Key Findings:
- Implementing a structured approach to identify and mitigate cyber threats is essential for protecting digital assets and business continuity.
- Cybersecurity incidents can lead to massive financial losses and damage to a company's reputation, which means proactive risk management is key.
- Utilizing established frameworks like NIST CSF and ISO/IEC 27001 can help organizations manage cybersecurity risks systematically.
We’ll guide you through a comprehensive, step-by-step overview of effective cybersecurity risk management. Learn how to develop robust strategies to protect your organization’s assets, from identifying potential threats to leveraging advanced monitoring tools.
How Cybersecurity Risk Management Works: Step-by-Step Process
To give critical business assets the necessary level of protection and ensure business continuity, a well-structured cybersecurity risk management strategy is essential. Effective cybersecurity risk management is primarily about four key components:
1. Risk Identification
Before you go swinging swords, you need to know what you’re fighting. The first step is figuring out what needs protecting — and where the vulnerabilities are.
Inventorying Your Assets
Begin by cataloging all essential components of your IT infrastructure. This inventory should encompass:
- Hardware: Devices such as computers, servers, and that dusty router from 2012.
- Software: Applications, operating systems vital to daily operations, and anything with a login.
- Data: Sensitive information, including customer details and financial records.
- Networks: All those invisible highways your data travels on.
Asset management tools like Axonius Cybersecurity Asset Management or Qualys CyberSecurity Asset Management (CSAM) 3.0 can help make sure nothing gets left off the list.
Identifying Potential Threats
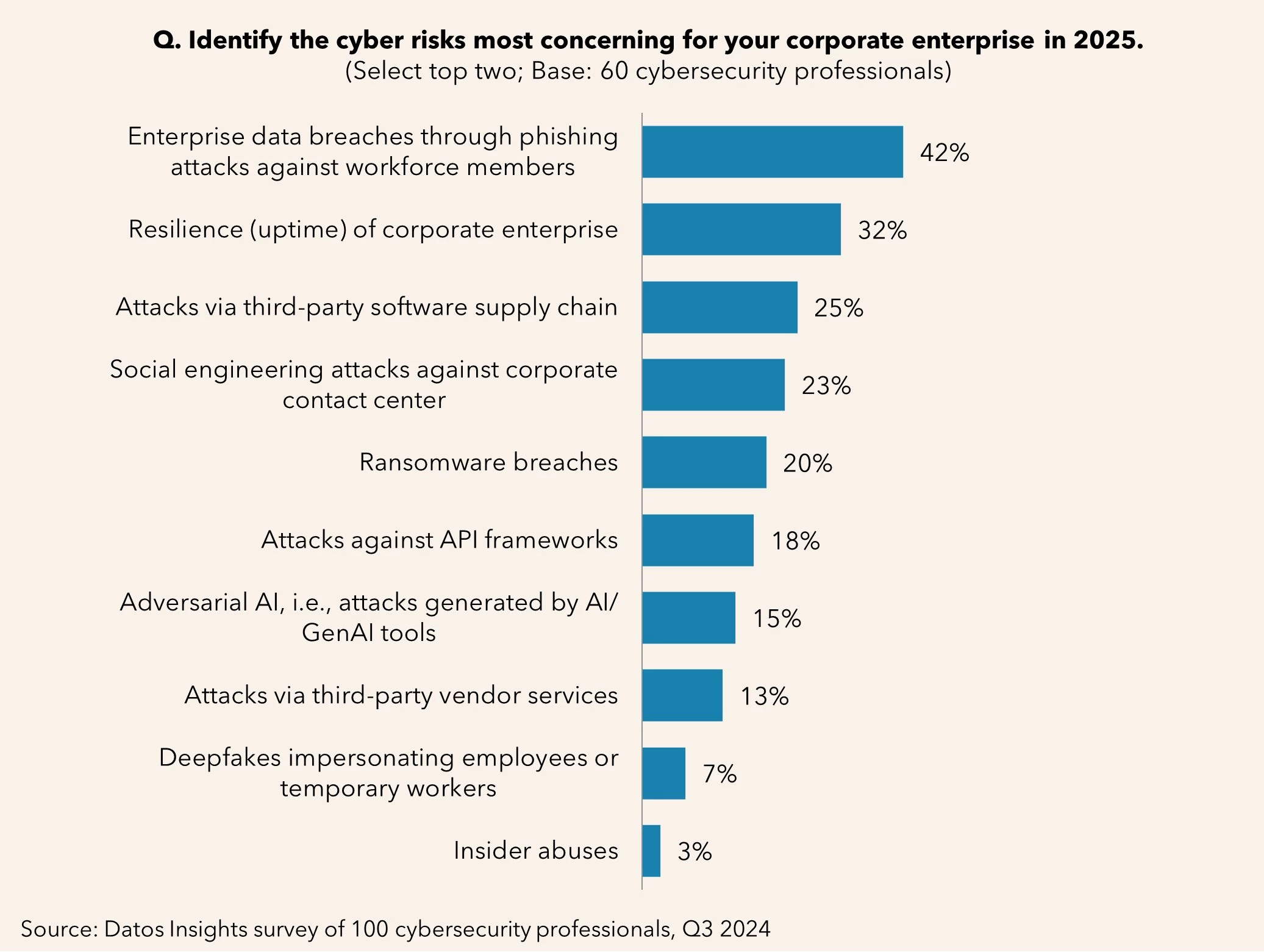
You can’t counter cyberthreats if you don’t understand the threat landscape. You need to be able to recognize threats like:
- Malware attacks: Malicious software designed to damage or disrupt systems.
- Phishing schemes: Deceptive attempts to acquire sensitive information by masquerading as trustworthy entities. In other words, that “urgent” email from your “CEO” asking for gift cards.
- Insider threats: Risks posed by employees or associates who have access to sensitive information (whether intentional or accidental). Donna from Accounting might not mean harm, but clicking that link? Yikes.
- Third-party vulnerabilities: Security gaps introduced through external vendors or partners with access to your systems. That vendor you trust? Hackers might trust them too.
Using Risk Identification Tools
