In a world where mobile apps are business front doors, security is your brand's foundation. By embedding security into your culture, development process, and value proposition, you create mobile apps that users and enterprises feel safe adopting.
Mobile App Security: Key Points
- 91% of apps use outdated libraries and open-source components that haven’t been patched, creating silent vulnerabilities that attackers can easily exploit.
- 80% of apps have at least one security flaw and the average data breach in 2025 costs over $4 million.
- Stolen credentials were a top cause of breaches in 2023. Apps without MFA, session token protection, and secure login flows risk exposing users.
Mobile App Security Overview
In the digital age, mobile app security is increasingly about competitive advantage and business resilience.
Learn how to transform security from a liability into a competitive edge, so you can close big deals and access new revenue streams.
How Mobile App Security Leads to Business Growth
A vast majority of apps are vulnerable – 80% of applications have at least one security flaw – and breaches are more costly than ever. The average data breach costs $4.4 million, underscoring that poor security can literally break the bank.
Notably, a recent IBM study found a 10% jump in organizations planning to increase security budgets and invest in staff training, a sign that companies recognize the ROI of preventing breaches and building customer trust.
Security lapses have graduated from IT concerns to boardroom crises. Here’s why mobile app security demands immediate attention from both technical and business leaders:
- Enterprise sales require proof of security: B2B customers now include detailed security questionnaires and scoring in RFPs (request for proposal). Whether you’re an agency or software vendor, lacking clear DevSecOps documentation will get you filtered out early.
- Compliance enables market expansion: If you want to expand into regulated markets or work with Fortune 500 clients, you need to show that your app meets industry security standards. Compliance certifications open doors to new customer segments.
- Security builds trust and lifetime value: Companies that deliver secure-by-design mobile products foster higher user trust, which translates into greater retention and brand loyalty. Fewer incidents and more positive reviews lead to increased user engagement over time.
- AppSec offerings unlock premium margins: App security audits, ongoing maintenance, and compliance packages are great ways to monetize security features or simply command higher prices due to demonstrated advantages.
Top Threats Facing Mobile Applications in 2026
Mobile apps face a range of threats, from code-level vulnerabilities to misconfigurations. Serge Motin, Director of Start Mobile, points out:
“The most overlooked vulnerabilities in mobile app development today include insecure data storage, weak API security, and lack of input validation.”
Understanding evolving risk vectors enable you to design smarter, safer apps. Below are some of the most important threat categories that developers and security leads must address in 2025:
- Insecure data storage
- Reverse engineering & code tampering
- Weak authentication & session management
- Inadequate supply chain security
@chiara_techforfounders I want to make this conversation as constructive as possible, so I will start sharing some tips to review and improve the security stance of your application. #womenintech#confidentlytech#webdevelopment#appdevelopment#vibecoding♬ original sound - Chiara | Tech for Founders
1. Insecure Data Storage
Nearly 60% of iOS apps (and 43% of Android apps) have vulnerabilities that could expose personal data. This risk is especially pronounced in consumer finance and travel apps (which often cache data for offline use).
Storing sensitive data on any device without proper encryption remains a top breach vector for mobile apps. If an attacker obtains a lost/stolen device or malware compromises the app, they can easily extract user credentials, authentication tokens, personal data, or API keys.
Bottom line: Always assume any data stored on the mobile device can be accessed by an attacker, and protect it accordingly through encryption, keychain usage, or secure storage APIs. More on these later.
2. Reverse Engineering & Code Tampering
Given enough time and tools, hackers can unpack or decompile your mobile app’s code to see how it works, and then modify it. This leads to intellectual property theft (your proprietary code/algorithms stolen), creation of modded apps or cheat clients, and even the insertion of malware into repackaged apps.
