Data breaches are everywhere, and protecting user privacy is a critical challenge. IT compliance security should be built into every business, from budding startups to established enterprises. Ensuring IT systems and processes align with regulatory standards can make or break your reputation, operations, and bottom line.
Understanding IT compliance security is vital to ensure your organization is compliant with relevant laws and regulations. Here, we’ll demystify IT compliance security and offer actionable insights to keep your business ahead of the curve.
Unpacking IT Compliance Security
IT compliance security refers to the processes, policies, and technologies a business implements to ensure its IT systems, data, and operations meet regulatory and legal requirements.
It involves aligning your organization’s IT systems, processes, and operational practices with specific standards and frameworks designed to ensure compliance with legal and regulatory requirements, maintain data privacy, and safeguard sensitive information.
Depending on the industry, companies may need to follow different compliance frameworks that dictate how data should be protected, how incidents should be handled, and how security measures are enforced.
Key elements of security compliance in IT typically include:
- Data protection: Safeguarding sensitive information from unauthorized access or breaches
- Risk management: Identifying and mitigating potential vulnerabilities
- Access control: Ensuring only authorized personnel can access critical systems or data
- Incident response: Establishing protocols for detecting, addressing, and recovering from breaches
- Audit trails: Maintaining comprehensive records of all system activities for accountability and review
Why IT Compliance Security Matters
There are compelling reasons to take security compliance seriously. You don’t want to face the legal consequences of non-compliance, but you do want to foster trust, protect against cyber threats, and enable operational efficiency.
Aligning your organization’s IT operations with regulatory standards reduces risks while unlocking valuable opportunities to strengthen your brand, expand into new markets, and build a robust, compliant IT infrastructure.
- Legal requirements and risk reduction: Non-compliance can lead to hefty fines, lawsuits, and even business closures. For instance, GDPR violations can incur penalties up to €20 million or 4% of annual global turnover, whichever is higher. Meeting compliance requirements minimizes legal risks and ensures smooth operations.
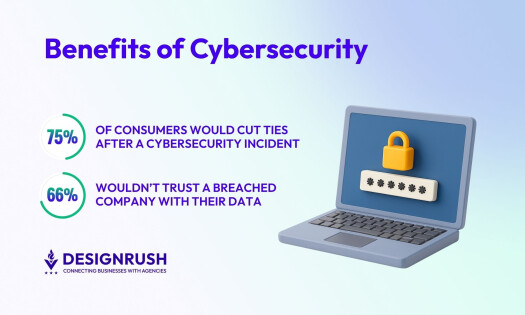
- Building trust and improving reputation: In a competitive marketplace, consumer trust is invaluable. Demonstrating a commitment to cybersecurity compliance reassures customers, partners, and stakeholders that their data is in safe hands, enhancing your brand’s credibility.
- Enabling global market access: IT compliance security is essential for businesses seeking to operate in international markets. Adhering to frameworks like GDPR not only ensures the protection of customer data but also facilitates smoother operations across European jurisdictions. Similarly, compliance with cybersecurity aspects of CCPA helps businesses targeting California's consumer base to avoid penalties and maintain customer trust.
- Preventing breaches: Data breaches can be catastrophic as a result of financial losses, reputational harm, and operational downtime. Compliant security provides the framework to prevent such incidents, offering peace of mind in an unpredictable digital landscape.
- Enhancing operational efficiency: Standardizing compliance processes often leads to streamlined operations. Automated tools, regular assessments, and clear protocols reduce redundancies and improve overall productivity.
Examples of IT Compliance Security Regulations
The rules governing compliance are expanding, particularly in the realm of IT security. These regulations are designed to address emerging threats and protect sensitive information. New cybersecurity regulations reflect a growing global emphasis on standardized approaches to risk management and data protection.
Below are some prominent examples of cybersecurity compliance requirements that businesses need to navigate.
1. NIS2 Directive
Effective from 2024, the EU’s Network and Information Systems Directive 2, or NIS2, directive strengthens cybersecurity requirements for businesses across critical sectors such as healthcare, energy, transportation, and finance. The directive mandates measures like IT risk management, timely incident reporting, and enforcing IT governance standards across the supply chain.
For example, an energy provider failing to report a cyberattack within the specified time could face fines up to 2% of its global turnover or operational suspensions. This highlights the pressing need for organizations to proactively adapt to these regulations.
