychologists, dentists, chiropractors, nursing homes, and pharmacies.
- Health plans: This includes health insurance companies, health maintenance organizations (HMOs), company health plans, and government programs.
- Healthcare clearinghouses: Entities that process nonstandard health information into a standard format are also required to comply.
- Business associates: Any third party that handles PHI on behalf of a covered entity, such as billing companies, transcription services, and IT providers, must also adhere to HIPAA regulations.
What Are the Rules of HIPAA?
HIPAA compliance is built around several critical rules, each designed to uphold the protection of PHI. Understanding these rules is essential for any entity handling health information. Let’s break them down.
Privacy Rule
This rule sets the standards for protecting patients' health information. It dictates when and how patient information can be shared, ensuring patients have control over their data.
For example, if a patient requests their medical records to be sent to a specialist for a second opinion, the privacy rule ensures this can be done securely and that the patient can authorize or restrict further sharing of this information.
Security Rule
This rule focuses on electronic protected health information (ePHI). It provides guidelines for securing ePHI through administrative, physical, and technical safeguards.
For instance, a hospital implementing this rule would use encryption to protect patient data stored in electronic health records (EHRs) and establish strong passwords and access controls to ensure only authorized staff can view sensitive information.
Breach Notification Rule
If there's a data breach, this rule requires entities to notify the affected individuals, the Department of Health and Human Services (HHS), and sometimes the media.
For example, if a healthcare provider’s system is hacked and patient information is compromised, the provider must quickly inform the patients affected by the breach, report the incident to the HHS, and if the breach involves more than 500 patients, notify the media too.
Enforcement Rule
This rule outlines the procedures for investigations and the penalties for HIPAA violations. It ensures there are consequences for not following HIPAA rules.
For example, if a clinic fails to conduct regular risk assessments and a breach occurs, it might face significant fines and be required to take corrective actions to prevent future violations.
Omnibus Rule
This rule enhances HIPAA by adding provisions from the Health Information Technology for Economic and Clinical Health (HITECH) Act. It extends HIPAA requirements to business associates — third parties handling health information — and strengthens overall privacy and security measures.
For example, a medical transcription service working for a hospital must comply with HIPAA regulations and implement safeguards to protect the patient data they handle.
Requirements for HIPAA Compliance
Achieving HIPAA compliance isn’t a one-time task but an ongoing process that requires continuous attention and action. If this sounds daunting already, you can always refer to the pros and let them handle the situation.
Let’s go through the fundamental requirements to ensure compliance.
- Risk analysis and management
- Policies and procedures
- Training and awareness
- Secure communication
- Access controls
- Data encryption
- Incident response
- Documentation
Risk Analysis and Management
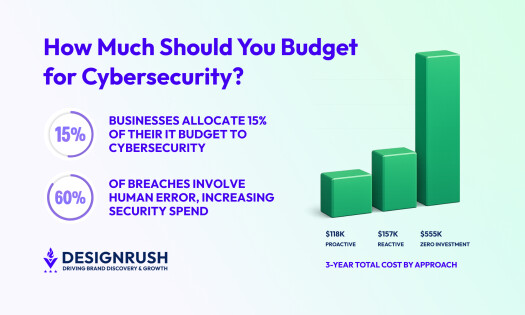
Conduct regular risk assessments to identify vulnerabilities and implement measures to mitigate them. Incorporating cybersecurity frameworks can help structure these assessments and ensure comprehensive coverage.
Let’s say a healthcare provider might discover that their electronic health record (EHR) system has outdated software that could be exploited by hackers. By identifying this risk, they can update the software and enhance their security protocols, which is made that much easier by hiring a cybersecurity company.
Policies and Procedures
Develop, maintain, and enforce comprehensive policies and procedures related to PHI handling. This includes everything from how data is stored to how it’s destroyed. For instance, a clinic might have a policy that mandates shredding paper records after they have been digitalized and securely stored.
Training and Awareness
Regularly train employees on HIPAA requirements and the importance of protecting PHI. An informed staff is your first line of defense against breaches. For example, holding quarterly training sessions on recognizing phishing emails can help prevent employees from inadvertently compromising sensitive data.
Secure Communication
Ensure all communication channels that handle PHI, such as emails and messaging apps, are secure and encrypted. For instance, a doctor sending patient information to a specialist should use a secure email service that encrypts the message to prevent unauthorized access.
Access Controls
Implement strict access controls to ensure only authorized personnel can access PHI. This involves user authentication, role-based access, and audit controls. For example, a hospital may use biometric scans for staff access to sensitive areas and regularly review access logs to detect any unusual activity.
