A cybersecurity request for proposal (RFP) is a document companies use to find the right vendor for their security needs. It outlines the organization’s needs, the technical requirements, and how responses will be evaluated. The challenge is knowing where to start and how to write one that actually gets quality responses.
Our guide will walk you through each essential section of a cybersecurity RFP. You’ll also get practical advice for evaluating vendors and a free, customizable template to help you start strong and save time.
Why Do You Need a Cybersecurity RFP?
A cybersecurity RFP is essential for any organization investing in protection, compliance, or infrastructure upgrades. It provides vendors with the right information, helping your company make a confident, informed decision.
Companies typically need a cybersecurity RFP when adopting new IoT tools, reviewing existing systems, or ensuring compliance. Any time a serious investment in cybersecurity is on the table, an RFP helps set a clear direction.
The following are the key benefits of a cybersecurity RFP:
- Brings structure and clarity to the process
- Helps vendors understand exactly what’s needed
- Encourages focused, competitive responses
- Reduces confusion and misalignment
- Supports better decision-making across teams
Key Components of a Cybersecurity RFP (With Examples)
-content.jpg)
Each section in a cybersecurity RFP is vital in helping vendors understand what you need, how to meet those needs, and how you’ll decide who gets the job.
Here’s what to include — and how to get it right.
- Executive summary
- Background and context
- Scope of work
- Technical requirements
- Deliverables and reporting expectations
- Timeline and milestones
- Budget constraints and pricing format
- Evaluation criteria
- Proposal submission instructions
1. Executive Summary
This section gives vendors a quick snapshot of the project. It should explain what you’re looking for, why you need it, and what success looks like from your point of view. Think of it as the opening pitch that frames the entire opportunity.
Example:
A mid-sized financial firm is looking for a vendor to provide 24/7 managed detection and response services across its cloud and on-prem infrastructure. The goal is to improve visibility, reduce threat response time, and maintain compliance with FINRA and NIST 800-53 standards. The company is looking for a long-term partner who can grow with its evolving needs.
2. Background and Context
Give vendors some context so they can tailor their approach. Share who your organization is, what it does, and what prompted the RFP. This helps vendors avoid making assumptions and focus on solutions that fit.
Example:
A regional healthcare provider is expanding its digital services and needs to strengthen its cybersecurity posture to meet HIPAA and HITRUST requirements. Its internal IT team handles day-to-day operations but lacks bandwidth for 24/7 threat detection and response. The company is now looking for outside support to close that gap and prepare for an upcoming audit.
3. Scope of Work
This is where you spell out what the vendor is actually responsible for. Be clear about which services are required, which ones are optional, and what systems or platforms are involved. Vendors need this detail to price and plan their work accurately.
Example:
The selected vendor will manage endpoint protection, cloud security monitoring, and incident response across Microsoft 365 and AWS. Optional services include third-party risk assessments and SOC 2 readiness support. Knowledge transfer and training for the internal IT team are also expected before the final handoff.
4. Technical Requirements
Outline the minimum technical standards a vendor must meet. This includes compliance frameworks, system compatibility, and preferred cybersecurity tools or certifications. The more specific you are, the easier it is to filter out poor-fit proposals.
Example:
Vendors should have experience with ISO 27001 and NIST CSF, and their solutions must integrate with Azure AD, CrowdStrike, and Splunk. Any cloud components must follow zero trust architecture and support role-based access. Certifications like SOC 2 Type II and CISSP are preferred.
5. Deliverables and Reporting Expectations
Let vendors know what they’re expected to deliver — and when. Be clear about the types of reports, documents, and updates you’ll need throughout the project. This helps prevent gaps and sets a standard from the start.
Example:
The vendor must provide monthly threat activity reports, quarterly risk assessments, and real-time access to incident logs through a secure portal. Executive summaries should be included with each quarterly report. All documentation must be audit-ready and follow the company’s internal formatting guidelines.
6. Timeline and Milestones
Set expectations around timing. Include when the work should start, how long each phase should take, and any key deadlines tied to compliance or internal planning. A milestone-based approach helps vendors stay on track.
Example:
The project should kick off by Aug. 1, with onboarding completed within 30 days. A full risk assessment is due within 45 days of contract signing. The final implementation must be completed by Dec. 15 to align with the company’s year-end goals.
7. Budget Constraints and Pricing Format
Giving vendors a general idea of your budget range and how you want them to format their pricing is helpful. That way, you can compare proposals apples-to-apples. Include whether your budget is fixed or flexible and if you want itemized costs.
Example:
The company has set aside up to $250,000 for the first year. Vendors should break out pricing by service category (e.g., monitoring, response, reporting) and list any one-time setup fees. Include fixed-rate and usage-based pricing options if available.
8. Evaluation Criteria
Let vendors know how you’ll be reviewing their proposals. List the main categories you’ll be scoring and what matters most within each one. This helps vendors focus their proposals and saves you time during review.