There are many specialized tools designed to help you do this. These include:
- Automated tools, like Nessus, that assess systems for known security weaknesses.
- Tools like Metasploit simulate cyberattacks to test your defenses.
- Threat intelligence feeds, like Recorded Future, keep you one step ahead of the cybercriminal grapevine.
These will help to keep you informed about emerging threats pertinent to your industry, making timely and informed responses possible.
2. Risk Assessment
So, you’ve identified threats. Now what? It’s time to assess which ones could actually burn your house down.
Determine Likelihood and Impact
Ask yourself:
- How robust are the current defenses?
- Have similar incidents occurred in the past?
- Is the threat emerging or well-known?
Understanding the likelihood of an event will help you focus on risks that are more probable and need immediate attention. Outdated systems? You’re a prime target. Legacy software is basically a welcome mat for malware.
Assess the Consequences
What happens if a risk becomes reality?
- Operational disruptions: Cyberattacks, such as ransomware, can halt important business operations, leading to significant downtime and productivity losses.
- Financial losses: Cybercrime could cost businesses globally roughly $1.2 trillion annually by the end of 2025, factoring remediation, legal fees, and potential regulatory fines.
- Reputational damage: What price can you put on your brand’s reputation? Data breaches erode customer trust as they lose confidence in the affected organization, potentially leading to customer attrition and diminished brand value.
Apply Assessment Methodologies
It's essential to employ structured methodologies to systematically evaluate the potential impact and likelihood of identified risks. You can go with:
- Qualitative assessments: Assign simple ratings (low, medium, high) to risks.
- Quantitative analyses: Estimate potential financial losses in monetary terms.
- Hybrid models: Combine both approaches for a balanced perspective.
If this sounds like too much, you’re not alone. Templates and expert consultants exist for a reason.
3. Risk Mitigation
Now it’s time to act. Once you’ve prioritized the risks, the next step is to implement strategies that effectively reduce their likelihood or impact. Here’s how you can do that.
Develop a Comprehensive Mitigation Plan
Begin by formulating a detailed plan that addresses each identified risk with tailored strategies. This plan should encompass both technological solutions and organizational policies to create a robust defense. Combine tech tools with solid policies. It’s not just about firewalls — it’s about foresight.
