Network security is what safeguards your website against the rising number of online threats and is absolutely essential for preserving the integrity of your business and the trust of your customers.
In this article, we will discuss how to secure a website using seven tried and tested methods and strategies that efficiently repel the most common types of cyberattacks.
What is Network Security?
Network security is a crucial aspect of keeping your network safe when running a business. It involves implementing protective measures to ensure digital systems, networks, and programs are protected from malicious attacks or unauthorized access.
By safeguarding company data and devices, network security guards against potential cyberattacks, safeguards confidential information, and grants employees access while restricting unauthorized access.
How To Secure a Website: Seven Essential Strategies
The seven website security methods are efficient against the above-mentioned types of threats as well as against human errors.
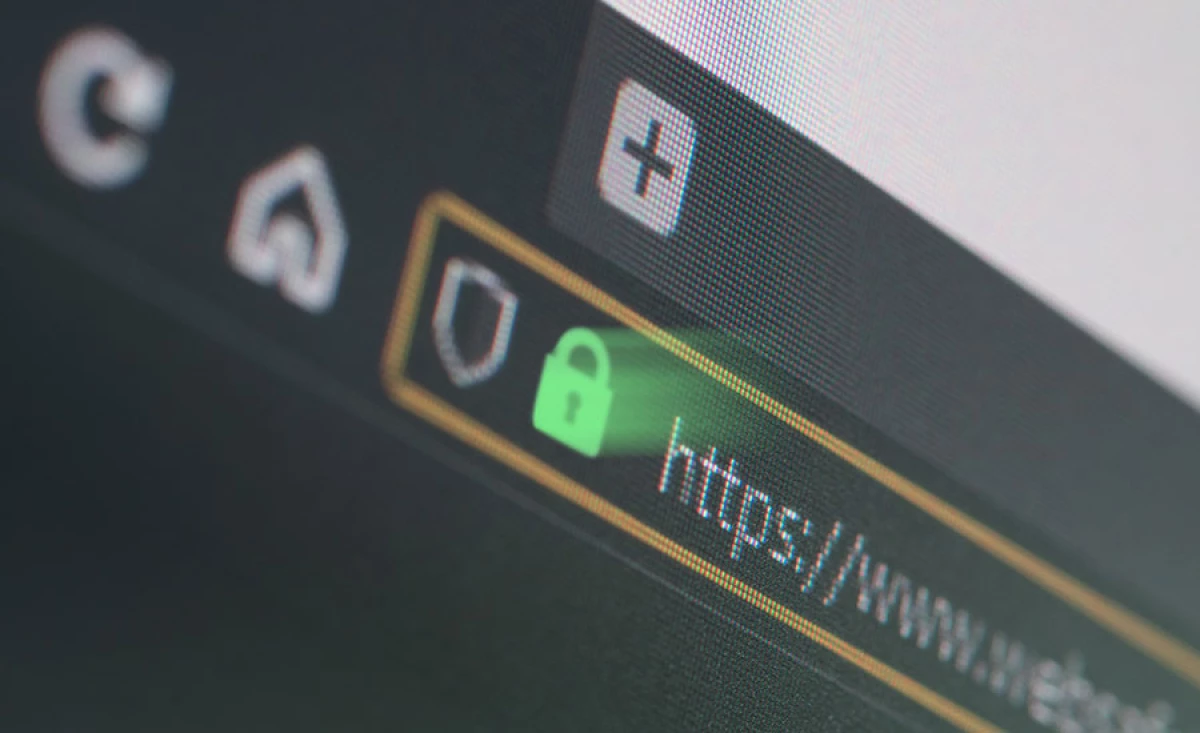
1. Claim and Install an SSL Certificate
Installing an SSL certificate is crucial to safeguarding your website and users.
SSL encrypts information passing between your site and visitors, and non-SSL sites are now "discriminated" against in Google search results.
SSL is especially crucial for websites that handle sensitive data such as payments or login information. Here are three main methods for installing SSL:
- Choose a reputable website builder that offers free SSL.