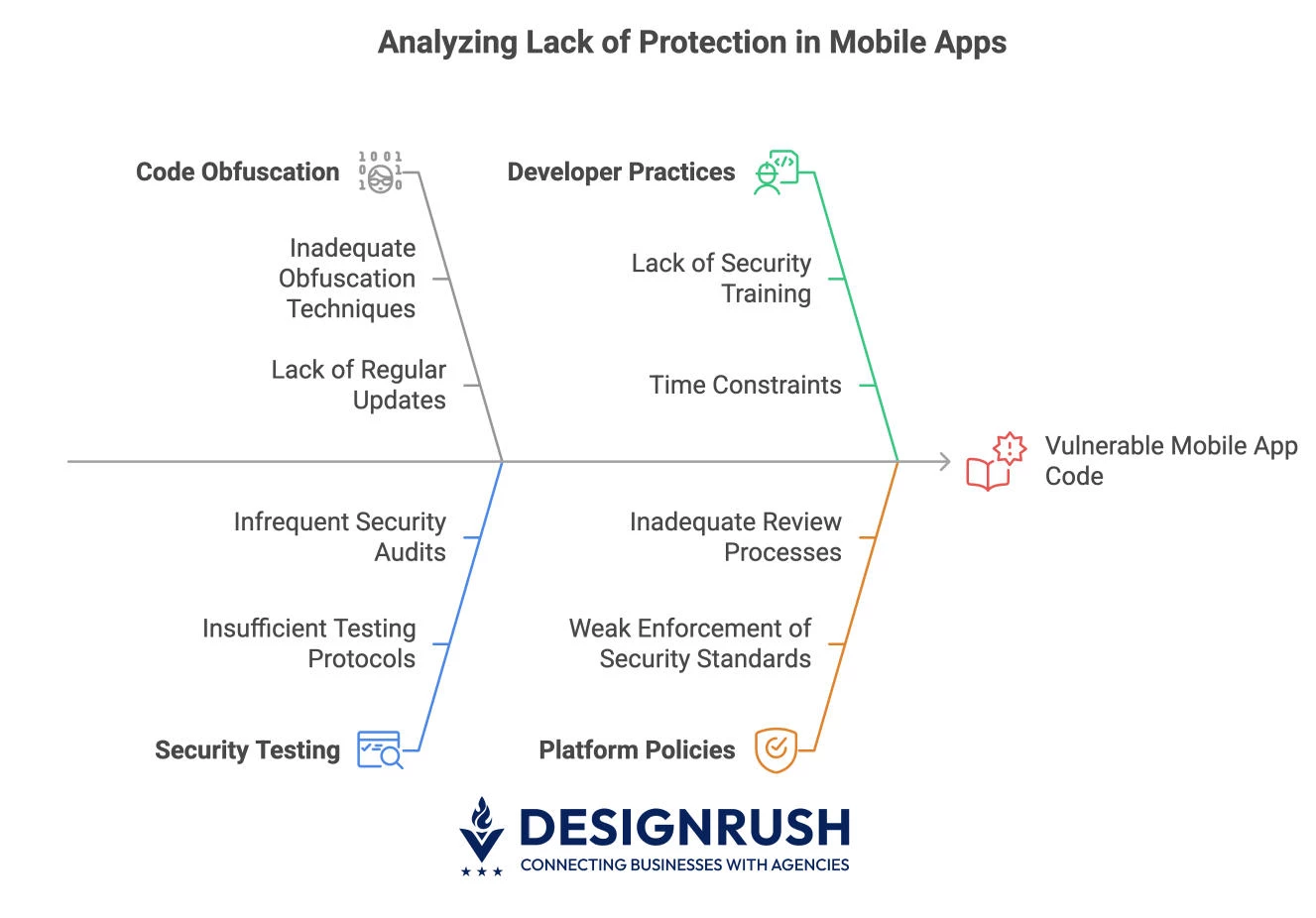
Unfortunately, many apps lack binary protections, so an attacker can analyze and alter the code almost as if they were open source. The consequences include cloned apps, exposed secrets, or Trojanized versions of your app circulating on the internet.
3. Weak Authentication & Session Management
Credential theft and reuse attacks have been on the rise: globally, stolen credentials were one of the top causes of breaches in 2023.
If your app’s authentication and session handling are weak, attackers don’t even need to bother with your code. They can simply walk in through the front door.
Common pitfalls include the lack of multi-factor authentication (MFA) for high-value accounts, easily guessable or hard-coded passwords, poor password reset flows, and leaking session tokens.
Mobile apps that rely only on device identifiers or single-factor logins are also vulnerable to credential stuffing and brute-force attacks.
4. Inadequate Supply Chain Security
An emerging threat category in mobile is the software supply chain, i.e. the third-party code, libraries, and services your app depends on. A vulnerable or malicious SDK can compromise your app just as surely as a bug in your own code.