Implementing Technical Safeguards
Consider the following technical measures to fortify your organization's defenses:
- Firewalls: You need barriers between trusted internal networks and untrusted external networks. Firewalls control incoming and outgoing traffic based on predetermined security rules.
- Antivirus and anti-malware software: Employ these tools to detect and remove malicious software and prevent infections that can compromise system integrity.
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): These tools monitor network traffic for suspicious activity, alert administrators to potential threats, and actively block identified malicious actions.
- Network segmentation: Divide your network into distinct zones to limit unauthorized access and contain potential breaches.
- Data encryption: Ivan Dabic, CEO and Co-Founder of BlueGrid, emphasizes the importance of using strong encryption protocols, noting that they "protect your data from prying eyes, ensuring confidentiality and integrity." He warns, however, that not all tools offer complete protection: “Some tools don’t guarantee 100% end-to-end encryption, so make sure to check with your vendor their tools as well as their standard of operations,” he adds.
- Multi-factor authentication (MFA): Require multiple forms of verification before granting access to critical systems.
- Regular software updates: Keep all systems and applications up to date to patch vulnerabilities and defend against emerging threats.
Create a Risk Response Plan
Mitigation isn’t foolproof. If a breach happens, you need an Incident Response Plan (IRP) that includes:
- Preparation: Establish and train an Incident Response Team (IRT) with clearly defined roles and responsibilities. All members should be equipped with the necessary tools and knowledge to handle a potential incident effectively.
- Detection and analysis: Develop protocols to assess the nature and severity of incidents to facilitate informed and swift decision-making.
- Containment, eradication, and recovery: Develop strategies to isolate affected systems to prevent further damage, remove the root cause of the incident, and restore systems to normal operations.
- Post-incident activity: Conduct thorough reviews after incidents to identify lessons learned and areas for improvement. Update the IRP accordingly to improve future responses and bolster your overall security posture.
4. Continuous Monitoring and Improvement
In cybersecurity, standing still means falling behind. Because threats are constantly evolving, your defense strategy must too. Continuous monitoring and regular updates aren’t just best practices, they’re necessities.
- Use real-time tools like security information and event management (SIEM) systems o sniff out shady activity.
- Review and update regularly, what worked last year might not fly today.
- Compliance requirements and technology never stop changing and your cybersecurity posture should be flexible enough to adapt to new regulations and smart enough to evolve in tune with threats.
Key Cybersecurity Risk Management Frameworks and Standards
Frameworks are your roadmap in this chaotic world of cyber threats. Stick with the proven ones.
Adopting established frameworks like these widely recognized examples to ensure your business complies with industry standards and realizes the benefits of a robust cybersecurity posture.
- NIST Cybersecurity Framework (CSF): Developed by the National Institute of Standards and Technology, this framework offers a comprehensive approach to managing cybersecurity risks through five core functions: identify, protect, detect, respond, and recover.
- ISO/IEC 27001: This international standard outlines requirements for establishing, implementing, and maintaining an information security management system (ISMS). A company with Achieving ISO 27001 certification demonstrates a commitment to security.
- CIS controls: The Center for Internet Security (CIS) controls outline specific actions to defend against common cyber threats. These controls are categorized into basic, foundational, and organizational levels, making them accessible to businesses of all sizes.
