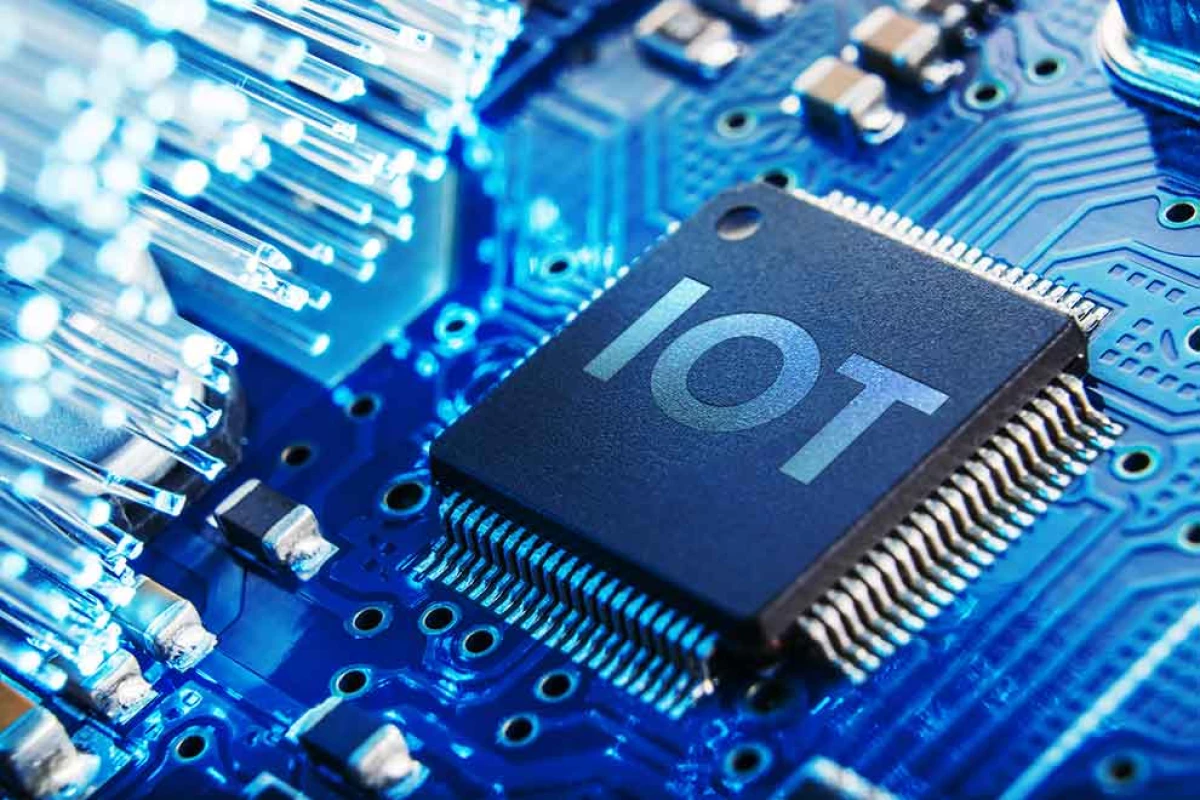
Internet of things (IoT) security issues are vulnerabilities that can be exploited in the interconnected network of devices. These problems can lead to potential data breaches and identity theft. As the IoT market grows, it’s becoming increasingly crucial to ensure robust security to continually protect sensitive information.
Let’s uncover the seven biggest IoT security issues currently jeopardizing these systems everywhere. Our experts also share the best practices to address these challenges.
Top 7 Internet of Things Security Issues
From hijacking of IoT devices and potential home invasions to dangers of rogue devices, these are the seven most serious internet of things security concerns that IoT experts single out.