Example:
Proposals will be evaluated on technical approach (30%), experience (25%), cost (20%), reporting and documentation quality (15%) and timeline (10%). Under the technical approach, the company will look at scalability, automation, and how well the solution integrates with current systems. Documentation will be judged based on clarity, completeness, and usefulness for audits.
9. Proposal Submission Instructions
Close with clear instructions on how to submit. Include the deadline, preferred file format, submission method, and a contact person for questions. If there’s a Q&A window or a pre-bid meeting, mention that too.
Example:
All proposals need to be forwarded in PDF format by 5 p.m. ET on May 10 through the company’s procurement portal. Questions will be accepted until Apr. 25 at securityrfp@company.com. Late proposals will not be considered.
How To Evaluate Cybersecurity Proposals Effectively
Getting strong proposals is only half the battle — knowing how to evaluate them is what makes the difference. Without a clear process, it’s easy to get lost in technical jargon, flashy presentations, or pricing that looks better than it is. A company needs a consistent framework for comparing responses to make a smart, confident decision.
Below are key tips to help evaluate cybersecurity proposals with focus and clarity:
- Build a weighted scoring system: Assign a value to each evaluation category, such as technical approach, vendor experience, and cost. This gives structure to your review process and helps avoid decisions based on guesswork.
- Compare how each solution fits: Look at how well each proposal aligns with your current systems, processes, and compliance obligations. Proposals that require major changes or custom work without clear benefits should be weighed carefully.
- Ask the right questions: Once you’ve shortlisted finalists, use interviews to clarify key details and test how well the vendor understands your priorities. Pay attention to how they communicate, not just what they say.
- Request examples: Ask for sample reports, playbooks, or dashboards the vendor has created for other clients. These materials reveal their communication style, knowledge depth, and documentation approach.
- Verify credentials and references: Don’t rely on what’s written in the proposal — confirm certifications, test their experience, and speak to other clients if possible. A strong track record means more than a polished pitch.
- Factor in post-sale support: Evaluate how each vendor plans to handle onboarding, ongoing support, and knowledge transfer. Proposals that end at delivery without a clear support plan should raise concerns.
- Look for pricing clarity: Pricing should be transparent, detailed, and easy to follow. Unclear terms or vague cost structures can lead to confusion and even budget issues.
Common Cybersecurity Requirements To Include in Your RFP
Defining clear cybersecurity requirements is one of the most important steps in writing an effective RFP. Without detailed expectations, vendors are left to guess what matters most, which leads to vague proposals and mismatched solutions.
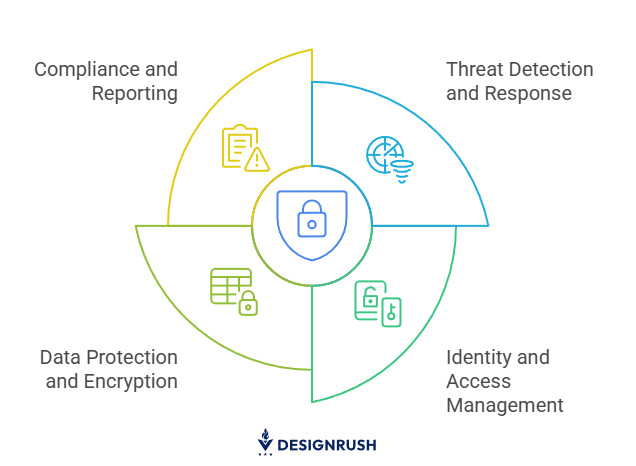
Here are the most common cybersecurity requirements to include:
- Threat detection and incident response
- Identity and access management (IAM)
- Data protection and encryption
- Compliance and reporting
1. Threat Detection and Incident Response
Companies need vendors who can detect and respond to threats in real time across all environments. This should include behavioral analytics, automated response capabilities, and 24/7 coverage. The RFP should ask vendors to explain their detection methods, provide sample response timelines, and describe how incidents are tracked and resolved.
2. Identity and Access Management (IAM)
Strong IAM controls are essential for minimizing risk and managing user access across systems. Vendors should support MFA, role-based access, and SSO and provide detailed audit logs that track permissions and login activity. The RFP should also ask how IAM integrates with platforms like Azure AD, Okta, or Google Workspace.
3. Data Protection and Encryption
Protecting sensitive data is non-negotiable. The RFP should require encryption for data in transit and at rest, clear key management practices, and support for secure backup and recovery. Vendors should also detail how they handle data loss prevention and whether controls can be customized by risk level or data type.
4. Compliance and Reporting
Every organization must meet certain regulatory or internal compliance standards, and the vendor should help support that. The RFP should ask which frameworks the vendor aligns with (e.g., NIST, ISO 27001, HIPAA) and request sample reports or documentation used in audits.
Companies should also clarify how often reports are delivered and who they’re intended for — technical teams, auditors, or executives.