According to a 2023 Synopsys audit, 84% of codebases contained at least one known open-source vulnerability. Additionally, many mobile apps incorporate dozens of open-source libraries, and 91% of apps were found to use outdated components with known fixes available.
Proven Strategies to Secure Mobile Apps
Security can’t be retrofitted at the last minute — it must be embedded from the start of mobile app development. The following are key strategies that reduce risk and can become differentiators for your organization:
- Shift security left with CI/CD integration
- Harden apps with runtime protections
- Vet SDKs and third-party libraries
- Establish a mobile app development security playbook
1. Shift Security Left with CI/CD Integration

By baking security protocols into your GitHub/GitLab workflows, you can get rapid feedback on security issues during development rather than after release.
Early fixes are dramatically cheaper (fixing a bug in production can cost 30x more than fixing it during coding). “Shifting left” reduces remediation cost and prevents security issues from snowballing.
To catch vulnerabilities before your app ships, follow these steps:
- Integrate security tests into your development pipeline (CI/CD)
- Utilize tools like MobSF (Mobile Security Framework) for automated static/dynamic analysis of your mobile app builds
- Use SAST (static application security testing) to scan code for flaws on every commit
- Incorporate DAST (dynamic testing) using frameworks like OWASP ZAP or Burp Suite against staging builds
2. Harden Apps with Runtime Protections
Runtime protections defend against active exploitation once the app is live. This is especially critical for consumer-facing apps or those operating in high-risk verticals like fintech, healthtech, and gaming, where IP theft, code tampering, and fraud are rampant.
It’s important to obfuscate your code and enable anti-tampering, anti-debugging, and root/jailbreak detection in your app. Here’s how:
@appdome Welcome to episode 27 of Mobile Security Knowledge! Let’s discuss Runtime Application Self Protection (conmonly known as RASP). Visit https://www.appdome.com/free-trial/mobile-rasp-security-android-ios/ to get starter today. #appdome#RASP#appsecurity#mobileapps#mobilesecurity#videoseries#securityattack♬ original sound - Appdome
- Obfuscate your code: Use tools like DexGuard and iXGuard to obfuscate code and embed protections that detect debugging, hooking, or tampering — making it significantly harder for attackers to analyze, reverse-engineer, or alter your app.
- Layer active runtime defenses: Apply no-code solutions like AppSealing to add server-managed security layers that prevent repackaging, code injection, and dynamic attacks. These actively detect threats and enforce shutdowns on compromised or tampered environments.
- Enforce device integrity checks: Restrict or limit app functionality on rooted or jailbroken devices where security is weakened. At minimum, alert users and disable sensitive features to reduce the risk of data leaks and unauthorized access.
3. Vet SDKs and Third-Party Libraries
Third-party software development kits (SDKs) and open-source libraries accelerate development, but they also expand your attack surface. Every external dependency introduces potential vulnerabilities you don’t directly control, yet are fully accountable for.
A secure, transparent software supply chain can help win enterprise trust, pass compliance audits, and avoid costly reengineering down the line.