- Pick a hosting company that offers a free SSL with all plans if you're building your site with a content management system like WordPress.
- Install a free, basic Let's Encrypt SSL.
For higher security, advanced SSL certificates are available for purchase at a range of prices from hosting companies or domain registrars.
2. Update and Backup Your Site Regularly
By making backups of your website, you can be sure that in the worst-case scenario, with the assistance of a reliable cybersecurity agency, you'd still have a current version of the site safely stored and prepared for a relaunch.
A backup is essentially a copy of the files, content, media, and databases that make up your website. You will require more backup storage to store all of your data if your website is large or complex.
How do you back up your website so that everything continues to run smoothly? There are a variety of ways to backup your website, for example by using a:
- Paid backup service like CodeGuard or Sucuri to handle the work for you
- A web host that offers backups as part of its plans. Some hosts come with built-in backup software or offer it as an add-on.
- A WordPress plugin like VaultPress or UpdraftPlus. Users of WordPress can easily manage their own backup preferences and install the plugin of their choice.
If you don't update the scripts, security, and software on your website, malware and hackers will have no trouble exploiting your website.
This also applies to patches from the hosting provider for your website. When a website update becomes available, install it as soon as you can.
The certificates for your website should also be kept current. While your website's security won't be directly impacted, doing this will keep it visible in search results.
3. Opt For Secure Hosting
Web hosting services are a big consideration for making your website secure. Pick yours carefully.
Inquire about their security platform prior to building or transferring your website to a host. The best hosts collaborate with or employ professionals in the area of internet security. They are aware of how crucial it is that their client's websites are secure from attacks.
Make sure a fallback is offered. You might lose important data as a result of hack attacks. Rebuilding your website from a backup is simpler than starting from scratch.
4. Use Anti-Malware Software and Other Tools
There are numerous anti-malware options available. Some have free plans while others require payment.
Different levels of security with these programs imply that you can customize your security to meet both the needs of your website and your budget. It offers a variety of security services, such as:
- Vulnerability patching
- DDoS protection
- PCI compliance
- Web scanning
- Malware detection and removal
- Web application firewall
You should trust a reputable website builder or hosting company to take care of your site's security. Anti-malware software is frequently a part of hosting providers' plans.
Another set of tools is integrated by other providers, such as:
- Unfree SSL
- Hack protection
- Automatic backups
- DDoS defense
These are the fundamental security requirements for your website and the features you should search for when choosing a hosting company. Anti-malware software provides you with a welcome additional layer of protection, whether your provider includes built-in tools or offers supplemental freebies.
5. Implement Multi-level Login and Strong Passwords
There is a lot of ground to cover in terms of login security. But with just two straightforward implementations—strong passwords and multi-factor authentication—you can achieve a lot in that regard.
This is due to the fact that strong login security is built on a minimum of two layers. It’s usually a strong password and a code sent to an email or a phone.
Create multi-factor authentication logins once you have a secure password. This simply means that whenever a user wants to log in to your website, they will have to enter a code, which is typically sent to a device.
A strong password is the first step to the best website security. Every website's backend (the developer side) has a password-protected area. Although it may be tempting, resist the urge to use an easy-to-remember password.
Choose something that is extremely secure and difficult to decipher for anyone other than you. Use a combination of capital letters, punctuation, and numbers when creating passwords, or use a secure password generated by a password manager. Never use anything that is simple to deduce. This applies to every employee in your company.
6. Use a Web Application Firewall
A web application firewall is crucial in preventing common IT issues like SQL injections, XSS, and cross-site forgery. WAFs rely on pre-established rules to recognize and stop attacks, similar to the firewall on your computer. The three main types of WAFs are:
- Host-based firewall: Included in the application via a plugin or application.
- Cloud-based firewall: The most popular and easiest to integrate.
- Network-based firewall: Installed between the application and the user.
7. Educate and Train Your Employees
95% of online and network security breaches are caused by human error.