 Free Cybersecurity RFP Template [Downloadable]
Free Cybersecurity RFP Template [Downloadable]
[Your Company Name]
[Your Company Address]
[City, State, ZIP Code]
[Your Email] | [Your Phone Number]
[Date]
Subject: Request for Proposal – Cybersecurity Services
Dear [Vendor Name],
[Your Company Name] is seeking a cybersecurity partner to support our organization’s security infrastructure, detection and response capabilities, and compliance efforts. We invite your team to submit a proposal outlining your approach, relevant experience, deliverables, and pricing for this engagement.
1. Company Overview
Please find below our company background for context:
Industry: [Insert Industry]
Services/products: [Insert Offerings]
Primary operations: [E.g., Cloud-based SaaS, financial services, retail locations]
Compliance requirements: [E.g., HIPAA, PCI-DSS, ISO 27001]
Website: [Insert URL]
2. Project Overview & Objectives
Our organization is undertaking a cybersecurity initiative to strengthen our defenses and meet compliance standards.
Current challenges: [E.g., lack of 24/7 monitoring, limited internal security resources]
Primary objectives: [E.g., real-time threat detection, faster incident response]
Secondary objectives: [E.g., improved reporting, better endpoint visibility]
3. Scope of Work & Requirements
Below is an outline of the required cybersecurity services:
Required services:
- 24/7 monitoring and incident response
- Threat intelligence integration
- Endpoint protection and EDR
- IAM support and MFA configuration
- Security reporting and documentation
- Compliance alignment with [Insert Frameworks]
- Employee security awareness training
Platforms in use: [E.g., Microsoft 365, AWS, Azure, Okta]
Preferred integrations: [E.g., Splunk, CrowdStrike, ServiceNow]
4. Timeline & Deadlines
Please refer to the following key dates:
RFP issue date: [Insert Date]
Proposal deadline: [Insert Date]
Vendor selection: [Insert Date]
Project start date: [Insert Date]
Target go-live: [Insert Date]
5. Budget Information
We request a pricing proposal that aligns with the following:
Estimated budget: [Insert Range or “To be determined based on scope”]
Preferred pricing model: [E.g., fixed fee, hourly rate, milestone-based]
Any additional costs: [E.g., licensing, onboarding fees]
6. Evaluation Criteria
Proposals will be evaluated based on the following weighted criteria:
- Experience with similar cybersecurity projects (30%)
- Technical approach and compatibility with our environment (25%)
- Pricing and long-term value (20%)
- Reporting and documentation quality (15%)
- Client references and past performance (10%)
7. Submission Requirements
Please include the following in your proposal:
- Company background and relevant cybersecurity experience
- Case studies or examples of similar projects
- Key team members and certifications
- Proposed service approach and project plan
- Timeline and pricing breakdown
- Any assumptions or constraints
8. Contact Information
For any questions regarding this RFP, please contact:
Primary contact: [Full Name, Title]
Email: [Insert Email]
Phone: [Insert Phone]
We appreciate your time and interest in partnering with [Your Company Name]. We look forward to reviewing your proposal.
Sincerely,
[Your Name]
[Your Title]
[Your Company Name]
Download Your Free Cybersecurity RFP Template
Want this template in a ready-to-use format? Get the fully editable version in Word or Google Docs.
Download your free eCommerce RFP template from the right side of this page.
Final Tips for Writing a Successful Cybersecurity RFP
A strong cybersecurity RFP helps your team make confident, informed decisions. Clear language, realistic expectations, and internal alignment can make or break the process.
Before sending your RFP out, keep these final tips in mind to increase your chances of finding the right partner.
- Tailor the RFP to your unique needs: Avoid reusing generic templates without adjusting them to your environment, infrastructure, and compliance priorities. Specificity will attract vendors who actually understand your challenges.
- Collaborate with internal stakeholders: Work closely with IT, legal, and procurement teams to make sure every section reflects operational, technical, and contractual needs. Internal alignment early on prevents delays later in the process.
- Keep it clear and vendor-friendly: Use straightforward language, avoid vague requirements, and organize your RFP in a way that's easy to navigate. A well-structured document encourages better responses from qualified vendors.
- Don't rush the vendor selection process: Give yourself time to review proposals, conduct interviews, and check references properly. The right vendor is an investment — not just a quick fix.
Cybersecurity RFP Takeaways
Creating a strong cybersecurity RFP takes more than listing requirements — it's about clarity, structure, and setting the right expectations. When done well, it helps your organization attract qualified vendors, compare proposals fairly, and choose a partner that fits both your goals and risk profile. Use this guide to walk through each section, apply the tips, and avoid common pitfalls.
Ready to get started? Download the free cybersecurity RFP template and customize it for your next project.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory to find top-rated cybersecurity companies, as well as:
- Top AI Cybersecurity Companies
- Top Digital Forensics Companies
- Top Identity Access Management Companies
- Top Penetration Testing Companies
- Top Security Assessment Companies
Our team also curates standout creative work on our Design Awards page, where you can explore award-winning branding, web, and digital design projects to see what strong execution looks like in practice.

-preview.jpg)



