Do you need a reputable security assessment company to identify security threats and protect your business? We have carefully assessed case studies, portfolios, and client testimonials of leading risk assessment services providers to create our list and help businesses like yours find a suitable partner. Explore our directory today and filter it according to location, hourly rates, minimum budgets, and other key criteria for a more personalized search.
Security Assessment Company Hiring Guide
What is a security assessment company?
A security assessment company is a specialized firm that evaluates an organization's security posture by identifying vulnerabilities, assessing risks, and recommending measures to protect systems, networks, and data from potential threats. These companies perform tasks such as penetration testing, vulnerability scanning, compliance audits, and risk analysis to make sure that businesses are protected against cyberattacks, data breaches, and other security issues. They aim to help organizations strengthen their defenses, meet regulatory requirements, and prevent security incidents.
Security assessment programs can typically be broken down into three stages:
- Preparation stage
Preparing the company’s security system or network for testing and evaluation. This includes identifying the organization’s important information and data, creating, gathering, and updating documentation, and creating user accounts for testers to access different tools and systems as needed. - Assessment stage
Conducting physical and penetration tests of servers, databases, networks, and other infrastructure, including their backups. IT risk assessment companies can also craft scenarios that might expose the company to attacks, such as theft or unauthorized access. - Evaluation stage
After reviewing all the information gathered during the assessment phase, security risk assessment companies will determine whether there are gaps in the security that an attacker can exploit. They will also recommend measures to prevent attacks or mitigate their impact on the business.
The insights and services provided by IT security assessment companies can help businesses address specific challenges and pain points, such as:
- Outdated software or those with unpatched vulnerabilities that attackers can exploit
- Weak or incorrect network configurations and inadequate firewall rules that can expose systems to threats
- Hardware failures and other physical vulnerabilities that can compromise data integrity
- Phishing attacks, identity theft, and other social engineering tactics that trick employees into providing sensitive information or unauthorized access
- Insufficient security policies, procedures, governance structures, and incident response plans
- Lack of security training for in-house employees
- Lack of compliance with industry-specific regulations such as GDPR and HIPAA that lead to hefty fines and vulnerabilities.
According to industry reports, a cyberattack occurs every 39 seconds, and nearly 61% of small to medium businesses report successful attacks on their infrastructure. On average, organizations experience five successful incidents, such as data breaches, malware, or ransomware, which result in significant downtime and loss of customer trust.
Success story
As the threats of cyberattacks continue to increase, security assessment companies like CyberSecOp can help businesses prepare for the worst, as shown by this case study:
- Challenge: A financial services institution suspected potential threat actors within their network. However, with over 2,000 networked windows scattered across different offices, the company needed a professional to hunt down these threats and install a security solution into its infrastructure without disrupting its operations.
- Solution: CyberSecOp implemented an evidence collection that scanned the network without affecting the client’s servers or services. After several scanning rounds, it identified the breach in the network, isolated the malicious content, and coordinated with the client’s internal IT team to conduct remedial actions to purge the system of any lingering threats or backdoors that could be exploited in the future.
- Results: The suspected threat actor’s access and malicious software were successfully removed from the client’s devices, and any vulnerabilities were patched up. All client services and endpoints are scanned periodically to ensure no other threat actors can breach the network.
What do security assessment companies do?
Security assessment companies perform various services to identify and mitigate security threats and vulnerabilities.
The services they commonly provide include:
- Vulnerability scanning
Identifying weak points within an application, networks, or systems that could be compromised and exploited by a third party. - Risk analysis
Evaluating the client’s security infrastructure to determine potential risks, their impact on the organization, and how likely they are to occur. - Penetration testing
Testing the effectiveness of IT security measures and detecting potential weaknesses through simulated attack scenarios. - Compliance audits
Verifying whether the client complies with regulations and standards set by the government, industry governing bodies, or the client’s internal policies. - Security consulting
Providing expert advice and guidance on security policies, procedures, and best practices that clients can use to better protect their data and systems. - Incident response planning
Developing plans and procedures to detect, respond to, and recover from various security incidents. - Security awareness training
Educating employees on recognizing and avoiding common threats and protecting the organization’s assets and data.
