Data security isn’t just an IT task — it’s a critical business priority. A single mistake can trigger a data leak that costs you money, customers, and your reputation. Cyber threats are evolving constantly, and a data leak can inflict severe damage beyond just your bottom line. It might lead to legal complications, erode customer trust, and, in worst-case scenarios, jeopardize the very existence of your business.
The good news is that with the right security measures in place, you can minimize these risks and keep your sensitive information safe. In this guide we’ll cover what data leak really is, lay out the essential strategies you need to prevent data leaks, protect your assets, and build a robust defense against potential cyber threats. Let’s dive in.
What Is a Data Leak?
The definition of a data leak refers to the unintentional exposure of protected, confidential, or sensitive information to unauthorized parties. Unlike a data breach involving malicious intent, a data leak typically happens due to accidental factors like human error, software misconfigurations, or weak security practices.
Data leaks can involve personal details, financial records, trade secrets, or other sensitive information. The result? Compromised data that can pave the way for future breaches, leading to financial losses, reputational damage, and potential legal consequences for both individuals and organizations.
Business data vulnerabilities often come from three key areas:
- Unintentional sharing of sensitive files
- Misconfigured cloud storage
- Mishandling customer information
These weak points are often overlooked but can quickly spiral into serious risks for your organization.
What makes data leaks so dangerous? They’re silent but devastating. Common scenarios — like forwarding work emails to personal accounts or using unauthorized cloud services — may seem harmless but often lead to major data exposures.
While the terms “data leak” and “data breach” are often mixed up, the distinction lies in intent: leaks are accidental, often stemming from poor security setups, while breaches involve deliberate exploitation. Understanding this difference is key to strengthening your organization’s data security strategies. Let’s explore this further.
The Difference Between Data Leaks and Data Breaches
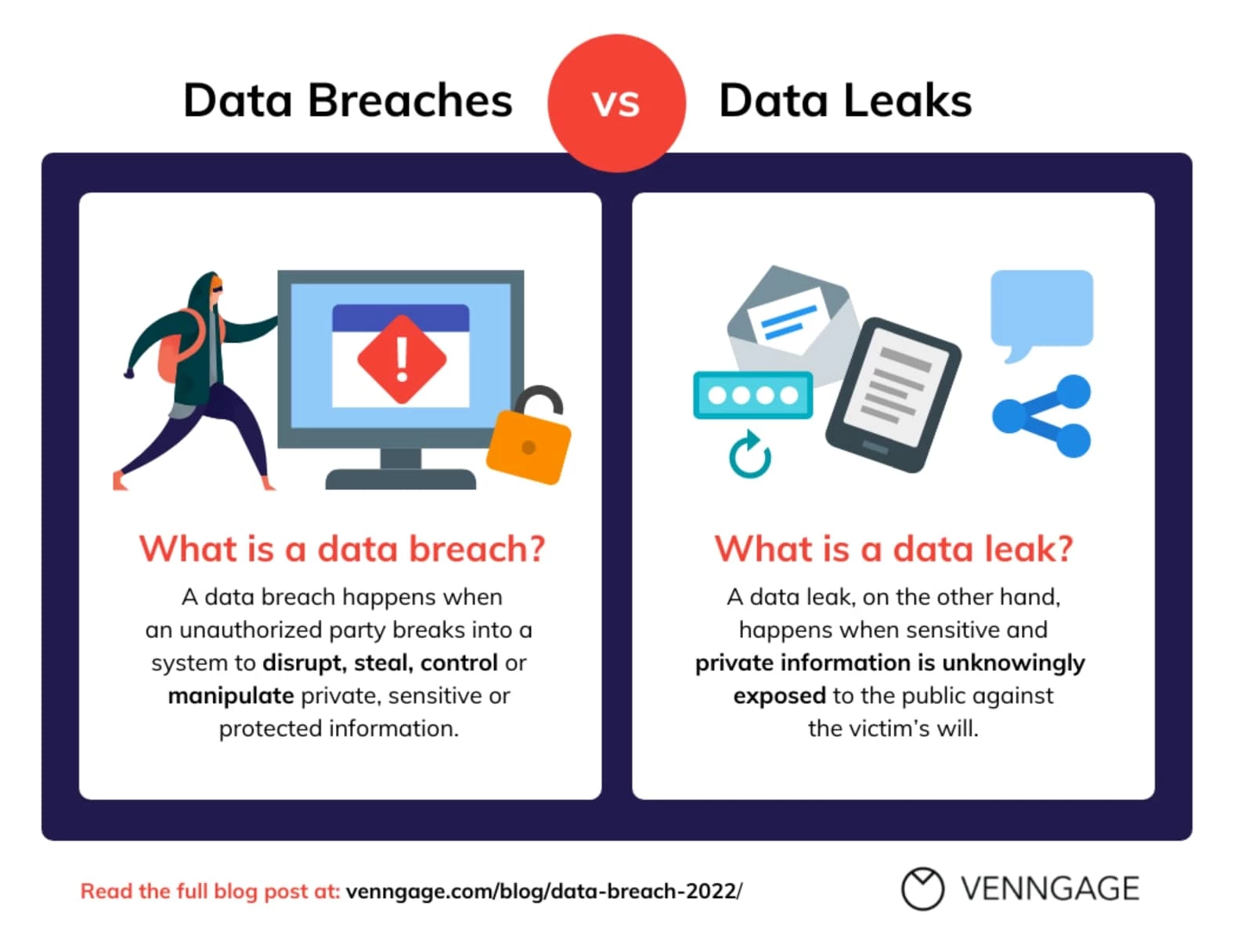