Smart hackers can trick even the best cyber security firms, but occasionally the guilty party is identified as an untrained employee. Even if your staff members are the best in the business at what they do, they are still capable of making simple errors that invite viruses and attacks.
You must teach your staff to be alert for suspicious activity and cautious when clicking any dubious links or emails from unknown senders if you want to prevent these kinds of errors. Employees may give unauthorized access to sensitive data, including email addresses, phone numbers, login information, and credit/debit information, as a result of phishing attacks in particular.
Run a cyber security awareness training program within your company to instruct your staff on how to safeguard the information of the business and its clients.
How To Secure a Website Takeaways
Websites and their users are most commonly exposed to ransomware, malicious codes and viruses, phishing attempts and Denial of Service. Enterprise cybersecurity is a crucial consideration when running an online business.
To effectively put a stop to these attempts, you should cover these website security grounds:
- Install an SSL certificate
- Make regular backups
- Update your website
- Choose secure hosting
- Use two-factor authentication and strong passwords
- Use anti-malware software
- Opt for a web application firewall
It's also worth mentioning that there are hordes of excellent web development agencies out there that are ready to help you tackle your web security, and they could even save you time, money, and resources in the long run.
How to Secure a Website FAQs
How to check if a website is secure?
The first step you can take is to find and check the secure sockets layer (SSL) certificate. This protects sensitive information transmitted from the browser to the server.
Your URL should be safe if it starts with “https” instead of “http.” This means that the site is secured and encrypted with an SSL certificate. There should also be a trust seal that states “Secure” or “Verified.” This indicates that a website uses HTTPS security, among other safety features like the latest malware scan schedule.
Next, take a good look at the domain name. If it is similar to an existing big website but does not seem quite right, it must be a fake phishing site trying to trick users into accessing it.
Finally, you can check the website’s privacy policy. A legitimate site should declare a privacy policy that mentions what data are collected and how they are used and protected.
How do websites get hacked?
Websites can get hacked by brute-force attacks. These may be the simplest form of accessing a site, where the hacker tries to guess and log in with potential username and password combinations.
Another way attackers use is social engineering, i.e., building phishing web pages to trick people into keying in a username and password.
There is also cross-site scripting (XSS) or cross-site request forgery (CSRF) through which a hacker can intercept login credentials via unsecured networks or the user’s own browser.
Another hacking method is "dorking." It is when malicious intruders exploit search engine functionalities to locate these credentials and other login information.
What are the most common types of cyberattacks?
Malware can be ransomware, spyware, worms, or other viruses. Network vulnerability breaches through malware typically occur when a user clicks on malicious email attachments and links that automatically download risky software.
When malware enters a system, it can block access to the network’s key components, install harmful software, obtain sensitive information from the drive, and disrupt system operations, making it inaccessible.
Another one of the most common types of cyberattacks is phishing. It sends fraudulent correspondences, usually emails, that seem to come from popular or reputable sources. It intends to steal sensitive data, such as login credentials or bank and credit card information from the unsuspecting user.
There is also the man-in-the-middle (MITM) attack or eavesdropping attack. The two most common points of entry for this type of cyberattack are unsecured public Wi-Fi connections and a device breached with malware.
The intrusive practice involves intercepting web traffic, filtering, and stealing the victim’s information in the process.
Meanwhile, there is the denial-of-service attack. It aims to flood a network or server with heavy traffic to exhaust bandwidth and resources. In turn, the system cannot fulfill legitimate requests. This can also result in the system confusing valid requests with malicious ones.
Cybercriminals need to utilize several compromised devices to launch a denial-of-service attack.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the Top Web Development Companies, as well as:
- Top Cybersecurity Companies
- UI/UX Design Agencies
- Cybersecurity Incident Response Companies
- B2B Web Design Agencies
- Top Web Development Companies in Chicago
Our design experts also recognize the most innovative design projects across the globe. Visit our Awards section to see the best in design.


-preview-webp.webp)