Data Encryption
Encrypt PHI both in transit and at rest to protect it from unauthorized access. Encryption acts as a vital barrier against potential breaches. For instance, if a healthcare provider’s laptop is stolen, the encrypted data on the device would remain unreadable to unauthorized users.
Incident Response
Have a robust incident response plan in place to quickly address any breaches or security incidents, minimizing and even preventing potential damage. A healthcare organization might have a team ready to investigate and contain a ransomware attack, ensuring that patient data is recovered.
Documentation
Keep thorough records of all compliance efforts, including risk assessments, training sessions, and incident reports. Documentation is crucial evidence for demonstrating compliance and avoiding penalties. Maintaining detailed logs of all security audits and training programs can help prove compliance during an official inspection.
Most Common Violations of HIPAA Compliance
Now, despite best efforts, HIPAA violations can occur. We will go through some of the most common violations and some of the consequences associated with them.
Unauthorized Access
This type of violation involves employees accessing patient records without a legitimate reason. If a hospital employee, let’s say looks at a celebrity’s medical records out of curiosity or a nurse at a doctor's office discusses patient information in a public area, thoughtlessly for anyone to overhear, this would constitute unauthorized access.
In 2017, South Florida Memorial Healthcare System (MHS) paid $5.5 million for employees unlawfully accessing and selling PHI. MHS reported that two of its employees illegally accessed and stole PHI of over 115.000 patients to sell.
Lack of Encryption
This involves failing to encrypt ePHI, making it vulnerable to breaches. For example, in 2014, Touchstone Medical Imaging was informed by the FBI that one of its file transfer protocol (FTP) servers was accessible over the internet and allowed anonymous connections to a shared directory. The directory contained files that included the protected health information (PHI) of 307,839 individuals.
Because of this, Touchstone Medical Imaging has agreed to a settlement of $3 million to resolve the violations and adopted a corrective action plan (CAP) to address its HIPAA compliance issues.
Improper Disposal
Discarding PHI without following proper destruction protocols, such as shredding documents or wiping electronic devices. In 2021, the Massachusetts-based practice filed a breach report with the Office for Civil Rights (OCR) stating that empty specimen containers with labels that included PHI were thrown away in a garbage bin in the New England Dermatology and Laser Center’s (NEDLC) parking lot.
After investigation, the OCR settled a case with the practice to resolve a potential HIPAA violation involving improper PHI disposal. NEDLC paid $300,640 to OCR and agreed to implement a corrective action plan.
Unreported Breaches
Failing to notify affected individuals and authorities promptly after a breach can get you in a lot of trouble on top of the one you are having with the breach itself. A notable example of unreported HIPAA breaches involves Connecticut’s Health Insurance Exchange, Access Health CT.
An audit by the state auditor uncovered that Access Health CT had experienced 44 data breaches over the span of 3.5 years that had not been fully reported to the state auditor and comptroller, as required by state law.
Access Health CT concurred with the recommendations made in the report and said third-party vendors are assisting with the implementation of a new risk management framework, which will provide comprehensive visibility and oversight of compliance with the information security requirements of state and federal laws.
HIPAA Compliance Takeaways
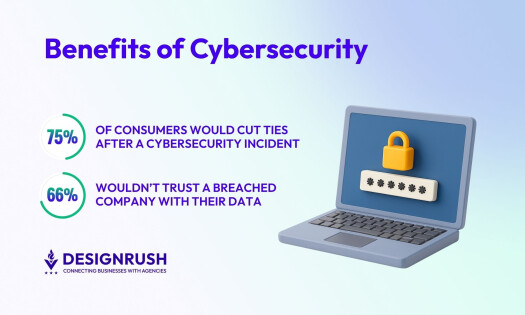
Navigating HIPAA compliance might seem daunting, but it is essential for safeguarding patient information and avoiding severe penalties.
Understanding its key aspects — from the definition and need for compliance to the specific rules and requirements — is crucial for any healthcare entity handling PHI. Regular risk assessments, thorough employee training, secure communication channels, and robust incident response plans are integral components of a HIPAA-compliant strategy.
Moreover, maintaining meticulous documentation of all compliance efforts ensures adherence to standards and readiness for audits. By following these guidelines, you can protect patient data, avoid common violations, and maintain trust and integrity in your operations.
HIPAA Compliance FAQs
What is PHI?
PHI stands for protected health information and includes any information about health status, provision of healthcare, or payment for healthcare that can be linked to an individual.
Who enforces HIPAA compliance?
The Office for Civil Rights (OCR) within the US Department of Health and Human Services (HHS) is responsible for enforcing HIPAA compliance.
Can patients file a complaint if they believe their PHI has been mishandled?
Patients can file a complaint with the OCR if they believe their PHI has been mishandled or their HIPAA rights violated.