Success story
The following case study highlights the multiple services a security assessment company can provide to a business:
- Challenge: A healthcare company had just released a mobile app and wanted to determine if the patient data stored in its database was exposed to vulnerabilities. It also needed to assess whether it complies with the Health Insurance Portability and Accountability Act (HIPAA) and other healthcare industry regulations.
- Solution: Qualysec conducted a comprehensive penetration testing program using various proven methodologies, including PTES, OWSAP, and SANS 25. It worked closely with internal developers to mitigate vulnerabilities identified and apply best practices to ensure regulatory compliance.
- Results: Qualysec identified a range of vulnerabilities that the client could address effectively. It also achieved compliance with industry requirements.
What is the difference between a security audit and a security assessment?
The difference between a security audit and a security assessment lies in their purpose, scope, methodology, and expected outcomes. Security audits focus on compliance with security policies and controls, while security assessments look for vulnerabilities and potential risks. Audits also cover an organization's entire infrastructure to check for industry compliance with industry standards, while assessments delve into specific systems or networks.
Here are some main differences between a security audit and a security assessment:
| Security Audit | Security Assessment | |
| Purpose | Verifies compliance with industry and internal security policies and the presence of control mechanisms such as firewalls and intrusion detection devices | Identifies vulnerabilities and other potential risks within an organization’s security posture |
| Scope | Covers all aspects of an organization’s internal infrastructure | Focuses on specific IT systems, networks, or applications |
| Methodology | Examines security controls, protocols, and documentation to ensure they meet specific criteria | Conducts vulnerability scanning, penetration testing, and risk analysis to identify weaknesses and threats |
| Outcome | A report detailing whether the organization has successfully achieved compliance and recommendations for improvement | A report listing identified vulnerabilities, their potential impact, and recommendations on how to resolve them. |
How long does a security assessment take?
A security assessment takes between 2 and 8 weeks, depending on the size of the company and the scope and level of detail required.
Here is a breakdown of the typical timeline for IT security assessment services:
- Small businesses: 2-3 weeks
- Medium businesses: 3-4 weeks
- Large businesses: 4-5 weeks
- Enterprises: 6-8 weeks
The timeline of security assessments can also be affected by the following factors:
- The complexity of the systems and networks that are being evaluated
- The depth and thoroughness of testing and assessment procedures required
- The techniques and tools to be used in the assessment
How often should a business conduct security assessment?
Businesses should conduct security assessments at least once a year or as often as every three months, depending on the organization's risk level.
The following criteria can determine the frequency of security assessments:
- The amount of sensitive data stored
- The regulations and standards covering the organization
- Recent changes to systems, networks, or applications
- Previous assessments have identified significant vulnerabilities
Based on that information, the general guidelines that businesses should follow are:
- High-risk level: Quarterly assessment
- Medium risk level: Quarterly or semi-annually
- Low-risk level: Annually
How much do risk assessment services cost?
Risk assessment services cost between $3,000 and $150,000 or higher, depending on the company's size, the services to be rendered, and the number of tests to be conducted.
Here’s a general breakdown of the costs of hiring a security assessment company:
- Small businesses: $3,000-$10,000 per assessment
- Mid-sized businesses: $10,000-$50,000 per assessment
- Large to enterprise-level businesses: $50,000-$150,000 per assessment
Security risk assessment companies can also charge separate fees for specific services, such as:
- Vulnerability scanning: $200-$400 per month
- Penetration testing: $5,000-$35,000
- Security audit: $3,000-$30,000
- Legal discovery & compliance: $3,000-$12,000
- Remediation and security awareness training: $500-$5,000
- Security posture management: $2,000-$10,000 per year
Other factors that can influence the total cost of risk assessment services include:
- The complexity of the client’s operations, systems, and networks to be assessed
- The types and number of industry regulations to be checked for compliance
- The size, experience, and reputation of the assessment agency
- Ongoing remediation, monitoring, and reporting services provided after the initial assessment
Why should I hire a security assessment company?
You should hire a security assessment company because it can effectively protect your organization’s assets, minimize the risk of security breaches, and ensure your company’s operations and reputation despite these threats.
Some of the key benefits IT security assessment services provide include:
- Identify and take preventive measures against various types of vulnerabilities and security threats
- Allocate resources effectively in the event of a security incident and mitigate its impact on the business
- Make improved decision-making processes on security policies, procedures, and investments in security solutions and infrastructure
- Minimize financial losses and customer trust caused by security breaches
- Improve the company’s resilience and ensure its continued operation despite security threats
Success story
Our research team recommends the following case study that highlights how IT security assessment services provided by ELEKS, a Chicago-based specialist, can benefit even a major cybersecurity provider.
