Key Findings
- Attackers exploited default credentials on Juniper Networks routers, turning IoT devices into cyber weapons, highlighting how factory logins can turn secure devices into cyber weapons.
- Hackers targeted outdated firmware on Dahua surveillance devices and infected nearly 1 million IoT endpoints, demonstrating the importance of ongoing update management.
- The Target data breach showed that poor network segmentation causes major security failures, emphasizing the need for strict vendor controls and proactive security alert responses.
Let’s explore the most critical IoT vulnerabilities organizations should address, examine real-world breaches that highlight risks, and practical approaches businesses can adopt to strengthen security.
1. Insecure Device Authentication and Default Credentials
Weak authentication is one of the easiest ways for attackers to compromise IoT devices. Many come pre-configured with default, easily guessable credentials like "admin" or "12345," leaving them vulnerable to brute-force attacks. Manufacturers often prioritize cost and usability over security, resulting in devices with weak authentication mechanisms.
Alessandro Pellizzari, CEO & CTO of Mostrum Srl, agrees: "IoT devices, by their very nature, present a unique security challenge. Many have limited processing power and memory, making it difficult to implement robust security measures like encryption or complex authentication."
These credentials are intended to be changed upon setup; however, many organizations fail to do so, leaving devices exposed.
The Juniper Networks Mirai Incident
Take the case of Juniper Networks a provider of networking and cybersecurity solutions. In December 2024, the company reported that several of its customers experienced Mirai infections on their Session Smart Router (SSR) devices. The affected systems were found to be using default passwords, which allowed the malware to infect the devices and use them to launch Distributed Denial-of-Service (DDoS) attacks.
While Juniper itself wasn’t directly attacked, the incident raised concerns about how security vendors enforce best practices within their own ecosystems. Customers relying on these routers for secure networking found themselves unintentionally fueling DDoS attacks, which could raise questions about Juniper’s security posture and product oversight.
How the Infection Occurred
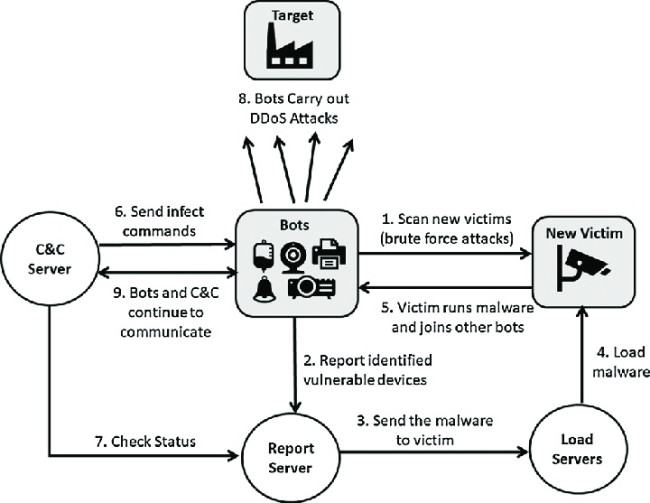
- Scanning for IoT device vulnerability: Mirai continuously scanned the internet for IoT devices with open Telnet ports, which are client-server protocols that run on a reliable connection-oriented transport.
- Attempting default credentials: It attempted to log in using a predefined list of common default usernames and passwords.
- Infecting the device: If successful, Mirai installed malware and added the device to its botnet.
- Launching DDoS attacks: The compromised devices were then used to flood networks with traffic, disrupting services.
Failing to change default credentials is one of the most preventable cybersecurity mistakes businesses can make. It takes little effort to fix, yet countless organizations leave their IoT devices vulnerable, effectively handing cybercriminals the keys to their networks.
Remember: a single compromised device can serve as a gateway for attackers to launch large-scale attacks, steal sensitive data, or disrupt critical operations.
Preventive Measures
To prevent this, organizations must take proactive measures to prevent IoT security vulnerabilities:
- Change default passwords: Immediately update factory-set credentials to strong, unique passwords.
- Implement multi-factor authentication (MFA): Add an extra layer of security to prevent unauthorized access.
2. Unpatched Firmware and Unsupported IoT Devices
Many IoT devices operate on firmware that, if not regularly updated, can harbor vulnerabilities. Manufacturers don't usually provide long-term support, so the devices receive infrequent or worse, no updates at all.
"Firmware vulnerabilities are a constant concern, as updates can be infrequent or difficult to deploy, especially across a large fleet of devices," Pellizzari said.