Why Cybersecurity Risk Management Actually Matters
Cyber threats can have a devastating impact a company's finances, operations, and reputation. And the damage is usually compounded over an extended period of time, since the fallout from a single breach can spread to multiple domains. Here’s the drama you’d like to avoid:
1. Financial Impact
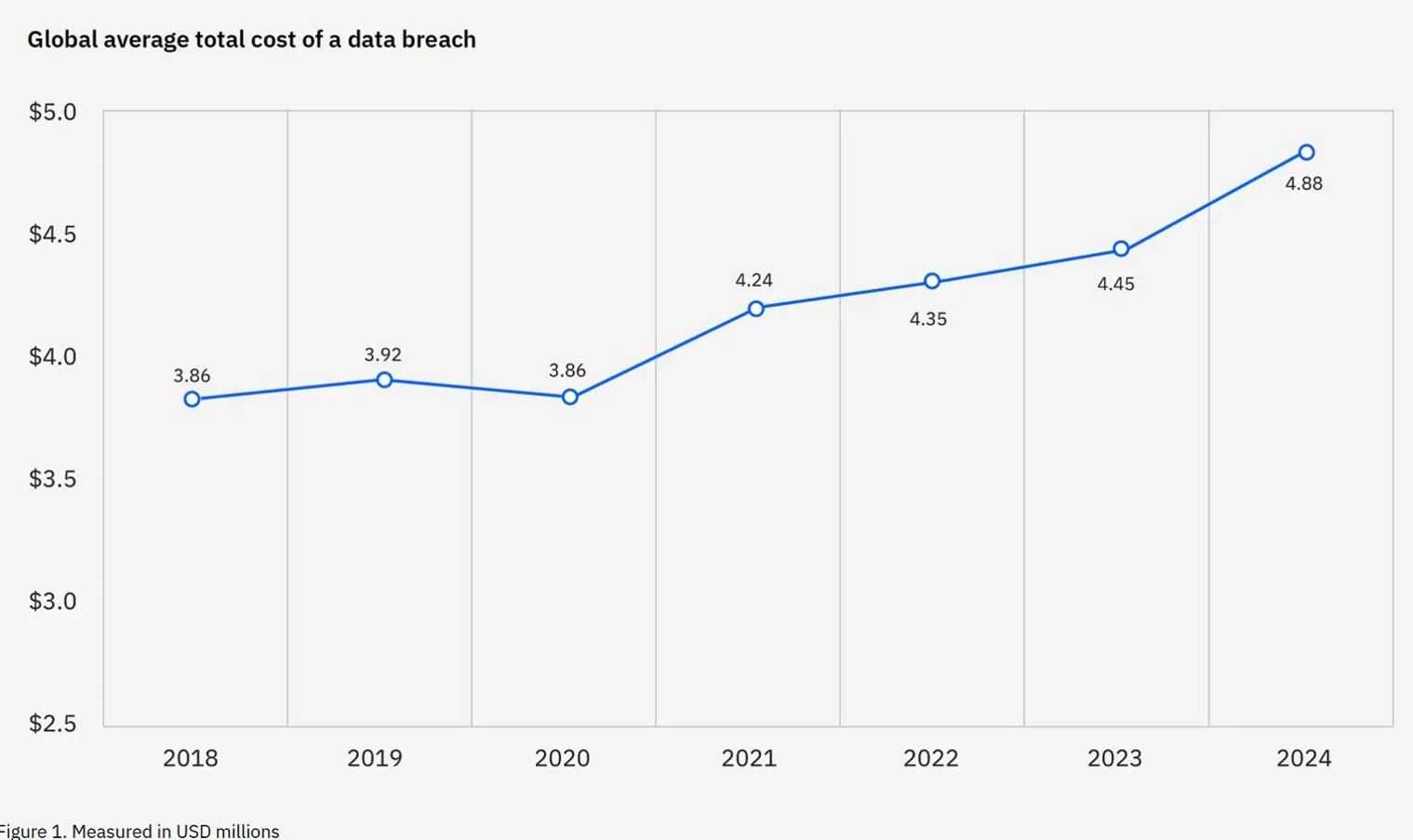
Cyberattacks often lead to significant monetary losses. In 2024, the global average cost of a data breach reached $4.88 million, a 10% increase from the previous year, as per IBM’s latest figures.
A notable example of how costly an incident can be is the 2021 ransomware attack on Colonial Pipeline which resulted in a $4.4 million ransom payment, not accounting for additional costs related to operational disruptions and reputational damage. For smaller businesses, such incidents can lead directly to bankruptcy.
Implementing a zero-trust architecture, which operates on the principle of "never trust, always verify," could have significantly reduced the risk of such an attack. This approach enforces strict access controls and continuous verification of all users and devices, which greatly minimizes the attack surface and prevents unauthorized lateral movement within the network.