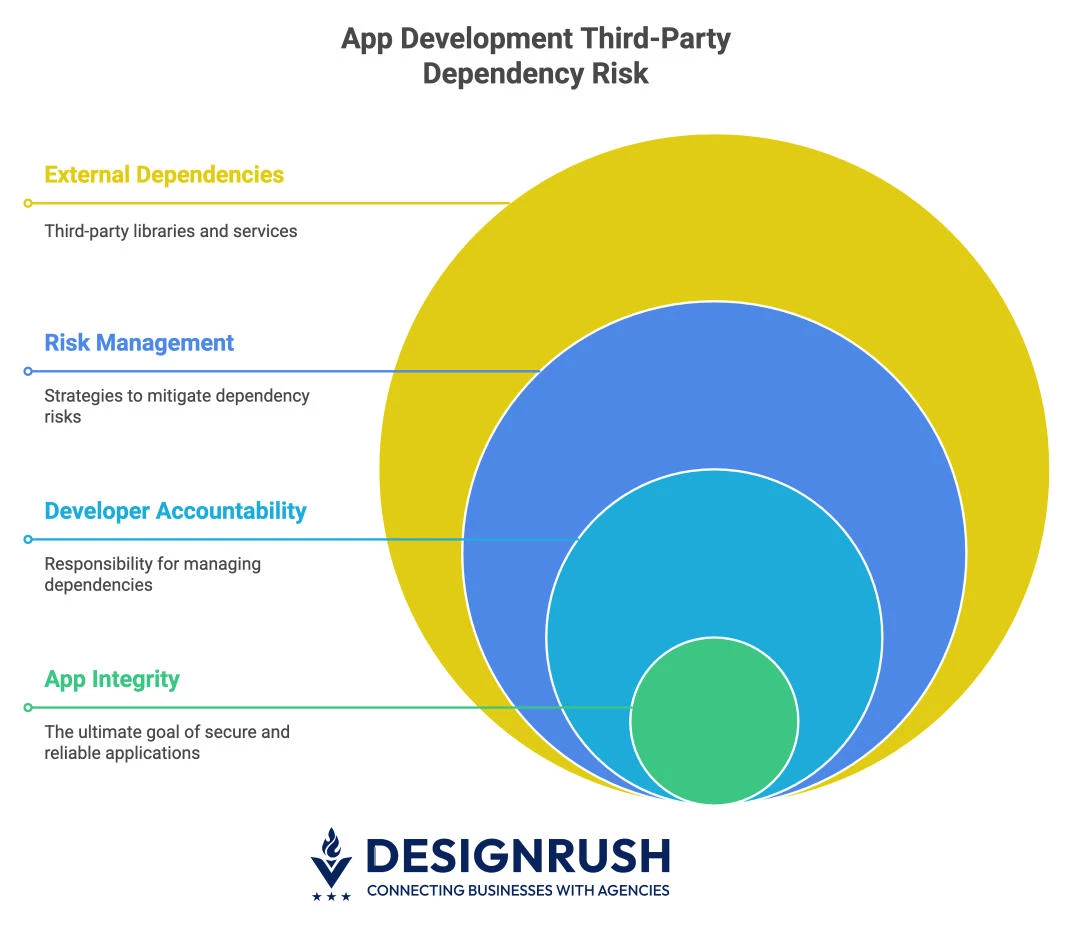
To reduce exposure and improve security resilience, adopt these best practices:
- Perform continuous software composition analysis (SCA): Use tools like Snyk or Black Duck to scan for known vulnerabilities in third-party code and automate this process within your CI/CD pipeline for real-time visibility and rapid mitigation.
- Maintain and update your software supply chain: Regularly update dependencies and remove any modules or SDKs that are outdated, unmaintained, or non-essential. Fewer, current components reduce your attack surface and compliance risk.
- Audit SDK behavior and data access: Closely evaluate third-party SDKs — especially those for ads, analytics, or social login — for excessive permissions or data collection. Eliminate those that compromise privacy or security standards.
4. Establish a Mobile App Development Security Playbook
A documented security approach for your development process aligns developers, satisfies enterprise procurement requirements, and reinforces that security is embedded in your product culture.
Whether you're building in-house or client-facing apps, it’s a powerful differentiator. To implement a playbook that drives trust and operational efficiency:
- Define and document your secure development lifecycle: Clearly outline each stage of development with embedded security checkpoints. This ensures consistent protection from design through deployment.
- Standardize secure coding practices across your team: Include detailed guidance on topics like input validation, credential storage, encryption, and handling secrets. Your team should follow a unified approach to prevent common vulnerabilities and streamline peer reviews.
- Use the playbook to support audits and client trust: Share your playbook during client engagements or procurement reviews to demonstrate readiness and rigor. For internal teams, it simplifies onboarding and incident response across departments.
Best Tools for Security in Mobile App Development
Integrating these security tools into your workflow will automate a lot of security checks and balances, making it easier to develop secure apps without relying purely on manual reviews. Automation is key – you want security to be a built-in continuous process.
| Tool | Best For | Use Cases |
| MobSF | All-in-one mobile security testing | Static, dynamic, and malware analysis |
| Snyk | Open-source dependency scanning | Identify and fix vulnerable libraries |
| SonarQube | Code quality and SAST | Detect insecure code patterns early |
| AppSealing | Runtime protection without code changes | Shield apps from tampering or hooking |
| Checkmarx | Enterprise-grade SAST/DAST | Secure lifecycle development for large teams |
| Guardsquare | Code obfuscation and RASP | Prevent reverse engineering, protect IP |
| ZAP | Dynamic application testing | Pen test APIs and client-side logic |
| Black Duck | Software composition analysis (SCA) | Track and manage open-source risk |
Navigating Compliance: A Strategic Advantage
Compliance often demands strong security measures and achieving it can be a strategic business move to unlock certain markets. When you align with relevant compliance frameworks early, you can turn legal requirements into competitive advantages.