2. GDPR
Organizations handling the personal data of EU citizens must comply with GDPR, or General Data Protection Regulation. This regulation impacts sectors such as e-commerce, healthcare, and finance, which routinely process large volumes of personal data.
In addition to requiring explicit consent before collecting data and providing users with access to their data, organizations must ensure their IT systems support data portability, transparency, and timely breach reporting.
3. ISO/IEC 27001

The International Organization for Standardization/International Electrotechnical Commission 27001 or ISO/IEC 27001 is a globally recognized standard for managing information security. It provides a systematic approach to managing IT operations and ensuring compliance through an information security management system (ISMS).
The standard outlines best practices for assessing and addressing information security risks, including access control, incident management, and continuous improvement.
Compliance with ISO/IEC 27001 demonstrates a commitment to data protection, reduces the risk of security breaches, and often serves as a competitive differentiator in industries that prioritize information security. Organizations seeking certification must undergo rigorous audits to prove their adherence to the standard.
4. PCI DSS
Businesses processing credit card transactions must adhere to PCI DSS, or Payment Card Industry Data Security Standard. This standard is crucial for the retail, hospitality, and e-commerce sectors, which manage vast amounts of payment-related data.
Key requirements include encrypting cardholder data, maintaining secure networks, implementing access controls, and regularly testing security systems. Adhering to this standard ensures the safe handling of payment information and reduces the risk of fraud.
5. The European Cyber Resilience Act
The European Cyber Resilience Act (CRA) strengthens cybersecurity for a wide range of digital products, including everyday devices like baby monitors and smartwatches. Industries such as consumer electronics, automotive, and manufacturing are significantly impacted.
The act mandates robust cybersecurity protocols throughout the product lifecycle, from design to maintenance, and establishes unified rules for bringing digital products to market. For example, a manufacturer of smart home devices could face market bans or recalls if vulnerabilities leading to data breaches are discovered and not promptly addressed.
IT Compliance Security Challenges and Best Practices
Several challenges arise when trying to meet the ever-evolving regulatory requirements, particularly in managing complex IT systems and adapting to new compliance mandates. Some of the most common challenges include:
- Keeping pace: One of the main difficulties is keeping up with the sheer volume of regulations, especially when operating across multiple jurisdictions with differing standards. Companies must also constantly adapt their security protocols to address new threats and vulnerabilities.
- Resource limitations: Many businesses struggle with resource limitations, as they may not have the specialized expertise or manpower required to maintain rigorous compliance standards.
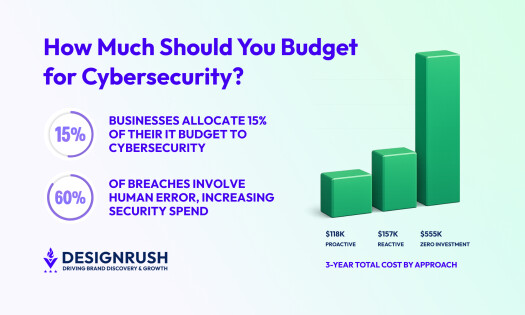
- Employee training: Ensuring that all employees understand and follow the necessary security protocols also presents a challenge, as human error remains one of the leading causes of data breaches and security failures.
To address these challenges, you can implement several best practices to streamline your compliance efforts and enhance the overall security posture, namely:
- Make the most of technology
- Conduct regular risk assessments
- Foster a compliance-first culture
- Create a continuous improvement plan
- Partner with experts
1. Make the Most of Technology
Leveraging technology is a key strategy in overcoming compliance challenges. Tools such as automated compliance management systems, encryption software, and intrusion detection systems simplify the management of compliance by automating routine tasks and offering real-time monitoring.
AI and automation software, broadly speaking, are key to managing risk and compliance in an increasingly complex environment. They can help track regulatory changes and ensure that compliance measures are always up to date.
However, “AI can turn a blind spot into a wildfire if biased data or faulty logic slips through unnoticed,” cautions Emre Alemdar, CEO of Buinsoft.
Luke Irwin, Principal Consultant at Aegis Cybersecurity, emphasizes, “You need to know and understand how to read, interpret, and correct for the outcome needed.”