2. Operational Impact
Cyber incidents can cripple business operations. In 2017, the NotPetya ransomware attack forced global shipping giant Maersk to halt operations for days, preventing the loading and unloading of ships at ports. Estimated losses from the incident were in excess of $200 million resulting from operational downtime and the cost of restoring systems.
Maersk could have mitigated the impact if it had adhered to a more robust cybersecurity framework, such as the NIST Cybersecurity Framework.
3. Reputational Impact
A tarnished reputation can do more damage than immediate financial losses. The 2017 Equifax data breach, which exposed the personal information of approximately 147 million people, put the company in the spotlight for all the wrong reasons, severely damaged its reputation and leading to a huge loss of consumer trust.
Adhering to standards like ISO/IEC 27001, which emphasize strong access controls, regular patch management, and continuous monitoring of vulnerabilities, can make a big difference, helping to prevent such breaches and maintain customer confidence.
Navigating Common Challenges in Cybersecurity Risk Management
No strategy is perfect. But knowing the potholes helps you steer better.
Let's explore some common obstacles with some tips and security best practices to address them:
- Resource constraints: Not every company has a CISO and six-figure tools. Focus on high-impact basics like training and endpoint security. Managed service providers (MSPs) can also offer cost-effective solutions that eliminate the need for extensive in-house resources.
- Managing third-party risks: Collaborations with vendors and partners can inadvertently introduce security weaknesses. Be sure to conduct thorough due diligence, establish robust vendor risk management programs, and enforce stringent access controls for external parties.
- Balancing risk with business goals: Locking everything down is great — until no one can access anything. Strive for a risk-based approach that harmonizes protective measures with your company's goals, ensuring that security doesn’t hinder productivity.
- Cultivating a culture of cybersecurity awareness: Human error is major factor in 95% of security breaches. Regular training programs can equip employees to identify phishing attempts, adopt strong password practices, and stick to security protocols, thereby strengthening the organization's overall security posture.
- Keeping security policies updated: The rapid advancement of technology can quickly render existing security policies obsolete. Regularly review and update your security policies, conduct vulnerability assessments, and stay informed about emerging threats.
The shift to remote work and rapid adoption of cloud-based tools have made it harder for organizations to define the edge of their networks, which has created new vulnerabilities, explains Erik Gaston, CIO for Global Executive Engagement at Tanium.
He adds that many traditional security tools and processes no longer meet the demands of today’s distributed environments, and leadership teams are being forced to rethink their strategies. The key, he says, is to view your network from an attacker’s perspective, and to equip teams with modern, integrated platforms that provide unified visibility, control over every endpoint, and a shared understanding of the threats.
Cybersecurity Risk Management: Final Words
Cyber threats are getting more sophisticated, so organizations must proactively implement comprehensive strategies and adhere to established frameworks. This not only mitigates risks but also enhances reputation and competitiveness. To navigate this complex realm effectively, specialized expertise is a must-have.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the Top Cybersecurity Companies as well as:
- Top Cybersecurity Marketing Agencies
- Top Cybersecurity Incident Response Companies
- Top AI Cybersecurity Companies
- Top Cybersecurity Companies in Virginia
And don’t miss our Awards section, where we celebrate the most innovative projects in design — from logo and app design to print and packaging.
Cybersecurity Risk Management FAQs
1. Can small businesses afford risk management?
Yes — cybersecurity risk management doesn’t have to drain your budget. Start with the basics: enable multi-factor authentication, train your team to spot phishing attempts, and keep your software up to date. Many affordable tools are built with small businesses in mind.
2. How often should I reassess risks?
A good rule of thumb is to reassess quarterly. But certain events should trigger an immediate review — like when you onboard new technology, change third-party vendors, hire remote employees, or see headlines about data breaches in your industry. Cyber threats evolve fast, so your risk management strategy should too. Stay proactive rather than reactive.
3. Is ISO 27001 worth it?
If your business handles sensitive information or serves enterprise-level clients, ISO 27001 is more than worth it — it’s a competitive advantage. It shows customers and partners that you take data protection seriously and follow globally recognized standards. The certification process requires time and commitment, but the payoff is trust, credibility, and often, access to bigger contracts.