- Challenge: ESET, one of the world’s leaders in cybersecurity solutions, lacked the manpower to assess the information security risks in its essential business systems and services. It also required additional resources to establish an efficient testing process for its core product line.
- Solution: ELEKS set up a security team that conducted risk assessments for ESET’s systems and applications and provided recommendations on addressing potential threats. It also assigned a team of over 30 engineers to test multiple product configurations across different platforms.
- Results: By allocating testing to ELEKS, ESET could streamline its resources and speed up the time to market for its products without compromising quality. The client also identified weaknesses in its infrastructure and implemented the necessary controls.
How do I choose the best security assessment company for my business?
To choose the best security assessment company for your business, we recommend the following steps:
- Define your needs and goals
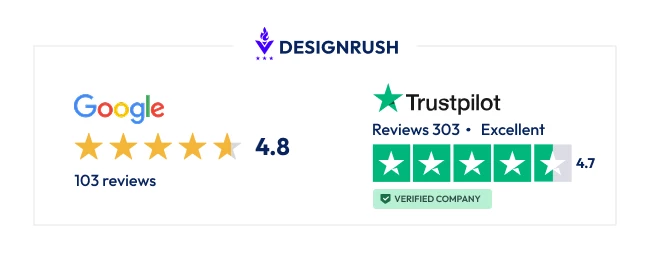
Determine the specific security risks you want to address or the regulations and standards you must comply with. You should also define the scope of the assessment, including the areas of your organization to be evaluated. - Research and shortlist companies
Agency directories like DesignRush are a great place to start, as we provide ratings and detailed information on security assessment companies. You can also ask colleagues or your local chamber of commerce for agencies they might recommend. - Services and qualifications
Check if your prospects offer the services you require, such as vulnerability or risk assessments, penetration testing, and compliance audits. Take note of certifications such as Certified Information Systems Security Professional (CISSP) and Certified Ethical Hacker (CEH) that attest to their expertise in the field. - Send out RFPs
Your request for proposal (RFP) should indicate the project’s goals and requirements, including its scope and expected timeline, the assessment services needed, and the budget. If the agency will be given access to sensitive information, include a non-disclosure agreement (NDA). - Evaluate proposals
Based on the information you get, assess their approach to conducting the assessment, including the methodologies, tools, and techniques they will use. Compare pricing packages and ask for a breakdown of the estimated cost for all services. - Experience and expertise
Ask prospects if they can provide you with case studies of projects they’ve done in the past. Ideally, the agency should have significant experience in doing assessments in your industry and with businesses similar to yours. - References and testimonials
Request for references from previous clients who can vouch for their work. You can also check for reviews on Google My Business or online directories like DesignRush, which provide more detailed reviews. - Communication and collaboration
The agency should be able to communicate clearly before and during the interview. Take note of their willingness to collaborate with your IT team to conduct assessments and implement remediation measures. - Negotiate terms
Review the terms and conditions of the contract, such as the scope of work, the expected timelines and deliverables, pricing, and confidentiality. - Choose a partner
Decide on a security assessment company that aligns best with your project.
Need help locating the right security assessment company? Check out the DesignRush Marketplace, and provide us with the core details about your project. We’ll send you a shortlist of suitable prospects free of charge.
How do I find the best security assessment services on DesignRush that fit my budget?
To find the best security assessment services on DesignRush that fit your budget, we recommend narrowing your search by budget. Use the directory filters to list security risk assessment companies according to minimum budget and sort by highest to lowest according to your needs.
For example, among the top-rated agencies that accept budgets is A1qa. For bigger projects with budgets of $25,000 or higher, agencies like ELEKS and Vention are highly recommended
You can also use the same filter tools to sort agencies according to hourly rates, location, areas of specialization, and other key criteria to help make your search even more accurate.
What are the key success metrics in security assessment services?