2. Conduct Regular Risk Assessments
Conducting regular risk assessments will help you maintain compliance in a constantly changing threat landscape. Frequent evaluations help identify vulnerabilities in systems, processes, and personnel. By continuously assessing potential risks, your business can adjust its cybersecurity strategies accordingly.
Risk assessments allow organizations to prioritize security resources where they are most needed and ensure that compliance efforts address both current and emerging threats.
3. Foster a Compliance-First Culture
Creating a compliance-first culture within your organization will ensure that all employees understand the importance of IT security and compliance. That means using regular training sessions, workshops, and clear communication about security policies to reduce human errors (often a major contributor to security breaches).
Taking a proactive approach by educating and empowering employees builds a collective commitment to the organization’s security objectives. When every team member understands their role in maintaining compliance, the organization as a whole is better equipped to handle challenges.
“In my experience, the most effective way to train employees to follow guidelines is by organizing regular training sessions and incorporating one-on-one interactions,” says Ketan Sodvadiya, Project Manager at Differenz System.
“Involving leadership during these sessions also plays a key role, as it allows them to learn alongside employees and reinforce compliance with a stronger, more practical approach,” Sodvadiya concludes.
4. Create a Continuous Improvement Plan
Don’t view compliance as a one-time effort — it’s a continuous process. Regulations, threats, and technologies are always changing, and organizations must adapt accordingly. Regularly updating policies, procedures, and security technologies is essential to keep your business aligned with new regulatory standards and industry best practices.
A well-structured continuous improvement plan will help you stay agile and responsive to changes while ensuring ongoing compliance and security resilience.
5. Partner with Experts
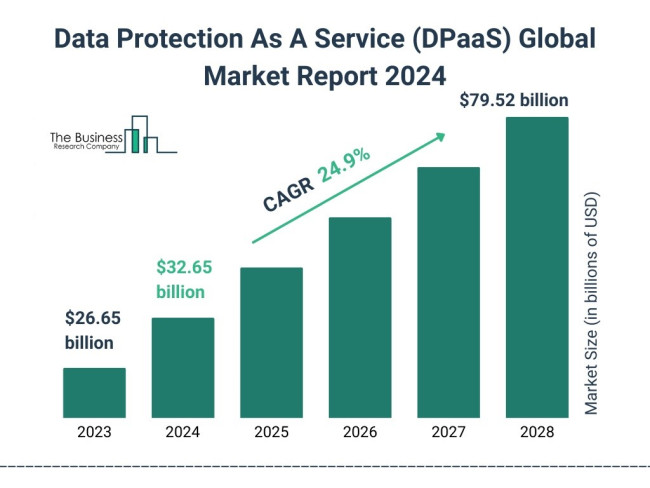
Collaborate with legal, cybersecurity, and IT professionals to navigate complex regulations and implement robust security frameworks. Many organizations also benefit from Data Protection as a Service (DPaaS) providers, which offer expert solutions tailored to manage and safeguard sensitive information efficiently.
These services combine advanced technology and industry expertise to streamline compliance and enhance overall data protection.
IT Compliance Security in Brief
IT compliance security is essential for protecting sensitive data, avoiding legal penalties, and fostering trust. From understanding key regulations to adopting best practices such as risk assessments and IT governance tools, businesses must prioritize compliance and operational alignment.
By integrating IT compliance security into your operations, you safeguard your business against breaches, enhance operational efficiency, and build a strong foundation for global market access.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the Top Cybersecurity Companies as well as:
- Top AI Cybersecurity Companies
- Top Cybersecurity Marketing Agencies
- Top Cybersecurity Incident Response Companies
- Top Cybersecurity Companies in Virginia
- Top IT Compliance Solution Companies
And don’t miss our Awards section, where we celebrate the most innovative projects in design — from logo and app design to print and packaging.
IT Compliance Security FAQs
1. What is the difference between cybersecurity and IT compliance security?
Cybersecurity involves implementing measures to protect systems, networks, and data from cyber threats such as hacking or malware. IT compliance security, on the other hand, ensures that these measures meet specific legal, regulatory, and industry standards, such as GDPR or PCI DSS, to ensure accountability and avoid penalties.
2. What are the first steps a business should take to achieve IT security compliance?
Start by identifying the regulations applicable to your industry and location (e.g., GDPR, PCI DSS). Conduct a thorough risk assessment to pinpoint vulnerabilities and then begin implementing necessary security measures. After that you can establish policies to monitor and maintain compliance.