- Ransomware and Hijacking of IoT Devices
- Insufficient Testing and Lack of Updates
- Home Invasions
- IoT-Driven Financial Crime
- Remote Smart Vehicle Access
- Rogue and Counterfeit IoT Devices
- Lack of User Awareness on Internet of Things Security
1. Ransomware and Hijacking of IoT Devices
Internet of things devices that have weak enterprise cybersecurity measures can become a target of ransomware — malware that encrypts and blocks access to users’ sensitive files. The situation escalates when a hacker responsible for the malware infection demands a ransom for the decryption key, which leaves victims unable to access their files until payment is made.
This type of security threat poses significant risks to smart homes, wearable technology, and healthcare trackers. Think of being locked out of your house or smart vehicle because you have been hacked and haven’t yet settled the ransom.
Ransomware attacks not only prevent users from accessing their IoT devices and related platforms but also completely disable them while stealing personal data. However, the good news is that, since most of IoT information is stored in the cloud, this malware may not have valuable data to lock.

2. Lack of Updates and Testing
One of the security issues with IoT devices is that companies producing them are often careless when it comes to proper testing and providing timely software updates. This is a big problem because consumers tend to trust manufacturers and their judgment, often believing that they have taken all necessary measures to provide safety mechanisms.
However, due to the fast-paced growth of the IoT market, many manufacturers rush to create and release products without thorough testing. Sometimes, the only updates available are for short periods. Given the reality of hyperproduction, manufacturers may abandon these updates entirely to focus on the new generation of devices, urging people to switch to them. As a result, your IoT device with outdated software may be exposed to countless malware, hacker attacks, and other security breaches.
There is another alarming possibility: during an update, there might be downtime when a device sends its information to the cloud. During this period, if your connection is not encrypted, the update files may be unprotected, opening the doors to hackers.
Cybersecurity companies constantly remind organizations to perform regular updates to avoid IoT security issues. This practice helps guarantee the protection of devices against the latest vulnerabilities, which can evolve rapidly today.
3. Home Invasions
The most distressing scenario of IoT security issues is home intrusions or invasions, as they blur the line between the virtual and physical worlds, placing users in genuine, tangible danger.
The Internet of Things devices are becoming integral to a growing number of homes, which gave birth to the concept of “smart homes.” However, this home automation comes with a significant threat: unsafe devices with poor defense mechanisms could broadcast IP addresses. The so-called Shodan searches may make it possible for hackers to locate the address of the device user.
The potential for abuse is evident and could even go as far as the user’s address reaching criminal circles. To prevent this type of IoT security breach, it’s crucial to connect through VPNs and secure your login credentials — a topic we will discuss later in the article.
4. IoT-Driven Financial Crime
With electronic payment companies slowly adopting IoT technology, it’s only reasonable to prepare for a potential rise in financial crime and synthetic identity fraud. Some of these organizations experiment with AI and machine learning, while many of them will soon need to recognize the importance of integrating information on different business levels. This is to ensure the timely detection of fraud patterns and their complex signals using deep learning.
Financial companies will encounter obstacles in introducing these new models due to operational and compliance concerns. To overcome this, they need to enhance their model lifecycle and risk management strategies, especially to address the increasing threat of IoT security breaches.
5. Remote Smart Vehicle Access
Hijacking of smart vehicles is another IoT security problem that’s similar to a home invasion. These scenarios are increasingly inevitable on roads thanks to the implementation of the Internet of Things in cars. Vulnerable IoT devices can pave the way for great risks, such as remote hijacking of your smart car’s access. This can compromise their autonomous capabilities, such as self-driving and the detection of other vehicles.
These breaches pose a significant risk to public safety as they can cause accidents. Additionally, hackers can send out ransomware targeting remote vehicle access and demand payment to unlock compromised vehicles.
Besides IoT device manufacturers working on solving this security breach issue, car manufacturers are also paying attention to it. Microsoft and Ford Motor have developed an infotainment system that has proven vulnerable and open to these attacks. Luckily, the developers had enough time to address these attacks appropriately as they were mostly happening in a time before widespread wireless networks.

6. Rogue and Counterfeit IoT Devices
Rogue and counterfeit IoT devices are a major concern in IoT security today due to their proliferation. These unauthorized units exacerbate the challenge of securing networks and protecting sensitive information.