Devices running outdated firmware are susceptible to known vulnerabilities, which attackers can exploit with minimal effort. A single unpatched flaw can be leveraged across thousands of devices, turning them into entry points for cyberattacks or components of large-scale botnets.
The Malware That Infected a Video Surveillance Company
One high-profile IoT vulnerability example of unpatched firmware exploitation occurred with Dahua Technology, a manufacturer of video surveillance equipment.
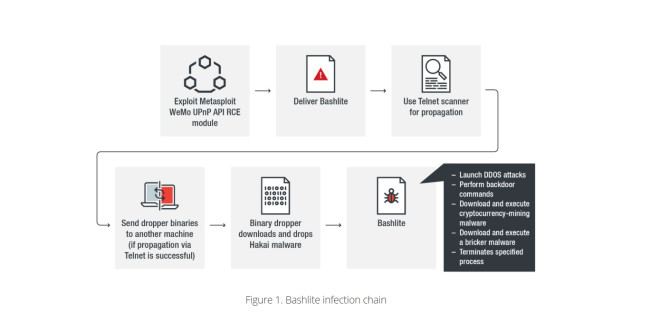
In 2016, researchers discovered that Dahua DVRs and cameras were being hijacked by the BASHLITE malware, infecting nearly one million IoT devices worldwide. The primary cause? Hardcoded passwords and outdated firmware that were never patched.
These compromised devices were weaponized for large-scale DDoS attacks, flooding targets with massive amounts of traffic.
Security experts noted that many Dahua devices shared vulnerable code, meaning attackers could exploit a single flaw across thousands of systems.
How the Infection Occurred
- Scanning for outdated devices: Attackers identified vulnerable Dahua DVRs and cameras running unpatched firmware.
- Exploiting hardcoded credentials: Many devices had built-in usernames and passwords that couldn't be changed.
- Installing the malware: BASHLITE infected the devices, adding them to a botnet.
- Launching DDoS attacks: The compromised devices were used to flood networks with traffic, disrupting services worldwide.
In addition to being exploited for DDoS attacks, researchers uncovered a backdoor in many Dahua cameras and Digital Video Recorders (DVRs). This vulnerability allowed unauthorized remote access, enabling attackers to view live feeds or hijack the devices for other cyberattacks.
Even after Dahua released a firmware update, researchers found the same flaw in a different part of the code, raising concerns about the effectiveness of their security measures.
Preventive Measures
To mitigate risks associated with unpatched firmware and vulnerable IoT devices, organizations should:
- Implement a firmware update policy: Regularly check for and apply firmware updates from manufacturers to ensure devices are protected against known vulnerabilities.
- Assess manufacturer support: Before purchasing IoT devices, evaluate the manufacturer's commitment to security updates and choose products with a proven track record of timely support.
- Replace unsupported devices: Identify and phase out devices that no longer receive security updates to prevent them from becoming entry points for attackers.
3. Insecure APIs and Weak Data Encryption
Application programming interfaces (APIs) serve as the communication bridges between IoT devices and their corresponding servers or cloud services. When these APIs lack robust security measures, they become prime targets for cyberattacks.
Similarly, inadequate encryption practices during data transmission or storage can expose sensitive information to interception and misuse.
Attackers often exploit API misconfigurations, weak authentication, or exposed keys to gain unauthorized access to IoT systems. Once inside, they can exfiltrate data, manipulate device behavior, or use the API as a gateway to deeper network infiltration.
Ripple20 Vulnerabilities in Treck TCP/IP Stack
In 2020, security researchers uncovered a series of 19 vulnerabilities, collectively known as Ripple20, in the Treck TCP/IP stack—a networking software library widely used in IoT devices across various industries.
These vulnerabilities, some of which allowed for remote code execution, stemmed from issues like improper input validation and inadequate handling of length parameters. Attackers exploiting these flaws could remotely execute malicious code, leading to unauthorized control over affected devices.
How the Breach Occurred
- Vulnerable library integration: Manufacturers incorporated the Treck TCP/IP stack into their IoT devices without full visibility into its security flaws.
- Exploitation of vulnerabilities: Attackers identified and exploited the Ripple20 vulnerabilities to gain unauthorized access and control over the devices.
- Potential consequences: Successful exploitation could lead to data theft, device malfunction, or use of the compromised device as a launchpad for further network attacks.
Preventive Measures
To minimize these risks, organizations should:
- Conduct thorough component vetting: Evaluate third-party software components for security vulnerabilities before integration into IoT devices.