The key success metrics in security assessment vary greatly in scope, but the most common ones include:
- Mean Time to Detect (MMTD)
Measures the average duration a security team identifies an incident or security breach. A low MTTD typically indicates the security team’s effectiveness in identifying and addressing incidents and minimizing their impact. This metric can also be used to assess the performance of detection and monitoring tools. - Mean Time to Resolution (MTTR)
Gauges the speed and efficiency in responding to security incidents. It enables organizations to pinpoint areas of improvement within their incident response plan and procedures. - Mean Time to Attend and Analyze (MTTAA)
The average duration taken by security teams to respond to and analyze an incident. It enables the organization to evaluate and improve its incident response protocols. - Number of Security Incidents
Counts the number of security incidents identified and reported within a certain period. It provides businesses insight into patterns or trends in security incidents. It also makes identifying common types of incidents easier and enables the organization to prioritize mitigation efforts more effectively. - False Positive Rate
The proportion of incidents that were erroneously categorized as security threats. It is used to assess the accuracy of the client’s threat detection systems and helps prevent expenditures incurred from investigating harmless events. - False Negative Rates
The proportion of security threats is mistakenly classified as non-viable threats. A heightened rate indicates that the client’s security mechanisms are inefficient at identifying authentic security threats. - Cost Per Incident
Quantifies the direct and indirect expenses in addressing incidents, including time, legal fees, and regulatory fines. It might also include expenses incurred from software upgrades and preventative measures against future incidents. - Incident Escalation Rate
The proportion of incidents that result in escalations to higher-level team members or external specialists. A high escalation rate might indicate a lack of expertise within the assessment team or a misaligned allocation of resources needed to handle incidents. - Incident Closure Rate
The proportion of resolved security incidents compared to the total reported incidents within a set time frame. A high closure rate indicates the effectiveness in detecting, responding to, and resolving the threat. - Incident Containment Rate
Evaluate the effectiveness of containing incidents after they’ve been identified. This metric is crucial in reducing the extent of cyberattacks and their impact on the client.
What questions should I ask risk assessment companies before hiring one?
The questions you should ask risk assessment companies before hiring one include the following:
Its Relevant Background
- How long has your agency provided security assessment services?
- Do you have experience assessing risk in our industry or with similar businesses?
- Do you have certifications to conduct risk assessments in our industry?
- Can you provide relevant case studies or references from your past clients?
- What are the pricing models that you offer?
- What are the general terms and conditions of your service agreement?
Its Services and Processes
- What are the risk assessment services do you offer?
- What risk assessment frameworks do you use?
- How do you collect and analyze data for assessments?
- How will the confidentiality of our sensitive information be ensured?
- Do you offer assistance in implementing recommended security measures?
- Can you customize your services to fit our needs and processes?
- How is the cost of an assessment calculated?
Relevant To Your Project
- What’s your estimated timeline for completing the assessment?
- How will you ensure the project is completed on time and within budget?
- What deliverables will be provided for the duration of the project?
- Are there additional costs to consider, including training, software licenses, or ongoing support?
- How will your team communicate with us during the assessment process?
- How often will progress updates and reports be provided?
- Can you also provide ongoing support after the initial assessment?
What are the best security assessment companies in the US?
The best security assessment companies in the US listed in DesignRush are the following:
- ELEKS
- 4.9 stars on DesignRush (27 reviews)
- 4.7 stars on Google (561 reviews)
- Top clients: ESET, TAIT, GRTgaz, DPD, Aramex
- Vention
- 4.7 stars on DesignRush (12 reviews)
- 5.0 stars on DesignRush (35 reviews)
- Top clients: Cuvva, Costa Coffee, Paypal, Glassdoor
- A1qa
- 4.8 stars on DesignRush (7 reviews)
- 4.6 stars on DesignRush (12 reviews)
- Top clients: Adidas, SAP, Acronis, Colliers International
- Buchanan Technologies
- 5.0 stars on Google (12 reviews)
- Top clients: Amazon, Atmos Energy, Citibank, Berkshire Hathaway Automotive
- RedZone Technologies
- 4.0 stars on Google (6 reviews)
- Top clients: Federal Credit Union, Advanced Medical Management Inc., Baltimore Ravens
About The Author and Expert Reviewer
Sergio is a technology leader with over six years of experience managing global teams and delivering projects across fintech, sportstech, and B2B platforms. At DesignRush, he drove product growth and development execution, building tools that speed up processes by 95% and cut costs by 35% while maintaining full uptime.