Without any authorization, users can easily install rogue and counterfeit IoT devices in secured networks. These units either replace the original ones or integrate into the network to collect confidential info and data, breaking the network perimeter. Additionally, devices can turn into rogue access points that steal communication data without the user’s knowledge.
7. Lack of User Awareness on Internet of Things Security
The lack of user awareness in using IoT is also becoming a significant security challenge. Most aren’t as informed about IoT security, which can easily make them vulnerable to sophisticated threats such as social engineering attacks. Additionally, social engineering attacks capitalize on the simple fact that a human factor is the easiest to bypass by targeting humans using the Internet of Things.
A particularly severe example of such abuse was the devastating 2010 attack on a nuclear facility in Iran. The target was an IoT device called a programmable logic controller. It took only one worker plugging a USB flash drive into an internal computer to disrupt the isolation of the internal network from the public one, which made it vulnerable to attack.
IoT Security Solutions
With the above user-related IoT security issues in mind, let’s explore some effective ways to prevent IoT security breaches from happening.
- Change Passwords Often and Make Them Strong
- Don’t Rely on Cloud Technology
- Disable Universal Plug & Play Features
- Use Secondary Network
- Update Your IoT Device Regularly
1. Change Passwords Often and Make Them Strong
Changing passwords regularly on Internet accounts, computers, and mobile phones should become the standard for Internet of Things (IoT) devices.
You should always do your due diligence and make sure that:
- Each IoT device has a unique password
- You change these passwords at least several times a year
- Avoid common and generic passwords
- Make these passwords very complex and tough to crack
Ransomware attacks could not only lock users out of IoT devices and related platforms but also disable devices and steal users’ data. It’s worth mentioning that data vulnerability can often result from unprotected default passwords. To address this, users can apply high-quality password manager tools to manage their secure password system and prevent their data from being stolen.
2. Don’t Rely on Cloud Technology
Cloud technology is very convenient, but it is also a vulnerable emerging technology prone to attacks. IoT manufacturers usually provide cloud storage space with every device you buy. While it is enticing to use something that comes free of charge, consider the following:
- You need an active connection to access data and files stored in the cloud
- This connection can be hacked while you’re accessing your cloud account
Thoroughly review the privacy measures that come with your cloud account. Ensure you secure your date or, even better, store your files and data locally, where they’re beyond the reach of fraudsters.
Learn more about the types of cloud services.
3. Disable Universal Plug & Play Features
The Universal Plug-and-Play (UPnP) feature found in many IoT devices allows multiple devices to connect without needing to configure every device.
While this provides obvious convenience to the Internet of Things ecosystem in your home or workspace, be aware that:
- UPnP protocols use local networks for connecting.
- These networks are quite prone to outside attacks and can be easily accessed.
- If the attack occurs, it might affect multiple IoT devices, allowing attackers to access them remotely
Turning off the Plug & Play feature on IoT devices can provide peace of mind by reducing the risk of unauthorized access. This action prevents suspicious, automatic connections so only trusted devices and networks interact with your systems.
4. Use Secondary Networks
Creating multiple networks, including one with restricted access for themselves and their families, can enhance security by safeguarding sensitive data from unauthorized users.
This approach helps in the following:
- Preventing unauthorized access to private files
- Blocking attempts to hijack IoT units and implant malware
- Completely isolating the IoT device from outside entities
When you isolate IoT devices in this manner, you can significantly reduce the risk of external attacks while maintaining better control over your digital environment. It also helps ensure that any IoT security risks won’t compromise other critical systems on your network.
5. Update Your IoT Device Regularly
As we’ve highlighted the lack of updates as a major IoT security issue, automatic updates must be in place to check for official updates from the device manufacturer. This ensures security patches are installed on your device(s), preventing hackers from using novel ways of intruding on them.