Data leaks and data breaches may both expose sensitive information, but the causes and impacts set them apart. A data breach is a calculated attack — cybercriminals exploiting system vulnerabilities to steal data. A data leak, on the other hand, is accidental, often triggered by human error, misconfigurations, or sloppy security practices.
Both are serious threats, but they call for different prevention strategies. Addressing these challenges starts with understanding their unique risks. By identifying vulnerabilities and tailoring security measures, businesses can protect critical information and reduce the fallout from leaks and breaches.
Comparing Data Leaks & Data Breaches
Let’s compare data leaks and data breaches side by side to highlight their key differences more clearly.
| Aspect | Data Leak | Data Breach |
| Intent | Unintentional exposure | Deliberate attack |
| Source | Internal vulnerabilities | External threats |
| Detection Time | Often discovered by third parties | Usually detected through security systems |
| Scale | Typically limited to specific data sets | Can affect entire systems |
| Response Needed | Internal process review | Immediate security intervention |
| Cost Impact | $422.61 average recovery cost | $9.36 million average recovery cost |
| Prevention Focus | Process improvement | Security enhancement |
| Legal Requirements | May require notification | Mandatory reporting |
Let’s look at a real-world example: a team member accidentally sets incorrect cloud permissions, causing a data leak. Contrast this with a breach, where hackers actively exploit firewall gaps to gain access. These differences highlight the importance of tailored security measures to address each threat effectively and protect your organization’s critical data.
7 Steps to Protect Your Business From Data Leaks
Strong data security starts with smart strategies. Proven methods can help businesses protect sensitive information from data leaks in 2026 and beyond, ensuring their defenses stay a step ahead of evolving threats.
- Conduct regular security audits
- Implement strong access controls
- Educate employees on data security
- Utilize data loss prevention (DLP) tools
- Establish an incident response plan
- Monitor third-party risks
- Implement Zero-Trust architecture
1. Conduct Regular Security Audits
A quarterly assessment is integral for maintaining solid data security. By focusing on these major areas, businesses can proactively address risks and stay protected:
- System vulnerability scans: Regularly identify and address weaknesses in your infrastructure before cybercriminals can exploit them.