Here a some of the major compliance areas that affect mobile apps, and how focusing on security will help you meet them:
1. GDPR & CCPA (Data Privacy)
If your app handles personal data from users in regions like the EU (GDPR) or California (CCPA), you must build in privacy by design. Regulators expect that sensitive user data (PII) is protected by strong encryption both on the device and on servers.
Demonstrating privacy-by-design can accelerate enterprise partnerships and win over privacy-conscious users. Noncompliance can result in multi-million-dollar fines and permanent brand damage.
To ensure your mobile app meets modern data privacy expectations:
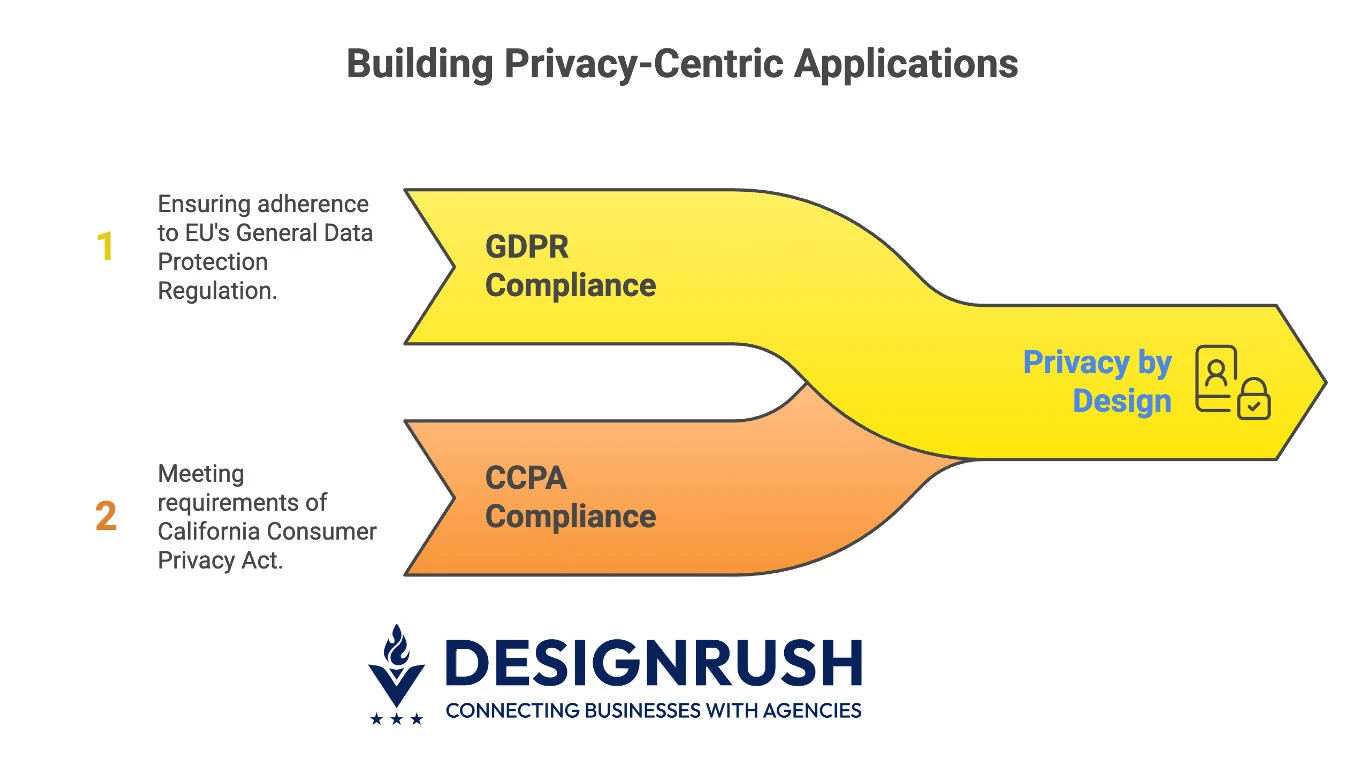
- Encrypt personal data in transit and at rest: Apply strong encryption standards (e.g., AES-256, TLS 1.2+) to protect sensitive data both on the device and server. This safeguards user information and meets baseline expectations from regulators and enterprise clients.