- Regularly update and patch devices: Stay informed about vulnerabilities in integrated components and apply patches promptly to mitigate risks.
- Implement robust API security practices: Ensure APIs have strong authentication and encryption mechanisms to protect data integrity and confidentiality.
4. Lack of Network Segmentation for IoT Systems
Many IoT devices — such as security cameras, smart thermostats, and industrial sensors — are often connected to the same network as critical business systems like employee databases, cloud applications, or financial records. This means that if an IoT device is compromised, an attacker could potentially access the entire business network rather than just the infected device.
Unlike traditional IT infrastructure, IoT devices are not designed with strong security controls. Many lack built-in firewalls, encryption, or advanced authentication, making them easy targets for attackers. If these devices are not isolated on a separate network, cybercriminals can use them as entry points to infiltrate sensitive business systems.
Target Data Breach
In 2013, retail giant Target fell victim to one of the most infamous data breaches in US history, compromising the personal and financial information of over 40 million customers. The attack began when hackers gained access through a third-party HVAC vendor, exploiting weak credentials to infiltrate Target’s network.
From there, attackers moved laterally within the system, ultimately installing malware on point-of-sale (POS) systems to steal customer credit card data during transactions. The breach went undetected for weeks, allowing significant damage before being discovered — and even then, Target initially ignored early warnings from its security software.
This incident underscores the critical importance of network segmentation and proactive threat detection. Had Target implemented stricter access controls, monitored vendor activity more closely, and acted immediately on system alerts, the breach could have been mitigated or even prevented.
How the Breach Occurred
- Compromised IoT device: Attackers exploited a vulnerability in the retailer’s internet-connected HVAC system.
- Lateral movement: Since the HVAC system was not isolated, attackers gained access to critical business systems, including the customer database.
- Data exfiltration: Cybercriminals extracted sensitive customer data, leading to a large-scale breach.
While specific financial losses were not disclosed, customer data breaches often result in regulatory fines, reputational damage, and increased costs for security improvements.
This incident highlights how a single compromised IoT device can create a major security risk if not properly isolated from critical systems.
Preventive Measures
Without proper isolation, businesses risk widespread lateral movement, where attackers can use a compromised IoT device as a steppingstone to infiltrate more valuable systems. One of the most effective ways to prevent this is by enforcing network segmentation and adopting a Zero Trust architecture.
"Network segmentation and Zero Trust architectures limit the impact of compromised devices, " Fabricio Defelippe, CEO of TUXDI, emphasized.
To mitigate risks, organizations should also:
- Regular security assessments: Conduct periodic vulnerability assessments of all IoT devices to identify and address potential security gaps.
- Access controls: Establish strict access controls to ensure that IoT devices have limited permissions and cannot interact with sensitive data repositories without authorization.
IoT Vulnerabilities: Conclusion
Securing an IoT ecosystem isn’t just a technical necessity — it’s a business-critical imperative.
Paul Marshall, Co-Founder and CCO of Eseye, warns that unreliable connectivity in IoT can have far-reaching consequences. He paints a vivid picture:
“Imagine IoT health devices losing their connection and the impact that might have on life, or an EV charger failing because of defective connectivity and the millions of dollars in revenue lost as a result — not to mention stranded drivers or the impact on brand reputation.”

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the Top Software Development Companies, as well as:
- Top IoT Development Companies
- Cybersecurity Companies
- Software Consulting Agencies
- AI Development Companies
- Top Software Companies in Nashville
Our design experts also recognize the most innovative design projects across the globe. Visit our Awards section for the best & latest in app designs.
IoT Vulnerabilities: FAQs
1. What are the biggest Internet of Things vulnerabilities businesses should be aware of?
Some of the most critical IoT security vulnerabilities include weak authentication, outdated firmware, insecure APIs, and lack of network segmentation. These flaws allow attackers to exploit IoT device vulnerabilities, gain unauthorized access, and move laterally across business networks.
2. How can businesses prevent IoT device vulnerabilities from being exploited?
Organizations should enforce strong authentication, regularly update firmware, secure APIs, and segment IoT networks to minimize risk. Investing in real-time monitoring and intrusion detection also helps detect threats before they escalate.
3. How do IoT security vulnerabilities impact regulatory compliance?
Many industries must comply with data protection laws like GDPR, HIPAA, and NIST standards. Unsecured IoT devices can lead to non-compliance, resulting in fines, legal consequences, and reputational damage. Businesses handling sensitive data must implement strong IoT security controls to meet compliance requirements.