- Access permission reviews: Review who has access to sensitive data and systems, removing unnecessary permissions to reduce exposure.
- Data flow mapping: Monitor how data moves within your organization to find vulnerabilities and ensure secure handling of sensitive information.
- Compliance verification: Ensure your processes and systems align with current regulatory standards, minimizing legal and financial risks.
Together, these steps provide a comprehensive approach to safeguarding your data and keeping your security posture strong.
2. Implement Strong Access Controls
Effective data security begins with precise access management. Implement role-based access control (RBAC) to limit user access to only what they need, and pair it with multi-factor authentication (MFA) for an extra layer of protection.
Google Cloud has announced mandatory MFA for all users in 2025. This move aligns with industry trends, as AWS and Azure have also mandated MFA to combat phishing and credential theft. Regularly reviewing and updating permissions — ideally every 60 days — ensures access stays restricted to the right individuals, minimizing risks and keeping your systems secure.
Adding MFA through providers like Google ensures robust security, addressing the ongoing risks posed by stolen credentials and unauthorized access.
3. Educate Employees on Data Security
A training framework empowers teams with the knowledge and tools to protect sensitive information. It focuses on four main areas:
- Identifying sensitive data: Teach employees to recognize sensitive and confidential information, things like personal records, financial data, and trade secrets, ensuring they know what requires extra care.
- Proper data handling procedures: Provide clear guidelines on securely storing, sharing, and accessing data to minimize the risk of accidental exposure or leaks.
- Reporting potential leaks: Train staff to identify and report suspicious activity or data mishandling, thereby ensuring quick action to prevent further risks.
- Safe remote work practices: Equip remote employees with strategies to properly secure their devices, networks, and communications.
By tackling these areas, your framework builds a culture of security awareness, reducing risks and strengthening your organization’s defenses.
4. Utilize Data Loss Prevention (DLP) Tools

Data loss prevention (DLP) solutions are the frontline defense for monitoring and safeguarding sensitive information. These tools keep a keen eye on data movement patterns, ensuring that your organization’s most sensitive assets remain secure. Your security protocols should integrate these key measures for impenetrable data protection:
- Email scanning: DLP solutions analyze outgoing emails to detect sensitive information, such as personal or financial details, being sent outside authorized channels. This helps prevent accidental data leaks through email communication.
- File transfer monitoring: By tracking file transfers across your network, DLP tools catch unauthorized or unusual activity, ensuring sensitive files are only shared with the right parties.
- Unauthorized sharing prevention: Policies and technologies work together to block attempts to share protected data through unsafe methods, like unauthorized cloud platforms or external drives.
These protocols don’t just react to threats — they actively prevent them, ensuring your business’s data stays where it belongs.
5. Establish an Incident Response Plan

Clear response strategies are non-negotiable for handling data security incidents effectively. They empower teams to act fast, contain threats, and avoid costly fallout. A prepared team is the difference between a quick recovery and a massive escalation.
To stay ready, focus on these primary steps:
- Quarterly response drills: Regular simulations of potential security incidents — phishing attacks or data leaks — help teams practice their roles and responsibilities in a controlled environment. These drills build confidence, highlight areas for improvement, and keep response protocols sharp.
- Refining procedures: Each drill offers valuable insights. Post-drill reviews allow teams to identify gaps in the process, update response plans, and incorporate lessons learned to continuously enhance preparedness.
- Cross-department coordination: Response strategies should include clear communication protocols across IT, legal, PR, and leadership teams to ensure a smooth and unified response during an actual event.
- Real-world scenarios: Incorporate scenarios based on current threat trends to keep the drills relevant and aligned with current risks.
6. Monitor Third-Party Risks
Effective vendor management is needed to maintain a strong data security posture.
To protect your business, focus on these three areas:
- Regular security audits: Schedule routine audits to assess vendors’ security measures. This helps ensure their practices align with your organization’s standards and allows you to identify and address potential vulnerabilities early.