- Implement explicit consent and opt-in flows: Design clear, user-friendly consent screens for any data collection, especially for tracking or sensitive categories. Allow users to manage consent preferences easily through in-app privacy settings.
- Support right-to-erasure and data portability: Enable users to request deletion of their data or download a complete export. Build backend workflows that can fulfill these requests within legally mandated timeframes.
- Minimize data collection and limit third-party exposure: Collect only the data you truly need and avoid unnecessary sharing with third-party SDKs. A leaner data footprint lowers compliance risk and simplifies privacy management in your ecosystem.
2. HIPAA & PCI-DSS (Industry-Specific Security)
Regulations like HIPAA (for healthcare) and PCI-DSS (for payment processing) are non-negotiable for apps operating in regulated industries. These frameworks set the standard for how sensitive data (e.g., health records or credit card details) must be protected.
To align with HIPAA and PCI-DSS standards, take these key actions:
- Follow structured frameworks like HITRUST or NIST: Adopt security frameworks that map directly to HIPAA and PCI-DSS controls. They offer detailed guidance on encryption, access, and data lifecycle management.
- Conduct regular security testing and vulnerability scans: Use penetration testing, SAST/DAST tools, and third-party audits to uncover and resolve vulnerabilities. This is a PCI-DSS requirement and a HIPAA best practice for safeguarding critical systems.
- Maintain detailed audit trails for all data access: Log every interaction with health or cardholder data, including who accessed it, when, and what actions were taken. These logs are critical for compliance reporting and breach forensics.
- Enforce strong access control and authentication: Use role-based access, secure login protocols, and MFA for privileged users. This ensures only authorized individuals can view or manage sensitive information.
3. OWASP Mobile Top 10 Alignment
@_shark_byte Explaining the OWASP top 10 in 60 seconds #owasptop10#owasp#ethicalhacker🕵️♂️#bugbountyhunting#pentesting#cybersecurity#csstudent#careersintech♬ Paint The Town Red (Instrumental) - Doja Cat
Beyond laws and industry standards, there are also community-driven standards like the OWASP Mobile Top 10 that can guide your security program. Ensuring your development and testing address each of those Top 10 risks can effectively make your app OWASP compliant.
Many organizations treat OWASP guidelines as a minimum bar for their vendors. This isn’t a formal certification, but it’s something you can highlight in proposals and documentation.
For instance, you might maintain an OWASP compliance matrix for your app or service, mapping how you mitigate each of the Top 10 risks. Enterprise clients (especially security-savvy ones) appreciate this level of diligence.
Pro Tip: Use your compliance readiness as a marketing asset. When you prominently advertise expertise in “HIPAA-compliant development” or “GDPR data practices,” your team can win trust faster.
Mobile App Security: Final Thoughts
By turning robust mobile app security into a core strength, you’re not only reducing risk; you’re accelerating your business. In the competitive digital economy of 2026, the winners will be those who are trusted to deliver secure experiences.
So, bake in that security, flaunt it (with well-earned confidence), and watch it pay dividends in both protection and profit.

Our team ranks agencies worldwide to help you find a qualified partner. Visit our Agency Directory for the top mobile app development companies as well as:
- Top Android App Development Companies
- Top iPhone App Development Companies
- Top Cross-Platform App Development Companies
- Top Enterprise Mobile App Development Companies
- Top App Development Companies for Startups
Our design experts also recognize the most innovative design projects across the globe. Visit our Awards section to see the best & latest in app design.
Mobile App Security FAQs
1. Do I need different compliance strategies for Android and iOS apps?
While core compliance goals (like encryption or consent) remain the same, each OS has unique APIs and limitations. For example, Android apps often require explicit keychain handling, while iOS may offer more built-in secure storage options.
2. How can I prove my app is secure to clients and enterprise buyers?
Create a mobile security playbook that documents your threat model, testing tools, DevSecOps practices, and alignment with OWASP and compliance standards. Sharing this proactively builds buyer confidence and accelerates RFP approvals.