Regular IoT software updates offer several benefits:
- Safety in knowing your systems are updated with the latest security measures to thwart new forms of attacks
- A higher level of security for your home or office
Other IoT Security Best Practices
Here are some more IoT security best practices to help protect your devices and data:
- Limit access
- Use a firewall to protect your network
- Use encryption
- Train employees on IoT security protocols and best practices
- Use a separate network for IoT devices if possible
- Perform regular backups of important data
- Keep software on devices and systems up to date
- Update firmware on IoT devices regularly
- Monitor for suspicious activity on your network
- Disable unnecessary features and services
- Be cautious when connecting to public networks
The Future of Internet of Things Security: How Will IoT Evolve in 2026?
IoT security challenges are the subject of intensive research within the industry. Even the best software engineering schools recognize and study the potential and vulnerabilities these systems possess.
In 2024, $260 billion was spent on IoT technology worldwide. This underscores the need for manufacturers to intensify their cybersecurity efforts to meet corporate expectations. Average users must also play their part by educating themselves on IoT cloud cybersecurity innovations and their importance.
Luka Marić, Project Management Team Director at Infinum with numerous IoT projects under his belt, believes IoT will extend beyond merely connecting devices and instead be about building custom solutions that meet the unique needs of businesses.
"As industries evolve, the focus will shift to security, scalability, and smooth integration. To stay ahead, companies need agile, future-proof IoT solutions that can adapt to new challenges and tech advancements," he states.
Like most technological advances, organized efforts at higher levels are crucial. The U.S. Congress introduced the Internet of Things Cybersecurity Improvement Act of 2020 aimed at ensuring that IoT units they purchase meet minimum safety standards.
Some manufacturers are already offering IoT products with embedded security. Also, wireless communication and information processing are being improved with certain optimization methods such as:
- Convex optimization
- Heuristic methods
- Machine learning
- Artificial neural networks
- Evolutionary algorithms
- Hybrids of AI and other optimization methods
We can also expect a formation of industry-specific fields of IoT security research that may focus on and bring forth development in:
- End-to-end system security models
- Secure cloud computing in IoT
- IoT design and implementation security and privacy issues
- Prediction of attacks on IoT systems and detection of intrusion based on machine learning
- Secure IoT systems architecture
- Privacy of data and techniques of IoT device security
IoT Security Issues Takeaways
IoT security is a complex issue with potential breaches from multiple sources. As this technology is still in its infancy, both manufacturers and users are consistently searching for solutions.
Security challenges can arise from malware attacks, user incompetence, lack of official updates, uneven manufacturing standards, and rogue IoT devices.
To minimize the impact of bad security, users can take measures such as keeping IoT networks separate, avoiding Plug & Play features, not using cloud storage, and keeping unique and complex passwords for IoT devices.


Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the Top Software Development Companies, as well as:
- Top IoT Development Companies
- Cybersecurity Companies
- Software Consulting Agencies
- AI Development Companies
- Top Software Companies in Nashville
Our design experts also recognize the most innovative design projects across the globe. Visit our Awards section for the best & latest in app designs.
IoT Security FAQs
1. What is IoT security?
IoT security refers to the practices and measures put in place to protect the privacy, integrity, and availability of data transmitted by and stored on IoT devices. It involves implementing strong encryption protocols, regular firmware updates, and robust authentication to safeguard against potential cyber threats.
2. What is the importance of IoT security?
IoT security is essential for protecting privacy, preventing cyberattacks, ensuring business continuity and regulatory maintenance, and maintaining brand reputation. Implementing strong IoT security measures is critical to ensure the safe and secure operation of IoT devices and networks.
3. What are examples of attacks on IoT systems and IoT devices?
Some common attacks that target IoT systems and devices are botnet attacks, DDoS attacks, data theft, ransomware attacks, man-in-the-middle attacks, physical attacks, credential stuffing attacks, supply chain attacks, and more.
4. What are the top IoT security threats?
The top IoT security threats are unauthorized access, data breaches, distributed denial of service (DDoS) attacks, and botnet attacks. These Internet of Things security issues can significantly compromise sensitive data and disrupt operations.