- Clear data handling agreements: Establish detailed agreements with vendors that outline how sensitive data will be accessed, stored, and shared. These agreements set clear expectations and boundaries, reducing the risk of mishandling.
- Precise third-party access inventories: Keep an updated inventory of all third-party access points, including who has access to your data and why. Regularly review and adjust these permissions to limit access to only what’s necessary.
By prioritizing these steps, you can reduce the risks associated with third-party relationships and ensure your data remains secure.
7. Implement Zero-Trust Architecture
The "never trust, always verify" principle is a cornerstone of modern network security. This approach requires continuous validation of every user, device, and access point to maintain a secure environment.
The table below outlines the security levels, implementation timelines, and priority rankings for adopting a Zero-Trust framework.
| Security Level | Implementation Timeline | Priority |
| Basic | 1-2 months | High |
| Advanced | 3-4 months | Medium |
| Enterprise | 4-6 months | Strategic |
To stay effective, your security measures should evolve alongside emerging threats. A strong security framework must be adaptable, keeping pace with changes in your business operations and technological advancements. Flexibility and vigilance are key to protecting your organization in an ever-changing threat landscape.
Current Data Leak Statistics and Trends for 2026
The security challenges of 2026 are clear and pressing. Research highlights key insights:
| Category | Impact |
| Average Detection Time | 194 days |
| Small Business Risk | 46% of all leaks impact businesses with fewer than 1,000 employees |
| Cloud Storage Leaks | 82% of data leaks involve data stored in the cloud |
Healthcare organizations are navigating serious security challenges in 2026. Patient records are now worth 300% more on underground markets than credit card details, making them a prime target for cybercriminals.
Remote work adds another layer of risk, with 73% of data leaks linked to distributed workforce settings. Misconfigured cloud storage is another major culprit, accounting for 67% of all data leaks.
These trends highlight the need for stronger protection protocols and a deeper understanding of vulnerabilities. Organizations must prioritize robust cloud security measures and adapt to the evolving threat landscape to safeguard sensitive data effectively.
What Is a Data Leak? Conclusion
Understanding the difference between data leaks and breaches is key to creating targeted strategies that safeguard critical business assets.
Strong data protection starts with your people. Educating employees and implementing rigorous security protocols are the foundation of a solid defense. A seven-step framework focused on proven methods can help businesses protect sensitive information and avoid incidents.
Regular monitoring and strategic updates to protection measures are a must to stay ahead of emerging threats. The time to act is now.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the Top Cybersecurity Companies as well as:
- Top Cybersecurity Marketing Agencies
- Top Cybersecurity Incident Response Companies
- Top AI Cybersecurity Companies
- Top Cybersecurity Companies in Virginia
And don’t miss our Awards section, where we celebrate the most innovative projects in design — from logo and app design to print and packaging.
What Is a Data Leak FAQs
1. What is the difference between a data leak and a data breach?
Data leaks stem from internal mistakes, such as misconfigured cloud settings or accidental file sharing, and are typically unintentional. For example, an employee sending sensitive documents to the wrong email address is a classic data leak scenario.
On the other hand, data breaches involve deliberate and unauthorized access by cybercriminals, targeting systems with the intent to steal or exploit information. Recognizing these distinctions helps shape tailored solutions to address each type of incident effectively and protect your organization’s sensitive data.
2. How can small businesses protect themselves from data leaks?
Small businesses can secure data affordably by encrypting sensitive information, using password managers to store and share strong passwords, automating backups for reliable data recovery, installing endpoint protection to block threats, and establishing clear policies for secure data handling.
3. What are the legal implications of a data leak?
Data protection regulations shape compliance by enforcing privacy laws like GDPR and CCPA, requiring strict data handling with heavy fines for violations. Industry-specific rules, such as HIPAA for healthcare and SOX for finance, add further obligations. Global businesses must navigate varying laws, increasing complexity. Beyond fines, breaches can severely damage reputation and customer trust.






